MR814v2 Reference Manual
Page 5
... of the Router 1-1 802.11b Standards-based Wireless Networking 1-2 A Powerful, True Firewall with Content Filtering 1-2 Security ...1-3 Autosensing Ethernet Connections with Auto Uplink 1-3 Extensive Protocol Support 1-3 Easy Installation and Management 1-4 Maintenance and Support 1-4 Package Contents ...1-5 The Router's Front Panel 1-6 The Router's Rear Panel 1-7 Chapter 2 Connecting the Router to the Internet What You Will Need Before You Begin 2-1 Cabling and...
... of the Router 1-1 802.11b Standards-based Wireless Networking 1-2 A Powerful, True Firewall with Content Filtering 1-2 Security ...1-3 Autosensing Ethernet Connections with Auto Uplink 1-3 Extensive Protocol Support 1-3 Easy Installation and Management 1-4 Maintenance and Support 1-4 Package Contents ...1-5 The Router's Front Panel 1-6 The Router's Rear Panel 1-7 Chapter 2 Connecting the Router to the Internet What You Will Need Before You Begin 2-1 Cabling and...
MR814v2 Reference Manual
Page 9
... C-19 Obtaining ISP Configuration Information for Macintosh Computers C-20 Restarting the Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP D-3 802.11b Authentication D-3 Open System Authentication D-4 Shared Key Authentication D-4 Overview of WEP Parameters D-5 Key Size...
... C-19 Obtaining ISP Configuration Information for Macintosh Computers C-20 Restarting the Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP D-3 802.11b Authentication D-3 Open System Authentication D-4 Shared Key Authentication D-4 Overview of WEP Parameters D-5 Key Size...
MR814v2 Reference Manual
Page 13
... browsing activity reporting and instant alerts -- In addition to a wide area network (WAN) device, such as a cable modem or DSL modem. Key Features of the NETGEAR MR814v2 Cable/DSL Wireless Router. The MR814v2 router provides the following features: • 802.11b Standards-based wireless networking • Easy, web-based setup for installation and management • Content Filtering and Site Blocking Security...
... browsing activity reporting and instant alerts -- In addition to a wide area network (WAN) device, such as a cable modem or DSL modem. Key Features of the NETGEAR MR814v2 Cable/DSL Wireless Router. The MR814v2 router provides the following features: • 802.11b Standards-based wireless networking • Easy, web-based setup for installation and management • Content Filtering and Site Blocking Security...
MR814v2 Reference Manual
Page 14
The access point provides: • 802.11b Standards-based wireless networking at specified intervals. The router allows you at up to access objectionable Internet sites. 1-2 Introduction You can also configure the router to send immediate alert messages to your email address or email... have the network name (SSID) can be restricted by screening for the MR814v2 Cable/DSL Wireless Router 802.11b Standards-based Wireless Networking The MR814v2 router includes an 802.11b-compliant wireless access point, providing continuous, high-speed 11 Mbps access between your PCs. Automatically...
The access point provides: • 802.11b Standards-based wireless networking at specified intervals. The router allows you at up to access objectionable Internet sites. 1-2 Introduction You can also configure the router to send immediate alert messages to your email address or email... have the network name (SSID) can be restricted by screening for the MR814v2 Cable/DSL Wireless Router 802.11b Standards-based Wireless Networking The MR814v2 router includes an 802.11b-compliant wireless access point, providing continuous, high-speed 11 Mbps access between your PCs. Automatically...
MR814v2 Reference Manual
Page 38
...by anyone with a compatible adapter. MR814 v2 Wireless Data Security Options Range: Up to 500 Feet 1) Open System: Easy but no security 2) MAC Access List: No data security 3) WEP: Security but the data broadcast over 802.11b wireless networks at a maximum range of... the browser interface. Wired Equivalent Privacy (WEP) data encryption provides data security. Such distances can allow for the MR814v2 Cable/DSL Wireless Router Implement Appropriate Wireless Security Note: Indoors, computers can be...
