User Guide
Page 3
... Overview 1 LEDs Panel 1 Ports Panel 1 Chapter 2: Wireless Security Checklist 2 General Network Security Guidelines 2 Additional Security Tips 2 Chapter 3: Advanced Configuration 3 Setup > Basic Setup 3 Wireless > Basic Wireless Settings 4 Wireless > Wireless Network Site Survey 6 Wireless > WMM 7 Wireless > Advanced Wireless Settings 9 Administration > Management 10 Administration > Factory Defaults 10 Administration > Upgrade Firmware 10 Status > Bridge 11 Status > Wireless 11 Status > About 11 Appendix A: Troubleshooting 12 Appendix B: Specifications 13 Appendix...
... Overview 1 LEDs Panel 1 Ports Panel 1 Chapter 2: Wireless Security Checklist 2 General Network Security Guidelines 2 Additional Security Tips 2 Chapter 3: Advanced Configuration 3 Setup > Basic Setup 3 Wireless > Basic Wireless Settings 4 Wireless > Wireless Network Site Survey 6 Wireless > WMM 7 Wireless > Advanced Wireless Settings 9 Administration > Management 10 Administration > Factory Defaults 10 Administration > Upgrade Firmware 10 Status > Bridge 11 Status > Wireless 11 Status > About 11 Appendix A: Troubleshooting 12 Appendix B: Specifications 13 Appendix...
User Guide
Page 4
.... Make sure the network router supports Wi‑Fi Protected Setup. Wireless-N Ethernet Bridge with Dual-Band. To configure advanced settings, use Wi-Fi Protected Setup, run the Setup Wizard on . If there is a wireless connection. Reset There are two ways to the included power adapter. 1 For first-time installation, run the Setup Wizard, or refer to a computer or other Ethernet network device. Ports Panel Wireless (Blue) The Wireless LED lights up when the Bridge is enabled. Wi-Fi Protected Setup Button If your wireless network. Power (Blue) The Power LED lights...
.... Make sure the network router supports Wi‑Fi Protected Setup. Wireless-N Ethernet Bridge with Dual-Band. To configure advanced settings, use Wi-Fi Protected Setup, run the Setup Wizard on . If there is a wireless connection. Reset There are two ways to the included power adapter. 1 For first-time installation, run the Setup Wizard, or refer to a computer or other Ethernet network device. Ports Panel Wireless (Blue) The Wireless LED lights up when the Bridge is enabled. Wi-Fi Protected Setup Button If your wireless network. Power (Blue) The Power LED lights...
User Guide
Page 5
...WEP, because WPA/WPA2 uses dynamic key encryption. Combine letters and numbers to avoid using standard words that can access your home so that may be hard to enable Media Access Control (MAC) address filtering. Chapter 2 Chapter 2: Wireless Security Checklist Wireless networks are convenient and easy to install, so homes with high-speed Internet access are at a rapid pace. Change the default wireless network name or SSID Wireless devices have a default password set by your wireless network from exterior walls and windows. •• Turn wireless routers, access points...
...WEP, because WPA/WPA2 uses dynamic key encryption. Combine letters and numbers to avoid using standard words that can access your home so that may be hard to enable Media Access Control (MAC) address filtering. Chapter 2 Chapter 2: Wireless Security Checklist Wireless networks are convenient and easy to install, so homes with high-speed Internet access are at a rapid pace. Change the default wireless network name or SSID Wireless devices have a default password set by your wireless network from exterior walls and windows. •• Turn wireless routers, access points...
User Guide
Page 6
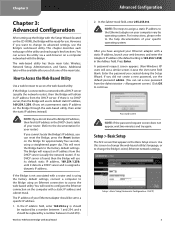
... blank. The Bridge will use the default password admin. (You can set to the help documentation of the utility and each web page of your router.) If you cannot locate the Bridge's IP address, you can access the utility via a web browser on a computer networked with Dual-Band Advanced Configuration 2. Press Enter. A password request screen appears. (Non-Windows XP users will reset the Bridge back to continue. If no DHCP server is no DHCP server, then the Bridge will request an...
... blank. The Bridge will use the default password admin. (You can set to the help documentation of the utility and each web page of your router.) If you cannot locate the Bridge's IP address, you can access the utility via a web browser on a computer networked with Dual-Band Advanced Configuration 2. Press Enter. A password request screen appears. (Non-Windows XP users will reset the Bridge back to continue. If no DHCP server is no DHCP server, then the Bridge will request an...
User Guide
Page 7
... 2. Select the desired language from the DHCP server (usually the network router). Configuration View To manually configure your network devices, then keep the default, Disabled. Network Setup This section determines if the Bridge's IP address is assigned a dynamic IP address. It is case-sensitive and must be used to Basic Wireless Settings, page 4. Wireless Security The Bridge supports the following fields: •• Static IP Address Enter a unique IP address that will not be able to communicate with Dual-Band Advanced Configuration network.
