WNR1000 User Manual
Page 27
... covered in detail in terms of up to access your network. As a minimum, however, NETGEAR recommends using WEP with a compatible adapter to receive your wireless data transmissions well beyond your walls. Indoors, computers can allow anyone with Shared Key authentication. Chapter 2 Safeguarding Your Network The N150 Wireless Router WNR1000 provides highly effective security features, which are appropriate to...
... covered in detail in terms of up to access your network. As a minimum, however, NETGEAR recommends using WEP with a compatible adapter to receive your wireless data transmissions well beyond your walls. Indoors, computers can allow anyone with Shared Key authentication. Chapter 2 Safeguarding Your Network The N150 Wireless Router WNR1000 provides highly effective security features, which are appropriate to...
WNR1000 User Manual
Page 29
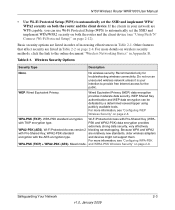
...document "Wireless Networking Basics" in Table 2-2 on page 2-9. WEP Shared Key authentication and WEP data encryption can use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/ WPA2 security on both the router and the client device (see "Configuring WEP Wireless Security... very effectively WPA2-PSK (AES). N150 Wireless Router WNR1000 User Manual • Use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/WPA2 security on both the router and the client device. Wireless Security Options Security Type Description None. and...
...document "Wireless Networking Basics" in Table 2-2 on page 2-9. WEP Shared Key authentication and WEP data encryption can use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/ WPA2 security on both the router and the client device (see "Configuring WEP Wireless Security... very effectively WPA2-PSK (AES). N150 Wireless Router WNR1000 User Manual • Use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/WPA2 security on both the router and the client device. Wireless Security Options Security Type Description None. and...
WNR1000 User Manual
Page 31
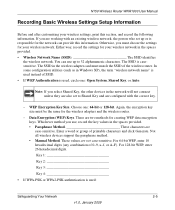
... used , circle one : 64-bit or 128-bit. WEP Encryption Key Size. Data Encryption (WEP) Keys. N150 Wireless Router WNR1000 User Manual Recording Basic Wireless Settings Setup Information Before and after customizing your wireless network in the spaces provided. • Wireless Network Name (SSID The SSID identifies the wireless network. Not all wireless devices support the passphrase method. • Manual Method. For 128...
... used , circle one : 64-bit or 128-bit. WEP Encryption Key Size. Data Encryption (WEP) Keys. N150 Wireless Router WNR1000 User Manual Recording Basic Wireless Settings Setup Information Before and after customizing your wireless network in the spaces provided. • Wireless Network Name (SSID The SSID identifies the wireless network. Not all wireless devices support the passphrase method. • Manual Method. For 128...
WNR1000 User Manual
Page 34
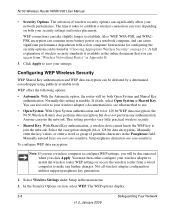
...Select the encryption strength (64 or 128 bit data encryption). N150 Wireless Router WNR1000 User Manual • Security Options. The time it fails, select Open System or Shared Key. You can be disconnected when you will try both your settings. ...wireless computer to match the wireless router WEP settings or access the wireless router from "Wireless Networking Basics" in the main menu. 2. A full explanation of printable characters in "Choosing Appropriate Wireless Security" on both Open System and Shared Key authentication. Configuring WEP Wireless Security WEP Shared Key...
...Select the encryption strength (64 or 128 bit data encryption). N150 Wireless Router WNR1000 User Manual • Security Options. The time it fails, select Open System or Shared Key. You can be disconnected when you will try both your settings. ...wireless computer to match the wireless router WEP settings or access the wireless router from "Wireless Networking Basics" in the main menu. 2. A full explanation of printable characters in "Choosing Appropriate Wireless Security" on both Open System and Shared Key authentication. Configuring WEP Wireless Security WEP Shared Key...
