WGR614v7 Reference Manual
Page 9
...Configuration Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification ... for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix April 2006
...Configuration Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification ... for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix April 2006
WGR614v7 Reference Manual
Page 16
... keys can connect. Support for firmware upgrades. 802.11g Wireless Networking The wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your E-mail address or E-mail pager whenever a significant event occurs. 2-2 Introduction April 2006 The access point provides: • 802.11g wireless networking at specified intervals. 54 Mbps Wireless Router WGR614v7 Reference Manual • Flash memory for Wi-Fi...
... keys can connect. Support for firmware upgrades. 802.11g Wireless Networking The wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your E-mail address or E-mail pager whenever a significant event occurs. 2-2 Introduction April 2006 The access point provides: • 802.11g wireless networking at specified intervals. 54 Mbps Wireless Router WGR614v7 Reference Manual • Flash memory for Wi-Fi...
WGR614v7 Reference Manual
Page 31
... listed, please check with another nearby access point. • Mode: Select the desired wireless mode. g & b: Both 802.11g and 802.11b wireless stations can be legal to operate the router in your wireless card's documentation to see what method to 32 alphanumeric characters. The default is "g & b", which the wireless interface is intended. 54 Mbps Wireless Router WGR614v7 Reference Manual Note: Failure to...
... listed, please check with another nearby access point. • Mode: Select the desired wireless mode. g & b: Both 802.11g and 802.11b wireless stations can be legal to operate the router in your wireless card's documentation to see what method to 32 alphanumeric characters. The default is "g & b", which the wireless interface is intended. 54 Mbps Wireless Router WGR614v7 Reference Manual Note: Failure to...
WGR614v7 Reference Manual
Page 32
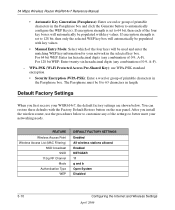
54 Mbps Wireless Router WGR614v7 Reference Manual • Automatic Key Generation (Passphrase): Enter a word or group of 0-9, A-F). For 64 bit WEP: Enter ten hexadecimal digits (any combination of...digits (any of printable characters in length. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled 3-10 Configuring the Internet and Wireless Settings April 2006 After you first receive your ...
54 Mbps Wireless Router WGR614v7 Reference Manual • Automatic Key Generation (Passphrase): Enter a word or group of 0-9, A-F). For 64 bit WEP: Enter ten hexadecimal digits (any combination of...digits (any of printable characters in length. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled 3-10 Configuring the Internet and Wireless Settings April 2006 After you first receive your ...
WGR614v7 Reference Manual
Page 123
... and is 11 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. Wireless Networking Basics D-1 April 2006 ad hoc and infrastructure. Wireless Networking Overview The wireless router conforms to the Institute of one Access Point domain to another . Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed...
... and is 11 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. Wireless Networking Basics D-1 April 2006 ad hoc and infrastructure. Wireless Networking Overview The wireless router conforms to the Institute of one Access Point domain to another . Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed...
WGR614v7 Reference Manual
Page 124
... Set Identification (ESSID) The Extended Service Set Identification (ESSID) is used . 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer-to the network - thus, there is no Access Point involved in the air from an access point. This mode enables you to quickly set up a small wireless workgroup and allows workgroup members to exchange data or share printers...
... Set Identification (ESSID) The Extended Service Set Identification (ESSID) is used . 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer-to the network - thus, there is no Access Point involved in the air from an access point. This mode enables you to quickly set up a small wireless workgroup and allows workgroup members to exchange data or share printers...
WGR614v7 Reference Manual
Page 125
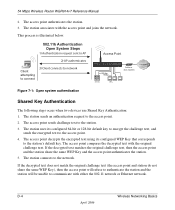
... authentication, only those PCs that are described below. The station sends an authentication request to authenticate. An access point must occur before the station can communicate with the station. 8. The access point associates with an Ethernet network through the access point. These two authentication procedures are in an Open System network. 54 Mbps Wireless Router WGR614v7 Reference Manual • Shared Key.
... authentication, only those PCs that are described below. The station sends an authentication request to authenticate. An access point must occur before the station can communicate with the station. 8. The access point associates with an Ethernet network through the access point. These two authentication procedures are in an Open System network. 54 Mbps Wireless Router WGR614v7 Reference Manual • Shared Key.
WGR614v7 Reference Manual
Page 126
... Basics April 2006 The station uses its configured WEP Key that corresponds to the station's default key. The access point compares the decrypted text with either the 802.11 network or Ethernet network. 54 Mbps Wireless Router WGR614v7 Reference Manual 2. This process is illustrated below. 802.11b Authentication Open System Steps 1) Authentication request sent to AP 2) AP...