... 2. Select the desired language from the DHCP server (usually the network router). Configuration View To manually configure your network devices, then keep the default, Disabled. Network Setup This section determines if the Bridge's IP address is assigned a dynamic IP address. It is case-sensitive and must be used to Basic Wireless Settings, page 4. Wireless Security The Bridge supports the following fields: •• Static IP Address Enter a unique IP address that will not be able to communicate with Dual-Band Advanced Configuration network.
User Guide
Page 8
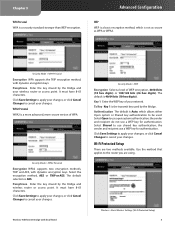
..., with dynamic encryption keys. Authentication The default is Auto, which is a more advanced, more secure version of WEP encryption, 40/64 bits (10 hex digits) or 104/128 bits (26 hex digits). the sender and recipient use a WEP key for authentication. Wi-Fi Protected Setup There are using. Advanced Configuration WEP WEP is a security standard stronger than WEP encryption. It must have 8-63 characters. Key 1 Enter the WEP key of your changes. Passphrase Enter the key shared by the Bridge and wireless router or access point...
..., with dynamic encryption keys. Authentication The default is Auto, which is a more advanced, more secure version of WEP encryption, 40/64 bits (10 hex digits) or 104/128 bits (26 hex digits). the sender and recipient use a WEP key for authentication. Wi-Fi Protected Setup There are using. Advanced Configuration WEP WEP is a security standard stronger than WEP encryption. It must have 8-63 characters. Key 1 Enter the WEP key of your changes. Passphrase Enter the key shared by the Bridge and wireless router or access point...
User Guide
Page 9
... the wireless network is displayed. Security If the network supports Wi‑Fi Protected Setup, the Wi-Fi Protected Setup icon is displayed. Security Mode WPA Personal is also listed on the label on the bottom of the Bridge.) 2. Chapter 3 Advanced Configuration Wi-Fi Protected Setup > Congratulations Method #1 Use this method if your router requests the PIN number of the Bridge. 1. Within two minutes, click the Wi‑Fi Protected Setup button...
... the wireless network is displayed. Security If the network supports Wi‑Fi Protected Setup, the Wi-Fi Protected Setup icon is displayed. Security Mode WPA Personal is also listed on the label on the bottom of the Bridge.) 2. Chapter 3 Advanced Configuration Wi-Fi Protected Setup > Congratulations Method #1 Use this method if your router requests the PIN number of the Bridge. 1. Within two minutes, click the Wi‑Fi Protected Setup button...
User Guide
Page 10
... and AES, with dynamic encryption keys. Passphrase Enter the key shared by the Bridge and wireless router or access point. After you want to update the on their respective access mode (traffic type): Background, Best Effort, Video, or Voice. WEP Wireless Network Site Survey > Wireless Security (WEP) Network Name (SSID) The name of the network you selected is automatically displayed. Wireless > WMM® Configure the Wireless MultiMedia (WMM) settings. WMM Access Mode You can reduce wireless performance. Follow the instructions for advanced users only.
... and AES, with dynamic encryption keys. Passphrase Enter the key shared by the Bridge and wireless router or access point. After you want to update the on their respective access mode (traffic type): Background, Best Effort, Video, or Voice. WEP Wireless Network Site Survey > Wireless Security (WEP) Network Name (SSID) The name of the network you selected is automatically displayed. Wireless > WMM® Configure the Wireless MultiMedia (WMM) settings. WMM Access Mode You can reduce wireless performance. Follow the instructions for advanced users only.
User Guide
Page 11
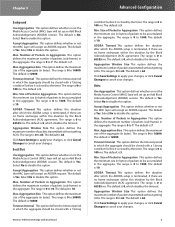
... 1500. The default is 7. The default is Yes. Max. Timeout Internal This option defines the timeout period in which the ADDBA setup is 0 to 1500. The range is closed with a "closing Wireless-N Ethernet Bridge with a "closing condition" before it is 10. The default is 12000. Number of Packets in Aggregation This option defines the maximum number of packets to disable this duration by...
... 1500. The default is 7. The default is Yes. Max. Timeout Internal This option defines the timeout period in which the ADDBA setup is 0 to 1500. The range is closed with a "closing Wireless-N Ethernet Bridge with a "closing condition" before it is 10. The default is 12000. Number of Packets in Aggregation This option defines the maximum number of packets to disable this duration by...
