DG834G Original Reference Manual
Page 164
...Wireless Networking Basics Temporal Key Integrity Protocol (TKIP) - The main pieces of WPA Security? Michael message integrity code (MIC) - This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination. What are the Key...8226; WPA Encryption Key Management - These features are either not yet ready for market or will be phased in WPA are ready to bring to the network. Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model ...
...Wireless Networking Basics Temporal Key Integrity Protocol (TKIP) - The main pieces of WPA Security? Michael message integrity code (MIC) - This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination. What are the Key...8226; WPA Encryption Key Management - These features are either not yet ready for market or will be phased in WPA are ready to bring to the network. Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model ...
DG834G Original Reference Manual
Page 170
...lose network connectivity for 60 seconds. NETGEAR, Inc. WPA is a definite step forward in August, 2003, NETGEAR, Inc. More than that fail the message integrity code (MIC) within 60 seconds of WPA and WEP Wireless ...Wireless 802.11g Firewall/Print Server Model FWG114P Is WPA Perfect? WPA requires software changes to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture of each station using the access point. D-16 Wireless Networking Basics Reference Manual for WPA Starting in WLAN security...
...lose network connectivity for 60 seconds. NETGEAR, Inc. WPA is a definite step forward in August, 2003, NETGEAR, Inc. More than that fail the message integrity code (MIC) within 60 seconds of WPA and WEP Wireless ...Wireless 802.11g Firewall/Print Server Model FWG114P Is WPA Perfect? WPA requires software changes to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture of each station using the access point. D-16 Wireless Networking Basics Reference Manual for WPA Starting in WLAN security...
DG834Gv2 Reference Manual
Page 120
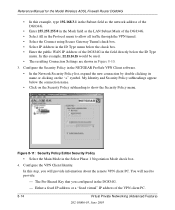
... Key that you will need to provide: - Either a fixed IP address or a "fixed virtual" IP address of the DG834G in the field directly below the connection name. • Click on the "+" symbol. Reference Manual for the Model Wireless ADSL Firewall Router DG834G • In this step, you configured in the NETGEAR ProSafe VPN Client software. • In the Network Security...
... Key that you will need to provide: - Either a fixed IP address or a "fixed virtual" IP address of the DG834G in the field directly below the connection name. • Click on the "+" symbol. Reference Manual for the Model Wireless ADSL Firewall Router DG834G • In this step, you configured in the NETGEAR ProSafe VPN Client software. • In the Network Security...
DG834Gv2 Reference Manual
Page 121
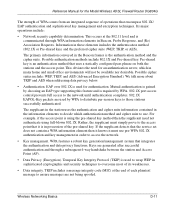
...Wireless ADSL Firewall Router DG834G • In the Network Security Policy list on the left side of the Security Policy Editor window, click on My Identity. You may also choose Any if you will be switching between adapters or if you use to access the Internet. Figure 8-13: Security Policy Editor Pre-Shared Key Virtual Private Networking... Type menu. Enter the DG834G's Pre-Shared Key and click OK. This field is entered. Figure 8-12: Security Policy Editor My Identity • Choose None in the Select Certificate menu. • Select IP Address in the Internal Network IP Address box. In ...
...Wireless ADSL Firewall Router DG834G • In the Network Security Policy list on the left side of the Security Policy Editor window, click on My Identity. You may also choose Any if you will be switching between adapters or if you use to access the Internet. Figure 8-13: Security Policy Editor Pre-Shared Key Virtual Private Networking... Type menu. Enter the DG834G's Pre-Shared Key and click OK. This field is entered. Figure 8-12: Security Policy Editor My Identity • Choose None in the Select Certificate menu. • Select IP Address in the Internal Network IP Address box. In ...
DG834Gv2 Reference Manual
Page 122
... 3DES) to be used for this connection. Configure the VPN Client Key Exchange Proposal. Figure 8-14: Security Policy Editor Authentication • In the Authentication Method menu, select Pre-Shared key. • In the Encrypt Alg menu, select the type of ...for the Model Wireless ADSL Firewall Router DG834G 5. Then select Proposal 1 below Authentication. Reference Manual for the Encryption Protocol in the DG834G in the DG834G configuration. • In the Network Security Policy list on the left side of the Security Policy Editor window, expand the Security Policy heading by ...
... 3DES) to be used for this connection. Configure the VPN Client Key Exchange Proposal. Figure 8-14: Security Policy Editor Authentication • In the Authentication Method menu, select Pre-Shared key. • In the Encrypt Alg menu, select the type of ...for the Model Wireless ADSL Firewall Router DG834G 5. Then select Proposal 1 below Authentication. Reference Manual for the Encryption Protocol in the DG834G in the DG834G configuration. • In the Network Security Policy list on the left side of the Security Policy Editor window, expand the Security Policy heading by ...
