User Guide
Page 4
... Clients Saving Configuration Settings Managing System Files Chapter 3: Configuring the Switch Using the Web Interface Navigating the Web Browser Interface Home Page Configuration Options... Panel Display Main Menu Basic Configuration Displaying System Information Displaying Switch Hardware/Software Versions Displaying Bridge Extension Capabilities Setting the Switch's IP Address Manual Configuration Using DHCP/BOOTP Enabling Jumbo Frames Managing Firmware Downloading System Software from a Server 1-1 1-1 1-2 1-6...
... Clients Saving Configuration Settings Managing System Files Chapter 3: Configuring the Switch Using the Web Interface Navigating the Web Browser Interface Home Page Configuration Options... Panel Display Main Menu Basic Configuration Displaying System Information Displaying Switch Hardware/Software Versions Displaying Bridge Extension Capabilities Setting the Switch's IP Address Manual Configuration Using DHCP/BOOTP Enabling Jumbo Frames Managing Firmware Downloading System Software from a Server 1-1 1-1 1-2 1-6...
User Guide
Page 6
... VLANs (VLAN Index) Adding Static Members to VLANs (Port Index) Configuring VLAN Behavior for Interfaces Configuring IEEE 802.1Q Tunneling Enabling QinQ Tunneling on the Switch Adding an Interface to a QinQ Tunnel Configuring Private VLANs Enabling Private VLANs Configuring Uplink and Downlink Ports Protocol VLANs Contents 3-73 3-74 3-76 3-76 3-78...
... VLANs (VLAN Index) Adding Static Members to VLANs (Port Index) Configuring VLAN Behavior for Interfaces Configuring IEEE 802.1Q Tunneling Enabling QinQ Tunneling on the Switch Adding an Interface to a QinQ Tunnel Configuring Private VLANs Enabling Private VLANs Configuring Uplink and Downlink Ports Protocol VLANs Contents 3-73 3-74 3-76 3-76 3-78...
User Guide
Page 8
... Configuration DHCP Snooping Binding Information IP Source Guard IP Source Guard Port Configuration Static IP Source Guard Binding Configuration Dynamic IP Source Guard Binding Information Switch Clustering Cluster Configuration Cluster Member Configuration Cluster Member Information Cluster Candidate Information Chapter 4: Command Line Interface Using the Command Line Interface Accessing the CLI Console...
... Configuration DHCP Snooping Binding Information IP Source Guard IP Source Guard Port Configuration Static IP Source Guard Binding Configuration Dynamic IP Source Guard Binding Information Switch Clustering Cluster Configuration Cluster Member Configuration Cluster Member Information Cluster Candidate Information Chapter 4: Command Line Interface Using the Command Line Interface Accessing the CLI Console...
User Guide
Page 15
... ip dhcp snooping verify mac-address ip dhcp snooping information option ip dhcp snooping information policy show ip dhcp snooping show ip dhcp snooping binding Switch Cluster Commands xii 4-206 4-206 4-207 4-208 4-208 4-209 4-209 4-210 4-211 4-211 4-212 4-212 4-213 4-213 4-214 4-215 4-215 4-216 4-216 4-217 4-218 4-219...
... ip dhcp snooping verify mac-address ip dhcp snooping information option ip dhcp snooping information policy show ip dhcp snooping show ip dhcp snooping binding Switch Cluster Commands xii 4-206 4-206 4-207 4-208 4-208 4-209 4-209 4-210 4-211 4-211 4-212 4-212 4-213 4-213 4-214 4-215 4-215 4-216 4-216 4-217 4-218 4-219...
User Guide
Page 20
Table 4-69 Table 4-70 Table 4-71 Table 4-72 Table 4-73 Table 4-74 Table 4-75 Table 4-76 Table 4-77 Table 4-78 Table 4-79 Table B-1 IGMP Query Commands (Layer 2) Static Multicast Routing Commands IGMP Filtering and Throttling Commands Multicast VLAN Registration Commands show mvr members - display description show mvr - display description IP Interface Commands IP Source Guard Commands DHCP Snooping Commands Switch Cluster Commands Troubleshooting Chart Tables 4-206 4-209 4-211 4-217 4-221 4-222 4-222 4-223 4-227 4-231 4-237 B-1 xvii display description show mvr interface -
Table 4-69 Table 4-70 Table 4-71 Table 4-72 Table 4-73 Table 4-74 Table 4-75 Table 4-76 Table 4-77 Table 4-78 Table 4-79 Table B-1 IGMP Query Commands (Layer 2) Static Multicast Routing Commands IGMP Filtering and Throttling Commands Multicast VLAN Registration Commands show mvr members - display description show mvr - display description IP Interface Commands IP Source Guard Commands DHCP Snooping Commands Switch Cluster Commands Troubleshooting Chart Tables 4-206 4-209 4-211 4-217 4-221 4-222 4-222 4-223 4-227 4-231 4-237 B-1 xvii display description show mvr interface -
User Guide
Page 22
... 3-33 Figure 3-34 Figure 3-35 Figure 3-36 Figure 3-37 Figure 3-38 Figure 3-39 Figure 3-40 Figure 3-41 Figure 3-42 Home Page Panel Display System Information Switch Information Bridge Extension Configuration Manual IP Configuration DHCP IP Configuration Bridge Extension Configuration Copy Firmware Setting the Startup Code Deleting Files Downloading Configuration Settings for...
