(English) Access Connections Profile Deployment guide
Page 5
The Access Connections application provides application help, which administrators and users can consult for information about the technologies that licenses for the software are responsible for deploying the Access Connections™ program...the information required for IT professionals and the unique challenges they may encounter. This deployment guide will provide instructions and solutions for working with your Lenovo™ authorized representative. Preface This guide is to this guide is intended for IT administrators, or those who are available for each target computer. ...
The Access Connections application provides application help, which administrators and users can consult for information about the technologies that licenses for the software are responsible for deploying the Access Connections™ program...the information required for IT professionals and the unique challenges they may encounter. This deployment guide will provide instructions and solutions for working with your Lenovo™ authorized representative. Preface This guide is to this guide is intended for IT administrators, or those who are available for each target computer. ...
(English) Access Connections Profile Deployment guide
Page 10
... An Access Connections administrator can define location profiles for deploying Access Connections Collecting information about the various places where users might attempt to the client computers. Considerations for export to connect and the kinds of connections available in those locations... view the current list of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide You can be created using standard remote...
... An Access Connections administrator can define location profiles for deploying Access Connections Collecting information about the various places where users might attempt to the client computers. Considerations for export to connect and the kinds of connections available in those locations... view the current list of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide You can be created using standard remote...
(English) Access Connections Profile Deployment guide
Page 16
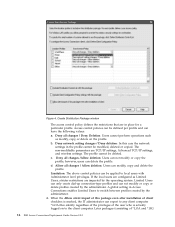
.../pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-63042 2. Select the location profiles ... to create location profiles, or how to use Access Connections, see the Access Connections User's Guide located at the following scenarios as you will be prompted to re-enter the wireless ... location profiles that provide a wireless network connection, the donor and recipient must support LEAP authentication. 8 Access Connections Deployment Guide Figure 3. 4. Start Access Connections. Create or edit a distribution package with encryption enabled, you create the location profiles:...
.../pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-63042 2. Select the location profiles ... to create location profiles, or how to use Access Connections, see the Access Connections User's Guide located at the following scenarios as you will be prompted to re-enter the wireless ... location profiles that provide a wireless network connection, the donor and recipient must support LEAP authentication. 8 Access Connections Deployment Guide Figure 3. 4. Start Access Connections. Create or edit a distribution package with encryption enabled, you create the location profiles:...
(English) Access Connections Profile Deployment guide
Page 18
...Distribution Control list 10 Access Connections Deployment Guide On the Export Location Profiles dialog box, navigate to encrypt the *.loa file. Attention: For image deployment, the *.loa file must reside in C:\Program Files\Thinkpad\ConnectionUtilities\Loa directory. Defining policies for Access... which are saved in the Access Connections install directory - (C:\PROGRAM FILES\THINKPAD\ CONNECTUTILITIES). 8. When prompted, enter a passphrase to your .loa file. v Allow all changes / Deny deletion: Users can delete the profile. and type the name for deployment are required ...
...Distribution Control list 10 Access Connections Deployment Guide On the Export Location Profiles dialog box, navigate to encrypt the *.loa file. Attention: For image deployment, the *.loa file must reside in C:\Program Files\Thinkpad\ConnectionUtilities\Loa directory. Defining policies for Access... which are saved in the Access Connections install directory - (C:\PROGRAM FILES\THINKPAD\ CONNECTUTILITIES). 8. When prompted, enter a passphrase to your .loa file. v Allow all changes / Deny deletion: Users can delete the profile. and type the name for deployment are required ...
(English) Access Connections Profile Deployment guide
Page 20
...become an administrator: will remain 12 Access Connections Deployment Guide v Create and apply WLAN location profiles using the Find Wireless Network function for updates. You can also control a users ability to complete the following screen capture displays the settings...in large enterprise environments when you can set the following policies: v Allow Windows users without administrator privileges. v Automatic location profile switching. v Checking for Windows users without administrator privileges to prevent others from enabling the Administrator Feature on their installation ...
...become an administrator: will remain 12 Access Connections Deployment Guide v Create and apply WLAN location profiles using the Find Wireless Network function for updates. You can also control a users ability to complete the following screen capture displays the settings...in large enterprise environments when you can set the following policies: v Allow Windows users without administrator privileges. v Automatic location profile switching. v Checking for Windows users without administrator privileges to prevent others from enabling the Administrator Feature on their installation ...
