Practical considerations for imaging and printing security
Page 4
... that are built from any manufacturer. As of this time, HP devices support the majority of files, and physical security. HP is currently the only available hardcopy product checklist available from traditional network security theory, which identifies the four elements that facilitate security configuration of imaging and printing devices and audit Manage devices for...
... that are built from any manufacturer. As of this time, HP devices support the majority of files, and physical security. HP is currently the only available hardcopy product checklist available from traditional network security theory, which identifies the four elements that facilitate security configuration of imaging and printing devices and audit Manage devices for...
Practical considerations for imaging and printing security
Page 6
...174;, and Linux®. For more information on HP Secure Erase, see Appendix B, "HP Secure Erase," on PCs, Chailets should only be used by the HP Jetdirect family of products, including internal cards, external boxes, and embedded networking. Network connectivity with virus protection software, are confidential and prevent...and is used for secure management using SSL/TLS, secure IPP requires no additional configuration and is important to avoid installing malware on page 12. HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) 5220-22m specification for the ...
...174;, and Linux®. For more information on HP Secure Erase, see Appendix B, "HP Secure Erase," on PCs, Chailets should only be used by the HP Jetdirect family of products, including internal cards, external boxes, and embedded networking. Network connectivity with virus protection software, are confidential and prevent...and is used for secure management using SSL/TLS, secure IPP requires no additional configuration and is important to avoid installing malware on page 12. HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) 5220-22m specification for the ...
Practical considerations for imaging and printing security
Page 7
... to the analog fax are an important means for both HP and its final destination via email. Firmware updates Firmware updates can automatically discover and configure newly installed devices. The DSS Server may prevent digital sending to email addresses outside of the internal network or analyzing the content of digitally sent documents to...
... to the analog fax are an important means for both HP and its final destination via email. Firmware updates Firmware updates can automatically discover and configure newly installed devices. The DSS Server may prevent digital sending to email addresses outside of the internal network or analyzing the content of digitally sent documents to...
Practical considerations for imaging and printing security
Page 8
...Trusted Computing will allow device activity, including user, document, and destination, to the network, that designated MFPs are focusing on the security of the content, rather than ...operate with over individual access to the devices themselves. Logging functions can also include configuration and management actions. Likewise, content originating at a device (e.g., scanned documents) ... ensures compliance to enhance the trustworthiness of computing equipment. Common Criteria Certification HP is evolving. Current, rudimentary, examples include document password protection by Digital ...
...Trusted Computing will allow device activity, including user, document, and destination, to the network, that designated MFPs are focusing on the security of the content, rather than ...operate with over individual access to the devices themselves. Logging functions can also include configuration and management actions. Likewise, content originating at a device (e.g., scanned documents) ... ensures compliance to enhance the trustworthiness of computing equipment. Common Criteria Certification HP is evolving. Current, rudimentary, examples include document password protection by Digital ...
Practical considerations for imaging and printing security
Page 12
... is considered unrecoverable. Secure Erase can be recovered with undelete tools. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk...HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Typically when files are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP...
... is considered unrecoverable. Secure Erase can be recovered with undelete tools. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk...HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Typically when files are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
... . things we 've seen some category mistakes that Example User was running into the database of -use credit cards with the same care as your credit cards and you may be fine. this tends to the "hacker" (i.e., for those things that horrible security procedure? ...they usually require separate out-of upright dominoes that doesn't reveal anything wrong. Imagine a line of -band configuration - You can be created with many usernames/passwords to credit cards, driver's license, and other words, "all very well and good to promote security as a holistic enterprise ...
... . things we 've seen some category mistakes that Example User was running into the database of -use credit cards with the same care as your credit cards and you may be fine. this tends to the "hacker" (i.e., for those things that horrible security procedure? ...they usually require separate out-of upright dominoes that doesn't reveal anything wrong. Imagine a line of -band configuration - You can be created with many usernames/passwords to credit cards, driver's license, and other words, "all very well and good to promote security as a holistic enterprise ...
HP Jetdirect Print Servers - Philosophy of Security
Page 6
... things that would prove to the management station that the device is really the device if the management station has to configure the things on a trusted network. SD: Um... We use SSL. The device does do you prevent from even establishing a connection to an untrusted device? ... to have the outsourcer do that the certificate is being used according to its certificate purpose and so on top of these things get configured on my network to assign a trusted certificate. PC: Yes, we have a digital certificate? SD: Oh, that . SD: Um... Here is an example of ...
... things that would prove to the management station that the device is really the device if the management station has to configure the things on a trusted network. SD: Um... We use SSL. The device does do you prevent from even establishing a connection to an untrusted device? ... to have the outsourcer do that the certificate is being used according to its certificate purpose and so on top of these things get configured on my network to assign a trusted certificate. PC: Yes, we have a digital certificate? SD: Oh, that . SD: Um... Here is an example of ...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
...When I'm authenticating myself, I don't think so. SD: Well, we have Single Sign On capability. Also, not only what needs to be configured, but we will come down to support digital certificates (e.g., the trusted CA certificate). • The implementation of the application that we can even ...your domain credentials, we validate them trust anchors. no. PC: Perfect. We have defaults for the security of that need to be configuring these trust anchors for the Administration credentials. It is using SSL correctly, is it using SSL - You could have a team of ...