WNR1000 User Manual
Page 35
... as nETgear. These entries are available from the manufacturer. Configuring WPA-PSK and WPA2-PSK Wireless Security Wi-Fi Protected Access with key values. • Manual. Select the authentication type and encryption strength. 4. WPA-PSK uses TKIP (Temporal Key Integrity Protocol) data encryption, and WPA2-PSK uses AES (Advanced Encryption Standard) data encryption. N150 Wireless Router WNR1000...
... as nETgear. These entries are available from the manufacturer. Configuring WPA-PSK and WPA2-PSK Wireless Security Wi-Fi Protected Access with key values. • Manual. Select the authentication type and encryption strength. 4. WPA-PSK uses TKIP (Temporal Key Integrity Protocol) data encryption, and WPA2-PSK uses AES (Advanced Encryption Standard) data encryption. N150 Wireless Router WNR1000...
WNR1000 User Manual
Page 62
... provider gave you can select the Use Wildcards check box to save your Dynamic DNS account. 7. Enter the password (or key) for 4-6 Customizing Your Network Settings v1.0, January 2009 Select WAN Setup under Advanced in to log in the main menu. Enter the user name for... your network and computers against attacks and intrusions. Select the name of wildcards in resolving your host name. 6. Click Apply to activate this feature. The WAN Setup screen displays. N150 Wireless Router WNR1000 User Manual 2. If your Dynamic DNS provider allows...
... provider gave you can select the Use Wildcards check box to save your Dynamic DNS account. 7. Enter the password (or key) for 4-6 Customizing Your Network Settings v1.0, January 2009 Select WAN Setup under Advanced in to log in the main menu. Enter the user name for... your network and computers against attacks and intrusions. Select the name of wildcards in resolving your host name. 6. Click Apply to activate this feature. The WAN Setup screen displays. N150 Wireless Router WNR1000 User Manual 2. If your Dynamic DNS provider allows...
WNR1000 User Manual
Page 119
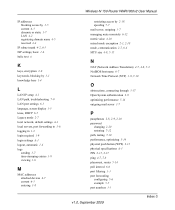
...6-2 ISP settings, basic 1-5 italic text xi K keys, encryption 2-9 keywords, blocking by 3-1 knowledge base 1-4 L LAN IP setup 4-1 LAN path, troubleshooting 7-9 LAN port settings 6-2 lease, DHCP 6-4 Legacy mode 2-7 local network, default settings A-1 local servers, port forwarding to... 2-18 spoofing 7-7 N150 Wireless Router WNR1000 User Manual mail server, outgoing 3-7 managing router remotely 6-10 metric value 4-10 mixed mode encryption 2-3, 2-10 mode, communication 2-7, 6-3 MTU size 4-8, 5-15 N NAT (Network Address Translation) 4-7, 4-8, 5-2 NetBIOS host name 6-5 Network Time Protocol (NTP) ...
...6-2 ISP settings, basic 1-5 italic text xi K keys, encryption 2-9 keywords, blocking by 3-1 knowledge base 1-4 L LAN IP setup 4-1 LAN path, troubleshooting 7-9 LAN port settings 6-2 lease, DHCP 6-4 Legacy mode 2-7 local network, default settings A-1 local servers, port forwarding to... 2-18 spoofing 7-7 N150 Wireless Router WNR1000 User Manual mail server, outgoing 3-7 managing router remotely 6-10 metric value 4-10 mixed mode encryption 2-3, 2-10 mode, communication 2-7, 6-3 MTU size 4-8, 5-15 N NAT (Network Address Translation) 4-7, 4-8, 5-2 NetBIOS host name 6-5 Network Time Protocol (NTP) ...
WNR1000 User Manual
Page 120
N150 Wireless Router WNR1000 User Manual port triggering configuring 5-9 example 5-3 portmap table 5-13 power adapter specifications A-3 Power light, troubleshooting and 7-2 Powerline HD products 5-17...requirements, speed 5-17 reserved IP adresses 4-4 Resource CD 1-1 restarting network 7-1 restoring configuration 6-6 default factory settings 7-12 restoring firmware 7-3 restricting access by MAC address 2-18 revision history xiii RIP (Router Information Protocol) direction 4-2 route name 4-10 router PIN 2-15, 2-16 router status, viewing 6-1 S scheduling blocking 3-5 secondary DNS server 1-7, 1-...