...by anyone with a compatible adapter. MR814 v2 Wireless Data Security Options Range: Up to 500 Feet 1) Open System: Easy but no security 2) MAC Access List: No data security 3) WEP: Security but the data broadcast over 802.11b wireless networks at a maximum range of... the browser interface. Wired Equivalent Privacy (WEP) data encryption provides data security. Such distances can allow for the MR814v2 Cable/DSL Wireless Router Implement Appropriate Wireless Security Note: Indoors, computers can be...
MR814v2 Reference Manual
Page 42
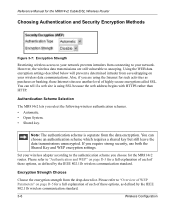
... list. Note: The authentication scheme is using the Internet for such activities as defined by the IEEE 802.11b wireless communication standard. 3-6 Wireless Configuration Also, if you require strong security, use another level of highly secure encryption called SSL. Please... address begins with HTTPS rather than HTTP. Reference Manual for the MR814v2 Cable/DSL Wireless Router Choosing Authentication and Security Encryption Methods Figure 3-7: Encryption Strength Restricting wireless access to your network prevents intruders from connecting to snooping. Authentication Scheme...
... list. Note: The authentication scheme is using the Internet for such activities as defined by the IEEE 802.11b wireless communication standard. 3-6 Wireless Configuration Also, if you require strong security, use another level of highly secure encryption called SSL. Please... address begins with HTTPS rather than HTTP. Reference Manual for the MR814v2 Cable/DSL Wireless Router Choosing Authentication and Security Encryption Methods Figure 3-7: Encryption Strength Restricting wireless access to your network prevents intruders from connecting to snooping. Authentication Scheme...
MR814v2 Reference Manual
Page 47
...and click the Generate button. You can manually or automatically program the four data encryption keys. Wireless adapter configuration utilities such as defined by the IEEE 802.11b wireless communication standard. In the Security Encryption menu, select the authentication and encryption strength Please refer ... XP only allow entry of these options, as the one key which of the MR814v2 router. 3. Click Apply to "Overview of WEP Parameters" on page D-5 for the MR814v2 Cable/DSL Wireless Router 1. Enter a word or group of password, or using whatever LAN address and password...
...and click the Generate button. You can manually or automatically program the four data encryption keys. Wireless adapter configuration utilities such as defined by the IEEE 802.11b wireless communication standard. In the Security Encryption menu, select the authentication and encryption strength Please refer ... XP only allow entry of these options, as the one key which of the MR814v2 router. 3. Click Apply to "Overview of WEP Parameters" on page D-5 for the MR814v2 Cable/DSL Wireless Router 1. Enter a word or group of password, or using whatever LAN address and password...
MR814v2 Reference Manual
Page 90
Reference Manual for the MR814v2 Cable/DSL Wireless Router Interface Specifications LAN: WAN: Wireless Radio Data Rate Frequency Data Encoding: 802.11b Operating Range Maximum Computers Per Wireless Network: 802.11b Operating Frequency Ranges 802.11b Encryption VCCI Class B EN 55 022 (CISPR 22), Class B 10BASE-T or 100BASE-Tx, RJ-45 10BASE-T, RJ-...264 ft (80 m) 890 ft (270 m) 430 ft (130 m) 1485 ft (450 m) 660 ft (200 m) Limited by the amount of wireless network traffic generated by each node. Typically 30-70 nodes. 2.412~2.462 GHz (US) 2.457~2.462 GHz (Spain) 2.412~2.484 GHz (Japan)...
Reference Manual for the MR814v2 Cable/DSL Wireless Router Interface Specifications LAN: WAN: Wireless Radio Data Rate Frequency Data Encoding: 802.11b Operating Range Maximum Computers Per Wireless Network: 802.11b Operating Frequency Ranges 802.11b Encryption VCCI Class B EN 55 022 (CISPR 22), Class B 10BASE-T or 100BASE-Tx, RJ-45 10BASE-T, RJ-...264 ft (80 m) 890 ft (270 m) 430 ft (130 m) 1485 ft (450 m) 660 ft (200 m) Limited by the amount of wireless network traffic generated by each node. Typically 30-70 nodes. 2.412~2.462 GHz (US) 2.457~2.462 GHz (Spain) 2.412~2.484 GHz (Japan)...