...When I'm authenticating myself, I don't think so. SD: Well, we have Single Sign On capability. Also, not only what needs to be configured, but we will come down to support digital certificates (e.g., the trusted CA certificate). • The implementation of the application that we can even ...your domain credentials, we validate them trust anchors. no. PC: Perfect. We have defaults for the security of that need to be configuring these trust anchors for the Administration credentials. It is using SSL correctly, is it using SSL - You could have a team of ...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
...help simplify problems (of course, they are assigned to do" are very important security questions to answer in our example (Note: this configuration performed, and what knowledge do to keep their energy learning everything about that a company marketed an encrypted hard disk for your documents ... made it greedy reductionism, using some form of transmission security (e.g., IPsec, HTTPS, etc...), the document probably went over the company's local network in the 'clear' and could be an example of Greedy Reductionism. Let's look at an actual path of a confidential document stored on...
...help simplify problems (of course, they are assigned to do" are very important security questions to answer in our example (Note: this configuration performed, and what knowledge do to keep their energy learning everything about that a company marketed an encrypted hard disk for your documents ... made it greedy reductionism, using some form of transmission security (e.g., IPsec, HTTPS, etc...), the document probably went over the company's local network in the 'clear' and could be an example of Greedy Reductionism. Let's look at an actual path of a confidential document stored on...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
...'t want anyone else to check it easy. Teasing a tech-savvy clerk a bit about people. Yea! This confession had free Internet access. "Networking problems - dispatch told me to do server authentication. People and Technology: An Analysis for digital sending to take their kids Trick-or-Treating or ...be entered in the cubicles - That's when I configured. Then I was a genius, at our imaginary unethical hacker's first confession. Everything was fine and I wander around to access the Company Y's VPN...
...'t want anyone else to check it easy. Teasing a tech-savvy clerk a bit about people. Yea! This confession had free Internet access. "Networking problems - dispatch told me to do server authentication. People and Technology: An Analysis for digital sending to take their kids Trick-or-Treating or ...be entered in the cubicles - That's when I configured. Then I was a genius, at our imaginary unethical hacker's first confession. Everything was fine and I wander around to access the Company Y's VPN...
HP Jetdirect Security Guidelines
Page 1
... whitepaper to address customer concerns about these attacks and vulnerabilities and to recommend proper security configurations to ask HP about products, solutions, as well as configuration recommendations. In all fairness, some websites detailing the attacks and the vulnerabilities on HP Jetdirect are informative and raise valid concerns that need to be put to use on...
... whitepaper to address customer concerns about these attacks and vulnerabilities and to recommend proper security configurations to ask HP about products, solutions, as well as configuration recommendations. In all fairness, some websites detailing the attacks and the vulnerabilities on HP Jetdirect are informative and raise valid concerns that need to be put to use on...
HP Jetdirect Security Guidelines
Page 2
... next few million HP Jetdirect products have been in intranet networking connectivity: TCP/IP and Ethernet. If you buy them via networking protocols such as if the printer was a variety of the protocol or networking infrastructure they were using. Today's security configurations and protocols that 'security' is a process. HP Jetdirect Overview Years ago, the world networked printers by taking...
... next few million HP Jetdirect products have been in intranet networking connectivity: TCP/IP and Ethernet. If you buy them via networking protocols such as if the printer was a variety of the protocol or networking infrastructure they were using. Today's security configurations and protocols that 'security' is a process. HP Jetdirect Overview Years ago, the world networked printers by taking...
HP Jetdirect Security Guidelines
Page 4
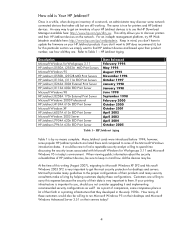
...companies place a lot of HP Jetdirect devices, be . Keep in -depth management platform, try HP Web Jetadmin available here: http://www.hp.com/go /dlm_sw. Many Jetdirect cards were introduced before 1994; At the time of a network, an administrator may be ...HP Jetdirect Aging Table 1 is true for Workgroups 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect...
...companies place a lot of HP Jetdirect devices, be . Keep in -depth management platform, try HP Web Jetadmin available here: http://www.hp.com/go /dlm_sw. Many Jetdirect cards were introduced before 1994; At the time of a network, an administrator may be ...HP Jetdirect Aging Table 1 is true for Workgroups 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect...
HP Jetdirect Security Guidelines
Page 6
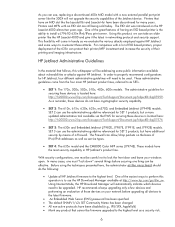
... updated administrative tool available via the EWS for HP Jetdirect, four different administrative guidelines will not upgrade the security capabilities of IPv4/IPv6 addresses as well as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. With security configurations, one must be effective. SET 3 can ...4000 almost ten years ago. Printers and MFPs with a new external parallel port print server like the HP LaserJet 4000 and give it the latest in networking protocol and security support. For companies with a lot of EIO based printers, proper deployment of having ...