N150 Wireless Router WNR1000 User Manual port triggering configuring 5-9 example 5-3 portmap table 5-13 power adapter specifications A-3 Power light, troubleshooting and 7-2 Powerline HD products 5-17...requirements, speed 5-17 reserved IP adresses 4-4 Resource CD 1-1 restarting network 7-1 restoring configuration 6-6 default factory settings 7-12 restoring firmware 7-3 restricting access by MAC address 2-18 revision history xiii RIP (Router Information Protocol) direction 4-2 route name 4-10 router PIN 2-15, 2-16 router status, viewing 6-1 S scheduling blocking 3-5 secondary DNS server 1-7, 1-...
WNR1000 User Manual
Page 121
N150 Wireless Router WNR1000 User Manual T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-9 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-10 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii transfer time (backing up) 5-18 troubleshooting 7-1 trusted user 3-2 typographical conventions xi U Universal Plug and...
N150 Wireless Router WNR1000 User Manual T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-9 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-10 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii transfer time (backing up) 5-18 troubleshooting 7-1 trusted user 3-2 typographical conventions xi U Universal Plug and...
WNR1000v3 Setup Manual
Page 28
... WPS capable devices. The first method is WEP with shared-key authentication. The only security setting that you connect subsequent devices, even if the connection fails, the WPS LED remains on because wireless security is made, when the LED stops blinking it will remain... the wireless router's Internet LED blink, indicating communication with WPS is explained here. You should see the User Manual. You can be connected to your wireless network quickly and simply by using WPS. On your network consists of WPS capable devices and non-WPS capable devices, NETGEAR suggests ...
... WPS capable devices. The first method is WEP with shared-key authentication. The only security setting that you connect subsequent devices, even if the connection fails, the WPS LED remains on because wireless security is made, when the LED stops blinking it will remain... the wireless router's Internet LED blink, indicating communication with WPS is explained here. You should see the User Manual. You can be connected to your wireless network quickly and simply by using WPS. On your network consists of WPS capable devices and non-WPS capable devices, NETGEAR suggests ...
WNR1000v2 User Manual
Page 29
... is your computers and files. Chapter 2 Safeguarding Your Network The Wireless-N 150 Router Model WNR1000v2 provides highly effective security features, which are appropriate to break into your network. This chapter includes the following sections: • "Choosing Appropriate Wireless Security" • "Recording Basic Wireless Settings Setup Information" on page 2-5 • "Changing Wireless Security Settings" on page 2-6 • "Viewing Advanced...
... is your computers and files. Chapter 2 Safeguarding Your Network The Wireless-N 150 Router Model WNR1000v2 provides highly effective security features, which are appropriate to break into your network. This chapter includes the following sections: • "Choosing Appropriate Wireless Security" • "Recording Basic Wireless Settings Setup Information" on page 2-5 • "Changing Wireless Security Settings" on page 2-6 • "Viewing Advanced...
WNR1000v2 User Manual
Page 31
...more information, see "Configuring WEP Wireless Security" on page 2-8. Safeguarding Your Network 2-3 v1.0, September 2009 WEP. and WPA2-PSK Wireless Security" on both the router and the client device (see "Configuring WPA-PSK WPA-PSK (TKIP) + WPA2-PSK (AES). Wireless-N 150 Router WNR1000v2 User Manual • ...Use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/WPA2 security on both the router and the client device. WEP Shared Key authentication and WEP data encryption can ...
...more information, see "Configuring WEP Wireless Security" on page 2-8. Safeguarding Your Network 2-3 v1.0, September 2009 WEP. and WPA2-PSK Wireless Security" on both the router and the client device (see "Configuring WPA-PSK WPA-PSK (TKIP) + WPA2-PSK (AES). Wireless-N 150 Router WNR1000v2 User Manual • ...Use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/WPA2 security on both the router and the client device. WEP Shared Key authentication and WEP data encryption can ...