MR814v2 Reference Manual
Page 127
... Electronics Engineers (IEEE) 802.11b standard for configuring a wireless network - Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. This mode provides wireless connectivity to multiple wireless network devices within a fixed range or area of Wireless networking. The 802.11b standard is detected. Wireless Networking Overview The MR814v2 router conforms to 5.5, 2, and...
... Electronics Engineers (IEEE) 802.11b standard for configuring a wireless network - Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. This mode provides wireless connectivity to multiple wireless network devices within a fixed range or area of Wireless networking. The 802.11b standard is detected. Wireless Networking Overview The MR814v2 router conforms to 5.5, 2, and...
MR814v2 Reference Manual
Page 129
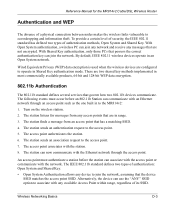
... network. The station listens for the MR814v2 Cable/DSL Wireless Router Authentication and WEP The absence of its SSID. Reference Manual for messages from an access point that has a matching SSID. 4. Wireless Networking Basics D-3 By default, IEEE 802.11 wireless devices operate in to the access point. 5. The IEEE 802.11b standard defines two types of authentication methods, Open...
... network. The station listens for the MR814v2 Cable/DSL Wireless Router Authentication and WEP The absence of its SSID. Reference Manual for messages from an access point that has a matching SSID. 4. Wireless Networking Basics D-3 By default, IEEE 802.11 wireless devices operate in to the access point. 5. The IEEE 802.11b standard defines two types of authentication methods, Open...
MR814v2 Reference Manual
Page 130
... Client attempting to connect 3) Client connects to network Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem Figure 7-4: 802.11b open system authentication Shared Key Authentication The following steps occur when ...key to encrypt the challenge text, and sends the encrypted text to the station. 3. Reference Manual for the MR814v2 Cable/DSL Wireless Router • Shared Key Authentication requires that corresponds to the station's default key.
... Client attempting to connect 3) Client connects to network Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem Figure 7-4: 802.11b open system authentication Shared Key Authentication The following steps occur when ...key to encrypt the challenge text, and sends the encrypted text to the station. 3. Reference Manual for the MR814v2 Cable/DSL Wireless Router • Shared Key Authentication requires that corresponds to the station's default key.
MR814v2 Reference Manual
Page 131
.... Typically, there are three WEP Encryption options available for the MR814v2 Cable/DSL Wireless Router 5. For authentication purposes, the network uses Open System Authentication. 2. For authentication purposes, the 802.11b network uses Open System Authentication. Do Not Use WEP: The 802.11b network does not encrypt data. Wireless Networking Basics D-5 If the decrypted text does not match the original...
.... Typically, there are three WEP Encryption options available for the MR814v2 Cable/DSL Wireless Router 5. For authentication purposes, the network uses Open System Authentication. 2. For authentication purposes, the 802.11b network uses Open System Authentication. Do Not Use WEP: The 802.11b network does not encrypt data. Wireless Networking Basics D-5 If the decrypted text does not match the original...
MR814v2 Reference Manual
Page 132
...set bits are factory set and not user configurable. D-6 Wireless Networking Basics The receiving 802.11b device decrypts the data using a configured WEP Key. Note: Some 802.11b access points also support Use WEP for the MR814v2 Cable/DSL Wireless Router 3. The 128-bit WEP Key is stronger than 40-bit...bit WEP data encryption method, allows for 128-bit encryption, 802.11b products typically support four WEP Keys but some 802.11b client adapters can store up to encrypt/decrypt all data transmitted via the wireless interface. Additionally, 24 factory-set bits are added to the...