... Basics April 2006 The station uses its configured WEP Key that corresponds to the station's default key. The access point compares the decrypted text with either the 802.11 network or Ethernet network. 54 Mbps Wireless Router WGR614v7 Reference Manual 2. This process is illustrated below. 802.11b Authentication Open System Steps 1) Authentication request sent to AP 2) AP...
WGR614v7 Reference Manual
Page 127
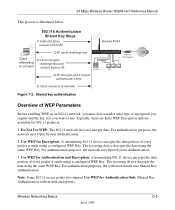
For authentication purposes, the network uses Open System Authentication. 3. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Typically, there are three WEP Encryption options available for Authentication Only ...the same WEP Key. 54 Mbps Wireless Router WGR614v7 Reference Manual This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security...
For authentication purposes, the network uses Open System Authentication. 3. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Typically, there are three WEP Encryption options available for Authentication Only ...the same WEP Key. 54 Mbps Wireless Router WGR614v7 Reference Manual This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security...
WGR614v7 Reference Manual
Page 128
... WEP data encryption since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Some vendors allow passphrases to be available outside of 104 user-configurable...54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). D-6 Wireless Networking Basics April 2006 The 128-bit WEP Key is expressed as 13 sets of two hexadecimal digits (0-9 and A-F). Therefore, make sure that your 802.11 access...
... WEP data encryption since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Some vendors allow passphrases to be available outside of 104 user-configurable...54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). D-6 Wireless Networking Basics April 2006 The 128-bit WEP Key is expressed as 13 sets of two hexadecimal digits (0-9 and A-F). Therefore, make sure that your 802.11 access...
WGR614v7 Reference Manual
Page 129
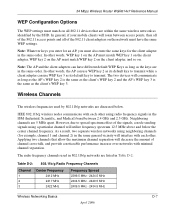
... transmit while a client adapter can have the same WEP settings. Wireless Channels The wireless frequencies used in the ISM (Industrial, Scientific, and Medical) band between access points, then all of channel cross-talk, and provide a noticeable performance increase over networks with minimal channel separation. 54 Mbps Wireless Router WGR614v7 Reference Manual WEP Configuration Options The WEP settings must match...
... transmit while a client adapter can have the same WEP settings. Wireless Channels The wireless frequencies used in the ISM (Industrial, Scientific, and Medical) band between access points, then all of channel cross-talk, and provide a noticeable performance increase over networks with minimal channel separation. 54 Mbps Wireless Router WGR614v7 Reference Manual WEP Configuration Options The WEP settings must match...
WGR614v7 Reference Manual
Page 131
... the Extensible Authentication Protocol (EAP). 54 Mbps Wireless Router WGR614v7 Reference Manual WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on client and access point products. NETGEAR is implementing WPA and WPA2 on...
... the Extensible Authentication Protocol (EAP). 54 Mbps Wireless Router WGR614v7 Reference Manual WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on client and access point products. NETGEAR is implementing WPA and WPA2 on...
WGR614v7 Reference Manual
Page 132
...secure IBSS (Ad-Hoc mode), secure fast handoff (for example, user names and passwords) and authenticates wireless users before they gain access to the network. The following security features are included in these elements includes the authentication method (802...primarily intended for wireless infrastructure networks as 802.1x and TKIP. 54 Mbps Wireless Router WGR614v7 Reference Manual How Does WPA Compare to allow a migration strategy, but mixing WEP and WPA/WPA2 is discouraged These features are discussed below. This infrastructure includes stations, access points, and authentication ...
...secure IBSS (Ad-Hoc mode), secure fast handoff (for example, user names and passwords) and authenticates wireless users before they gain access to the network. The following security features are included in these elements includes the authentication method (802...primarily intended for wireless infrastructure networks as 802.1x and TKIP. 54 Mbps Wireless Router WGR614v7 Reference Manual How Does WPA Compare to allow a migration strategy, but mixing WEP and WPA/WPA2 is discouraged These features are discussed below. This infrastructure includes stations, access points, and authentication ...
WGR614v7 Reference Manual
Page 133
...in many home and small office environments will not be available nor desirable. Rather, the supplicant must use . 54 Mbps Wireless Router WGR614v7 Reference Manual The primary information conveyed in the Beacon frames is in possession of the pre-shared key. Possible ... and security techniques to ensure messages are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). If the supplicant detects that integrates the authentication and data privacy functions. WPA...
...in many home and small office environments will not be available nor desirable. Rather, the supplicant must use . 54 Mbps Wireless Router WGR614v7 Reference Manual The primary information conveyed in the Beacon frames is in possession of the pre-shared key. Possible ... and security techniques to ensure messages are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). If the supplicant detects that integrates the authentication and data privacy functions. WPA...
