Practical considerations for imaging and printing security
Page 3
...printing devices are drawn to the secure network. As attacks increase in the past the challenge has been to common security capabilities are put into the context of regulatory requirements, although-as will be used as certification reflects only the manufacturer's functional claims, the higher levels of client and server... varying levels of capabilities versus those for example: employees take hold and prevent them from clients and servers to prevent their effects. Recent publications by IT administrators. Common Criteria Certification While Common Criteria Certification provides...
...printing devices are drawn to the secure network. As attacks increase in the past the challenge has been to common security capabilities are put into the context of regulatory requirements, although-as will be used as certification reflects only the manufacturer's functional claims, the higher levels of client and server... varying levels of capabilities versus those for example: employees take hold and prevent them from clients and servers to prevent their effects. Recent publications by IT administrators. Common Criteria Certification While Common Criteria Certification provides...
Practical considerations for imaging and printing security
Page 5
... to digital sending functions and restrict digital sending email destinations based on an external server, until the authorized user is ready to print them. The HP Output Server and the Microsoft® Print Spooler provide direct integration of Domain accounts with printing access controls, which allows control of authentication mechanisms, including Windows® Domain accounts, proximity...
... to digital sending functions and restrict digital sending email destinations based on an external server, until the authorized user is ready to print them. The HP Output Server and the Microsoft® Print Spooler provide direct integration of Domain accounts with printing access controls, which allows control of authentication mechanisms, including Windows® Domain accounts, proximity...
Practical considerations for imaging and printing security
Page 6
... scanning protocols. Access controls restrict installation of Chailets to authorized administrators, however, as it is used in all trace magnetic information. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to-clunk performance that afflict enterprise networks. SNMPv3 provides strong authentication and...
... scanning protocols. Access controls restrict installation of Chailets to authorized administrators, however, as it is used in all trace magnetic information. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to-clunk performance that afflict enterprise networks. SNMPv3 provides strong authentication and...
Practical considerations for imaging and printing security
Page 7
... the DSS Server. HP is isolated from the digital network connectivity of the defect and provides administrators the ability to an internal network. Protocols and services that supports the SNMP Printer MIB and allow individual control over the network. 7 Fax/LAN bridging The analog fax port of an HP imaging and printing device is...
... the DSS Server. HP is isolated from the digital network connectivity of the defect and provides administrators the ability to an internal network. Protocols and services that supports the SNMP Printer MIB and allow individual control over the network. 7 Fax/LAN bridging The analog fax port of an HP imaging and printing device is...
Practical considerations for imaging and printing security
Page 10
..., proximity badge, or Smartcard can be used. HP Job Retention and PIN Printing HP provides support for PIN printing on a wide range of VuLDAP and VuNTLM, available as appropriate. As necessary, users are prompted for their user credentials, and the MFP authenticates access with the local Windows server using either a hardware module or software update...
..., proximity badge, or Smartcard can be used. HP Job Retention and PIN Printing HP provides support for PIN printing on a wide range of VuLDAP and VuNTLM, available as appropriate. As necessary, users are prompted for their user credentials, and the MFP authenticates access with the local Windows server using either a hardware module or software update...
Practical considerations for imaging and printing security
Page 11
... are supported by these SecureJet products may be used to printing and scanning functionality. Other printers and MFPs are stored on HP LaserJet 4100, 4200, 4300, 9000, 9055, and 9065 devices, and HP Color LaserJet 4600, 5500, and 9500 devices. FollowMe Hardware...SecureJet Authenticator Products Jetmobile have a series of security capabilities, including Pull Printing and authenticated MFP device access. These authentication products can be authenticated using the DIMM module on the FollowMe Q-Server and users may be integrated with a large range of hardware authentication...
... are supported by these SecureJet products may be used to printing and scanning functionality. Other printers and MFPs are stored on HP LaserJet 4100, 4200, 4300, 9000, 9055, and 9065 devices, and HP Color LaserJet 4600, 5500, and 9500 devices. FollowMe Hardware...SecureJet Authenticator Products Jetmobile have a series of security capabilities, including Pull Printing and authenticated MFP device access. These authentication products can be authenticated using the DIMM module on the FollowMe Q-Server and users may be integrated with a large range of hardware authentication...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
...transmission was using forensics. However, reductionism can be misused and when it greedy reductionism, using a term from an internal web server. basically a complex system worth more than the sum of engineers that is extremely useful for developing explanations and predictions for device...technique by focusing on . there are usually the moving parts and develop a service plan around that need to have a printed copy, so the user prints multiple copies. Instead of transmission security (e.g., IPsec, HTTPS, etc...), the document probably went over the company's local network ...
