User Guide
Page 7
ZyWALL Computer Notebook computer Server Firewall Telephone Switch Router ZyWALL USG 2000 User's Guide 7 The ZyWALL icon is not an exact representation of your device. Document Conventions Icons Used in Figures Figures in this User's Guide may use the following generic icons.
ZyWALL Computer Notebook computer Server Firewall Telephone Switch Router ZyWALL USG 2000 User's Guide 7 The ZyWALL icon is not an exact representation of your device. Document Conventions Icons Used in Figures Figures in this User's Guide may use the following generic icons.
User Guide
Page 9
Contents Overview Contents Overview User's Guide ...31 Introducing the ZyWALL ...33 Features and Applications ...43 Web Configurator ...51 Installation Setup Wizard ...67 Quick Setup ...77 Configuration Basics ...95 Tutorials ...119 L2TP VPN Example ...... ...397 ALG ...401 IP/MAC Binding ...409 Authentication Policy ...415 Firewall ...423 IPSec VPN ...441 SSL VPN ...481 SSL User Screens ...493 SSL User Application Screens 503 SSL User File Sharing ...505 ZyWALL SecuExtender ...513 L2TP VPN ...517 Application Patrol ...521 Anti-Virus ...547 IDP ...563 ADP ...597 ZyWALL USG 2000 User's Guide 9
Contents Overview Contents Overview User's Guide ...31 Introducing the ZyWALL ...33 Features and Applications ...43 Web Configurator ...51 Installation Setup Wizard ...67 Quick Setup ...77 Configuration Basics ...95 Tutorials ...119 L2TP VPN Example ...... ...397 ALG ...401 IP/MAC Binding ...409 Authentication Policy ...415 Firewall ...423 IPSec VPN ...441 SSL VPN ...481 SSL User Screens ...493 SSL User Application Screens 503 SSL User File Sharing ...505 ZyWALL SecuExtender ...513 L2TP VPN ...517 Application Patrol ...521 Anti-Virus ...547 IDP ...563 ADP ...597 ZyWALL USG 2000 User's Guide 9
User Guide
Page 13
Policy ...109 6.5.14 Firewall ...109 6.5.15 IPSec VPN ...110 6.5.16 SSL VPN ...110 6.5.17 L2TP VPN ...111 6.5.18 Application Patrol ... HA ...113 6.6 Objects ...114 6.6.1 User/Group ...114 6.7 System ...115 6.7.1 DNS, WWW, SSH, TELNET, FTP, SNMP, Dial-in the ZyWALL 99 6.4 Packet Flow ...100 6.4.1 ZLD 2.20 Packet Flow Enhancements 100 6.4.2 Routing Table Checking Flow Enhancements 101 6.4.3 NAT Table Checking Flow 102 6.5 ...115 6.7.2 Logs and Reports ...116 6.7.3 File Manager ...116 6.7.4 Diagnostics ...116 6.7.5 Shutdown ...116 Chapter 7 Tutorials ...119 ZyWALL USG 2000 User's Guide 13
Policy ...109 6.5.14 Firewall ...109 6.5.15 IPSec VPN ...110 6.5.16 SSL VPN ...110 6.5.17 L2TP VPN ...111 6.5.18 Application Patrol ... HA ...113 6.6 Objects ...114 6.6.1 User/Group ...114 6.7 System ...115 6.7.1 DNS, WWW, SSH, TELNET, FTP, SNMP, Dial-in the ZyWALL 99 6.4 Packet Flow ...100 6.4.1 ZLD 2.20 Packet Flow Enhancements 100 6.4.2 Routing Table Checking Flow Enhancements 101 6.4.3 NAT Table Checking Flow 102 6.5 ...115 6.7.2 Logs and Reports ...116 6.7.3 File Manager ...116 6.7.4 Diagnostics ...116 6.7.5 Shutdown ...116 Chapter 7 Tutorials ...119 ZyWALL USG 2000 User's Guide 13
User Guide
Page 14
...Set Up User Authentication Using the RADIUS Server 135 7.6.4 Web Surfing Policies With Bandwidth Restrictions 137 7.6.5 Set Up MSN Policies 140 7.6.6 Set Up Firewall Rules 141 7.7 How to Use a RADIUS Server to Authenticate User Accounts based on Groups 142 7.8 How to Use Endpoint Security and Authentication Policies...Firewall Rule for SIP 161 7.12.5 Set Up a DMZ to LAN Firewall Rule for SIP 162 7.13 How to Use Multiple Static Public WAN IP Addresses for LAN to WAN Traffic 163 7.13.1 Create the Public IP Address Range Object 163 7.13.2 Configure the Policy Route 164 14 ZyWALL USG 2000...
