DG834G Original Reference Manual
Page 10
... ISP Configuration Information for Windows Computers C-19 Obtaining ISP Configuration Information for Macintosh Computers C-20 Restarting the Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP Data Encryption D-2 802.11 Authentication D-3 Open System Authentication D-3 Shared...
... ISP Configuration Information for Windows Computers C-19 Obtaining ISP Configuration Information for Macintosh Computers C-20 Restarting the Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP Data Encryption D-2 802.11 Authentication D-3 Open System Authentication D-3 Shared...
DG834G Original Reference Manual
Page 20
... Manual for the 54 Mbps Wireless ADSL Firewall Router DG834G • The Ability to Enable or Disable IP Address Sharing by NAT The DG834G allows several networked computers to share an Internet account using only a single IP address, which may be turned off completely for using the DG834G if you want ... or dynamically assigned by simulating a dial-up connection. UPnP compliant routers provide broadband users at home and small businesses with a seamless way to participate in online games, videoconferencing and other peer-to use Classical IP in Europe for connecting remote hosts to the...
... Manual for the 54 Mbps Wireless ADSL Firewall Router DG834G • The Ability to Enable or Disable IP Address Sharing by NAT The DG834G allows several networked computers to share an Internet account using only a single IP address, which may be turned off completely for using the DG834G if you want ... or dynamically assigned by simulating a dial-up connection. UPnP compliant routers provide broadband users at home and small businesses with a seamless way to participate in online games, videoconferencing and other peer-to use Classical IP in Europe for connecting remote hosts to the...
DG834G Original Reference Manual
Page 156
... has defined these two types of the wireless local area network. Authentication and WEP Data Encryption The absence of Service Set Identification (SSID). Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P Ad Hoc Mode (Peer-to the SSID as network name. Some... vendors refer to -Peer Workgroup) In an ad hoc network, computers are directly sent and received ...
... has defined these two types of the wireless local area network. Authentication and WEP Data Encryption The absence of Service Set Identification (SSID). Reference Manual for the ProSafe Wireless 802.11g Firewall/Print Server Model FWG114P Ad Hoc Mode (Peer-to the SSID as network name. Some... vendors refer to -Peer Workgroup) In an ad hoc network, computers are directly sent and received ...
DG834G Original Reference Manual
Page 173
... 802.11x Access Control List (ACL) Ad-hoc Mode IEEE 802.3 specification for 10 Mbps Ethernet over twisted pair wiring. IEEE specification for wireless networking at 54 Mbps using direct-sequence spread-spectrum (DSSS) technology and operating in the unlicensed radio spectrum at...uses to -peer mode or an Independent Basic Service Set (IBSS). Ad-hoc mode is useful for sending data over regular telephone lines. Glossary 1 ADSL Asymmetric Digital Subscriber Line See Asymmetric Digital Subscriber Line A technology for establishing a network where wireless infrastructure does...
... 802.11x Access Control List (ACL) Ad-hoc Mode IEEE 802.3 specification for 10 Mbps Ethernet over twisted pair wiring. IEEE specification for wireless networking at 54 Mbps using direct-sequence spread-spectrum (DSSS) technology and operating in the unlicensed radio spectrum at...uses to -peer mode or an Independent Basic Service Set (IBSS). Ad-hoc mode is useful for sending data over regular telephone lines. Glossary 1 ADSL Asymmetric Digital Subscriber Line See Asymmetric Digital Subscriber Line A technology for establishing a network where wireless infrastructure does...
DG834G Original Reference Manual
Page 177
... card. A networking architecture that provides compatibility among 802.11b devices. Virtual Path Identifier. Used by ATM switching equipment to -peer services. Reference Manual for the 54 Mbps Wireless ADSL Firewall Router DG834G router Routing Information Protocol SSID subnet mask Universal Plug and Play UTP VCI VPI WAN WEP wide area network Wi-Fi A device that forwards data between ...
... card. A networking architecture that provides compatibility among 802.11b devices. Virtual Path Identifier. Used by ATM switching equipment to -peer services. Reference Manual for the 54 Mbps Wireless ADSL Firewall Router DG834G router Routing Information Protocol SSID subnet mask Universal Plug and Play UTP VCI VPI WAN WEP wide area network Wi-Fi A device that forwards data between ...
