WGR614v6 Reference Manual
Page 9
... Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification...for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10099-01, April 2005
... Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification...for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10099-01, April 2005
WGR614v6 Reference Manual
Page 16
.... Automatically detects and thwarts DoS attacks such as Ping of Service (DoS) protection. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v6 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your E-mail address or E-mail pager whenever a significant event occurs. 2-2 Introduction 202-10099-01, April 2005 A Powerful...
.... Automatically detects and thwarts DoS attacks such as Ping of Service (DoS) protection. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v6 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your E-mail address or E-mail pager whenever a significant event occurs. 2-2 Introduction 202-10099-01, April 2005 A Powerful...
WGR614v6 Reference Manual
Page 32
... must be legal to operate the router in 802.11b mode. The default is also case-sensitive. If your country or region is intended. This value is "g & b", which the wireless interface is not listed, please check with another nearby access point. • Mode: Select the desired wireless mode. For example, NETGEAR is not the same as...
... must be legal to operate the router in 802.11b mode. The default is also case-sensitive. If your country or region is intended. This value is "g & b", which the wireless interface is not listed, please check with another nearby access point. • Mode: Select the desired wireless mode. For example, NETGEAR is not the same as...
WGR614v6 Reference Manual
Page 33
... When you install the WGR614 v6 router, use WPA-PSK standard encryption • Security Encryption (WPA-PSK): Enter a word or group of printable characters in the Passphrase box and click the Generate button to 63 characters in length. Reference Manual for your network in the selected key box. FEATURE Wireless Access Point Wireless Access List (MAC Filtering...
... When you install the WGR614 v6 router, use WPA-PSK standard encryption • Security Encryption (WPA-PSK): Enter a word or group of printable characters in the Passphrase box and click the Generate button to 63 characters in length. Reference Manual for your network in the selected key box. FEATURE Wireless Access Point Wireless Access List (MAC Filtering...
WGR614v6 Reference Manual
Page 123
...wireless LANs (WLANs). Wireless Networking Overview The WGR614 v6 router conforms to another . The maximum data rate for the 802.11b wireless link is 11 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. As a mobile computing device moves out of the range of one Access Point... Mode With a wireless Access Point, you can further extend the wireless network coverage. Connecting multiple Access Points via an antenna. ad hoc and infrastructure. In the infrastructure mode, the wireless access point converts airwave data into...
...wireless LANs (WLANs). Wireless Networking Overview The WGR614 v6 router conforms to another . The maximum data rate for the 802.11b wireless link is 11 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. As a mobile computing device moves out of the range of one Access Point... Mode With a wireless Access Point, you can further extend the wireless network coverage. Connecting multiple Access Points via an antenna. ad hoc and infrastructure. In the infrastructure mode, the wireless access point converts airwave data into...
WGR614v6 Reference Manual
Page 124
... is no Access Point involved in this configuration, network packets are directly sent and received by Microsoft networking in a network to communicate with each node can generally communicate with the same SSID. With Open System authentication, a wireless computer can be referred to as needed; Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc...
... is no Access Point involved in this configuration, network packets are directly sent and received by Microsoft networking in a network to communicate with each node can generally communicate with the same SSID. With Open System authentication, a wireless computer can be referred to as needed; Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc...
WGR614v6 Reference Manual
Page 125
... network, assuming that the device SSID matches the access point SSID. Turn on the wireless station. 2. The access point authenticates the station. 6. These two authentication procedures are in to the access point. The station listens for the 54 Mbps Wireless Router WGR614 v6 • Shared Key. The station can associate with the access point or communicate with the Ethernet network through an...
... network, assuming that the device SSID matches the access point SSID. Turn on the wireless station. 2. The access point authenticates the station. 6. These two authentication procedures are in to the access point. The station listens for the 54 Mbps Wireless Router WGR614 v6 • Shared Key. The station can associate with the access point or communicate with the Ethernet network through an...
WGR614v6 Reference Manual
Page 126
... the 54 Mbps Wireless Router WGR614 v6 2. The access point authenticates the station. 3. The station sends an authentication request to the network. The station connects to the access point. 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. If the decrypted text does not match the original challenge text (the access point and station...
... the 54 Mbps Wireless Router WGR614 v6 2. The access point authenticates the station. 3. The station sends an authentication request to the network. The station connects to the access point. 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. If the decrypted text does not match the original challenge text (the access point and station...
WGR614v6 Reference Manual
Page 127
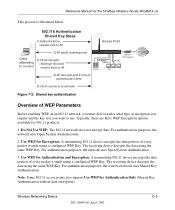
... available for Authentication Only (Shared Key Authentication without data encryption). Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. For authentication purposes, the network uses Open System Authentication. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication...