...Set Up User Authentication Using the RADIUS Server 135 7.6.4 Web Surfing Policies With Bandwidth Restrictions 137 7.6.5 Set Up MSN Policies 140 7.6.6 Set Up Firewall Rules 141 7.7 How to Use a RADIUS Server to Authenticate User Accounts based on Groups 142 7.8 How to Use Endpoint Security and Authentication Policies...Firewall Rule for SIP 161 7.12.5 Set Up a DMZ to LAN Firewall Rule for SIP 162 7.13 How to Use Multiple Static Public WAN IP Addresses for LAN to WAN Traffic 163 7.13.1 Create the Public IP Address Range Object 163 7.13.2 Configure the Policy Route 164 14 ZyWALL USG 2000...
User Guide
Page 19
...23.1.2 What You Need to Know 416 23.2 Authentication Policy Screen 416 23.2.1 Creating/Editing an Authentication Policy 419 Chapter 24 Firewall...423 24.1 Overview ...423 24.1.1 What You Can Do in this Chapter 423 24.1.2 What You Need to Know 424 24....1.3 Firewall Rule Example Applications 426 24.1.4 Firewall Rule Configuration Example 429 24.2 The Firewall Screen ...431 24.2.1 Configuring the Firewall Screen 432 24.2.2 The Firewall Add/Edit Screen 435 24.3 The Session Limit Screen 436 24.3.1 The Session Limit Add/Edit Screen 438 Chapter 25 IPSec VPN...441 ZyWALL USG 2000 User's ...
...23.1.2 What You Need to Know 416 23.2 Authentication Policy Screen 416 23.2.1 Creating/Editing an Authentication Policy 419 Chapter 24 Firewall...423 24.1 Overview ...423 24.1.1 What You Can Do in this Chapter 423 24.1.2 What You Need to Know 424 24....1.3 Firewall Rule Example Applications 426 24.1.4 Firewall Rule Configuration Example 429 24.2 The Firewall Screen ...431 24.2.1 Configuring the Firewall Screen 432 24.2.2 The Firewall Add/Edit Screen 435 24.3 The Session Limit Screen 436 24.3.1 The Session Limit Add/Edit Screen 438 Chapter 25 IPSec VPN...441 ZyWALL USG 2000 User's ...
User Guide
Page 33
The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates. It also provides bandwidth management, Instant Messaging (IM) and ... to ge1, P2 is the LAN interface, ge2 and ge3 are mapped to ge2 and so on a ZyWALL USG 2000 User's Guide 33 Follow the steps below to start or stop the ZyWALL. 1.1 Overview and Key Default Settings The ZyWALL is 192.168.1.1; The default LAN IP address is a comprehensive security device. CHAPTER 1 Introducing the...
The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates. It also provides bandwidth management, Instant Messaging (IM) and ... to ge1, P2 is the LAN interface, ge2 and ge3 are mapped to ge2 and so on a ZyWALL USG 2000 User's Guide 33 Follow the steps below to start or stop the ZyWALL. 1.1 Overview and Key Default Settings The ZyWALL is 192.168.1.1; The default LAN IP address is a comprehensive security device. CHAPTER 1 Introducing the...
User Guide
Page 43
... zones. CHAPTER 2 Features and Applications This chapter introduces the main features and applications of the ZyWALL. The ZyWALL also offers hub-and-spoke IPSec VPN. ZyWALL USG 2000 User's Guide 43 It also provides bandwidth management, NAT, port forwarding, policy routing, DHCP...to provide secure communication between these ports. • One or more information about the features of the ZyWALL. 2.1 Features The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and...
... zones. CHAPTER 2 Features and Applications This chapter introduces the main features and applications of the ZyWALL. The ZyWALL also offers hub-and-spoke IPSec VPN. ZyWALL USG 2000 User's Guide 43 It also provides bandwidth management, NAT, port forwarding, policy routing, DHCP...to provide secure communication between these ports. • One or more information about the features of the ZyWALL. 2.1 Features The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and...