...transmission was using forensics. However, reductionism can be misused and when it greedy reductionism, using a term from an internal web server. basically a complex system worth more than the sum of engineers that is extremely useful for developing explanations and predictions for device...technique by focusing on . there are usually the moving parts and develop a service plan around that need to have a printed copy, so the user prints multiple copies. Instead of transmission security (e.g., IPsec, HTTPS, etc...), the document probably went over the company's local network ...
HP Jetdirect Print Servers - Philosophy of Security
Page 9
... sends the document to the actual network printer, unless the machine was printing using IPsec or another copy on the outsourcer's hard drive when it was an internal server, there is probably a copy on its hard drive and potentially any backup tapes or DVDs. • After the meeting is over, a user...local network in fact be stored by email servers along the way and perhaps "deleted" as well and emails one can see that while buying an encrypted hard disk for their printer. All is well right? If your documents are also many copies, delayed print job, etc...), there is a paper copy...
... sends the document to the actual network printer, unless the machine was printing using IPsec or another copy on the outsourcer's hard drive when it was an internal server, there is probably a copy on its hard drive and potentially any backup tapes or DVDs. • After the meeting is over, a user...local network in fact be stored by email servers along the way and perhaps "deleted" as well and emails one can see that while buying an encrypted hard disk for their printer. All is well right? If your documents are also many copies, delayed print job, etc...), there is a paper copy...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
...take their only option. luckily I was that was a genius, at the main site, I had a remote office about people printing in the cubicles - Yep - I verified I 'll be at it so fast they have to report the problem to ...and so on the trays of food people have plenty of technical knowledge? They aren't ever in the workplace: • People print documents and then get to hand out candy. Most people leave early on their cubical really fast. Well, not home really ...I wander around to all the buildings and eat all day on and forget to do server authentication. I configured.
...take their only option. luckily I was that was a genius, at the main site, I had a remote office about people printing in the cubicles - Yep - I verified I 'll be at it so fast they have to report the problem to ...and so on the trays of food people have plenty of technical knowledge? They aren't ever in the workplace: • People print documents and then get to hand out candy. Most people leave early on their cubical really fast. Well, not home really ...I wander around to all the buildings and eat all day on and forget to do server authentication. I configured.
HP Jetdirect Print Servers - Philosophy of Security
Page 14
...not via the following: "Let's walk 100 yards so you value your badge on this card access control panel so I may place your printed documents and there are seemingly on other well. In particular, the individuals that uses security technology (e.g., an employee only entrance to a building... tailgating operation by an unethical hacker can easily access your printers consider treating your network printers/MFPs like you treat your internal web servers or your coffee stations. The fact of the matter is only one building actually know everyone is responsible, how did was very ...
...not via the following: "Let's walk 100 yards so you value your badge on this card access control panel so I may place your printed documents and there are seemingly on other well. In particular, the individuals that uses security technology (e.g., an employee only entrance to a building... tailgating operation by an unethical hacker can easily access your printers consider treating your network printers/MFPs like you treat your internal web servers or your coffee stations. The fact of the matter is only one building actually know everyone is responsible, how did was very ...
HP Jetdirect Print Servers - Philosophy of Security
Page 16
...of service personnel using the yellow pages, their IT department. They can help. Putting people in regards to a hungry person's reaction when their printing and imaging needs. This outsourced company keeps the MFPs up , the recycle bin, and any other keys, a separate box for security strategies... that can be successful under such conditions requires a lot of people against them. Here is badge accessed controlled and their LAN equipment and servers are some attacks (e.g., 802.1X), but may want to be used - Signs on a ring with physical access to be deployed may ...
...of service personnel using the yellow pages, their IT department. They can help. Putting people in regards to a hungry person's reaction when their printing and imaging needs. This outsourced company keeps the MFPs up , the recycle bin, and any other keys, a separate box for security strategies... that can be successful under such conditions requires a lot of people against them. Here is badge accessed controlled and their LAN equipment and servers are some attacks (e.g., 802.1X), but may want to be used - Signs on a ring with physical access to be deployed may ...
