User Guide
Page 60
LAN Fax software is connected to users' PCs as a fixed form. • ■...Ricoh's, as the primary task of manually • re-entering address book entries is now automated. • ■ Transmission Status: Transmission results can be checked via Email: In addition to the inbound paperless fax to SAF/HDD, the Aficio MP 6001/MP 7001/ • MP 8001/MP... a designated folder on SP models) in one operation. • ■ Wireless Faxing: If the Aficio MP 6001/MP 7001/MP 8001/MP 9001 Series is available with the Printer/Scanner Unit Type 9001 and standard with the SP versions of paper...
LAN Fax software is connected to users' PCs as a fixed form. • ■...Ricoh's, as the primary task of manually • re-entering address book entries is now automated. • ■ Transmission Status: Transmission results can be checked via Email: In addition to the inbound paperless fax to SAF/HDD, the Aficio MP 6001/MP 7001/ • MP 8001/MP... a designated folder on SP models) in one operation. • ■ Wireless Faxing: If the Aficio MP 6001/MP 7001/MP 8001/MP 9001 Series is available with the Printer/Scanner Unit Type 9001 and standard with the SP versions of paper...
Operating Instructions
Page 8
Also explains how to change User Tools settings and how to prevent unauthorized use the software provided. Facsimile Reference Explains Facsimile functions and operations. Printer Reference Explains Printer functions and operations. It also explains the control panel, preparation procedures for resolving ...
Also explains how to change User Tools settings and how to prevent unauthorized use the software provided. Facsimile Reference Explains Facsimile functions and operations. Printer Reference Explains Printer functions and operations. It also explains the control panel, preparation procedures for resolving ...
Operating Instructions
Page 9
... using general names: Product name DeskTopBinder Lite and DeskTopBinder Professional *1 General name DeskTopBinder *1 Optional 7 PostScript 3 Supplement Explains how to read this machine. • The following software products are specific to machine types. • For "UNIX Supplement", please visit our Web site or consult an authorized dealer. Be sure to set up...
... using general names: Product name DeskTopBinder Lite and DeskTopBinder Professional *1 General name DeskTopBinder *1 Optional 7 PostScript 3 Supplement Explains how to read this machine. • The following software products are specific to machine types. • For "UNIX Supplement", please visit our Web site or consult an authorized dealer. Be sure to set up...
Operating Instructions
Page 106
5. Cause Solution Limits have been imposed Contact the administrator. Cause Solution The delivery software may be changed. See "Network Settings Required to the destinations for the broadcasting sequence, the data is set, and plain text e-mails are sent to ...
5. Cause Solution Limits have been imposed Contact the administrator. Cause Solution The delivery software may be changed. See "Network Settings Required to the destinations for the broadcasting sequence, the data is set, and plain text e-mails are sent to ...
Design Guide
Page 2
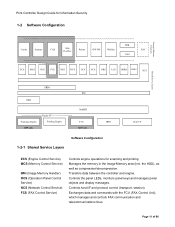
Internal System Configuration 7 1-1 Hardware Configuration 7 1-1-1 MFP ...7 1-1-2 LP ...9 1-2 Software Configuration 11 1-2-1 Shared Service Layers 11 1-2-2 Principal Machine Functions 12 1-3 Data Security ...14 1-3-1 External I/F ...14 1-3-2 Protection of Program Data from Illegal Access via an External ...
Internal System Configuration 7 1-1 Hardware Configuration 7 1-1-1 MFP ...7 1-1-2 LP ...9 1-2 Software Configuration 11 1-2-1 Shared Service Layers 11 1-2-2 Principal Machine Functions 12 1-3 Data Security ...14 1-3-1 External I/F ...14 1-3-2 Protection of Program Data from Illegal Access via an External ...
Design Guide
Page 6
... 1357 LD360 LD360sp LD370 LD370sp LD380 LD380sp LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX...machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific machine in question. external I/F) and functions described in this document may not be supported by...
... 1357 LD360 LD360sp LD370 LD370sp LD380 LD380sp LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX...machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific machine in question. external I/F) and functions described in this document may not be supported by...
