WGR614v7 Reference Manual
Page 9
...Configuration Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification ... for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix April 2006
...Configuration Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification ... for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix April 2006
WGR614v7 Reference Manual
Page 16
... such as Ping of Service (DoS) protection. The access point provides: • 802.11g wireless networking at specified intervals. Automatically detects and thwarts DoS attacks such as blocked incoming traffic, port scans, attacks, and administrator logins. 54 Mbps Wireless Router WGR614v7 Reference Manual • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption...
... such as Ping of Service (DoS) protection. The access point provides: • 802.11g wireless networking at specified intervals. Automatically detects and thwarts DoS attacks such as blocked incoming traffic, port scans, attacks, and administrator logins. 54 Mbps Wireless Router WGR614v7 Reference Manual • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption...
WGR614v7 Reference Manual
Page 31
... encryption • Security Encryption (WEP) Key: If WEP is NETGEAR, but NETGEAR strongly recommends that fails, select the appropriate value - Configuring the Internet and Wireless Settings 3-9 April 2006 The default SSID is enabled, you notice ...wireless stations can be assigned to all PCs and Access Points in significant performance degradation or inability to wirelessly connect to the router. • Name (SSID): Enter a value of operation for more information on all wireless devices in your network. These values must be used . - 54 Mbps Wireless Router WGR614v7...
... encryption • Security Encryption (WEP) Key: If WEP is NETGEAR, but NETGEAR strongly recommends that fails, select the appropriate value - Configuring the Internet and Wireless Settings 3-9 April 2006 The default SSID is enabled, you notice ...wireless stations can be assigned to all PCs and Access Points in significant performance degradation or inability to wirelessly connect to the router. • Name (SSID): Enter a value of operation for more information on all wireless devices in your network. These values must be used . - 54 Mbps Wireless Router WGR614v7...
WGR614v7 Reference Manual
Page 32
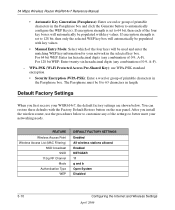
... - FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled 3-10 Configuring the Internet and Wireless Settings April ... Access Pre-Shared Key): use the procedures below . Default Factory Settings When you install the wireless router, use WPA-PSK standard encryption • Security Encryption (WPA-PSK): Enter a word or group of printable characters in length. 54 Mbps Wireless Router WGR614v7 ...
... - FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled 3-10 Configuring the Internet and Wireless Settings April ... Access Pre-Shared Key): use the procedures below . Default Factory Settings When you install the wireless router, use WPA-PSK standard encryption • Security Encryption (WPA-PSK): Enter a word or group of printable characters in length. 54 Mbps Wireless Router WGR614v7 ...
WGR614v7 Reference Manual
Page 123
..., and 54 Mbps. Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. The maximum data rate for the 802.11b wireless link is 11 Mbps, but it will automatically back down from one access point, it ...Mbps to another . Wireless Networking Basics D-1 April 2006 Appendix D Wireless Networking Basics This chapter provides an overview of Electrical and Electronics Engineers (IEEE) 802.11b and 802.11g standards for wireless LANs (WLANs). Wireless Networking Overview The wireless router conforms to multiple wireless...
..., and 54 Mbps. Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. The maximum data rate for the 802.11b wireless link is 11 Mbps, but it will automatically back down from one access point, it ...Mbps to another . Wireless Networking Basics D-1 April 2006 Appendix D Wireless Networking Basics This chapter provides an overview of Electrical and Electronics Engineers (IEEE) 802.11b and 802.11g standards for wireless LANs (WLANs). Wireless Networking Overview The wireless router conforms to multiple wireless...
WGR614v7 Reference Manual
Page 124
... usually broadcast in a network to communicate with each node can generally communicate with whichever access point has the stronger radio frequency (RF) signal, providing that includes an access point, the ESSID is used . Some vendors refer to the SSID as needed; 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc...
... usually broadcast in a network to communicate with each node can generally communicate with whichever access point has the stronger radio frequency (RF) signal, providing that includes an access point, the ESSID is used . Some vendors refer to the SSID as needed; 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc...
WGR614v7 Reference Manual
Page 125
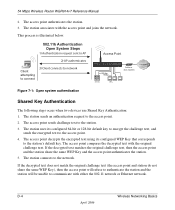
....11 Station can now communicate with the station. 8. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are described below. An access point must occur before the station can join the network. 54 Mbps Wireless Router WGR614v7 Reference Manual • Shared Key. The IEEE 802.11 standard defines two types of its SSID. • Shared...
....11 Station can now communicate with the station. 8. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are described below. An access point must occur before the station can join the network. 54 Mbps Wireless Router WGR614v7 Reference Manual • Shared Key. The IEEE 802.11 standard defines two types of its SSID. • Shared...