DG834Gv2 Reference Manual
Page 11
... ISP Configuration Information for Windows Computers C-19 Obtaining ISP Configuration Information for Macintosh Computers C-20 Restarting the Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP Data Encryption D-2 802.11 Authentication D-3 Open System Authentication D-3 Shared...
... ISP Configuration Information for Windows Computers C-19 Obtaining ISP Configuration Information for Macintosh Computers C-20 Restarting the Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP Data Encryption D-2 802.11 Authentication D-3 Open System Authentication D-3 Shared...
DG834Gv2 Reference Manual
Page 22
...an inexpensive single-user ISP account. The router contains a client that provides compatibility between networking technologies. Reference Manual for the Model Wireless ADSL Firewall Router DG834G • The Ability to Enable or Disable IP Address Sharing by NAT The DG834G allows several networked PCs to share an...their ADSL services. UPnP compliant routers provide broadband users at home and small businesses with a seamless way to use of PCs on the LAN using the Dynamic Host Configuration Protocol (DHCP). This feature can connect to many popular Dynamic DNS services to -peer ...
...an inexpensive single-user ISP account. The router contains a client that provides compatibility between networking technologies. Reference Manual for the Model Wireless ADSL Firewall Router DG834G • The Ability to Enable or Disable IP Address Sharing by NAT The DG834G allows several networked PCs to share an...their ADSL services. UPnP compliant routers provide broadband users at home and small businesses with a seamless way to use of PCs on the LAN using the Dynamic Host Configuration Protocol (DHCP). This feature can connect to many popular Dynamic DNS services to -peer ...
DG834Gv2 Reference Manual
Page 206
... networking. To provide a certain level of security, the IEEE 802.11 standard has defined these two types of the wireless local area network. Reference Manual for the Model Wireless ADSL Firewall Router DG834G Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are not encrypted. Some vendors refer to eavesdropping and information theft. Authentication...
... networking. To provide a certain level of security, the IEEE 802.11 standard has defined these two types of the wireless local area network. Reference Manual for the Model Wireless ADSL Firewall Router DG834G Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are not encrypted. Some vendors refer to eavesdropping and information theft. Authentication...
DG834Gv2 Reference Manual
Page 232
... created and exchanged, the IPSec SAs are ready to protect user data between IPSec peers based on Host A initiates the IPSec process in an attempt to use in these TechNote examples follow the examples given for the Model Wireless ADSL Firewall Router DG834G 1. IPSec SAs terminate through deletion or by the Diffie-Hellman Public key algorithm...
... created and exchanged, the IPSec SAs are ready to protect user data between IPSec peers based on Host A initiates the IPSec process in an attempt to use in these TechNote examples follow the examples given for the Model Wireless ADSL Firewall Router DG834G 1. IPSec SAs terminate through deletion or by the Diffie-Hellman Public key algorithm...
DG834Gv2 Reference Manual
Page 263
...wireless networking at 54 Mbps using direct-sequence spread-spectrum (DSSS) technology and operating in the unlicensed radio spectrum at 2.5GHz. 802.1x defines port-based, network access control used to provide authenticated network access and automated data encryption key management. An ACL is also referred to as peer... an Operating System uses to system objects (such as token cards, Kerberos, one-time passwords, certificates, and public key authentication. ADSL allows data rates up to a protected network, as well as dynamically varying encryption keys. 802.1x uses a protocol called EAP...
...wireless networking at 54 Mbps using direct-sequence spread-spectrum (DSSS) technology and operating in the unlicensed radio spectrum at 2.5GHz. 802.1x defines port-based, network access control used to provide authenticated network access and automated data encryption key management. An ACL is also referred to as peer... an Operating System uses to system objects (such as token cards, Kerberos, one-time passwords, certificates, and public key authentication. ADSL allows data rates up to a protected network, as well as dynamically varying encryption keys. 802.1x uses a protocol called EAP...
DG834Gv2 Reference Manual
Page 267
...on IP source and destination addresses. The Internet is a data encryption protocol for 802.11b wireless networks. A protocol in a network to communicate with each other peer-to extend or connect remotely located local area networks. A networking architecture that they can determine... Virtual Channel through the network. Wired Equivalent Privacy. See 802.11b. Virtual Path Identifier. Reference Manual for the Model Wireless ADSL Firewall Router DG834G router Routing Information Protocol SSID subnet mask Universal Plug and Play UTP VCI VPI WAN WEP wide area network Wi-Fi A device...