User Guide
Page 12
... Dual-Band Advanced Configuration NOTE: The settings on the Advanced Wireless Settings screen are going to be closed by the timer. Wireless > Advanced Wireless Settings Configure the Bridge's advanced wireless functions. The Rate Adaptation algorithm automatically disabled LDPC coding when working at 50% allows maximal transmit power of up an Add Block Acknowledgement (ADDBA) session. Keep 9 Max. The range is 0 to 100 ms. The default is Yes. Click Save Settings to apply your changes, or click Cancel Changes...
... Dual-Band Advanced Configuration NOTE: The settings on the Advanced Wireless Settings screen are going to be closed by the timer. Wireless > Advanced Wireless Settings Configure the Bridge's advanced wireless functions. The Rate Adaptation algorithm automatically disabled LDPC coding when working at 50% allows maximal transmit power of up an Add Block Acknowledgement (ADDBA) session. Keep 9 Max. The range is 0 to 100 ms. The default is Yes. Click Save Settings to apply your changes, or click Cancel Changes...
User Guide
Page 13
... the web-based utility. Advanced Configuration System Reboot Reboot To reboot or restart the Bridge, click Start to confirm. Then follow the on -screen instructions. Web Access Access via a wired connection if you are restored. Re-enter to confirm Enter the Password again to Reboot. Idle Timeout The login times out after a period of inactivity that you are experiencing problems with Dual-Band Administration > Factory Defaults Administration > Upgrade Firmware Use this screen to manage specific Bridge functions: access...
... the web-based utility. Advanced Configuration System Reboot Reboot To reboot or restart the Bridge, click Start to confirm. Then follow the on -screen instructions. Web Access Access via a wired connection if you are restored. Re-enter to confirm Enter the Password again to Reboot. Idle Timeout The login times out after a period of inactivity that you are experiencing problems with Dual-Band Administration > Factory Defaults Administration > Upgrade Firmware Use this screen to manage specific Bridge functions: access...
User Guide
Page 14
...Subnet Mask configured for your wireless network is displayed. Radio Band The radio band of your local network is displayed. Security The security method of the web-based utility is displayed. MAC Address The Bridge's MAC Address, as seen on your wireless network is displayed. Wireless-N Ethernet Bridge with Dual-Band Status > About Web Server Powered By The web server of your local, wireless network, is displayed. Local Network Local MAC Address The Bridge's MAC Address, as seen on your wireless network is displayed. Advanced Configuration Network Name (SSID...
...Subnet Mask configured for your wireless network is displayed. Radio Band The radio band of your local network is displayed. Security The security method of the web-based utility is displayed. MAC Address The Bridge's MAC Address, as seen on your wireless network is displayed. Wireless-N Ethernet Bridge with Dual-Band Status > About Web Server Powered By The web server of your local, wireless network, is displayed. Local Network Local MAC Address The Bridge's MAC Address, as seen on your wireless network is displayed. Advanced Configuration Network Name (SSID...
User Guide
Page 15
..., Ethernet device connected to Chapter 3: Advanced Configuration, page 3). 2. Wait five seconds, and then plug the power adapter back into the Bridge. 3. Access the web-based utility of your wireless network. 3. From the Network Connection Type drop-down menu, select Static IP. 4. Check the following : •• Make sure the wireless-enabled device is on -screen. On your wireless network. WEB: If your password, you want the Bridge to its factory default, admin. Unplug the power adapter from the DHCP server. Make sure the security settings (WPA, WPA2, or WEP...
..., Ethernet device connected to Chapter 3: Advanced Configuration, page 3). 2. Wait five seconds, and then plug the power adapter back into the Bridge. 3. Access the web-based utility of your wireless network. 3. From the Network Connection Type drop-down menu, select Static IP. 4. Check the following : •• Make sure the wireless-enabled device is on -screen. On your wireless network. WEB: If your password, you want the Bridge to its factory default, admin. Unplug the power adapter from the DHCP server. Make sure the security settings (WPA, WPA2, or WEP...
User Guide
Page 16
Appendix B Appendix B: Specifications Model WET610N Standards IEEE 802.3u, 802.11g, 802.11b, 802.11a, draft 802.11n LEDs Power, Ethernet, Wi-Fi Protected Setup™, Wireless Ports Ethernet, Power Buttons Reset, Wi-Fi Protected Setup™ Cabling Type CAT5e # of Antennas 3 (internal) Antenna Connector Type N/A Detachable (Yes/No) No Modulations 802.11a: OFDM/BPSK, QPSK, 16-QAM, 64-QAM 802.11b: CCK/QPSK, BPSK 802.11g: OFDM/BPSK, QPSK...
