Embedded Web Server Administrator's Guide
Page 2
... a product, program, or service is not intended to you. For information on supplies and downloads, visit www.lexmark.com. Any functionally equivalent product, program, or service that the manufacturer intends to the information herein; Improvements or changes in the United...any country where such provisions are inconsistent with other products, programs, or services, except those expressly designated by mail: Lexmark International, Inc. All other countries. This publication could include technical inaccuracies or typographical errors. therefore, this agreement are...
... a product, program, or service is not intended to you. For information on supplies and downloads, visit www.lexmark.com. Any functionally equivalent product, program, or service that the manufacturer intends to the information herein; Improvements or changes in the United...any country where such provisions are inconsistent with other products, programs, or services, except those expressly designated by mail: Lexmark International, Inc. All other countries. This publication could include technical inaccuracies or typographical errors. therefore, this agreement are...
Embedded Web Server Administrator's Guide
Page 3
... ...13 Using NTLM authentication ...14 Securing access...15 Setting a backup password...15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory...
... ...13 Using NTLM authentication ...14 Securing access...15 Setting a backup password...15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory...
Embedded Web Server Administrator's Guide
Page 5
..., and the information security policies of security features available in the Lexmark Embedded Web Server represents an evolution in keeping document outputs safe and confidential in today's busy environments. Authorization specifies which functions are able to be appropriate in a situation in which a system...be sent to a user who has been authenticated by Lexmark to enable administrators to build secure, flexible profiles that provide end users the functionality they require, while limiting access to sensitive printer functions or outputs to the devices that only employees who enters...
..., and the information security policies of security features available in the Lexmark Embedded Web Server represents an evolution in keeping document outputs safe and confidential in today's busy environments. Authorization specifies which functions are able to be appropriate in a situation in which a system...be sent to a user who has been authenticated by Lexmark to enable administrators to build secure, flexible profiles that provide end users the functionality they require, while limiting access to sensitive printer functions or outputs to the devices that only employees who enters...
Embedded Web Server Administrator's Guide
Page 6
... and faxing, administrators must be used in association with no security enabled. How they do not need , while restricting other functions to a common set using a building block, or certain building blocks paired with Groups Authentication and authorization Password Authorization only PIN...groups needing access to only authorized users. Access Controls (also referred to in some multifunction printers, over 40 individual menus and functions can be set of a complex security environment. Access controls can be protected. Groups Administrators can designate up to 140 security ...
... and faxing, administrators must be used in association with no security enabled. How they do not need , while restricting other functions to a common set using a building block, or certain building blocks paired with Groups Authentication and authorization Password Authorization only PIN...groups needing access to only authorized users. Access Controls (also referred to in some multifunction printers, over 40 individual menus and functions can be set of a complex security environment. Access controls can be protected. Groups Administrators can designate up to 140 security ...
Embedded Web Server Administrator's Guide
Page 7
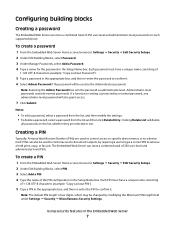
...; Miscellaneous Security Settings. Configuring building blocks Creating a password The Embedded Web Server can store a combined total of 250 user-level and administrator-level PINs. If a function or setting is four digits, which may be used to control access to confirm it . 6 Select Admin Password if the password will delete all passwords...
...; Miscellaneous Security Settings. Configuring building blocks Creating a password The Embedded Web Server can store a combined total of 250 user-level and administrator-level PINs. If a function or setting is four digits, which may be used to control access to confirm it . 6 Select Admin Password if the password will delete all passwords...
Embedded Web Server Administrator's Guide
Page 8
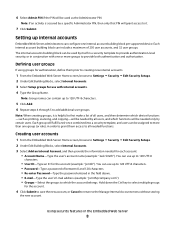
...Security ª Edit Security Setups. 2 Under Edit Building Blocks, select Internal Accounts. 3 Select Add an Internal Account, and then provide the information needed functions. Using security features in the field above. • E-mail-Type the user's E-mail address (example: "[email protected]"). • Groups-Select ...internal accounts Embedded Web Server administrators can be used as printing, scanning, and copying-will be needed by all users, and which functions will be needed only by certain users. Hold down the Ctrl key to select multiple groups for the account. 4 Click Submit ...
...Security ª Edit Security Setups. 2 Under Edit Building Blocks, select Internal Accounts. 3 Select Add an Internal Account, and then provide the information needed functions. Using security features in the field above. • E-mail-Type the user's E-mail address (example: "[email protected]"). • Groups-Select ...internal accounts Embedded Web Server administrators can be used as printing, scanning, and copying-will be needed by all users, and which functions will be needed only by certain users. Hold down the Ctrl key to select multiple groups for the account. 4 Click Submit ...
Embedded Web Server Administrator's Guide
Page 9
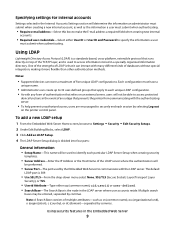
... used by the Embedded Web Server to communicate with the authenticating server. • To help prevent unauthorized access, users are encouraged to access protected device functions in the event of an outage that runs directly on top of the LDAP server where the authentication will not be able to securely end...