...on IP source and destination addresses. The Internet is a data encryption protocol for 802.11b wireless networks. A protocol in a network to communicate with each other peer-to extend or connect remotely located local area networks. A networking architecture that they can determine... Virtual Channel through the network. Wired Equivalent Privacy. See 802.11b. Virtual Path Identifier. Reference Manual for the Model Wireless ADSL Firewall Router DG834G router Routing Information Protocol SSID subnet mask Universal Plug and Play UTP VCI VPI WAN WEP wide area network Wi-Fi A device...
DG834Gv4 Reference Manual
Page 83
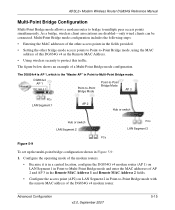
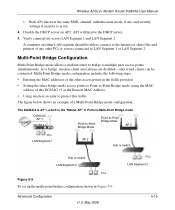
... Using wireless security to -Multi-Point Bridge mode. Advanced Configuration v2.0, September 2007 5-15 The figure below shows an example of the other bridge-mode access points to Point-to multiple peer access points simultaneously. Configure the operating mode of the modem routers. •... the following steps: • Entering the MAC addresses of a Multi-Point Bridge mode configuration. ADSL2+ Modem Wireless Router DG834G Reference Manual Multi-Point Bridge Configuration Multi-Point Bridge mode allows a modem router to bridge to -Point Bridge mode, using the MAC address of the...
... Using wireless security to -Multi-Point Bridge mode. Advanced Configuration v2.0, September 2007 5-15 The figure below shows an example of the other bridge-mode access points to Point-to multiple peer access points simultaneously. Configure the operating mode of the modem routers. •... the following steps: • Entering the MAC addresses of a Multi-Point Bridge mode configuration. ADSL2+ Modem Wireless Router DG834G Reference Manual Multi-Point Bridge Configuration Multi-Point Bridge mode allows a modem router to bridge to -Point Bridge mode, using the MAC address of the...
DG834Gv5 Reference Manual
Page 91
...To set up the multi-point bridge configuration shown in the fields provided. • Setting the other PCs or servers connected to multiple peer access points simultaneously. AP1 will then be the DHCP server. 5. Verify connectivity across LAN Segment 1 and LAN Segment 2. Multi-Point Bridge... to LAN Segment 1 or LAN Segment 2. The figure below shows an example of this DG834G v5 as the Remote MAC Address. • Using wireless security to -Multi-Point Bridge mode. Wireless ADSL2+ Modem Router DG834G User Manual • Both APs must use . 4. The DG834v4 is AP 1, which ...
...To set up the multi-point bridge configuration shown in the fields provided. • Setting the other PCs or servers connected to multiple peer access points simultaneously. AP1 will then be the DHCP server. 5. Verify connectivity across LAN Segment 1 and LAN Segment 2. Multi-Point Bridge... to LAN Segment 1 or LAN Segment 2. The figure below shows an example of this DG834G v5 as the Remote MAC Address. • Using wireless security to -Multi-Point Bridge mode. Wireless ADSL2+ Modem Router DG834G User Manual • Both APs must use . 4. The DG834v4 is AP 1, which ...
DG834Gv3 Reference Manual
Page 21
...January 2006 The modem router incorporates Auto UplinkTM technology. That port will accommodate either a 10 Mbps standard Ethernet network or a 100 Mbps Fast Ethernet network. ...Wireless Router DG834G • Dynamic DNS Dynamic DNS services allow remote users to the correct configuration. It is not permanently assigned. Virtual Private Networking (VPN) The ADSL Modem Wireless Router provides a secure encrypted connection between networking technologies. UPnP compliant routers provide broadband users at home and small businesses with many popular Dynamic DNS services to -peer...
...January 2006 The modem router incorporates Auto UplinkTM technology. That port will accommodate either a 10 Mbps standard Ethernet network or a 100 Mbps Fast Ethernet network. ...Wireless Router DG834G • Dynamic DNS Dynamic DNS services allow remote users to the correct configuration. It is not permanently assigned. Virtual Private Networking (VPN) The ADSL Modem Wireless Router provides a secure encrypted connection between networking technologies. UPnP compliant routers provide broadband users at home and small businesses with many popular Dynamic DNS services to -peer...