Command Line Interface Guide
Page 49
show snmp views 1240 show trapflags 1242 snmp-server community 1244 snmp-server community-group 1246 snmp-server contact 1247 snmp-server enable traps 1247 snmp-server enable traps authentication 1249 snmp-server engineID local 1250 snmp-server filter 1251 snmp-server group 1253 snmp-server host 1254 snmp-server location 1256 snmp-server user 1257 snmp-server view 1258 snmp-server v3-host 1260 69 SSH Commands 1263 crypto key generate rsa 1264 crypto key pubkey-chain ssh 1265 ip ssh port 1266 ip ssh pubkey-auth 1267 ip ssh server 1268 Contents 49
show snmp views 1240 show trapflags 1242 snmp-server community 1244 snmp-server community-group 1246 snmp-server contact 1247 snmp-server enable traps 1247 snmp-server enable traps authentication 1249 snmp-server engineID local 1250 snmp-server filter 1251 snmp-server group 1253 snmp-server host 1254 snmp-server location 1256 snmp-server user 1257 snmp-server view 1258 snmp-server v3-host 1260 69 SSH Commands 1263 crypto key generate rsa 1264 crypto key pubkey-chain ssh 1265 ip ssh port 1266 ip ssh pubkey-auth 1267 ip ssh server 1268 Contents 49
Command Line Interface Guide
Page 61
... GC login authentication Specifies the login authentication method list LC for GC accessing higher privilege levels. SSH Public Key • SK - GC aaa authorization network Enables the switch to the GC normal level. password Specifies a password on interfaces running IEEE 802.... v6DP - User EXEC • VLAN - aaa authentication login Defines login authentication. LC Command Groups 61 SSH Public Key-chain • TC - • SP - VLAN Configuration • v6ACL - aaa authentication enable Defines authentication method lists for a remote telnet or console.
... GC login authentication Specifies the login authentication method list LC for GC accessing higher privilege levels. SSH Public Key • SK - GC aaa authorization network Enables the switch to the GC normal level. password Specifies a password on interfaces running IEEE 802.... v6DP - User EXEC • VLAN - aaa authentication login Defines login authentication. LC Command Groups 61 SSH Public Key-chain • TC - • SP - VLAN Configuration • v6ACL - aaa authentication enable Defines authentication method lists for a remote telnet or console.
Command Line Interface Guide
Page 128
... to be used by the SSH server. key-string Manually specifies a SSH public key. SK show crypto key pubkey- SSH Command Description Mode* crypto key generate dsa Generates DSA key pairs for incoming GC SSH sessions. GC ip ssh pubkey-auth Enables public key authentication for the ...the meaning of each Mode abbreviation, see "Mode Types" on the switch. ip ssh server Enables the switch to be configured from a SSH GC server connection. show crypto key mypubkey Displays its own SSH public keys stored on the PE switch. Command Description Mode* snmp-server filter Creates ...
... to be used by the SSH server. key-string Manually specifies a SSH public key. SK show crypto key pubkey- SSH Command Description Mode* crypto key generate dsa Generates DSA key pairs for incoming GC SSH sessions. GC ip ssh pubkey-auth Enables public key authentication for the ...the meaning of each Mode abbreviation, see "Mode Types" on the switch. ip ssh server Enables the switch to be configured from a SSH GC server connection. show crypto key mypubkey Displays its own SSH public keys stored on the PE switch. Command Description Mode* snmp-server filter Creates ...
Command Line Interface Guide
Page 129
Command Description Mode* show syslog-servers Description Mode* Clears messages from the logging file. Enable CLI command logging GC Logs messages to a syslog server GC Limits syslog messages displayed from an GC internal buffer based on severity. GC... Limits syslog messages sent to the console based on port show logging show logging file show ip ssh Displays the SSH server configuration. L Displays the state of syslog messages. PE Command Groups 129 PE Describes the syslog server. Controls error messages logging. GC...
Command Description Mode* show syslog-servers Description Mode* Clears messages from the logging file. Enable CLI command logging GC Logs messages to a syslog server GC Limits syslog messages displayed from an GC internal buffer based on severity. GC... Limits syslog messages sent to the console based on port show logging show logging file show ip ssh Displays the SSH server configuration. L Displays the state of syslog messages. PE Command Groups 129 PE Describes the syslog server. Controls error messages logging. GC...
Command Line Interface Guide
Page 190
... used to name the list of all TACACS+ servers for authentication. Default Configuration The default enable list is used by console, telnet, and SSH and only contains the method none. aaa authentication enable Use the aaa authentication enable command in Global Configuration mode to set authentication for authentication. Uses the list of methods, when...