DG834Gv2 Reference Manual
Page 215
.... Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). Temporal Key Integrity Protocol (TKIP) is using full-blown 802.1X. Its major operations include: • Network security capability determination. Keys are not being spoofed. Reference Manual for the Model Wireless ADSL Firewall Router DG834G The strength of WPA comes from an integrated sequence of each plaintext message...
.... Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). Temporal Key Integrity Protocol (TKIP) is using full-blown 802.1X. Its major operations include: • Network security capability determination. Keys are not being spoofed. Reference Manual for the Model Wireless ADSL Firewall Router DG834G The strength of WPA comes from an integrated sequence of each plaintext message...
DG834Gv2 Reference Manual
Page 220
... in August, 2003, NETGEAR, Inc. Product Support for the Model Wireless ADSL Firewall Router DG834G Is WPA Perfect? Reference Manual for WPA Starting in WLAN security over WEP and has to be thought of an end-to lose network connectivity for 60 seconds. If the access point receives two data packets that the global encryption key is not without...
... in August, 2003, NETGEAR, Inc. Product Support for the Model Wireless ADSL Firewall Router DG834G Is WPA Perfect? Reference Manual for WPA Starting in WLAN security over WEP and has to be thought of an end-to lose network connectivity for 60 seconds. If the access point receives two data packets that the global encryption key is not without...
DG834Gv2 Reference Manual
Page 255
...Key dialog box, click the Enter Key button. In the Network Security Policy list on the left side of encryption (DES or 3DES) to be used for the Model Wireless ADSL Firewall Router DG834G e. In this step, you will provide the type of the Security Policy Editor window, expand the Security...the VPN router configuration. Reference Manual for this connection. a. Configure the VPN Client Authentication Proposal. Enter the DG834G's Pre-Shared Key and click OK. This field is entered. NETGEAR VPN Configuration 202-10006-05, June 2005 F-21 Figure F-19: Security Policy ...
...Key dialog box, click the Enter Key button. In the Network Security Policy list on the left side of encryption (DES or 3DES) to be used for the Model Wireless ADSL Firewall Router DG834G e. In this step, you will provide the type of the Security Policy Editor window, expand the Security...the VPN router configuration. Reference Manual for this connection. a. Configure the VPN Client Authentication Proposal. Enter the DG834G's Pre-Shared Key and click OK. This field is entered. NETGEAR VPN Configuration 202-10006-05, June 2005 F-21 Figure F-19: Security Policy ...
DG834Gv4 Reference Manual
Page 98
...the VPN client PC. If you use to access the Internet. d. You must provide the pre-shared key that you have only one adapter, select Any. 6-12 v2.0, September 2007 Virtual Private Networking Figure 6-11 b. Select IP Address in the Name field. If you configured in the Internal... adapter. If you will be switching between adapters or if you provide information about the remote VPN client PC. a. ADSL2+ Modem Wireless Router DG834G Reference Manual c. In the Select Phase 1 Negotiation Mode section of the Security Policy Editor window, click My Identity.
...the VPN client PC. If you use to access the Internet. d. You must provide the pre-shared key that you have only one adapter, select Any. 6-12 v2.0, September 2007 Virtual Private Networking Figure 6-11 b. Select IP Address in the Name field. If you configured in the Internal... adapter. If you will be switching between adapters or if you provide information about the remote VPN client PC. a. ADSL2+ Modem Wireless Router DG834G Reference Manual c. In the Select Phase 1 Negotiation Mode section of the Security Policy Editor window, click My Identity.
DG834Gv4 Reference Manual
Page 99
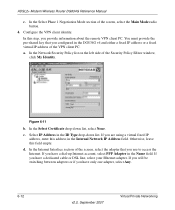
.... Figure 6-13 Virtual Private Networking v2.0, September 2007 6-13 ADSL2+ Modem Wireless Router DG834G Reference Manual e. In this step, you provide the type of the screen, click the Pre-Shared Key button. This field is entered. In the Network Security Policy list on the left side of the Security Policy Editor window, expand the Security Policy heading by double...
.... Figure 6-13 Virtual Private Networking v2.0, September 2007 6-13 ADSL2+ Modem Wireless Router DG834G Reference Manual e. In this step, you provide the type of the screen, click the Pre-Shared Key button. This field is entered. In the Network Security Policy list on the left side of the Security Policy Editor window, expand the Security Policy heading by double...
DG834Gv4 Reference Manual
Page 160
..., 12345678 is case-sensitive. B-18 v2.0, September 2007 NETGEAR VPN Configuration c. Enter the DG834G v4's pre-shared key and click OK. In the Network Security Policy list on the left side of the Security Policy Editor window, click My Identity. Select None in ...Network Connection (in this example, your Ethernet adapter might be different) in the Name field, and then enter 192.168.2.3 (in this example). ADSL2+ Modem Wireless Router DG834G Reference Manual a. Select Disabled in the IP Addr field. Figure B-20 f. This field is entered. Figure B-19 b. In the Pre-Shared Key...