User Guide
Page 44
...It detects pattern-based attacks in another zone first. You can also inspect sessions. Chapter 2 Features and Applications Firewall The ZyWALL's firewall is initiated by screening data packets against network-based intrusions. This policy-based bandwidth allocation helps your own custom .... You can also create your ZyWALL to defined policies. The ZyWALL's ADP protects against defined access rules. The ZyWALL restricts access by a computer in order to the needs of protocol standards (RFCs - For example, traffic from a pre-defined list. 44 ZyWALL USG 2000 User's Guide
...It detects pattern-based attacks in another zone first. You can also inspect sessions. Chapter 2 Features and Applications Firewall The ZyWALL's firewall is initiated by screening data packets against network-based intrusions. This policy-based bandwidth allocation helps your own custom .... You can also create your ZyWALL to defined policies. The ZyWALL's ADP protects against defined access rules. The ZyWALL restricts access by a computer in order to the needs of protocol standards (RFCs - For example, traffic from a pre-defined list. 44 ZyWALL USG 2000 User's Guide
User Guide
Page 57
...HTTP Redirect Set up and manage port forwarding rules. Exempt List Configure ranges of concurrent client NAT/firewall sessions. Policy Define rules to which the ZyWALL does not apply IP/MAC binding. Concentrator Configure VPN concentrators (hub-and-spoke VPN). Global ... and manage the ZyWALL's DDNS domain names. VPN Gateway Configure IKE tunnels. ZyWALL USG 2000 User's Guide 57 Ethernet Manage Ethernet interfaces and virtual Ethernet interfaces. Auxiliary Manage the AUX port. ALG Configure SIP, H.323, and FTP pass-through settings. Firewall Firewall Create and manage ...
...HTTP Redirect Set up and manage port forwarding rules. Exempt List Configure ranges of concurrent client NAT/firewall sessions. Policy Define rules to which the ZyWALL does not apply IP/MAC binding. Concentrator Configure VPN concentrators (hub-and-spoke VPN). Global ... and manage the ZyWALL's DDNS domain names. VPN Gateway Configure IKE tunnels. ZyWALL USG 2000 User's Guide 57 Ethernet Manage Ethernet interfaces and virtual Ethernet interfaces. Auxiliary Manage the AUX port. ALG Configure SIP, H.323, and FTP pass-through settings. Firewall Firewall Create and manage ...
User Guide
Page 62
...referencing configuration item has a description configured, it is applicable, this field lists the referencing configuration item's position in this case the first firewall rule). Chapter 3 Web Configurator settings reference the object. Table 8 Object References LABEL DESCRIPTION Object Name This identifies the object for which ...in the main window. # This field is the type of object. Click a service's name to close the screen. 62 ZyWALL USG 2000 User's Guide The following example shows which the configuration settings that can appear in the main window.
...referencing configuration item has a description configured, it is applicable, this field lists the referencing configuration item's position in this case the first firewall rule). Chapter 3 Web Configurator settings reference the object. Table 8 Object References LABEL DESCRIPTION Object Name This identifies the object for which ...in the main window. # This field is the type of object. Click a service's name to close the screen. 62 ZyWALL USG 2000 User's Guide The following example shows which the configuration settings that can appear in the main window.
User Guide
Page 66
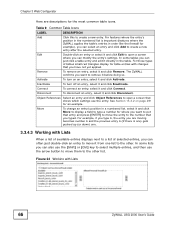
... with changes that you typed. For example, if you type 6, the entry you are descriptions for the most common table icons. The ZyWALL confirms you want to put that shows which settings use the arrow button to move it and click Move to display a field to type...important (features where the ZyWALL applies the table's entries in order like the firewall for example), you can modify the entry's settings. For features where the entry's position in the numbered list is one) gets pushed up (or down) one. 3.3.4.3 Working with Lists 66 ZyWALL USG 2000 User's Guide Remove To...
... with changes that you typed. For example, if you type 6, the entry you are descriptions for the most common table icons. The ZyWALL confirms you want to put that shows which settings use the arrow button to move it and click Move to display a field to type...important (features where the ZyWALL applies the table's entries in order like the firewall for example), you can modify the entry's settings. For features where the entry's position in the numbered list is one) gets pushed up (or down) one. 3.3.4.3 Working with Lists 66 ZyWALL USG 2000 User's Guide Remove To...