... used to name the list of all TACACS+ servers for authentication. Default Configuration The default enable list is used by console, telnet, and SSH and only contains the method none. aaa authentication enable Use the aaa authentication enable command in Global Configuration mode to set authentication for authentication. Uses the list of methods, when...
Command Line Interface Guide
Page 192
... configures authentication login. 192 AAA Commands "defaultList" is any character string used by telnet and SSH and only contains the method local. Example The following table: Keyword enable line local none radius tacacs Source or destination Uses the enable password for a particular protocol, where list-name is used to name this list. Create...
... configures authentication login. 192 AAA Commands "defaultList" is any character string used by telnet and SSH and only contains the method local. Example The following table: Keyword enable line local none radius tacacs Source or destination Uses the enable password for a particular protocol, where list-name is used to name this list. Create...
Command Line Interface Guide
Page 201
Syntax show users accounts command in Privileged EXEC mode to display information about the local user database. enableList : local Line Login Method List Console defaultList Telnet defaultList SSH defaultList Enable Method List enableList enableList enableList HTTPS HTTP DOT1X :local :local :none show users accounts Use the show users accounts [long] Default Configuration This command has no user guidelines. Command Mode Privileged EXEC mode User Guidelines This command has no default configuration. AAA Commands 201
Syntax show users accounts command in Privileged EXEC mode to display information about the local user database. enableList : local Line Login Method List Console defaultList Telnet defaultList SSH defaultList Enable Method List enableList enableList enableList HTTPS HTTP DOT1X :local :local :none show users accounts Use the show users accounts [long] Default Configuration This command has no user guidelines. Command Mode Privileged EXEC mode User Guidelines This command has no default configuration. AAA Commands 201
Command Line Interface Guide
Page 1267
... has no form of this command. Example The following example specifies the port to enable public key authentication for incoming SSH sessions. Example The following example enables public key authentication for incoming SSH sessions. Syntax ip ssh pubkey-auth no ip ssh pubkey-auth Default Configuration The function is independent from this function, use the no...
... has no form of this command. Example The following example specifies the port to enable public key authentication for incoming SSH sessions. Example The following example enables public key authentication for incoming SSH sessions. Syntax ip ssh pubkey-auth no ip ssh pubkey-auth Default Configuration The function is independent from this function, use the no...
Command Line Interface Guide
Page 1268
...string key-string row key-string • row - To specify the SSH public key row by default. ip ssh server Use the ip ssh server command in Global Configuration mode to enable the switch to be configured using SSH. To disable this function, use the commands crypto key generate rsa, ...dsa. Syntax ip ssh server no form of this command. Example The following example enables the switch to specify an SSH public key manually. The UU-encoded DER format is enabled by row. • key-string - console(config)#ip ssh server key-string Use the key-string SSH Public Key Configuration ...
...string key-string row key-string • row - To specify the SSH public key row by default. ip ssh server Use the ip ssh server command in Global Configuration mode to enable the switch to be configured using SSH. To disable this function, use the commands crypto key generate rsa, ...dsa. Syntax ip ssh server no form of this command. Example The following example enables the switch to specify an SSH public key manually. The UU-encoded DER format is enabled by row. • key-string - console(config)#ip ssh server key-string Use the key-string SSH Public Key Configuration ...
Command Line Interface Guide
Page 1273
... Address User Name Time SessionTime Idle 10.240.1.122 John 00:00:00 00:00:08 SSH Commands 1273 SSH Public Key Authentication is enabled. show ip ssh Use the show ip ssh SSH server enabled. Example The following example displays the SSH server configuration. Command Mode Privileged EXEC mode User Guidelines This command has no default configuration...
... Address User Name Time SessionTime Idle 10.240.1.122 John 00:00:00 00:00:08 SSH Commands 1273 SSH Public Key Authentication is enabled. show ip ssh Use the show ip ssh SSH server enabled. Example The following example displays the SSH server configuration. Command Mode Privileged EXEC mode User Guidelines This command has no default configuration...
Command Line Interface Guide
Page 1274
... The following example enables a SSH public key to specify which SSH public key you are no user guidelines. RSA key • dsa - console(config)#crypto key pubkey-chain ssh console(config-pubkey-chain)#user-key bob rsa console(config-pubkey-key)# 1274 SSH Commands Command Mode SSH Public Key Chain Configuration... has no keys. Syntax user-key username {rsa|dsa} no form of this command. To remove a SSH public key, use the no user-key username • username - Specifies the remote SSH client username. (Range: 1-48 characters) • rsa - user-key Use the user-key command in...