...set bits are factory set and not user configurable. D-6 Wireless Networking Basics The receiving 802.11b device decrypts the data using a configured WEP Key. Note: Some 802.11b access points also support Use WEP for the MR814v2 Cable/DSL Wireless Router 3. The 128-bit WEP Key is stronger than 40-bit...bit WEP data encryption method, allows for 128-bit encryption, 802.11b products typically support four WEP Keys but some 802.11b client adapters can store up to encrypt/decrypt all data transmitted via the wireless interface. Additionally, 24 factory-set bits are added to the...
MR814v2 Reference Manual
Page 133
...client adapter, WEP key 2 on the client adapter, etc. Wireless Networking Basics D-7 Reference Manual for the MR814v2 Cable/DSL Wireless Router WEP Configuration Options The WEP settings must match on all of the 802.11b client adapters on the network must have different default WEP Keys as...between access points, then all of the 802.11b access points and all 802.11b devices that allow the maximum channel separation will utilize frequency spectrum 12.5 MHz above and below the center channel frequency. Wireless Channels IEEE 802.11 wireless nodes communicate with each other . In ...
...client adapter, WEP key 2 on the client adapter, etc. Wireless Networking Basics D-7 Reference Manual for the MR814v2 Cable/DSL Wireless Router WEP Configuration Options The WEP settings must match on all of the 802.11b client adapters on the network must have different default WEP Keys as...between access points, then all of the 802.11b access points and all 802.11b devices that allow the maximum channel separation will utilize frequency spectrum 12.5 MHz above and below the center channel frequency. Wireless Channels IEEE 802.11 wireless nodes communicate with each other . In ...
MR814v2 Reference Manual
Page 135
...NETGEAR.com is the domain. IEEE 802.3 specification for 100 Mbps Ethernet over twisted pair wiring. See Dynamic Host Configuration Protocol. See Domain Name Server. See Internet Protocol. A hacker attack designed to other networks. A local device, usually a router... of predefined top level suffixes such as www.NETGEAR.com) to multiple DHCP clients. IEEE specification for wireless networking at 11 Mbps using direct-sequence spread-... addresses on the Internet. Glossary 10BASE-T 100BASE-Tx 802.11b Denial of Service attack DHCP DNS domain name Domain Name Server Dynamic Host ...
...NETGEAR.com is the domain. IEEE 802.3 specification for 100 Mbps Ethernet over twisted pair wiring. See Dynamic Host Configuration Protocol. See Domain Name Server. See Internet Protocol. A hacker attack designed to other networks. A local device, usually a router... of predefined top level suffixes such as www.NETGEAR.com) to multiple DHCP clients. IEEE specification for wireless networking at 11 Mbps using direct-sequence spread-... addresses on the Internet. Glossary 10BASE-T 100BASE-Tx 802.11b Denial of Service attack DHCP DNS domain name Domain Name Server Dynamic Host ...
MR814v2 Reference Manual
Page 137
... services. UPnP. A long distance link used by the Internet Engineering Task Force (IETF) proposing standard protocols and procedures for 802.11b wireless networks. See Windows Internet Naming Service. A protocol in online games, videoconferencing and other peer-to the Internet. A networking ...and destinations. The Internet is a server process for the MR814v2 Cable/DSL Wireless Router Point-to extend or connect remotely located local area networks. The cable used to -Point Protocol RFC RIP router Routing Information Protocol subnet mask UPnP Universal Plug and Play UTP...
... services. UPnP. A long distance link used by the Internet Engineering Task Force (IETF) proposing standard protocols and procedures for 802.11b wireless networks. See Windows Internet Naming Service. A protocol in online games, videoconferencing and other peer-to the Internet. A networking ...and destinations. The Internet is a server process for the MR814v2 Cable/DSL Wireless Router Point-to extend or connect remotely located local area networks. The cable used to -Point Protocol RFC RIP router Routing Information Protocol subnet mask UPnP Universal Plug and Play UTP...