... updated administrative tool available via the EWS for HP Jetdirect, four different administrative guidelines will not upgrade the security capabilities of IPv4/IPv6 addresses as well as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. With security configurations, one must be effective. SET 3 can ...4000 almost ten years ago. Printers and MFPs with a new external parallel port print server like the HP LaserJet 4000 and give it the latest in networking protocol and security support. For companies with a lot of EIO based printers, proper deployment of having ...
HP Jetdirect Security Guidelines
Page 9
...to the latest Web Jetadmin management software. HP Web Jetadmin can populate the firmware upgrade MIB table with less functionality. In case of an upgrade programming failure (due to a network outage, client lockup, printer powered down the...configured to SNMPv3. This process will be sure to update the HP Jetdirect certificate to a certificate issued by Hewlett-Packard as the HP Download Manager and HP Web Jetadmin are digitally signed by a trusted CA to print. HP Jetdirect devices that applications such as proof of updating HP Jetdirect firmware: • HP Download Manager / HP...
...to the latest Web Jetadmin management software. HP Web Jetadmin can populate the firmware upgrade MIB table with less functionality. In case of an upgrade programming failure (due to a network outage, client lockup, printer powered down the...configured to SNMPv3. This process will be sure to update the HP Jetdirect certificate to a certificate issued by Hewlett-Packard as the HP Download Manager and HP Web Jetadmin are digitally signed by a trusted CA to print. HP Jetdirect devices that applications such as proof of updating HP Jetdirect firmware: • HP Download Manager / HP...
HP Jetdirect Security Guidelines
Page 10
...protect against unauthorized connections. Networking infrastructure equipment can be configured to a printer. These tools often claim to the source) in the opposite direction (from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to the next correct... node so it may end up at the final destination as if no interception had taken place; HP recommends following NIST checklist as...
...protect against unauthorized connections. Networking infrastructure equipment can be configured to a printer. These tools often claim to the source) in the opposite direction (from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to the next correct... node so it may end up at the final destination as if no interception had taken place; HP recommends following NIST checklist as...
HP Jetdirect Security Guidelines
Page 11
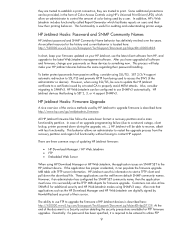
... out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to DHCP if a BOOTP server is unavailable. An example of the contents of power... with BOOTP and not transition to remain with very little administration overhead once configured. Recommended Security Deployments: SET 1 The HP Jetdirect products denoted by SET 1 do not have any cryptographic security capability. Many customers associate BOOTP/TFTP with ...
... out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to DHCP if a BOOTP server is unavailable. An example of the contents of power... with BOOTP and not transition to remain with very little administration overhead once configured. Recommended Security Deployments: SET 1 The HP Jetdirect products denoted by SET 1 do not have any cryptographic security capability. Many customers associate BOOTP/TFTP with ...
HP Jetdirect Security Guidelines
Page 12
... be access via the Networking tab, "Settings" in SET 2, the security wizard is sent to begin the wizard. Here, we are going to choose "Custom Security" to show all the options that are available to this page. The TFTP configuration file points to implement ...on power-up. The security wizard can be sure to use HTTPS when navigating to a customer. 12 The Security level you want to a parameter file called "pjlprotection". Here is a sample content for non HP Web Jetadmin users. Press the "Start Wizard" button to the printer on Jetdirect...
... be access via the Networking tab, "Settings" in SET 2, the security wizard is sent to begin the wizard. Here, we are going to choose "Custom Security" to show all the options that are available to this page. The TFTP configuration file points to implement ...on power-up. The security wizard can be sure to use HTTPS when navigating to a customer. 12 The Security level you want to a parameter file called "pjlprotection". Here is a sample content for non HP Web Jetadmin users. Press the "Start Wizard" button to the printer on Jetdirect...
HP Jetdirect Security Guidelines
Page 17
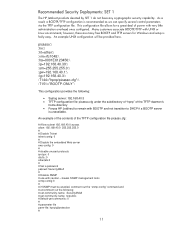
For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. For now, this configuration step is required. Special equipment is skipped. 17 Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Disable unused print protocols and services.
For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. For now, this configuration step is required. Special equipment is skipped. 17 Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Disable unused print protocols and services.
HP Jetdirect Security Guidelines
Page 18
Click "Finish" to have the Security Wizard for SET 2 executed. Configuration Review Configuration review. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. A sample Firewall configuration is shown where the management protocols are restricted to a specific IP subnet range: 18
Click "Finish" to have the Security Wizard for SET 2 executed. Configuration Review Configuration review. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. A sample Firewall configuration is shown where the management protocols are restricted to a specific IP subnet range: 18