... The following example enables a SSH public key to specify which SSH public key you are no user guidelines. RSA key • dsa - console(config)#crypto key pubkey-chain ssh console(config-pubkey-chain)#user-key bob rsa console(config-pubkey-key)# 1274 SSH Commands Command Mode SSH Public Key Chain Configuration... has no keys. Syntax user-key username {rsa|dsa} no form of this command. To remove a SSH public key, use the no user-key username • username - Specifies the remote SSH client username. (Range: 1-48 characters) • rsa - user-key Use the user-key command in...
User's Guide
Page 37
... with MLD v1. The protocol specifically discovers which types of traffic are forwarded or blocked, and above all provide security for SSH, Telnet, HTTP, HTTPS, and SNMP access are manually defined or learned on a port to discover the presence of multicast ... MACbased authentication allows multiple supplicants connected to the same port to send voice traffic through the port. For more information about enabling and configuring 802.1X port authentication, see "Password Management." These addresses are assigned security features. Only authenticated and approved system...
... with MLD v1. The protocol specifically discovers which types of traffic are forwarded or blocked, and above all provide security for SSH, Telnet, HTTP, HTTPS, and SNMP access are manually defined or learned on a port to discover the presence of multicast ... MACbased authentication allows multiple supplicants connected to the same port to send voice traffic through the port. For more information about enabling and configuring 802.1X port authentication, see "Password Management." These addresses are assigned security features. Only authenticated and approved system...
User's Guide
Page 91
...Enable Disable loopback2 0.0.0.0 0.0.0.0 Disable Disable Review Copy Security Management and Password Configuration System security is handled through the SSH mechanism. The procedure is handled through the AAA (Authentication, Authorization, and Accounting) mechanism that manages user access rights, privileges, and management methods. all passwords are user-defined. Configuring Dell PowerConnect... 91 Data encryption is applicable for the following services: • Console • Telnet • SSH • HTTP •...
...Enable Disable loopback2 0.0.0.0 0.0.0.0 Disable Disable Review Copy Security Management and Password Configuration System security is handled through the SSH mechanism. The procedure is handled through the AAA (Authentication, Authorization, and Accounting) mechanism that manages user access rights, privileges, and management methods. all passwords are user-defined. Configuring Dell PowerConnect... 91 Data encryption is applicable for the following services: • Console • Telnet • SSH • HTTP •...
User's Guide
Page 93
... time you upgrade (install a new version of) the control software application on the switch. Configuring Dell PowerConnect 93 Configuring an Initial HTTPS Password To configure an initial HTTPS password, enter the following commands once ...when configuring to use an HTTPS session over a console, a Telnet, or an SSH session. console#configure console(config)#crypto certificate 1 generate console(config-crypto-cert)#country US console(config-...to appear. NOTE: In the Web browser enable SSL 2.0 or greater for the page content to the configuration level access.
... time you upgrade (install a new version of) the control software application on the switch. Configuring Dell PowerConnect 93 Configuring an Initial HTTPS Password To configure an initial HTTPS password, enter the following commands once ...when configuring to use an HTTPS session over a console, a Telnet, or an SSH session. console#configure console(config)#crypto certificate 1 generate console(config-crypto-cert)#country US console(config-...to appear. NOTE: In the Web browser enable SSL 2.0 or greater for the page content to the configuration level access.
User's Guide
Page 113
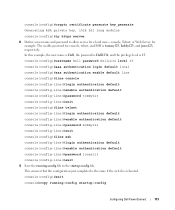
...login authentication default console(config-line)#enable authentication default console(config-line)#password bobby123 console(config-line)#exit console(config)#line ssh console(config-line)#login authentication default console(config-line)#enable authentication default console(config-line)#password...Web Server, for console, telnet, and SSH is tommy123, bobby123, and jones123, respectively. Define a user name and password to the startup-config file. Save the running -config startup-config Configuring Dell PowerConnect 113 console(config)#crypto certificate generate key_generate Generating...
...login authentication default console(config-line)#enable authentication default console(config-line)#password bobby123 console(config-line)#exit console(config)#line ssh console(config-line)#login authentication default console(config-line)#enable authentication default console(config-line)#password...Web Server, for console, telnet, and SSH is tommy123, bobby123, and jones123, respectively. Define a user name and password to the startup-config file. Save the running -config startup-config Configuring Dell PowerConnect 113 console(config)#crypto certificate generate key_generate Generating...
User's Guide
Page 157
... go to the following features: • Access Profile • Authentication Profiles • Select Authentication • Password Management • Local User Database • Line Passwords • Enable Password • TACACS+ Settings • RADIUS Global Configuration • RADIUS Server Configuration • RADIUS Accounting Server Statistics • RADIUS Server Statistics • Authorization Network RADIUS...