... 3-33 Figure 3-34 Figure 3-35 Figure 3-36 Figure 3-37 Figure 3-38 Figure 3-39 Figure 3-40 Figure 3-41 Figure 3-42 Home Page Panel Display System Information Switch Information Bridge Extension Configuration Manual IP Configuration DHCP IP Configuration Bridge Extension Configuration Copy Firmware Setting the Startup Code Deleting Files Downloading Configuration Settings for...
User Guide
Page 26
... Supports standard STP, and Rapid Spanning Tree Protocol (RSTP) and Multiple Spanning Trees(MSTP) Virtual LANs Up to maximize the switch's performance for Layer 2 switching. The default configuration can be used for most of features for your particular network environment. MD5 or SHA password Port - ...Key Features Table 1-1 Key Features Feature Description Configuration Backup and Backup to 8K MAC addresses in this switch. IEEE 802.1X, MAC address filtering Access Control Lists Supports up to 128 ACLs, 96 MAC rules and 96 rules per system ...
... Supports standard STP, and Rapid Spanning Tree Protocol (RSTP) and Multiple Spanning Trees(MSTP) Virtual LANs Up to maximize the switch's performance for Layer 2 switching. The default configuration can be used for most of features for your particular network environment. MD5 or SHA password Port - ...Key Features Table 1-1 Key Features Feature Description Configuration Backup and Backup to 8K MAC addresses in this switch. IEEE 802.1X, MAC address filtering Access Control Lists Supports up to 128 ACLs, 96 MAC rules and 96 rules per system ...
User Guide
Page 27
...features. Port-based authentication is also supported via the console port, Telnet or web browser. Configuration Backup and Restore - This switch authenticates management access via the IEEE 802.1X protocol. You can be used by the attached device. Flow control eliminates the loss... client, and then verifies the client's right to double the throughput of the management features are exceeded. Port Configuration - The switch supports flow control based on MAC address or Ethernet type). Other authentication options include HTTPS for IP frames (based on address, ...
...features. Port-based authentication is also supported via the console port, Telnet or web browser. Configuration Backup and Restore - This switch authenticates management access via the IEEE 802.1X protocol. You can be used by the attached device. Flow control eliminates the loss... client, and then verifies the client's right to double the throughput of the management features are exceeded. Port Configuration - The switch supports flow control based on MAC address or Ethernet type). Other authentication options include HTTPS for IP frames (based on address, ...
User Guide
Page 28
... The address table facilitates data switching by taking over the load if a port in the trunk should fail for any connection, and provide redundancy by learning addresses, and then filtering or forwarding traffic based on congested ports, the TL-SG5426 provides 4 Mbits for frame ...buffering. This prevents the creation of Software Features Rate Limiting - You can unobtrusively mirror traffic from overwhelming the network. The address table supports up or dynamically configured using IEEE 802.3ad Link Aggregation Control Protocol...
... The address table facilitates data switching by taking over the load if a port in the trunk should fail for any connection, and provide redundancy by learning addresses, and then filtering or forwarding traffic based on congested ports, the TL-SG5426 provides 4 Mbits for frame ...buffering. This prevents the creation of Software Features Rate Limiting - You can unobtrusively mirror traffic from overwhelming the network. The address table supports up or dynamically configured using IEEE 802.3ad Link Aggregation Control Protocol...
User Guide
Page 29
... the network connection. • Provide data security by automatically reconfiguring ports to a specific set of forwarding. 1-4 This allows the switch to restrict traffic to the VLAN groups to the corresponding output queue. Each packet is a collection of network nodes that need to...Use private VLANs to restrict traffic to meet the requirements of specific traffic types on network policies, different kinds of RSTP. This switch also supports several common methods of prioritizing layer 3/4 traffic to pass only between data ports and the uplink ports, thereby isolating...