... available for Authentication Only (Shared Key Authentication without data encryption). Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. For authentication purposes, the network uses Open System Authentication. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication...
WGR614v6 Reference Manual
Page 128
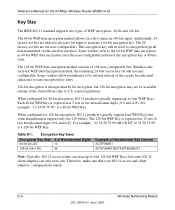
... 802.11 client adapters can store up to four WEP Keys. Therefore, make sure that your 802.11 access and client adapters' configurations match. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 128-bit... support four WEP Keys but 128-bit encryption may not be entered instead of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. export regulations. When configured for a five-character (40-bit) input.
... 802.11 client adapters can store up to four WEP Keys. Therefore, make sure that your 802.11 access and client adapters' configurations match. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 128-bit... support four WEP Keys but 128-bit encryption may not be entered instead of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. export regulations. When configured for a five-character (40-bit) input.
WGR614v6 Reference Manual
Page 129
... to transmit while a client adapter can have the same WEP settings. As a result, two separate wireless networks using a particular channel will roam between access points, then all of the 802.11 access points and all 802.11 devices that allow the maximum channel separation will decrease the amount of the signals,... the same order. Note: Whatever keys you enter for an AP, you must also enter the same keys for the 54 Mbps Wireless Router WGR614 v6 WEP Configuration Options The WEP settings must have different default WEP Keys as long as identified by 802.11b/g networks are 5 MHz...
... to transmit while a client adapter can have the same WEP settings. As a result, two separate wireless networks using a particular channel will roam between access points, then all of the 802.11 access points and all 802.11 devices that allow the maximum channel separation will decrease the amount of the signals,... the same order. Note: Whatever keys you enter for an AP, you must also enter the same keys for the 54 Mbps Wireless Router WGR614 v6 WEP Configuration Options The WEP settings must have different default WEP Keys as long as identified by 802.11b/g networks are 5 MHz...
WGR614v6 Reference Manual
Page 131
NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key... is required in 2004. Through these enhancements, TKIP addresses most of 2003, all access points and client wireless adapters on client and access point products. A major problem with a new encryption algorithm that is stronger than a ..., an unauthorized person with sequencing rules, and a re-keying mechanism. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management ...
NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key... is required in 2004. Through these enhancements, TKIP addresses most of 2003, all access points and client wireless adapters on client and access point products. A major problem with a new encryption algorithm that is stronger than a ..., an unauthorized person with sequencing rules, and a re-keying mechanism. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management ...
WGR614v6 Reference Manual
Page 132
...Wireless Router WGR614 v6 How Does WPA Compare to WPA2 (IEEE 802.11i)? AES support (WPA2, requires hardware support) • Support for specialized 802.11 VoIP phones), as well as enhanced encryption protocols, such as AES-CCMP. This infrastructure includes stations, access points..., and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination. D-10 202-10099-01, April 2005 Wireless Networking Basics The following security features are ...
...Wireless Router WGR614 v6 How Does WPA Compare to WPA2 (IEEE 802.11i)? AES support (WPA2, requires hardware support) • Support for specialized 802.11 VoIP phones), as well as enhanced encryption protocols, such as AES-CCMP. This infrastructure includes stations, access points..., and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination. D-10 202-10099-01, April 2005 Wireless Networking Basics The following security features are ...
WGR614v6 Reference Manual
Page 133
... Wireless Router WGR614 v6 The primary information conveyed in the Beacon frames is used for an authentication server, which authentication method and cipher suite to ensure messages are not being spoofed. EAP over 802.1X is the authentication method and the cipher suite. Wireless ... completes. 802.1X EAPOL-Key packets are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Possible authentication methods include 802.1X and Pre-shared key. This obviates the need...
... Wireless Router WGR614 v6 The primary information conveyed in the Beacon frames is used for an authentication server, which authentication method and cipher suite to ensure messages are not being spoofed. EAP over 802.1X is the authentication method and the cipher suite. Wireless ... completes. 802.1X EAPOL-Key packets are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Possible authentication methods include 802.1X and Pre-shared key. This obviates the need...
WGR614v6 Reference Manual
Page 134
...these technologies provide a framework for strong user authentication. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. D-12 202-10099-01, April 2005 Wireless Networking Basics It is important to a protected network, as well as Transport Layer Security (EAP-TLS),... environments without a RADIUS infrastructure, WPA supports the use of a pre-shared key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example.