Design Guide
Page 8
Page 8 of the software installed on the validity of 86 Print Controller Design Guide for Information Security • Serial communication between the external charge device I/F and external coin/card-...
Page 8 of the software installed on the validity of 86 Print Controller Design Guide for Information Security • Serial communication between the external charge device I/F and external coin/card-...
Design Guide
Page 10
Page 10 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes ...
Page 10 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes ...
Design Guide
Page 11
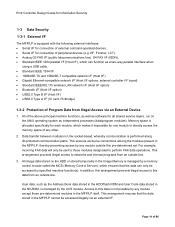
...) OCS (Operation Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS... Shared Service Layers SRM libc IMH Engine I/F Scanning Engine Printing Engine MFP only NetBSD FCU MFP only HDD Software Configuration 1-2-1 Shared Service Layers Host I /F and protocol control (transport, session). Manages the memory in the Image Memory area (incl.
...) OCS (Operation Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS... Shared Service Layers SRM libc IMH Engine I/F Scanning Engine Printing Engine MFP only NetBSD FCU MFP only HDD Software Configuration 1-2-1 Shared Service Layers Host I /F and protocol control (transport, session). Manages the memory in the Image Memory area (incl.
Design Guide
Page 14
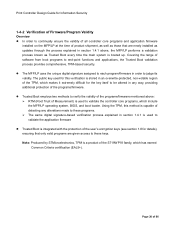
... external interfaces: • Serial I/F for connection of external coin/card-operated devices. • Serial I/F for connection of the above principal machine functions, as well as software for one module to directly access the memory space of 86 This arrangement prevents illegal access to perform FAX data operations. This ensures exclusive connections...
... external interfaces: • Serial I/F for connection of external coin/card-operated devices. • Serial I/F for connection of the above principal machine functions, as well as software for one module to directly access the memory space of 86 This arrangement prevents illegal access to perform FAX data operations. This ensures exclusive connections...
Design Guide
Page 20
... signature-based verification process explained in section 1.4.1 is used to validate the controller core programs, which has earned Common Criteria certification (EAL5+). Page 20 of software from boot programs to end-point functions and applications, the Trusted Boot validation process provides comprehensive, TPM-based security. Covering the range of 86 Trusted...
... signature-based verification process explained in section 1.4.1 is used to validate the controller core programs, which has earned Common Criteria certification (EAL5+). Page 20 of software from boot programs to end-point functions and applications, the Trusted Boot validation process provides comprehensive, TPM-based security. Covering the range of 86 Trusted...
Design Guide
Page 27
...activated on the HDD), the image data itself remains in the unlikely event that data reconstruction is not possible to the field as optional software stored on an SD card, renders this is removed from the MFP/LP, a third party would not be able to an indecipherable level...to access image data on the MFP/LP, a service or sales engineer must perform the setup procedure. National Security Agency The Ricoh randomized value method, a Ricoh-original method which method is selected, the more passes are made, the more indiscernible the original data becomes (although performing more passes...
...activated on the HDD), the image data itself remains in the unlikely event that data reconstruction is not possible to the field as optional software stored on an SD card, renders this is removed from the MFP/LP, a third party would not be able to an indecipherable level...to access image data on the MFP/LP, a service or sales engineer must perform the setup procedure. National Security Agency The Ricoh randomized value method, a Ricoh-original method which method is selected, the more passes are made, the more indiscernible the original data becomes (although performing more passes...
Design Guide
Page 55
...of 86 Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must be enabled at the PC side, the password necessary for changing the document's access level, and other cases, the MFP Scanner...the TWAIN V4 driver. In order to utilize the authentication features with the TWAIN V4 driver, the operator must first set the MFP or related software to enter a protection code whenever a destination folder stored in user performs a sending operation, this user does not have already been programmed in...
...of 86 Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must be enabled at the PC side, the password necessary for changing the document's access level, and other cases, the MFP Scanner...the TWAIN V4 driver. In order to utilize the authentication features with the TWAIN V4 driver, the operator must first set the MFP or related software to enter a protection code whenever a destination folder stored in user performs a sending operation, this user does not have already been programmed in...