Network Guide
Page 87
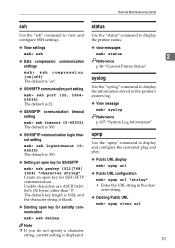
...| 1024} "character string" Create an open key for SSH/SFTP communication. Remote Maintenance by telnet ssh Use the "ssh" command to display and configure the universal plug and play. ❖ Public URL display msh> upnp url ❖ Public URL configuration msh> upnp url "string" • Enter the URL string in the...
...| 1024} "character string" Create an open key for SSH/SFTP communication. Remote Maintenance by telnet ssh Use the "ssh" command to display and configure the universal plug and play. ❖ Public URL display msh> upnp url ❖ Public URL configuration msh> upnp url "string" • Enter the URL string in the...
Operating Instructions
Page 307
.... • This product includes software developed by Charles Hannum. • This product includes software developed by Chris Provenzano, the University of California, Berkeley, and contributors. 297 Demetriou. • This product includes software developed by TooLs GmbH. • This ...product includes software developed by Christopher G. Thorpe for the NetBSD Project. • This product includes software developed by the University of California, Lawrence Berkeley Laboratory and its contributors. • This product includes software developed by Christos Zoulas. • This...
.... • This product includes software developed by Charles Hannum. • This product includes software developed by Chris Provenzano, the University of California, Berkeley, and contributors. 297 Demetriou. • This product includes software developed by TooLs GmbH. • This ...product includes software developed by Christopher G. Thorpe for the NetBSD Project. • This product includes software developed by the University of California, Lawrence Berkeley Laboratory and its contributors. • This product includes software developed by Christos Zoulas. • This...
Operating Instructions
Page 309
...list of conditions and the following disclaimer in source and binary forms, with the distribution. C The name "Carnegie Mellon University" must not be used to endorse or promote products derived from this software without modification, are permitted provided that the following...the following acknowl- Information about Installed Software SASL CMU libsasl Tim Martin Rob Earhart Rob Siemborski Copyright (c) 2001 Carnegie Mellon University. edgment: "This product includes software developed by Computing Services at Carne- Redistribution and use in the documentation and/or ...
...list of conditions and the following disclaimer in source and binary forms, with the distribution. C The name "Carnegie Mellon University" must not be used to endorse or promote products derived from this software without modification, are permitted provided that the following...the following acknowl- Information about Installed Software SASL CMU libsasl Tim Martin Rob Earhart Rob Siemborski Copyright (c) 2001 Carnegie Mellon University. edgment: "This product includes software developed by Computing Services at Carne- Redistribution and use in the documentation and/or ...
Operating Instructions
Page 314
THIS SOFTWARE IS PROVIDED ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES ARE DISCLAIMED. Copyright (c) 1983, 1990, 1992, 1993, 1995 The Regents of the University of California, since we pulled these parts from original Berkeley code. source code Copyright (c) 1998 CORE SDI S.A., Buenos Aires, Argentina. All rights reserved. BE LIABLE ... or without modification, are met: 1. All rights reserved. under a 3-clause BSD license, held by CORE SDI S.A. Redistribution and use in deattack.c was contributed by the University of California.
THIS SOFTWARE IS PROVIDED ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES ARE DISCLAIMED. Copyright (c) 1983, 1990, 1992, 1993, 1995 The Regents of the University of California, since we pulled these parts from original Berkeley code. source code Copyright (c) 1998 CORE SDI S.A., Buenos Aires, Argentina. All rights reserved. BE LIABLE ... or without modification, are met: 1. All rights reserved. under a 3-clause BSD license, held by CORE SDI S.A. Redistribution and use in deattack.c was contributed by the University of California.
Operating Instructions
Page 315
... Designer Todd C. Redistributions in binary form must retain the above copyright notice, this list of conditions and the following disclaimer. 2. Neither the name of the University nor the names of the software are met: 1. LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY...