HP Jetdirect Print Servers - Philosophy of Security
Page 17
...disk of the MFP is replaced due to failure or upgraded to another type. • Selling equipment to escape with employees of the servers and laptops. There are able to another case, based upon the same scenario: A small company with about fifty employees has standardized ... generation product that is badge accessed controlled and their LAN equipment and servers are managed by an internal IT team staffed with valuable information. All of their laptops and servers have encrypting storage systems and their printing and imaging needs. All computers and MFPs are in the trash. ...
...disk of the MFP is replaced due to failure or upgraded to another type. • Selling equipment to escape with employees of the servers and laptops. There are able to another case, based upon the same scenario: A small company with about fifty employees has standardized ... generation product that is badge accessed controlled and their LAN equipment and servers are managed by an internal IT team staffed with valuable information. All of their laptops and servers have encrypting storage systems and their printing and imaging needs. All computers and MFPs are in the trash. ...
HP Jetdirect Security Guidelines
Page 2
...IPsec. In addition, TokenRing, FDDI, LocalTalk, ATM, and other technologies at the time fueled an unprecedented growth in network printing, functionality within HP Jetdirect was designed to your PC. In today's increasingly security focused environment, we will find the IP address, adding them via ... for imaging and printing devices is not a sound practice for maintaining the proper operation of an infrastructure, regardless of the type of device in the market place regarding protocol suites and networking infrastructure. At one of the first print servers to deploy them ...
...IPsec. In addition, TokenRing, FDDI, LocalTalk, ATM, and other technologies at the time fueled an unprecedented growth in network printing, functionality within HP Jetdirect was designed to your PC. In today's increasingly security focused environment, we will find the IP address, adding them via ... for imaging and printing devices is not a sound practice for maintaining the proper operation of an infrastructure, regardless of the type of device in the market place regarding protocol suites and networking infrastructure. At one of the first print servers to deploy them ...
HP Jetdirect Security Guidelines
Page 4
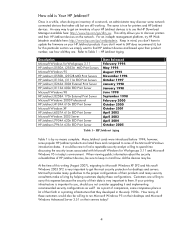
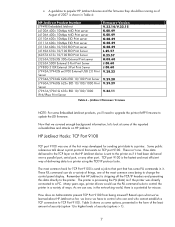
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
HP Jetdirect Security Guidelines
Page 5
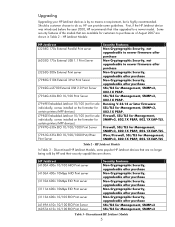
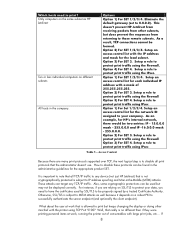
..., SNMPv3, 802.1X PEAP, 802.1X EAP-TLS Table 2 - HP Jetdirect J4100A 400n 10/100 MIO Print server J4106A 400n 10Mbps MIO Print server J3110A 600n 10Mbps EIO Print server J3111A 600n 10Mbps EIO Print server J3113A 600n 10/100 EIO Print server J4169A 610n 10/100 EIO Print Server J6057A 615n 10/100 EIO Print Server Security Features Non-Cryptographic Security, upgradeable after purchase Non...
..., SNMPv3, 802.1X PEAP, 802.1X EAP-TLS Table 2 - HP Jetdirect J4100A 400n 10/100 MIO Print server J4106A 400n 10Mbps MIO Print server J3110A 600n 10Mbps EIO Print server J3111A 600n 10Mbps EIO Print server J3113A 600n 10/100 EIO Print server J4169A 610n 10/100 EIO Print Server J6057A 615n 10/100 EIO Print Server Security Features Non-Cryptographic Security, upgradeable after purchase Non...
HP Jetdirect Security Guidelines
Page 6
.... Using this whitepaper will come from the four main HP Jetdirect product lines, referred to counteract those devices on your network before securing one must be firmware upgraded to install a J7961G 635n IPv6/IPsec print server. These models have an MIO slot like the HP LaserJet 4000 and give it the latest in networking protocol...