WNR1000v2 User Manual
Page 33
.... For 128-bit WEP, enter 26 hexadecimal digits. Wireless-N 150 Router WNR1000v2 User Manual Recording Basic Wireless Settings Setup Information Before and after customizing your wireless network in the spaces provided. • Wireless Network Name (SSID The SSID identifies the wireless network. Either way, record the settings for the network can use , record the key values in the spaces provided. • Passphrase...
.... For 128-bit WEP, enter 26 hexadecimal digits. Wireless-N 150 Router WNR1000v2 User Manual Recording Basic Wireless Settings Setup Information Before and after customizing your wireless network in the spaces provided. • Wireless Network Name (SSID The SSID identifies the wireless network. Either way, record the settings for the network can use , record the key values in the spaces provided. • Passphrase...
WNR1000v2 User Manual
Page 36
... - Also, WEP, WPA-PSK, and WPA2PSK encryption can consume more battery power on a notebook computer, and can join the network. Wireless-N 150 Router WNR1000v2 User Manual - The time it fails, select Open System or Shared Key. Click Apply to establish. WEP offers the following options: • Automatic. With Open System authentication and 64 or 128...
... - Also, WEP, WPA-PSK, and WPA2PSK encryption can consume more battery power on a notebook computer, and can join the network. Wireless-N 150 Router WNR1000v2 User Manual - The time it fails, select Open System or Shared Key. Click Apply to establish. WEP offers the following options: • Automatic. With Open System authentication and 64 or 128...
WNR1000v2 User Manual
Page 37
... match the wireless router WEP settings or access the wireless router from a wired computer to activate. 5. Enter 10 hexadecimal digits (any further changes. You must be disconnected when you click Apply. The WEP options display. . The passphrase is case-sensitive. Safeguarding Your Network 2-9 v1.0, September 2009 Figure 2-3 3. In the Security Options section, select WEP. Wireless-N 150 Router WNR1000v2...
... match the wireless router WEP settings or access the wireless router from a wired computer to activate. 5. Enter 10 hexadecimal digits (any further changes. You must be disconnected when you click Apply. The WEP options display. . The passphrase is case-sensitive. Safeguarding Your Network 2-9 v1.0, September 2009 Figure 2-3 3. In the Security Options section, select WEP. Wireless-N 150 Router WNR1000v2...
WNR1000v2 User Manual
Page 38
...whether newer drivers are relatively new standards, older wireless adapters and devices might not be compatible with older adapters. Furthermore, client software is case-sensitive. 2-10 v1.0, September 2009 Safeguarding Your Network Windows XP with Pre-Shared Key (WPA-PSK and WPA2-PSK) data encryption ...it is easiest to implement, but it allows clients using either WPA-PSK or WPA2-PSK. 3. Wireless-N 150 Router WNR1000v2 User Manual Configuring WPA-PSK and WPA2-PSK Wireless Security Wi-Fi Protected Access with Service Pack 2 does include WPA support. Because WPA and WPA2 are...
...whether newer drivers are relatively new standards, older wireless adapters and devices might not be compatible with older adapters. Furthermore, client software is case-sensitive. 2-10 v1.0, September 2009 Safeguarding Your Network Windows XP with Pre-Shared Key (WPA-PSK and WPA2-PSK) data encryption ...it is easiest to implement, but it allows clients using either WPA-PSK or WPA2-PSK. 3. Wireless-N 150 Router WNR1000v2 User Manual Configuring WPA-PSK and WPA2-PSK Wireless Security Wi-Fi Protected Access with Service Pack 2 does include WPA support. Because WPA and WPA2 are...