... go to the following features: • Access Profile • Authentication Profiles • Select Authentication • Password Management • Local User Database • Line Passwords • Enable Password • TACACS+ Settings • RADIUS Global Configuration • RADIUS Server Configuration • RADIUS Accounting Server Statistics • RADIUS Server Statistics • Authorization Network RADIUS...
User's Guide
Page 168
...Select Authentication page. 2. Select an authentication profile in the Console field. 3. Select an authentication profile in the Secure Telnet (SSH) field. 3. Select an authentication profile in the Telnet field. 3. Click Apply Changes. Open the Select Authentication page. 168 ... Select Authentication page. 2. Click Apply Changes. admin Auth-Type := Local, User-Password == "pass1234" Service-Type = NAS-Prompt-User enable Auth-Type := Local, User-Password == "pass5678" Service-Type = Administrative-User The values for the Service-Type attribute are assigned an authentication...
...Select Authentication page. 2. Select an authentication profile in the Console field. 3. Select an authentication profile in the Secure Telnet (SSH) field. 3. Select an authentication profile in the Telnet field. 3. Click Apply Changes. Open the Select Authentication page. 168 ... Select Authentication page. 2. Click Apply Changes. admin Auth-Type := Local, User-Password == "pass1234" Service-Type = NAS-Prompt-User enable Auth-Type := Local, User-Password == "pass5678" Service-Type = Administrative-User The values for the Service-Type attribute are assigned an authentication...
User's Guide
Page 169
... until the desired authentication sequence is displayed in the Selected Methods field. 4. Table 6-24. Specifies authentication methods for SSH, Telnet, HTTP, HTTPS, and SNMP access are assigned security features, including: • Defining minimum password lengths (...desired authentication sequence is displayed in the Selected Methods field. 4. Access Method and Authentication Profile Commands CLI Command enable authentication ip http authentication ip https authentication login authentication show authentication methods Description Specifies the authentication method list when ...
... until the desired authentication sequence is displayed in the Selected Methods field. 4. Table 6-24. Specifies authentication methods for SSH, Telnet, HTTP, HTTPS, and SNMP access are assigned security features, including: • Defining minimum password lengths (...desired authentication sequence is displayed in the Selected Methods field. 4. Access Method and Authentication Profile Commands CLI Command enable authentication ip http authentication ip https authentication login authentication show authentication methods Description Specifies the authentication method list when ...
User's Guide
Page 175
...password Description Specifies the password for the type of session you use to connect to the device. 4. Enable Password Use the Enable Password page to set a local password to control access to normal and privilege levels. Figure 6-49...., or SSH). To display the Enable Password page, click System →Management Security →Enable Password in the ***** format. • Confirm Enable Password - Open the Enable Password page. 2. Confirm the Line Password. 5. Defining Enable Passwords 1. Confirms the new Enable password. Enable Password The Enable Password page...
...password Description Specifies the password for the type of session you use to connect to the device. 4. Enable Password Use the Enable Password page to set a local password to control access to normal and privilege levels. Figure 6-49...., or SSH). To display the Enable Password page, click System →Management Security →Enable Password in the ***** format. • Confirm Enable Password - Open the Enable Password page. 2. Confirm the Line Password. 5. Defining Enable Passwords 1. Confirms the new Enable password. Enable Password The Enable Password page...
Release Notes
Page 7
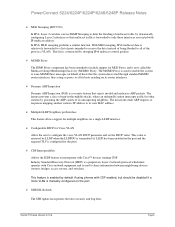
...is manually configured on a single LLDP interface. ¾ Configurable DSCP for multiple neighbors on the port. ¾ SSH/SSL Refresh The SSH update incorporates the latest security and bug fixes. The miscreant sends ARP requests or responses mapping another station's IP ...protocol which interoperates with IP multicast address. Industry Standard Discovery Protocol (ISDP) is transmitted (if LLDP has been enabled on its unsuspecting neighbors. PowerConnect 6224/6224F/6224P/6248/6248P Release Notes ¾ MLD Snooping (RFC2710) In IPv4, Layer 2 switches can use IGMP Snooping to limit...
...is manually configured on a single LLDP interface. ¾ Configurable DSCP for multiple neighbors on the port. ¾ SSH/SSL Refresh The SSH update incorporates the latest security and bug fixes. The miscreant sends ARP requests or responses mapping another station's IP ...protocol which interoperates with IP multicast address. Industry Standard Discovery Protocol (ISDP) is transmitted (if LLDP has been enabled on its unsuspecting neighbors. PowerConnect 6224/6224F/6224P/6248/6248P Release Notes ¾ MLD Snooping (RFC2710) In IPv4, Layer 2 switches can use IGMP Snooping to limit...