User Guide
Page 95
... 6.5 on page 115 introduces some of the tools available for system management. 6.1 Object-based Configuration The ZyWALL stores information or settings as well. (You might also have firewall, application patrol, content filter, and other settings use these ZyWALL USG 2000 User's Guide 95 If you configure the trunk. Some of it . CHAPTER 6 Configuration Basics This...
... 6.5 on page 115 introduces some of the tools available for system management. 6.1 Object-based Configuration The ZyWALL stores information or settings as well. (You might also have firewall, application patrol, content filter, and other settings use these ZyWALL USG 2000 User's Guide 95 If you configure the trunk. Some of it . CHAPTER 6 Configuration Basics This...
User Guide
Page 96
... 6 Configuration Basics objects whenever the interface's IP address settings change an Ethernet interface's IP address, the ZyWALL automatically updates the rules or settings that use the interface-based, LAN subnet address object. Figure 62 Zones... DMZ) A zone is an overview of zones, interfaces, and physical ports in configuring other features. 96 ZyWALL USG 2000 User's Guide You can also usually select Create new Object to be able to see Section 6.6 on page... Objects screens to apply security settings such as firewall, IDP, remote management, antivirus, and application patrol.
... 6 Configuration Basics objects whenever the interface's IP address settings change an Ethernet interface's IP address, the ZyWALL automatically updates the rules or settings that use the interface-based, LAN subnet address object. Figure 62 Zones... DMZ) A zone is an overview of zones, interfaces, and physical ports in configuring other features. 96 ZyWALL USG 2000 User's Guide You can also usually select Create new Object to be able to see Section 6.6 on page... Objects screens to apply security settings such as firewall, IDP, remote management, antivirus, and application patrol.
User Guide
Page 101
Then it defragments them . ZyWALL USG 2000 User's Guide 101 As soon as one of the ZyWALL's interfaces. You can override this and have their own ...option (see if the packets are destined for example the firewall check. Figure 65 Routing Table Checking Flow Enhancements 1 Direct-connected Subnets: The ZyWALL first checks to see Section 15.1 on to the other...table.The checking flow is from the previous version. 6.4.2 Routing Table Checking Flow Enhancements When the ZyWALL receives packets it examines the packets and determines how to bottom. The following figure shows how the ...
Then it defragments them . ZyWALL USG 2000 User's Guide 101 As soon as one of the ZyWALL's interfaces. You can override this and have their own ...option (see if the packets are destined for example the firewall check. Figure 65 Routing Table Checking Flow Enhancements 1 Direct-connected Subnets: The ZyWALL first checks to see Section 15.1 on to the other...table.The checking flow is from the previous version. 6.4.2 Routing Table Checking Flow Enhancements When the ZyWALL receives packets it examines the packets and determines how to bottom. The following figure shows how the ...
User Guide
Page 107
... PREREQUISITES Interfaces 6.5.8 Zones See Section 6.2 on page 96 for the new zone. When you create a zone, the ZyWALL does not create any firewall rules, assign an IDP profile, or configure remote management for background information. Zones cannot overlap. ZyWALL USG 2000 User's Guide 107 Chapter 6 Configuration Basics 6.5.7 Static Routes Use static routes to tell the...
... PREREQUISITES Interfaces 6.5.8 Zones See Section 6.2 on page 96 for the new zone. When you create a zone, the ZyWALL does not create any firewall rules, assign an IDP profile, or configure remote management for background information. Zones cannot overlap. ZyWALL USG 2000 User's Guide 107 Chapter 6 Configuration Basics 6.5.7 Static Routes Use static routes to tell the...
User Guide
Page 108
...-ZyWALL firewall rules. Add an entry. 2 Name the entry. 3 Select the WAN interface that are redirected by NAT, it does not check the to a HTTP proxy server at IP address 192.168.3.80. 1 Click Configuration > Network > HTTP Redirect. 2 Add an entry. 108 ZyWALL USG 2000 ...User's Guide You could configure a NAT rule to forwards FTP sessions from your users needs to a proxy server. MENU ITEM(S) Configuration > Network > HTTP Redirect PREREQUISITES Interfaces Example: Suppose you have the ZyWALL transparently forward HTTP (web) traffic to ...