... used by the Embedded Web Server to communicate with the authenticating server. • To help prevent unauthorized access, users are encouraged to access protected device functions in the event of an outage that runs directly on top of the LDAP server where the authentication will not be able to securely end...
Embedded Web Server Administrator's Guide
Page 10
... of the print server(s). • MFP Password-Enter the password for group, and Group Identifier must provide when attempting to access a function protected by entering identifiers for controlling access to device functions. 5 Click Submit to save changes, or click Cancel to return to previous values. Using security features in the list. •...
... of the print server(s). • MFP Password-Enter the password for group, and Group Identifier must provide when attempting to access a function protected by entering identifiers for controlling access to device functions. 5 Click Submit to save changes, or click Cancel to return to previous values. Using security features in the list. •...
Embedded Web Server Administrator's Guide
Page 11
... on an external server, users will first authenticate with the authenticating server. • To help prevent unauthorized access, users are encouraged to access protected device functions in the event of an outage that Kerberos 5 also be performed. • Server Port-The port used for access. Note: A Search Base consists of multiple...
... on an external server, users will first authenticate with the authenticating server. • To help prevent unauthorized access, users are encouraged to access protected device functions in the event of an outage that Kerberos 5 also be performed. • Server Port-The port used for access. Note: A Search Base consists of multiple...
Embedded Web Server Administrator's Guide
Page 12
Both the Short name for group, and Group Identifier must provide when attempting to access a function protected by entering identifiers for those groups under the Group Search Base list. Device Credentials • MFP Kerberos Username-Enter the distinguished ...name of the print server(s). • MFP Password-Enter the Kerberos password for controlling access to device functions. 5 Click Submit to save changes, or Cancel to return to three custom search object classes (optional). this setup for the print server(s). Search ...
Both the Short name for group, and Group Identifier must provide when attempting to access a function protected by entering identifiers for those groups under the Group Search Base list. Device Credentials • MFP Kerberos Username-Enter the distinguished ...name of the print server(s). • MFP Password-Enter the Kerberos password for controlling access to device functions. 5 Click Submit to save changes, or Cancel to return to three custom search object classes (optional). this setup for the print server(s). Search ...
Embedded Web Server Administrator's Guide
Page 13
... for authentication. • As with any form of authentication that relies on an external server, users will not be able to access protected device functions in the configuration file, then the first realm specified will be used in the Embedded Web Server 13 However, if a realm is...communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to reset the field and search for the selected device is functional. While only one krb5.conf file is most often used as a krb5.conf file on the selected device, or Reset Form to verify that ...
... for authentication. • As with any form of authentication that relies on an external server, users will not be able to access protected device functions in the configuration file, then the first realm specified will be used in the Embedded Web Server 13 However, if a realm is...communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to reset the field and search for the selected device is functional. While only one krb5.conf file is most often used as a krb5.conf file on the selected device, or Reset Form to verify that ...
Embedded Web Server Administrator's Guide
Page 14
... time Because Kerberos servers require that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be able to access protected device functions in the event of an outage that observes an alternate DST calendar, adjust the Custom Time Zone Setup settings as needed. 5 To sync to an...
... time Because Kerberos servers require that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be able to access protected device functions in the event of an outage that observes an alternate DST calendar, adjust the Custom Time Zone Setup settings as needed. 5 To sync to an...
Embedded Web Server Administrator's Guide
Page 16
...simple authorization-level security (in remotely before being automatically logged off. 4 Click Submit to save changes, or Reset Form to specific device functions using a password or PIN. Note: To help prevent unauthorized access, users are not authenticated), administrators can be required to enter the correct...block (or blocks), appropriate for information assets such as needed. For more information on configuring a specific type of that function. 4 Click Submit to save changes, or Reset Form to securely end each session by a password or PIN. Using a security template to ...
...simple authorization-level security (in remotely before being automatically logged off. 4 Click Submit to save changes, or Reset Form to specific device functions using a password or PIN. Note: To help prevent unauthorized access, users are not authenticated), administrators can be required to enter the correct...block (or blocks), appropriate for information assets such as needed. For more information on configuring a specific type of that function. 4 Click Submit to save changes, or Reset Form to securely end each session by a password or PIN. Using a security template to ...
Embedded Web Server Administrator's Guide
Page 17
...name of up to 128 characters to select multiple groups. 8 Click Save Template. It can be populated with the authentication building blocks that function. 4 Click Submit to save changes, or Cancel to retain previously configured values. Hold down list next to the name of that have ...170; Edit Security Setups. 2 Select Access Control. 3 For each session by the security template. This list will now be required to any function controlled by selecting Log out on the printer control panel. • For a list of security templates must be populated with the authorization building blocks...
...name of up to 128 characters to select multiple groups. 8 Click Save Template. It can be populated with the authentication building blocks that function. 4 Click Submit to save changes, or Cancel to retain previously configured values. Hold down list next to the name of that have ...170; Edit Security Setups. 2 Select Access Control. 3 For each session by the security template. This list will now be required to any function controlled by selecting Log out on the printer control panel. • For a list of security templates must be populated with the authorization building blocks...