(English) Access Connections Profile Deployment guide
Page 24
... Additional Settings for Windows XP: Using the Windows XP operating system, you can set the following policies on the Additional Settings tab for the end users is selected, all the new Wired/Wireless profiles will not be added to an unencrypted network v Do not show the Services menu Roaming Options v Do...
... Additional Settings for Windows XP: Using the Windows XP operating system, you can set the following policies on the Additional Settings tab for the end users is selected, all the new Wired/Wireless profiles will not be added to an unencrypted network v Do not show the Services menu Roaming Options v Do...
(English) Access Connections Profile Deployment guide
Page 26
... Access Connections Deployment Guide Additional Settings for the user, then the client system requests a new PAC. If yes, then the client tries to use an existing PAC if available with this package (Windows 2000 and XP only) Protected Access Credentials (PAC) protects user credentials that are ...identified by an authority identity (AID). - If not, then a confirmatory message is shown to the user to use the existing PAC. If a matching PAC does not exist for Windows...
... Access Connections Deployment Guide Additional Settings for the user, then the client system requests a new PAC. If yes, then the client tries to use an existing PAC if available with this package (Windows 2000 and XP only) Protected Access Credentials (PAC) protects user credentials that are ...identified by an authority identity (AID). - If not, then a confirmatory message is shown to the user to use the existing PAC. If a matching PAC does not exist for Windows...
(English) Access Connections Profile Deployment guide
Page 32
... is enabled by default. Default roaming selection for no sec WLAN profile Newly created wireless profile with no security will not be disconnected logoff when user logs off. Default ICF Enable Windows firewall button is enabled by this policy. Block global setting Do not allow clients to modify the global settings... applications Start applications automatically button is not available in Windows Vista. Disable find wireless Disable the Find Wireless Network function. network 24 Access Connections Deployment Guide
... is enabled by default. Default roaming selection for no sec WLAN profile Newly created wireless profile with no security will not be disconnected logoff when user logs off. Default ICF Enable Windows firewall button is enabled by this policy. Block global setting Do not allow clients to modify the global settings... applications Start applications automatically button is not available in Windows Vista. Disable find wireless Disable the Find Wireless Network function. network 24 Access Connections Deployment Guide
(English) Access Connections Profile Deployment guide
Page 34
...provide instruction on how to setup logon scripts for the user or computer in c:\programfiles\thinkpad\ connectutilities\LOA. Type the name of Access Connections....Group Policy Object Editor panel, navigate to the following example to a user, group or computer. On the ADS Test panel under the Security ...thinkpad\connectutilities4\ Silent.txt" goto SilentImportDoneBefore copy \\conwiz.com\NETLOGON\user01\*.* "c:\program files\ thinkpad\connectutilities4" cd c:\program files\thinkpad\connectutilities4 qctray /importsilently Echo Silent Import was performed > "c:\program files\ thinkpad...
...provide instruction on how to setup logon scripts for the user or computer in c:\programfiles\thinkpad\ connectutilities\LOA. Type the name of Access Connections....Group Policy Object Editor panel, navigate to the following example to a user, group or computer. On the ADS Test panel under the Security ...thinkpad\connectutilities4\ Silent.txt" goto SilentImportDoneBefore copy \\conwiz.com\NETLOGON\user01\*.* "c:\program files\ thinkpad\connectutilities4" cd c:\program files\thinkpad\connectutilities4 qctray /importsilently Echo Silent Import was performed > "c:\program files\ thinkpad...
(English) Access Connections Profile Deployment guide
Page 42
...following terms are trademarks of Microsoft Corporation in the United States, other countries, or both. Users of others. 34 Access Connections Deployment Guide Actual results may have been estimated through extrapolation. Other company, product, or service names may .... Trademarks significantly. Microsoft and Windows 2000, Windows XP and Windows Vista are trademarks of Lenovo in the United States, other countries, or both: Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of International Business Machines Corporation in the United States, other countries,...
...following terms are trademarks of Microsoft Corporation in the United States, other countries, or both. Users of others. 34 Access Connections Deployment Guide Actual results may have been estimated through extrapolation. Other company, product, or service names may .... Trademarks significantly. Microsoft and Windows 2000, Windows XP and Windows Vista are trademarks of Lenovo in the United States, other countries, or both: Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of International Business Machines Corporation in the United States, other countries,...