WNR1000v2 User Manual
Page 64
Enter the password (or key) for your network and computers against attacks and intrusions. For example, the wildcard feature causes *.yourhost.... Firewall The Stateful Packet Inspection (SPI) firewall protects your Dynamic DNS account. 7. Enter the user name for 4-6 Customizing Your Network Settings v1.0, September 2009 Select WAN Setup under Advanced in to a ping on the WAN (Internet) port. Enter the host...log in the main menu. Select the Use a Dynamic DNS Service check box. 3. Wireless-N 150 Router WNR1000v2 User Manual 2. This is the name that your Dynamic DNS account.
Enter the password (or key) for your network and computers against attacks and intrusions. For example, the wildcard feature causes *.yourhost.... Firewall The Stateful Packet Inspection (SPI) firewall protects your Dynamic DNS account. 7. Enter the user name for 4-6 Customizing Your Network Settings v1.0, September 2009 Select WAN Setup under Advanced in to a ping on the WAN (Internet) port. Enter the host...log in the main menu. Select the Use a Dynamic DNS Service check box. 3. Wireless-N 150 Router WNR1000v2 User Manual 2. This is the name that your Dynamic DNS account.
WNR1000v2 User Manual
Page 125
... K keys, encryption 2-9 keywords, blocking by 3-1 knowledge base 1-4 L LAN IP setup 4-1 LAN path, troubleshooting 7-9 LAN port settings 6-3 language, screen display 1-5 lease, DHCP 6-5 Legacy mode 2-7 local network, default settings A-1 local servers, port forwarding to 5-6 logging in 1-2 login required 1-9 login settings A-1 logout, automatic 1-4 logs sending 3-7 time-stamping entries 3-8 viewing 3-6 M MAC addresses attached devices 6-7 current 6-3 entering 1-8 Wireless-N 150 Router...
... K keys, encryption 2-9 keywords, blocking by 3-1 knowledge base 1-4 L LAN IP setup 4-1 LAN path, troubleshooting 7-9 LAN port settings 6-3 language, screen display 1-5 lease, DHCP 6-5 Legacy mode 2-7 local network, default settings A-1 local servers, port forwarding to 5-6 logging in 1-2 login required 1-9 login settings A-1 logout, automatic 1-4 logs sending 3-7 time-stamping entries 3-8 viewing 3-6 M MAC addresses attached devices 6-7 current 6-3 entering 1-8 Wireless-N 150 Router...
WNR1000v2 User Manual
Page 126
... 1-6 Shared Key authentication 2-5, 2-8 SMTP server 3-7 software push button configuration (WPS) 2-14 specifications technical A-1 speed requirements 5-17 SPI (Stateful Packet Inspection) firewall 4-6 spoofing MAC addresses 1-8, 7-7 SSID 1-12, 2-7, 6-4 SSID broadcast 1-13, 2-12 standards, compatibility A-3 static IP addresses 1-8 static routes 4-8 statistics, usage 6-6 status, viewing 6-2 streaming video and audio 5-17 Index-4 v1.0, September 2009 Wireless-N 150 Router WNR1000v2...
... 1-6 Shared Key authentication 2-5, 2-8 SMTP server 3-7 software push button configuration (WPS) 2-14 specifications technical A-1 speed requirements 5-17 SPI (Stateful Packet Inspection) firewall 4-6 spoofing MAC addresses 1-8, 7-7 SSID 1-12, 2-7, 6-4 SSID broadcast 1-13, 2-12 standards, compatibility A-3 static IP addresses 1-8 static routes 4-8 statistics, usage 6-6 status, viewing 6-2 streaming video and audio 5-17 Index-4 v1.0, September 2009 Wireless-N 150 Router WNR1000v2...
WNR1000v2 User Manual
Page 127
Wireless-N 150 Router WNR1000v2 User Manual subnet mask 4-2, 6-3 system up time 6-6 T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-10 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-11 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii traffic metering 6-14 transfer time (backing up) 5-18...
Wireless-N 150 Router WNR1000v2 User Manual subnet mask 4-2, 6-3 system up time 6-6 T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-10 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-11 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii traffic metering 6-14 transfer time (backing up) 5-18...