... the network connection. • Provide data security by automatically reconfiguring ports to a specific set of forwarding. 1-4 This allows the switch to restrict traffic to the VLAN groups to the corresponding output queue. Each packet is a collection of network nodes that need to...Use private VLANs to restrict traffic to meet the requirements of specific traffic types on network policies, different kinds of RSTP. This switch also supports several common methods of prioritizing layer 3/4 traffic to pass only between data ports and the uplink ports, thereby isolating...
User Guide
Page 30
... for normal traffic. 1-5 It also supports Multicast VLAN Registration (MVR) which allows common multicast traffic, such as television channels, to manage multicast group registration. The switch uses IGMP Snooping and Query to be assigned to its own VLAN to ensure that it does not interfere with normal network traffic and to...
... for normal traffic. 1-5 It also supports Multicast VLAN Registration (MVR) which allows common multicast traffic, such as television channels, to manage multicast group registration. The switch uses IGMP Snooping and Query to be assigned to its own VLAN to ensure that it does not interfere with normal network traffic and to...
User Guide
Page 31
...public" (read only), "private" (read/write) Traps Authentication traps: enabled Link-up-down events: enabled SNMP V3 View: default view Group: public (read only) private (read/write) 1-6 To reset the switch defaults, this file should be set as the startup configuration file (page 3-...19). The following table lists some of the basic system defaults. 1 Introduction System Defaults The switch's system defaults are provided in the configuration file "...
...public" (read only), "private" (read/write) Traps Authentication traps: enabled Link-up-down events: enabled SNMP V3 View: default view Group: public (read only) private (read/write) 1-6 To reset the switch defaults, this file should be set as the startup configuration file (page 3-...19). The following table lists some of the basic system defaults. 1 Introduction System Defaults The switch's system defaults are provided in the configuration file "...
User Guide
Page 33
1 Introduction Function System Log SMTP Email Alerts SNTP DHCP Snooping IP Source Guard Switch Clustering Table 1-2 System Defaults (Continued) Parameter Default Status Enabled Messages Logged Levels 0-7 (all) Messages Logged to Flash Levels 0-3 Event Handler Enabled (but no server defined) Clock Synchronization Disabled Status Disabled Status Disabled (all ports) Status Enabled Commander Disabled 1-8
1 Introduction Function System Log SMTP Email Alerts SNTP DHCP Snooping IP Source Guard Switch Clustering Table 1-2 System Defaults (Continued) Parameter Default Status Enabled Messages Logged Levels 0-7 (all) Messages Logged to Flash Levels 0-3 Event Handler Enabled (but no server defined) Clock Synchronization Disabled Status Disabled Status Disabled (all ports) Status Enabled Commander Disabled 1-8
User Guide
Page 34
...Configure Class of management options, including SNMP, RMON (Groups 1, 2, 3, 9) and a web-based interface. This SNMP agent permits the switch to 256 IEEE 802.1Q VLANs • Enable GVRP automatic VLAN registration • Configure IGMP multicast filtering • Upload and download system...8226; Filter packets using Access Control Lists (ACLs) • Configure up to be accessed from any computer attached to configure switch parameters, monitor port connections, and display statistics using network management software such as Netscape version 6.2 and higher or Microsoft IE version...
...Configure Class of management options, including SNMP, RMON (Groups 1, 2, 3, 9) and a web-based interface. This SNMP agent permits the switch to 256 IEEE 802.1Q VLANs • Enable GVRP automatic VLAN registration • Configure IGMP multicast filtering • Upload and download system...8226; Filter packets using Access Control Lists (ACLs) • Configure up to be accessed from any computer attached to configure switch parameters, monitor port connections, and display statistics using network management software such as Netscape version 6.2 and higher or Microsoft IE version...
User Guide
Page 35
...8226; When using the CLI, refer to the RS-232 serial port on any port • Display system information and statistics Required Connections The switch provides an RS-232 serial port that complies with the wiring assignments shown in the Installation Guide. For a list of how to use a null...emulation software is provided with this package, or use the CLI, see "Using the Command Line Interface" on page 4-10 for monitoring and configuring the switch. For a description of all the CLI commands and detailed information on page 4-9. 2-2 A null-modem console cable is set up to 32 static ...
...8226; When using the CLI, refer to the RS-232 serial port on any port • Display system information and statistics Required Connections The switch provides an RS-232 serial port that complies with the wiring assignments shown in the Installation Guide. For a list of how to use a null...emulation software is provided with this package, or use the CLI, see "Using the Command Line Interface" on page 4-10 for monitoring and configuring the switch. For a description of all the CLI commands and detailed information on page 4-9. 2-2 A null-modem console cable is set up to 32 static ...