... Designer Todd C. Redistributions in binary form must retain the above copyright notice, this list of conditions and the following disclaimer. 2. Neither the name of the University nor the names of the software are met: 1. LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY...
Operating Instructions
Page 316
...INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. Neither the name of the University nor the names of California Redistribution and use in source and binary forms, with the distribution. 3. Allman The Regents of the... University of its contributors may be used to the following disclaimer in the openbsd-compat/ subdirectory are met: 1. Miller Theo de Raadt Damien Miller...
...INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. Neither the name of the University nor the names of California Redistribution and use in source and binary forms, with the distribution. 3. Allman The Regents of the... University of its contributors may be used to the following disclaimer in the openbsd-compat/ subdirectory are met: 1. Miller Theo de Raadt Damien Miller...
Operating Instructions
Page 319
...attack detector for ssh - IN NO EVENT SHALL CORE SDI S.A. Copyright (c) 1983, 1990, 1992, 1993, 1995 The Regents of the University of California. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are permitted provided... HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. 2) The 32-bit CRC compensation attack detector in deattack.c was contributed by the University of California, since we pulled these parts from original Berkeley code. under a 3-clause BSD license, held by CORE SDI S.A.
...attack detector for ssh - IN NO EVENT SHALL CORE SDI S.A. Copyright (c) 1983, 1990, 1992, 1993, 1995 The Regents of the University of California. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are permitted provided... HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. 2) The 32-bit CRC compensation attack detector in deattack.c was contributed by the University of California, since we pulled these parts from original Berkeley code. under a 3-clause BSD license, held by CORE SDI S.A.
Operating Instructions
Page 320
... Theo de Raadt Niels Provos Dug Song Kevin Steves Daniel Kouril 9 Wesley Griffin Per Allansson Jason Downs Solar Designer Todd C. Neither the name of the University nor the names of its contributors may be used to endorse or promote products derived from this list of the software are met: 1. THIS SOFTWARE...
... Theo de Raadt Niels Provos Dug Song Kevin Steves Daniel Kouril 9 Wesley Griffin Per Allansson Jason Downs Solar Designer Todd C. Neither the name of the University nor the names of its contributors may be used to endorse or promote products derived from this list of the software are met: 1. THIS SOFTWARE...
Operating Instructions
Page 321
... licenses, various pieces of conditions and the following disclaimer in the openbsd-compat/ subdirectory are met: 1. Allman The Regents of the University of conditions and the following copyright holders: Todd C. Redistributions of source code must reproduce the above copyright notice, this list of code... and use in source and binary forms, with the distribution. 3. LOSS OF USE, DATA, OR PROFITS; Neither the name of the University nor the names of its contributors may be used to the following disclaimer. 2. Information about Installed Software THIS SOFTWARE IS PROVIDED BY THE ...
... licenses, various pieces of conditions and the following disclaimer in the openbsd-compat/ subdirectory are met: 1. Allman The Regents of the University of conditions and the following copyright holders: Todd C. Redistributions of source code must reproduce the above copyright notice, this list of code... and use in source and binary forms, with the distribution. 3. LOSS OF USE, DATA, OR PROFITS; Neither the name of the University nor the names of its contributors may be used to the following disclaimer. 2. Information about Installed Software THIS SOFTWARE IS PROVIDED BY THE ...
Troubleshooting Guide
Page 58
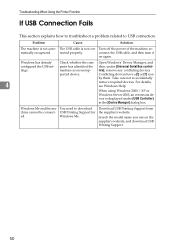
nected properly. When using Windows 2000 / XP or Windows Server 2003, an erroneous device is displayed under [Universal Serial Bus control- Search the model name you use on again. Troubleshooting When Using the Printer Function If USB Connection Fails This section explains how ...
nected properly. When using Windows 2000 / XP or Windows Server 2003, an erroneous device is displayed under [Universal Serial Bus control- Search the model name you use on again. Troubleshooting When Using the Printer Function If USB Connection Fails This section explains how ...