Jetdirect J2550A Setup - HP
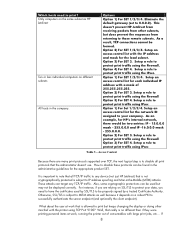
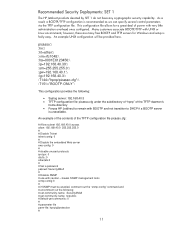
Jetdirect J2550A Setup

View Results Below
Free HP Jetdirect J2550A manuals!
Problems with HP Jetdirect J2550A?
Ask a Question
Free HP Jetdirect J2550A manuals!
Problems with HP Jetdirect J2550A?
Ask a Question
Related Manual Pages
Similar Questions
How Do I Setup An Hp Jetdirect 175x
(Posted by brucedonnab 10 years ago)
I Can Not Connect It With Hp 175x.setup How Can I Connect It When There Is No
(Posted by jacob0212 12 years ago)