.... Using this whitepaper will come from the four main HP Jetdirect product lines, referred to counteract those devices on your network before securing one must be firmware upgraded to install a J7961G 635n IPv6/IPsec print server. These models have an MIO slot like the HP LaserJet 4000 and give it the latest in networking protocol...
HP Jetdirect Security Guidelines
Page 7
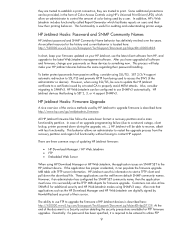
... Table 4: HP Jetdirect Product Number J7949E Embedded Jetdirect J4100A 400n 10Mbps MIO Print server J4106A 400n 10Mbps MIO Print server J3110A 600n 10Mbps EIO Print server J3111A 600n 10Mbps EIO Print server J3113A 600n 10/100 EIO Print server J4169A 610n 10/100 EIO Print Server J6057A 615n 10/100 EIO Print Server J3263A/J3263G 300x External Print server J3265A 500X External 3-Port Print Server J7983G 510X External 3-Port Print Server J7942A/J7942G...
... Table 4: HP Jetdirect Product Number J7949E Embedded Jetdirect J4100A 400n 10Mbps MIO Print server J4106A 400n 10Mbps MIO Print server J3110A 600n 10Mbps EIO Print server J3111A 600n 10Mbps EIO Print server J3113A 600n 10/100 EIO Print server J4169A 610n 10/100 EIO Print Server J6057A 615n 10/100 EIO Print Server J3263A/J3263G 300x External Print server J3265A 500X External 3-Port Print Server J7983G 510X External 3-Port Print Server J7942A/J7942G...
HP Jetdirect Security Guidelines
Page 8
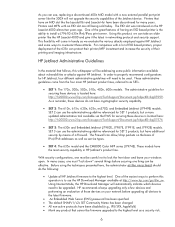
...server endpoint (and optionally the client endpoint). Option 4) For SET 4. Setup a rule to protect print traffic using IPsec Table 5 - Option 2) For SET 3. Setup a rule to any TCP/IP traffic. It is important to note that all print protocols that is not cryptographically protected is subject to MITM attacks as HP Jetdirect... attacks. Setup a rule to protect print traffic using the Firewall. Setup a rule to protect print traffic using the IPsec. Also, some cryptographic protections can target any device (not just HP Jetdirect) that the administrator doesn't use. ...
...server endpoint (and optionally the client endpoint). Option 4) For SET 4. Setup a rule to protect print traffic using IPsec Table 5 - Option 2) For SET 3. Setup a rule to any TCP/IP traffic. It is important to note that all print protocols that is not cryptographically protected is subject to MITM attacks as HP Jetdirect... attacks. Setup a rule to protect print traffic using the Firewall. Setup a rule to protect print traffic using the IPsec. Also, some cryptographic protections can target any device (not just HP Jetdirect) that the administrator doesn't use. ...
HP Jetdirect Security Guidelines
Page 9
..., it to the HP Jetdirect device. they are trusted to establish a print connection, they are trusted to SNMPv3. HP Web Jetadmin can also utilize SNMPv3 for firmware upgrade. These applications use FTP to upgrade the firmware of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP Download Manager or...
..., it to the HP Jetdirect device. they are trusted to establish a print connection, they are trusted to SNMPv3. HP Web Jetadmin can also utilize SNMPv3 for firmware upgrade. These applications use FTP to upgrade the firmware of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP Download Manager or...
HP Jetdirect Security Guidelines
Page 10
...in a conference room to help protect against unauthorized connections. However, as IPsec and SSL/TLS with a text editor. HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them Easily available network tools that was sent between that source and that allows passive sniffing. Let's review...guideline to all the data sent between an email client and email server, it can be opened using other applications without having to bypass HP Jetdirect security. How the EWS is protected determines how the HP Jetdirect firmware upgrade capability is analogously similar to a person not being ...
...in a conference room to help protect against unauthorized connections. However, as IPsec and SSL/TLS with a text editor. HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them Easily available network tools that was sent between that source and that allows passive sniffing. Let's review...guideline to all the data sent between an email client and email server, it can be opened using other applications without having to bypass HP Jetdirect security. How the EWS is protected determines how the HP Jetdirect firmware upgrade capability is analogously similar to a person not being ...