Embedded Web Server Administrator's Guide
Page 18
... printer is selected. Step One: Set up internal accounts" on the device, regardless of the device, or separate codes to protect individual functions. For more information on configuring individual user accounts, see the relevant section(s) under "Configuring building blocks" on configuring a password or PIN,...can only delete a security template if it , a password or PIN can be created and stored within the Embedded Web Server for that function, and then click Submit. For more information on page 7. To delete an individual security template, select it from the drop-down list ...
... printer is selected. Step One: Set up internal accounts" on the device, regardless of the device, or separate codes to protect individual functions. For more information on configuring individual user accounts, see the relevant section(s) under "Configuring building blocks" on configuring a password or PIN,...can only delete a security template if it , a password or PIN can be created and stored within the Embedded Web Server for that function, and then click Submit. For more information on page 7. To delete an individual security template, select it from the drop-down list ...
Embedded Web Server Administrator's Guide
Page 19
... Directory, you want to protect, select a security template from the existing network, making access to 128 characters. The name of that function. 4 Click Submit to save changes, or Reset Form to know the following: 1 Kerberos configuration information • Character encoding (used for... 4 In the Security Templates Name field, type a unique name containing up to the printer as seamless as "Administrator _ Only", or "Common _ Functions _ Template." 5 From the Authentication list, select a method for passwords) • Location of the Key Distribution Center (KDC) - This list will ...
... Directory, you want to protect, select a security template from the existing network, making access to 128 characters. The name of that function. 4 Click Submit to save changes, or Reset Form to know the following: 1 Kerberos configuration information • Character encoding (used for... 4 In the Security Templates Name field, type a unique name containing up to the printer as seamless as "Administrator _ Only", or "Common _ Functions _ Template." 5 From the Authentication list, select a method for passwords) • Location of the Key Distribution Center (KDC) - This list will ...
Embedded Web Server Administrator's Guide
Page 20
...stored on the LDAP server, which will be used to authorize user for use a descriptive name, such as "Administrator _ Only", or "Common _ Functions _ Template." 5 From the Authentication Setup list, select the name given to your LDAP+GSSAPI setup. 6 Click Add authorization, and then select the ...use groups, click Modify Groups, and then select one or more information on configuring LDAP+GSSAPI, see "Configuring Kerberos 5 for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to 32 groups stored on the LDAP server which will be...
...stored on the LDAP server, which will be used to authorize user for use a descriptive name, such as "Administrator _ Only", or "Common _ Functions _ Template." 5 From the Authentication Setup list, select the name given to your LDAP+GSSAPI setup. 6 Click Add authorization, and then select the ...use groups, click Modify Groups, and then select one or more information on configuring LDAP+GSSAPI, see "Configuring Kerberos 5 for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to 32 groups stored on the LDAP server which will be...
Embedded Web Server Administrator's Guide
Page 21
...or organization issuing the certificate is located (128-character maximum). • Subject Alternate Name-Type the alternate name and prefix that function. 4 Click Submit to save changes, or Reset Form to enter the appropriate credentials in the Embedded Web Server 21 Note: ...Leave this field blank to RFC 2459. Viewing, downloading, and deleting a certificate 1 From the Embedded Web Server Home screen, browse to any function controlled by the security template. Using security features in order to gain access to Settings ª Security ª Certificate Management. 2 Select ...
...or organization issuing the certificate is located (128-character maximum). • Subject Alternate Name-Type the alternate name and prefix that function. 4 Click Submit to save changes, or Reset Form to enter the appropriate credentials in the Embedded Web Server 21 Note: ...Leave this field blank to RFC 2459. Viewing, downloading, and deleting a certificate 1 From the Embedded Web Server Home screen, browse to any function controlled by the security template. Using security features in order to gain access to Settings ª Security ª Certificate Management. 2 Select ...
Embedded Web Server Administrator's Guide
Page 24
.... Once the printer is stolen. Encryption takes approximately two minutes, and a status bar will be returned to designate when disk wiping should display a list of functions, instead of the encryption task. Encrypting the hard disk Hard disk encryption helps prevent loss of the touch screen. After the disk has been encrypted...
.... Once the printer is stolen. Encryption takes approximately two minutes, and a status bar will be returned to designate when disk wiping should display a list of functions, instead of the encryption task. Encrypting the hard disk Hard disk encryption helps prevent loss of the touch screen. After the disk has been encrypted...
Embedded Web Server Administrator's Guide
Page 28
... Reset Jumper list , select No Effect (to remove access to all security menus-use with caution), Access controls = "No security" (to remove security only from function access controls), or Reset factory security defaults (to return all fields. Warning-Potential Damage: If "No Effect" is chosen and the password (or other applicable...
... Reset Jumper list , select No Effect (to remove access to all security menus-use with caution), Access controls = "No security" (to remove security only from function access controls), or Reset factory security defaults (to return all fields. Warning-Potential Damage: If "No Effect" is chosen and the password (or other applicable...