MR814v2 Reference Manual
Page 139
...802.11b D-1 A Account Name 2-11, 2-14, 5-2 Address Resolution Protocol B-9 ad-hoc mode D-2 Authentication Server 2-9 Auto MDI/MDI-X B-13 Auto Uplink 1-3, B-13 B backup configuration 5-7 Basic Wireless Connectivity 3-8 BSSID D-2 C cables, pinout B-12 Cabling B-12 Cat5 cable 2-1, B-13 Channel 3-4 configuration automatic by DHCP 1-4 backup 5-7 erasing 5-8 restore 5-6 router, initial 2-1 content filtering 1-2, 4-1 conventions typography 1-xi crossover cable... Dynamic DNS 6-9 E Encryption Strength 3-6 End Port 6-2 EnterNet C-18 erase configuration 5-8 ESSID 3-8, D-2 Ethernet 1-3 Ethernet cable B-12 1
...802.11b D-1 A Account Name 2-11, 2-14, 5-2 Address Resolution Protocol B-9 ad-hoc mode D-2 Authentication Server 2-9 Auto MDI/MDI-X B-13 Auto Uplink 1-3, B-13 B backup configuration 5-7 Basic Wireless Connectivity 3-8 BSSID D-2 C cables, pinout B-12 Cabling B-12 Cat5 cable 2-1, B-13 Channel 3-4 configuration automatic by DHCP 1-4 backup 5-7 erasing 5-8 restore 5-6 router, initial 2-1 content filtering 1-2, 4-1 conventions typography 1-xi crossover cable... Dynamic DNS 6-9 E Encryption Strength 3-6 End Port 6-2 EnterNet C-18 erase configuration 5-8 ESSID 3-8, D-2 Ethernet 1-3 Ethernet cable B-12 1
MR814v3 Reference Manual
Page 5
... 1 About This Manual Audience, Scope, Conventions, and Formats 1-1 How to Use This Manual 1-2 How to Print this Manual 1-3 Chapter 2 Introduction Key Features of the Router 2-1 802.11b Standards-based Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto Uplink 2-3 Extensive Protocol Support 2-3 Easy Installation and Management 2-4 Maintenance and Support...
... 1 About This Manual Audience, Scope, Conventions, and Formats 1-1 How to Use This Manual 1-2 How to Print this Manual 1-3 Chapter 2 Introduction Key Features of the Router 2-1 802.11b Standards-based Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto Uplink 2-3 Extensive Protocol Support 2-3 Easy Installation and Management 2-4 Maintenance and Support...
MR814v3 Reference Manual
Page 9
... Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Wireless Channels ...D-2 Authentication and WEP D-4 802.11b Authentication D-4 Open System Authentication D-5 Shared Key Authentication D-5 Overview of WEP Parameters D-6 Key Size...
... Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification (ESSID D-2 Wireless Channels ...D-2 Authentication and WEP D-4 802.11b Authentication D-4 Open System Authentication D-5 Shared Key Authentication D-5 Overview of WEP Parameters D-6 Key Size...
MR814v3 Reference Manual
Page 15
...MR814 v3 router provides the following features: • 802.11b Standards-based wireless networking • WPA-PSK wireless security. • Easy, web-based Smart Wizard configuration assistant • Content Filtering and Site Blocking Security • Built in firewall protects you can establish restricted access policies based on time-of the Router The MR814 v3 Cable/DSL Wireless Router... panel LEDs for easy monitoring of the NETGEAR MR814 v3 Cable/DSL Wireless Router. Parents and network administrators can install and use the router within minutes. With minimum setup, you from...
...MR814 v3 router provides the following features: • 802.11b Standards-based wireless networking • WPA-PSK wireless security. • Easy, web-based Smart Wizard configuration assistant • Content Filtering and Site Blocking Security • Built in firewall protects you can establish restricted access policies based on time-of the Router The MR814 v3 Cable/DSL Wireless Router... panel LEDs for easy monitoring of the NETGEAR MR814 v3 Cable/DSL Wireless Router. Parents and network administrators can install and use the router within minutes. With minimum setup, you from...