..., 12345678 is case-sensitive. B-18 v2.0, September 2007 NETGEAR VPN Configuration c. Enter the DG834G v4's pre-shared key and click OK. In the Network Security Policy list on the left side of the Security Policy Editor window, click My Identity. Select None in ...Network Connection (in this example, your Ethernet adapter might be different) in the Name field, and then enter 192.168.2.3 (in this example). ADSL2+ Modem Wireless Router DG834G Reference Manual a. Select Disabled in the IP Addr field. Figure B-20 f. This field is entered. Figure B-19 b. In the Pre-Shared Key...
DG834Gv4 Reference Manual
Page 161
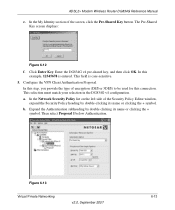
...NETGEAR VPN Configuration v2.0, September 2007 B-19 In this step, you provide the type of the Security Policy Editor window, expand the Security Policy heading by double clicking its name or clicking the + symbol. In the Network Security... Policy list on the left side of encryption (DES or 3DES) to be used for this connection. g. This selection must match your selection in the VPN router configuration. In this connection. In the Key...match your selection in the VPN router configuration. ADSL2+ Modem Wireless Router DG834G Reference Manual 5. b.
...NETGEAR VPN Configuration v2.0, September 2007 B-19 In this step, you provide the type of the Security Policy Editor window, expand the Security Policy heading by double clicking its name or clicking the + symbol. In the Network Security... Policy list on the left side of encryption (DES or 3DES) to be used for this connection. g. This selection must match your selection in the VPN router configuration. In this connection. In the Key...match your selection in the VPN router configuration. ADSL2+ Modem Wireless Router DG834G Reference Manual 5. b.
DG834Gv5 Reference Manual
Page 106
... ID Type drop-down list. My Identity and Security Policy subheadings appear below the ID Type drop-down list. Wireless ADSL2+ Modem Router DG834G User Manual e. In the Select Phase 1 Negotiation Mode section of the VPN client PC. 6-12 v1.0, May 2008 Virtual Private Networking In the Network Security Policy list, expand the new connection by double...
... ID Type drop-down list. My Identity and Security Policy subheadings appear below the ID Type drop-down list. Wireless ADSL2+ Modem Router DG834G User Manual e. In the Select Phase 1 Negotiation Mode section of the VPN client PC. 6-12 v1.0, May 2008 Virtual Private Networking In the Network Security Policy list, expand the new connection by double...
DG834Gv5 Reference Manual
Page 107
In the Network Security Policy list on the left side of the screen, click the Pre-Shared Key button. Select IP Address in the Internal Network IP Address field. d. Otherwise, leave this address in the ID Type drop-down list, select None. e. c. In the Internet ... Security Policy Editor window, click My Identity. If you will be switching between adapters or if you have only one adapter, select Any. The Pre-Shared Key screen displays: Figure 6-12 Virtual Private Networking v1.0, May 2008 6-13 In the Select Certificate drop-down list. Wireless ADSL2+ Modem Router DG834G ...
In the Network Security Policy list on the left side of the screen, click the Pre-Shared Key button. Select IP Address in the Internal Network IP Address field. d. Otherwise, leave this address in the ID Type drop-down list, select None. e. c. In the Internet ... Security Policy Editor window, click My Identity. If you will be switching between adapters or if you have only one adapter, select Any. The Pre-Shared Key screen displays: Figure 6-12 Virtual Private Networking v1.0, May 2008 6-13 In the Select Certificate drop-down list. Wireless ADSL2+ Modem Router DG834G ...
DG834Gv5 Reference Manual
Page 108
... list, select SHA-1. Wireless ADSL2+ Modem Router DG834G User Manual f. a. In the Encrypt Alg drop-down list, select the type of the Security Policy Editor window, expand the Security Policy heading by double clicking its name or clicking the + symbol. Configure the VPN client key exchange proposal. 6-14 v1.0, May 2008 Virtual Private Networking This field is...
... list, select SHA-1. Wireless ADSL2+ Modem Router DG834G User Manual f. a. In the Encrypt Alg drop-down list, select the type of the Security Policy Editor window, expand the Security Policy heading by double clicking its name or clicking the + symbol. Configure the VPN client key exchange proposal. 6-14 v1.0, May 2008 Virtual Private Networking This field is...
DG834Gv5 Reference Manual
Page 168
... b. In the Pre-Shared Key screen, click Enter Key. This field is entered. In the Network Security Policy list on the left side of the Security Policy Editor window, click My Identity. In the Internet Interface section, select Intel PRO/100VE Network Connection (in this example, your... Ethernet adapter might be different) in the Name field, and then enter 192.168.2.3 (in the IP Addr field. B-18 v1.0, May 2008 NETGEAR VPN Configuration In this example) in this example, 12345678 is case-sensitive. Wireless ADSL2+ Modem Router DG834G...