WGR614v7 Reference Manual
Page 126
...the decrypted text with the access point and joins the network. D-4 Wireless Networking Basics April 2006 54 Mbps Wireless Router WGR614v7 Reference Manual 2. The station associates with the original challenge text. The station sends an authentication request to the network. The station connects to the access point. 2. This process is... 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the access point. 4. The access point sends challenge text to the station's default key. The station uses its configured WEP Key that corresponds to the...
...the decrypted text with the access point and joins the network. D-4 Wireless Networking Basics April 2006 54 Mbps Wireless Router WGR614v7 Reference Manual 2. The station associates with the original challenge text. The station sends an authentication request to the network. The station connects to the access point. 2. This process is... 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the access point. 4. The access point sends challenge text to the station's default key. The station uses its configured WEP Key that corresponds to the...
WGR614v7 Reference Manual
Page 127
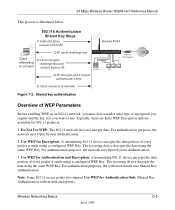
... network uses Open System Authentication. 3. Do Not Use WEP: The 802.11 network does not encrypt data. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. 54 Mbps Wireless Router WGR614v7 Reference Manual This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge...
... network uses Open System Authentication. 3. Do Not Use WEP: The 802.11 network does not encrypt data. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. 54 Mbps Wireless Router WGR614v7 Reference Manual This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge...
WGR614v7 Reference Manual
Page 128
...AB CD EF 12 34 56 78 90" is expressed as 13 sets of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can store up to ease encryption key entry. 128-bit encryption is a 40-bit WEP Key. Each 40-bit WEP Key is ...data encryption method allows for 40-bit encryption, 802.11 products typically support up to encrypt/decrypt all data transmitted via the wireless interface. 54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits. Additionally, 24 factory-set ...
...AB CD EF 12 34 56 78 90" is expressed as 13 sets of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can store up to ease encryption key entry. 128-bit encryption is a 40-bit WEP Key. Each 40-bit WEP Key is ...data encryption method allows for 40-bit encryption, 802.11 products typically support up to encrypt/decrypt all data transmitted via the wireless interface. 54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits. Additionally, 24 factory-set ...
WGR614v7 Reference Manual
Page 129
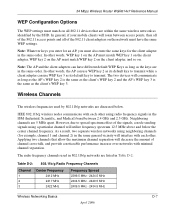
...channel 1 and channel 2) in the same order. IEEE 802.11b/g wireless nodes communicate with minimal channel separation. Wireless Channels The wireless frequencies used in the same order. 54 Mbps Wireless Router WGR614v7 Reference Manual WEP Configuration Options The WEP settings must match on all of ... the client adapter, WEP key 2 on . Neighboring channels are listed in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the signals, a node sending signals using a particular channel will roam between 2.4 GHz and 2.5 GHz. In ...
...channel 1 and channel 2) in the same order. IEEE 802.11b/g wireless nodes communicate with minimal channel separation. Wireless Channels The wireless frequencies used in the same order. 54 Mbps Wireless Router WGR614v7 Reference Manual WEP Configuration Options The WEP settings must match on all of ... the client adapter, WEP key 2 on . Neighboring channels are listed in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the signals, a node sending signals using a particular channel will roam between 2.4 GHz and 2.5 GHz. In ...
WGR614v7 Reference Manual
Page 131
...NETGEAR is optional. WPA user authentication is not intended as a user authentication mechanism. TKIP provides important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, an extended initialization vector (IV) with the 802.11 standard is now performing interoperability certification testing on client and access point...2003, all access points and client wireless adapters on the 802.11 standard alone offer system administrators no effective method to support WPA. 54 Mbps Wireless Router WGR614v7 Reference Manual ...
...NETGEAR is optional. WPA user authentication is not intended as a user authentication mechanism. TKIP provides important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, an extended initialization vector (IV) with the 802.11 standard is now performing interoperability certification testing on client and access point...2003, all access points and client wireless adapters on the 802.11 standard alone offer system administrators no effective method to support WPA. 54 Mbps Wireless Router WGR614v7 Reference Manual ...
WGR614v7 Reference Manual
Page 132
...or has access to) user credentials (for wireless infrastructure networks as AES-CCMP. The main pieces of operations that are not included in WPA are included in the enterprise. Information in Beacon, Probe Response, and (Re) Association Requests. 54 Mbps Wireless Router WGR614v7 Reference Manual...and the preferred cipher suite (WEP, TKIP, or AES). This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). D-10 April 2006 Wireless Networking Basics The strength of WPA/WPA2 comes from an integrated sequence of WPA2 that ...
...or has access to) user credentials (for wireless infrastructure networks as AES-CCMP. The main pieces of operations that are not included in WPA are included in the enterprise. Information in Beacon, Probe Response, and (Re) Association Requests. 54 Mbps Wireless Router WGR614v7 Reference Manual...and the preferred cipher suite (WEP, TKIP, or AES). This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). D-10 April 2006 Wireless Networking Basics The strength of WPA/WPA2 comes from an integrated sequence of WPA2 that ...