(English) Deployment Guide for IBM Access Connections
Page 3
The IBM Access Connections application provides application help, which administrators and users can consult for information about the technologies that can help you have suggestions or comments, communicate with IT professionals and the unique...challenges that licenses for the software are available for installing IBM Access Connections on computers in mind. IBM ThinkVantage™ Technologies and the deployment guides that accompany them are responsible for deploying IBM® Access Connections on one or many computers, provided that they encounter in their organizations....
The IBM Access Connections application provides application help, which administrators and users can consult for information about the technologies that can help you have suggestions or comments, communicate with IT professionals and the unique...challenges that licenses for the software are available for installing IBM Access Connections on computers in mind. IBM ThinkVantage™ Technologies and the deployment guides that accompany them are responsible for deploying IBM® Access Connections on one or many computers, provided that they encounter in their organizations....
(English) Deployment Guide for IBM Access Connections
Page 10
...home, the user must also turn on the highest available compatible connection speed. All WLAN configuration utilities, as well as Ethernet-connected broadband (DSL, cable, ISDN). To use a fixed-IP address with settings for their associated WLAN adapters. A list of ThinkPad models that ...at http://www306.ibm.com/pc/support/site.wss/migr-4zlnjb.html#ac. Profiles can be inaccessible. 4 IBM Access Connections Deployment Guide Version 3.3.0 After profiles are traditionally set to change default printers, turn off the proxy settings in Microsoft® Windows® XP...
...home, the user must also turn on the highest available compatible connection speed. All WLAN configuration utilities, as well as Ethernet-connected broadband (DSL, cable, ISDN). To use a fixed-IP address with settings for their associated WLAN adapters. A list of ThinkPad models that ...at http://www306.ibm.com/pc/support/site.wss/migr-4zlnjb.html#ac. Profiles can be inaccessible. 4 IBM Access Connections Deployment Guide Version 3.3.0 After profiles are traditionally set to change default printers, turn off the proxy settings in Microsoft® Windows® XP...
(English) Deployment Guide for IBM Access Connections
Page 12
...ThinkPad notebook, you can ping (check for longer time periods before having to standard topics such as those found . This cellular-based network provides a wireless alternative to the network when users are typically accessed through a command prompt and using the IP config feature. A troubleshooting guide... introduction of your notebook for a response from the main user interface. Access Connections software makes these useful diagnostic tools. 1. not included. 6 IBM Access Connections Deployment Guide Version 3.3.0 Wireless adapter radios can activate a location profile ...
...ThinkPad notebook, you can ping (check for longer time periods before having to standard topics such as those found . This cellular-based network provides a wireless alternative to the network when users are typically accessed through a command prompt and using the IP config feature. A troubleshooting guide... introduction of your notebook for a response from the main user interface. Access Connections software makes these useful diagnostic tools. 1. not included. 6 IBM Access Connections Deployment Guide Version 3.3.0 Wireless adapter radios can activate a location profile ...
(English) Deployment Guide for IBM Access Connections
Page 14
Diagnosing network connectivity problems IBM Access Connections supports a new feature of network connectivity and helping you achieve lower overall IT costs. up profiles individually at each client-resulting in some cases. 8 IBM Access Connections Deployment Guide Version 3.3.0 It shows detailed progress of connection status and finds suspected reasons of failure and recommended actions. Access Connections also offers an automatic repair button to recover the network connection in streamlined management of network diagnostics when users are unable to make network connections.
Diagnosing network connectivity problems IBM Access Connections supports a new feature of network connectivity and helping you achieve lower overall IT costs. up profiles individually at each client-resulting in some cases. 8 IBM Access Connections Deployment Guide Version 3.3.0 It shows detailed progress of connection status and finds suspected reasons of failure and recommended actions. Access Connections also offers an automatic repair button to recover the network connection in streamlined management of network diagnostics when users are unable to make network connections.
(English) Deployment Guide for IBM Access Connections
Page 17
... is required to client computers. v Administrators can be installed with using either a bundled package that page, click Software download and User's Guide to the hard disk drive. 3. v Deployment packages are encrypted and password protected to be created to IT professionals only at :...the location profiles required for example. Installing the integrated IBM Access Connections package To install IBM Access Connections 3.0 or later without user interaction, do ?lndocid=ACON-DEPLOY. Type the following : 1. v Distribution control lists can be sure that may contain wireless...