...-ZyWALL firewall rules. Add an entry. 2 Name the entry. 3 Select the WAN interface that are redirected by NAT, it does not check the to a HTTP proxy server at IP address 192.168.3.80. 1 Click Configuration > Network > HTTP Redirect. 2 Add an entry. 108 ZyWALL USG 2000 ...User's Guide You could configure a NAT rule to forwards FTP sessions from your users needs to a proxy server. MENU ITEM(S) Configuration > Network > HTTP Redirect PREREQUISITES Interfaces Example: Suppose you have the ZyWALL transparently forward HTTP (web) traffic to ...
User Guide
Page 109
... can access the network. MENU ITEM(S) Configuration > Firewall Zones, schedules, users, user groups, addresses (source, PREREQUISITES destination), address groups (source, destination), services, service groups ZyWALL USG 2000 User's Guide 109 Policy PREREQUISITES Addresses, services, endpoint... security objects, users, authentication methods 6.5.14 Firewall The firewall controls the travel of the HTTP proxy server. 6 ...
... can access the network. MENU ITEM(S) Configuration > Firewall Zones, schedules, users, user groups, addresses (source, PREREQUISITES destination), address groups (source, destination), services, service groups ZyWALL USG 2000 User's Guide 109 Policy PREREQUISITES Addresses, services, endpoint... security objects, users, authentication methods 6.5.14 Firewall The firewall controls the travel of the HTTP proxy server. 6 ...
User Guide
Page 110
... two sites over the Internet or any insecure network that uses TCP/IP for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall 110 ZyWALL USG 2000 User's Guide MENU ITEM(S) Configuration > VPN > IPSec VPN; You could configure a firewall rule to allow VoIP sessions from the DMZ zone to the LAN1 zone, and add...
... two sites over the Internet or any insecure network that uses TCP/IP for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall 110 ZyWALL USG 2000 User's Guide MENU ITEM(S) Configuration > VPN > IPSec VPN; You could configure a firewall rule to allow VoIP sessions from the DMZ zone to the LAN1 zone, and add...
User Guide
Page 111
...), addresses (local network, remote network, NAT, IP pool for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall WHERE USED The IPSec VPN connection used for L2TP VPN can leave the source, destination and log settings at the default.... remote users use the L2TP and IPSec client software included with their computers' operating systems to securely connect to use application patrol. ZyWALL USG 2000 User's Guide 111 MENU ITEM(S) Configuration > AppPatrol Registration, zones, Schedules, users, user groups, addresses PREREQUISITES (source, destination), ...
...), addresses (local network, remote network, NAT, IP pool for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall WHERE USED The IPSec VPN connection used for L2TP VPN can leave the source, destination and log settings at the default.... remote users use the L2TP and IPSec client software included with their computers' operating systems to securely connect to use application patrol. ZyWALL USG 2000 User's Guide 111 MENU ITEM(S) Configuration > AppPatrol Registration, zones, Schedules, users, user groups, addresses PREREQUISITES (source, destination), ...
User Guide
Page 113
ZyWALL USG 2000 User's Guide 113 MENU ITEM(S) Configuration > Device HA PREREQUISITES Interfaces (with a static ... user account for Bill if you created. 6.5.23 Anti-Spam Use anti-spam to detect and take over if a master ZyWALL fails. Click the Add icon to go to the screen where you can configure a category-based profile. 4 Name the ...the Arts/Entertainment category (you need to click Advanced to display it) and click OK. 8 Click General to go to -ZyWALL firewall Example: See Chapter 7 on spam mail. MENU ITEM(S) Configuration > Anti-X > Anti-Spam PREREQUISITES Zones 6.5.24 Device HA To...
ZyWALL USG 2000 User's Guide 113 MENU ITEM(S) Configuration > Device HA PREREQUISITES Interfaces (with a static ... user account for Bill if you created. 6.5.23 Anti-Spam Use anti-spam to detect and take over if a master ZyWALL fails. Click the Add icon to go to the screen where you can configure a category-based profile. 4 Name the ...the Arts/Entertainment category (you need to click Advanced to display it) and click OK. 8 Click General to go to -ZyWALL firewall Example: See Chapter 7 on spam mail. MENU ITEM(S) Configuration > Anti-X > Anti-Spam PREREQUISITES Zones 6.5.24 Device HA To...