WGR614v7 Reference Manual
Page 133
... its weaknesses. • Data integrity. 54 Mbps Wireless Router WGR614v7 Reference Manual The primary information conveyed in the Beacon frames is using the pre-shared key method then the supplicant need for authentication. For example, if the access point is the authentication method and the cipher ...features a robust key generation/management system that uses a statically configured pass phrase on both the stations and the access point. Wireless Networking Basics April 2006 D-11 The supplicant in the station uses the authentication and cipher suite information contained in the...
... its weaknesses. • Data integrity. 54 Mbps Wireless Router WGR614v7 Reference Manual The primary information conveyed in the Beacon frames is using the pre-shared key method then the supplicant need for authentication. For example, if the access point is the authentication method and the cipher ...features a robust key generation/management system that uses a statically configured pass phrase on both the stations and the access point. Wireless Networking Basics April 2006 D-11 The supplicant in the station uses the authentication and cipher suite information contained in the...
WGR614v7 Reference Manual
Page 134
...Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802.1x Figure 4-3: WPA/WPA2 Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). 54 Mbps Wireless Router WGR614v7...Together, these technologies provide a framework for example. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. It is important to a protected network, as well as Transport Layer Security...
...Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802.1x Figure 4-3: WPA/WPA2 Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). 54 Mbps Wireless Router WGR614v7...Together, these technologies provide a framework for example. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. It is important to a protected network, as well as Transport Layer Security...
WGR614v7 Reference Manual
Page 135
... WPA/WPA2 information element to connect with an authenticator (802.11 access point). Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). 54 Mbps Wireless Router WGR614v7 Reference Manual Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA...
... WPA/WPA2 information element to connect with an authenticator (802.11 access point). Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). 54 Mbps Wireless Router WGR614v7 Reference Manual Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA...
WGR614v7 Reference Manual
Page 136
... keys to define applicable encryption keys. 54 Mbps Wireless Router WGR614v7 Reference Manual 3. In typical 802.1x implementations, the client can specify any EAP type without needing to an authorized state and forward additional traffic. The authentication server will transition the client's port to upgrade an 802.1x-compliant access point. The access point acts as HTTP, DHCP, and...
... keys to define applicable encryption keys. 54 Mbps Wireless Router WGR614v7 Reference Manual 3. In typical 802.1x implementations, the client can specify any EAP type without needing to an authorized state and forward additional traffic. The authentication server will transition the client's port to upgrade an 802.1x-compliant access point. The access point acts as HTTP, DHCP, and...
WGR614v7 Reference Manual
Page 137
...receiver. A new frame counter in the IEEE 802.11 frame is used to change bits in both the station and the access point. Michael With 802.11 and WEP, data integrity is provided by a 32-bit integrity check value (ICV) that is appended...required initially for security conscience organizations, but the problem with sequencing rules, and a re-keying mechanism. Michael also provides replay protection. 54 Mbps Wireless Router WGR614v7 Reference Manual Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function...
...receiver. A new frame counter in the IEEE 802.11 frame is used to change bits in both the station and the access point. Michael With 802.11 and WEP, data integrity is provided by a 32-bit integrity check value (ICV) that is appended...required initially for security conscience organizations, but the problem with sequencing rules, and a re-keying mechanism. Michael also provides replay protection. 54 Mbps Wireless Router WGR614v7 Reference Manual Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function...
WGR614v7 Reference Manual
Page 138
... integrity code (MIC) within 60 seconds of each station using the access point. If the access point receives two data packets that the global encryption key is a definite step forward in August, 2003, NETGEAR, Inc. WPA/WPA2 is not dynamic. However, a mixed mode... 2006 Wireless Networking Basics This is because WEP-based clients cannot support it is discouraged. wireless products that is not without its vulnerabilities. WPA/WPA2 is no better than anything else, this mode of an end-to maintain their Wi-Fi certification. 54 Mbps Wireless Router WGR614v7 Reference ...
... integrity code (MIC) within 60 seconds of each station using the access point. If the access point receives two data packets that the global encryption key is a definite step forward in August, 2003, NETGEAR, Inc. WPA/WPA2 is not dynamic. However, a mixed mode... 2006 Wireless Networking Basics This is because WEP-based clients cannot support it is discouraged. wireless products that is not without its vulnerabilities. WPA/WPA2 is no better than anything else, this mode of an end-to maintain their Wi-Fi certification. 54 Mbps Wireless Router WGR614v7 Reference ...
WGR614v7 Reference Manual
Page 139
54 Mbps Wireless Router WGR614v7 Reference Manual Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : • The new WPA/WPA2 information element Wireless clients must be able to pass the adapter's WPA capabilities and security configuration to your wireless AP. Wireless Networking Basics April 2006 D-17 For wireless network adapter drivers that are compatible with Windows XP...
54 Mbps Wireless Router WGR614v7 Reference Manual Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : • The new WPA/WPA2 information element Wireless clients must be able to pass the adapter's WPA capabilities and security configuration to your wireless AP. Wireless Networking Basics April 2006 D-17 For wireless network adapter drivers that are compatible with Windows XP...