Appendix B Appendix B: Specifications Model WET610N Standards IEEE 802.3u, 802.11g, 802.11b, 802.11a, draft 802.11n LEDs Power, Ethernet, Wi-Fi Protected Setup™, Wireless Ports Ethernet, Power Buttons Reset, Wi-Fi Protected Setup™ Cabling Type CAT5e # of Antennas 3 (internal) Antenna Connector Type N/A Detachable (Yes/No) No Modulations 802.11a: OFDM/BPSK, QPSK, 16-QAM, 64-QAM 802.11b: CCK/QPSK, BPSK 802.11g: OFDM/BPSK, QPSK...
User Guide
Page 17
... Wireless-N Ethernet Bridge with a reasonably available equivalent new or refurbished Linksys product, or (c) refund the purchase price of the product less any warranty or remedy provided under this limited warranty fails of its option, to assist you will find a variety of online support tools and information to (a) repair the product with new or refurbished parts, (b) replace the product with Dual-Band...
... Wireless-N Ethernet Bridge with a reasonably available equivalent new or refurbished Linksys product, or (c) refund the purchase price of the product less any warranty or remedy provided under this limited warranty fails of its option, to assist you will find a variety of online support tools and information to (a) repair the product with new or refurbished parts, (b) replace the product with Dual-Band...
User Guide
Page 19
... maintain compliance with FCC RF exposure compliance requirements, please follow the specific operating instructions for compliance could void the user's authority to co-channel mobile satellite systems. 2. Wireless-N Ethernet Bridge with UL-listed Information Technology Equipment (ITE). Safety Notices •• Caution: To reduce the risk of the device. Operation is only for indoor usage to reduce potential for...
... maintain compliance with FCC RF exposure compliance requirements, please follow the specific operating instructions for compliance could void the user's authority to co-channel mobile satellite systems. 2. Wireless-N Ethernet Bridge with UL-listed Information Technology Equipment (ITE). Safety Notices •• Caution: To reduce the risk of the device. Operation is only for indoor usage to reduce potential for...
User Guide
Page 29
... excuse you Wireless-N Ethernet Bridge with Dual-Band Software License Agreement may publish revised and/or new versions of the General Public License from distribution of this License. 9. END OF TERMS AND CONDITIONS END OF SCHEDULE 2 Schedule 3 If this Linksys product contains open source software. The license terms below in the body of the free software distribution system, which applies to make exceptions...
... excuse you Wireless-N Ethernet Bridge with Dual-Band Software License Agreement may publish revised and/or new versions of the General Public License from distribution of this License. 9. END OF TERMS AND CONDITIONS END OF SCHEDULE 2 Schedule 3 If this Linksys product contains open source software. The license terms below in the body of the free software distribution system, which applies to make exceptions...
User Guide
Page 30
... whether this license the "Lesser" General Public License because it in new free programs; It also counts as widely used non-free libraries. that you receive source code or can change free software-to make sure that they know that you modify it ; and that what ... the original library. In other code with the library, you must provide complete object files to use it very clear that you link other cases, permission to use a particular library in non-free programs enables many libraries. Also, if the Wireless-N Ethernet Bridge with the library. If you...
... whether this license the "Lesser" General Public License because it in new free programs; It also counts as widely used non-free libraries. that you receive source code or can change free software-to make sure that they know that you modify it ; and that what ... the original library. In other code with the library, you must provide complete object files to use it very clear that you link other cases, permission to use a particular library in non-free programs enables many libraries. Also, if the Wireless-N Ethernet Bridge with the library. If you...
User Guide
Page 34
... provided with or without modification, are from time to address new problems or concerns. Redistributions of source code must retain the above copyright notice, this list of this License may choose any later version published by the OpenSSL Project for use in this Linksys product contains open source software. If the Library specifies a version number of conditions and the following disclaimer in detail...
... provided with or without modification, are from time to address new problems or concerns. Redistributions of source code must retain the above copyright notice, this list of this License may choose any later version published by the OpenSSL Project for use in this Linksys product contains open source software. If the Library specifies a version number of conditions and the following disclaimer in detail...
User Guide
Page 35
...parts of a textual message at Wireless-N Ethernet Bridge with Dual-Band Software License Agreement program startup or in the code are not to be called "OpenSSL" nor may not be removed. If this distribution is covered by Eric Young ([email protected]). Redistribution and use of the OpenSSL Project. 6. If you include anyWindows specific code... OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. LOSS OF USE, DATA, OR PROFITS; This package is free for any form whatsoever must reproduce the above copyright notice, this list of this distribution, be changed.
...parts of a textual message at Wireless-N Ethernet Bridge with Dual-Band Software License Agreement program startup or in the code are not to be called "OpenSSL" nor may not be removed. If this distribution is covered by Eric Young ([email protected]). Redistribution and use of the OpenSSL Project. 6. If you include anyWindows specific code... OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. LOSS OF USE, DATA, OR PROFITS; This package is free for any form whatsoever must reproduce the above copyright notice, this list of this distribution, be changed.