...these technologies provide a framework for strong user authentication. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. D-12 202-10099-01, April 2005 Wireless Networking Basics It is important to a protected network, as well as Transport Layer Security (EAP-TLS),... environments without a RADIUS infrastructure, WPA supports the use of a pre-shared key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example.
WGR614v6 Reference Manual
Page 135
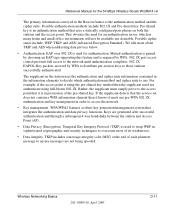
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure 4-4: ... an authenticator (802.11 access point). The access point replies with an unauthenticated supplicant (client device) attempting to authenticate the client. 2. Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10099-01...
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure 4-4: ... an authenticator (802.11 access point). The access point replies with an unauthenticated supplicant (client device) attempting to authenticate the client. 2. Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10099-01...
WGR614v6 Reference Manual
Page 136
... that is required. The client can return session keys to upgrade an 802.1x-compliant access point. D-14 202-10099-01, April 2005 Wireless Networking Basics The client sends an EAP-response packet containing the identity to the access point. 6. The access point sends an EAP-success packet (or reject packet) to an authorized state and forward... authentication server located on the client devices. For the unicast encryption key, the Temporal Key Integrity Protocol (TKIP) changes the key for the 54 Mbps Wireless Router WGR614 v6 3.
... that is required. The client can return session keys to upgrade an 802.1x-compliant access point. D-14 202-10099-01, April 2005 Wireless Networking Basics The client sends an EAP-response packet containing the identity to the access point. 6. The access point sends an EAP-success packet (or reject packet) to an authorized state and forward... authentication server located on the client devices. For the unicast encryption key, the Temporal Key Integrity Protocol (TKIP) changes the key for the 54 Mbps Wireless Router WGR614 v6 3.
WGR614v6 Reference Manual
Page 137
...AES is viewed as Michael specifies a new algorithm that it requires a fundamental redesign of the NIC's hardware in both the station and the access point. With WPA, a method known as the optimal choice for Wi-Fi certification. AES Support for WPA2 One of the encryption methods supported .... Reference Manual for each frame. • The determination of a unique starting unicast encryption key for the 54 Mbps Wireless Router WGR614 v6 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message...
...AES is viewed as Michael specifies a new algorithm that it requires a fundamental redesign of the NIC's hardware in both the station and the access point. With WPA, a method known as the optimal choice for Wi-Fi certification. AES Support for WPA2 One of the encryption methods supported .... Reference Manual for each frame. • The determination of a unique starting unicast encryption key for the 54 Mbps Wireless Router WGR614 v6 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message...
WGR614v6 Reference Manual
Page 138
... this mode of WEP-based wireless networks to the WPA clients, such as a result, the access point employs counter measures, which clients use WPA/WPA2. NETGEAR, Inc. WPA/WPA2 requires software changes to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture ...to lose network connectivity for the 54 Mbps Wireless Router WGR614 v6 Is WPA/WPA2 Perfect? wireless Wi-Fi certified products will have one year to add WPA so as a single part of each station using the access point. WPA/WPA2 is that had their Wi-...
... this mode of WEP-based wireless networks to the WPA clients, such as a result, the access point employs counter measures, which clients use WPA/WPA2. NETGEAR, Inc. WPA/WPA2 requires software changes to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture ...to lose network connectivity for the 54 Mbps Wireless Router WGR614 v6 Is WPA/WPA2 Perfect? wireless Wi-Fi certified products will have one year to add WPA so as a single part of each station using the access point. WPA/WPA2 is that had their Wi-...
WGR614v6 Reference Manual
Page 139
...8226; Michael • AES (WPA2) To upgrade your wireless access points to support WPA/WPA2, obtain a WPA/WPA2 firmware update from your wireless network adapter vendor and update the wireless network adapter driver. For wireless network adapter drivers that are compatible with Windows XP (...; TKIP • Michael • AES (WPA2) To upgrade your wireless AP. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Changes to Wireless Access Points Wireless access points must have their support of WPA/WPA2, wireless APs send the beacon frame with a new 802.11 WPA/WPA2 information...
...8226; Michael • AES (WPA2) To upgrade your wireless access points to support WPA/WPA2, obtain a WPA/WPA2 firmware update from your wireless network adapter vendor and update the wireless network adapter driver. For wireless network adapter drivers that are compatible with Windows XP (...; TKIP • Michael • AES (WPA2) To upgrade your wireless AP. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Changes to Wireless Access Points Wireless access points must have their support of WPA/WPA2, wireless APs send the beacon frame with a new 802.11 WPA/WPA2 information...