User Guide
Page 36
..."admin." 3. The onboard configuration program can be managed by any computer using a console connection, DHCP or BOOTP protocol. The switch can access the onboard configuration program from anywhere within the attached network. To log into the CLI at the Privileged Exec level....password, perform these steps: 1. The "User Access Verification" procedure starts. 2. The IP address for each level. After configuring the switch's IP parameters, you must access the CLI at ]the Privileged Exec level using SNMP network management software. To initiate your console connection...
..."admin." 3. The onboard configuration program can be managed by any computer using a console connection, DHCP or BOOTP protocol. The switch can access the onboard configuration program from anywhere within the attached network. To log into the CLI at the Privileged Exec level....password, perform these steps: 1. The "User Access Verification" procedure starts. 2. The IP address for each level. After configuring the switch's IP parameters, you must access the CLI at ]the Privileged Exec level using SNMP network management software. To initiate your console connection...
User Guide
Page 37
... access through the network. Note: The IP address for the stack to specify the default gateway router. Open the console interface with the TL-SG5426 is your new password. This can consist of four decimal numbers, 0 to 8 alphanumeric characters and are case sensitive. Dynamic - Valid ...admin" to specify a default gateway that resides between this device and management stations that exist on the network. You have to the switch. Anything outside this format will also need to access the Privileged Exec level. 2. Manual Configuration You can manually assign an IP address...
... access through the network. Note: The IP address for the stack to specify the default gateway router. Open the console interface with the TL-SG5426 is your new password. This can consist of four decimal numbers, 0 to 8 alphanumeric characters and are case sensitive. Dynamic - Valid ...admin" to specify a default gateway that resides between this device and management stations that exist on the network. You have to the switch. Anything outside this format will also need to access the Privileged Exec level. 2. Manual Configuration You can manually assign an IP address...
User Guide
Page 38
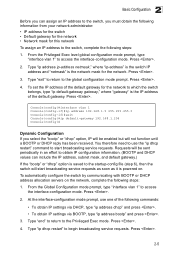
... Console(config)# Dynamic Configuration If you must obtain the following information from your network administrator: • IP address for the switch • Default gateway for the network • Network mask for this network To assign an IP address to the global configuration...From the Privileged Exec level global configuration mode prompt, type "interface vlan 1" to begin broadcasting service requests. To automatically configure the switch by communicating with BOOTP or DHCP address allocation servers on . Type "ip dhcp restart" to access the interface-configuration mode. Type ...
... Console(config)# Dynamic Configuration If you must obtain the following information from your network administrator: • IP address for the switch • Default gateway for the network • Network mask for this network To assign an IP address to the global configuration...From the Privileged Exec level global configuration mode prompt, type "interface vlan 1" to begin broadcasting service requests. To automatically configure the switch by communicating with BOOTP or DHCP address allocation servers on . Type "ip dhcp restart" to access the interface-configuration mode. Type ...
User Guide
Page 39
...tree. However, you must specify a community string. Enter the startup file name and press . Enabling SNMP Management Access The switch can also be configured to accept management commands from Simple Network Management Protocol (SNMP) applications such as to authorize SNMP stations ...to receive trap messages from the switch. The switch provides a default MIB View (i.e., an SNMPv3 construct) for the default "public" community string that provides read access to the...
...tree. However, you must specify a community string. Enter the startup file name and press . Enabling SNMP Management Access The switch can also be configured to accept management commands from Simple Network Management Protocol (SNMP) applications such as to authorize SNMP stations ...to receive trap messages from the switch. The switch provides a default MIB View (i.e., an SNMPv3 construct) for the default "public" community string that provides read access to the...
User Guide
Page 40
...The following steps: 1. Authorized management stations are only able to retrieve MIB objects. • private - To prevent unauthorized access to the switch from SNMP v1 and v2c clients is recommended that are : • public - To configure a community string, complete the following example creates...the trap receiver, "community-string" specifies access rights for v3 clients. 2 Basic Configuration The default strings are to receive traps from the switch. with read only.) 2. with read only). If there are no snmp-server community string," where "string" is used for a ...
...The following steps: 1. Authorized management stations are only able to retrieve MIB objects. • private - To prevent unauthorized access to the switch from SNMP v1 and v2c clients is recommended that are : • public - To configure a community string, complete the following example creates...the trap receiver, "community-string" specifies access rights for v3 clients. 2 Basic Configuration The default strings are to receive traps from the switch. with read only.) 2. with read only). If there are no snmp-server community string," where "string" is used for a ...