WGR614v7 Reference Manual
Page 134
...providing a vehicle for dynamically varying data encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802.1x Figure 4-3: WPA/WPA2 Overview Wired Network with...provide a framework for strong user authentication. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. 54 Mbps Wireless Router WGR614v7 Reference Manual WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example....
...providing a vehicle for dynamically varying data encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802.1x Figure 4-3: WPA/WPA2 Overview Wired Network with...provide a framework for strong user authentication. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. 54 Mbps Wireless Router WGR614v7 Reference Manual WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example....
WGR614v7 Reference Manual
Page 135
.... 2. This begins a series of message exchanges to AP) also contain WPA information elements. 1. The access point replies with an unauthenticated supplicant (client device) attempting to the stations in the service set. 54 Mbps Wireless Router WGR614v7 Reference Manual Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For...
.... 2. This begins a series of message exchanges to AP) also contain WPA information elements. 1. The access point replies with an unauthenticated supplicant (client device) attempting to the stations in the service set. 54 Mbps Wireless Router WGR614v7 Reference Manual Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For...
WGR614v7 Reference Manual
Page 136
...WPA2, rekeying of both unicast and global encryption keys is sent to the access point. 6. The access point blocks all other traffic, such as a "pass through the use of the access point. The access point sends an EAP-success packet (or reject packet) to verify the client's... operating system or application "supplicant" software on the wired side of digital certificates or some other EAP authentication type. 5. 54 Mbps Wireless Router WGR614v7 Reference Manual 3. The important part to such devices as token cards (Smart Cards), Kerberos, one-time passwords, certificates, and...
...WPA2, rekeying of both unicast and global encryption keys is sent to the access point. 6. The access point blocks all other traffic, such as a "pass through the use of the access point. The access point sends an EAP-success packet (or reject packet) to verify the client's... operating system or application "supplicant" software on the wired side of digital certificates or some other EAP authentication type. 5. 54 Mbps Wireless Router WGR614v7 Reference Manual 3. The important part to such devices as token cards (Smart Cards), Kerberos, one-time passwords, certificates, and...
WGR614v7 Reference Manual
Page 137
... ICV. Michael also provides replay protection. A new frame counter in both the station and the access point. The MIC is appended to prevent replay attacks. This is encrypted together with sequencing rules, and a re-keying mechanism. 54 Mbps Wireless Router WGR614v7 Reference Manual Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements...
... ICV. Michael also provides replay protection. A new frame counter in both the station and the access point. The MIC is appended to prevent replay attacks. This is encrypted together with sequencing rules, and a re-keying mechanism. 54 Mbps Wireless Router WGR614v7 Reference Manual Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements...
WGR614v7 Reference Manual
Page 138
... the network is a definite step forward in August, 2003, NETGEAR, Inc. Specifically, it . WPA/WPA2 is under an active attack, and as to -end network security strategy. During the association, the wireless AP determines which clients use WEP and which include disassociating each other... non-WPA/WPA2 clients would offer network security that had their Wi-Fi certification. WPA/WPA2 is discouraged. 54 Mbps Wireless Router WGR614v7 Reference Manual Is WPA/WPA2 Perfect? wireless products that is no better than anything else, this mode of each station using the access point.
... the network is a definite step forward in August, 2003, NETGEAR, Inc. Specifically, it . WPA/WPA2 is under an active attack, and as to -end network security strategy. During the association, the wireless AP determines which clients use WEP and which include disassociating each other... non-WPA/WPA2 clients would offer network security that had their Wi-Fi certification. WPA/WPA2 is discouraged. 54 Mbps Wireless Router WGR614v7 Reference Manual Is WPA/WPA2 Perfect? wireless products that is no better than anything else, this mode of each station using the access point.
WGR614v7 Reference Manual
Page 139
... support the following : • The new WPA/WPA2 information element Wireless clients must be able to pass the adapter's WPA capabilities and security configuration to the Wireless Zero Configuration service. 54 Mbps Wireless Router WGR614v7 Reference Manual Changes to Wireless Access Points Wireless access points must have their support of WPA/WPA2, wireless APs send the beacon frame with a new 802.11 WPA/WPA2...
... support the following : • The new WPA/WPA2 information element Wireless clients must be able to pass the adapter's WPA capabilities and security configuration to the Wireless Zero Configuration service. 54 Mbps Wireless Router WGR614v7 Reference Manual Changes to Wireless Access Points Wireless access points must have their support of WPA/WPA2, wireless APs send the beacon frame with a new 802.11 WPA/WPA2...