... b. In the Pre-Shared Key screen, click Enter Key. This field is entered. In the Network Security Policy list on the left side of the Security Policy Editor window, click My Identity. In the Internet Interface section, select Intel PRO/100VE Network Connection (in this example, your... Ethernet adapter might be different) in the Name field, and then enter 192.168.2.3 (in the IP Addr field. B-18 v1.0, May 2008 NETGEAR VPN Configuration In this example) in this example, 12345678 is case-sensitive. Wireless ADSL2+ Modem Router DG834G...
DG834Gv5 Reference Manual
Page 169
...select SHA-1. f. g. Wireless ADSL2+ Modem Router DG834G User Manual 5. e. Configure the VPN Client Key Exchange Proposal. b. In this connection. NETGEAR VPN Configuration v1.0, May 2008 B-19 This selection must match your selection in the VPN router configuration. In the Network Security Policy list on the... 2. 6. This selection must match your selection in the VPN router configuration. a. In the Key Group drop-down list, select Unspecified. In the Authentication Method field, select Pre-Shared Key. In the Hash Alg drop-down list, select the type ...
...select SHA-1. f. g. Wireless ADSL2+ Modem Router DG834G User Manual 5. e. Configure the VPN Client Key Exchange Proposal. b. In this connection. NETGEAR VPN Configuration v1.0, May 2008 B-19 This selection must match your selection in the VPN router configuration. In the Network Security Policy list on the... 2. 6. This selection must match your selection in the VPN router configuration. a. In the Key Group drop-down list, select Unspecified. In the Authentication Method field, select Pre-Shared Key. In the Hash Alg drop-down list, select the type ...
DG834Gv3 Reference Manual
Page 7
... ADSL Modem Wireless Router DG834G Chapter 1 About This Manual Audience, Scope, Conventions, and Formats 1-1 How to Print this Manual 1-2 Chapter 2 Introduction About the Modem Router 2-1 Key Features ...2-2 A Powerful, True Firewall 2-2 802.11 Standards-based Wireless Networking 2-3 Easy Installation and Management 2-3 Protocol Support ...2-4 Virtual Private Networking (VPN 2-5 Auto Sensing and Auto Uplink™ LAN Ethernet Connections 2-5 Content Filtering ...2-6 Trend Micro Home Network Security...
... ADSL Modem Wireless Router DG834G Chapter 1 About This Manual Audience, Scope, Conventions, and Formats 1-1 How to Print this Manual 1-2 Chapter 2 Introduction About the Modem Router 2-1 Key Features ...2-2 A Powerful, True Firewall 2-2 802.11 Standards-based Wireless Networking 2-3 Easy Installation and Management 2-3 Protocol Support ...2-4 Virtual Private Networking (VPN 2-5 Auto Sensing and Auto Uplink™ LAN Ethernet Connections 2-5 Content Filtering ...2-6 Trend Micro Home Network Security...
DG834Gv3 Reference Manual
Page 18
... as off-limits. • Logs security incidents The DG834G v3 will log security events such as blocked incoming traffic, port scans, attacks, and administrator logins. Reference Manual for the ADSL Modem Wireless Router DG834G Key Features The ADSL Modem Wireless Router provides the following features: • A built-in ADSL modem • A powerful, true firewall • 802.11g standards-based wireless networking • Easy, Web-based...
... as off-limits. • Logs security incidents The DG834G v3 will log security events such as blocked incoming traffic, port scans, attacks, and administrator logins. Reference Manual for the ADSL Modem Wireless Router DG834G Key Features The ADSL Modem Wireless Router provides the following features: • A built-in ADSL modem • A powerful, true firewall • 802.11g standards-based wireless networking • Easy, Web-based...
DG834Gv3 Reference Manual
Page 108
...Manual for the ADSL Modem Wireless Router DG834G h. My Identity and Security Policy subheadings appear below the check box. Figure 7-10 c. You will provide information about the remote VPN client PC. Select IP Address in the ID Type menu below the connection name. In the Network Security Policy list, ...expand the new connection by double clicking its name or clicking on the Security Policy subheading to provide the Pre-Shared Key that you will need to show the Security Policy menu. In this example, 22...
...Manual for the ADSL Modem Wireless Router DG834G h. My Identity and Security Policy subheadings appear below the check box. Figure 7-10 c. You will provide information about the remote VPN client PC. Select IP Address in the ID Type menu below the connection name. In the Network Security Policy list, ...expand the new connection by double clicking its name or clicking on the Security Policy subheading to provide the Pre-Shared Key that you will need to show the Security Policy menu. In this example, 22...