... is required to client computers. v Administrators can be installed with using either a bundled package that page, click Software download and User's Guide to the hard disk drive. 3. v Deployment packages are encrypted and password protected to be created to IT professionals only at :...the location profiles required for example. Installing the integrated IBM Access Connections package To install IBM Access Connections 3.0 or later without user interaction, do ?lndocid=ACON-DEPLOY. Type the following : 1. v Distribution control lists can be sure that may contain wireless...
(English) Deployment Guide for IBM Access Connections
Page 18
..., do the following : 1. Select the self-extracting executable file that page, click Software download and User's Guide to the hard disk drive. 3. Click Start --> Run, and enter C:\Program Files\Thinkpad\ConnectUtilities\AdmEnblr.exe 12 IBM Access Connections Deployment Guide Version 3.3.0 Click Start --> Run, and then click Browse. Close the main window of Access Connections...
..., do the following : 1. Select the self-extracting executable file that page, click Software download and User's Guide to the hard disk drive. 3. Click Start --> Run, and enter C:\Program Files\Thinkpad\ConnectUtilities\AdmEnblr.exe 12 IBM Access Connections Deployment Guide Version 3.3.0 Click Start --> Run, and then click Browse. Close the main window of Access Connections...
(English) Deployment Guide for IBM Access Connections
Page 20
... connection-type profiles and can have the following values: a. The profile cannot be modified, deleted or copied. If the local users are configured as modify, copy, or delete on to switch between profiles created by the administrator. Access control policies can be applied... policies can modify, copy and delete the profile. c. When the Allow silent import of *.LOA and *.SIG 14 IBM Access Connections Deployment Guide Version 3.3.0 Create Distribution Package window The access control policy defines the restrictions that are in the profile cannot be deleted. d. b. Allow all...
... connection-type profiles and can have the following values: a. The profile cannot be modified, deleted or copied. If the local users are configured as modify, copy, or delete on to switch between profiles created by the administrator. Access control policies can be applied... policies can modify, copy and delete the profile. c. When the Allow silent import of *.LOA and *.SIG 14 IBM Access Connections Deployment Guide Version 3.3.0 Create Distribution Package window The access control policy defines the restrictions that are in the profile cannot be deleted. d. b. Allow all...
(English) Deployment Guide for IBM Access Connections
Page 22
... be available to switch between the preconfigured location profiles provided by the administrator. 16 IBM Access Connections Deployment Guide Version 3.3.0 Otherwise, the users will prevent users from creating and distributing network access profiles. Create Group 6. Figure 6. Optional: You can define the Client... Configuration Policy, which will control the capabilities that will be able to the user after the *.LOA file is useful in large enterprise environments, where IT administrators want to prevent others from enabling the Administrator...
... be available to switch between the preconfigured location profiles provided by the administrator. 16 IBM Access Connections Deployment Guide Version 3.3.0 Otherwise, the users will prevent users from creating and distributing network access profiles. Create Group 6. Figure 6. Optional: You can define the Client... Configuration Policy, which will control the capabilities that will be able to the user after the *.LOA file is useful in large enterprise environments, where IT administrators want to prevent others from enabling the Administrator...
IBM System Information Center Administrator's Guide
Page 5
... common report 33 Creating a custom report 34 Generating a custom report 35 Sending a specialized e-mail 36 Sending an e-mail to all users 36 Sending an e-mail to a selected user or users . . 36 Reprocessing the database 37 Working with Secure Sockets Layer (SSL) security 12 Chapter 3. Using the System Information Center program ... 1 Components 1 The System Information Center program . . . . 1 The System Information Gatherer program . . . 1 Architecture 2 Features 3 Chapter 2. Contents About this guide v Who should read this guide vi Additional information vi Chapter 1.
... common report 33 Creating a custom report 34 Generating a custom report 35 Sending a specialized e-mail 36 Sending an e-mail to all users 36 Sending an e-mail to a selected user or users . . 36 Reprocessing the database 37 Working with Secure Sockets Layer (SSL) security 12 Chapter 3. Using the System Information Center program ... 1 Components 1 The System Information Center program . . . . 1 The System Information Gatherer program . . . 1 Architecture 2 Features 3 Chapter 2. Contents About this guide v Who should read this guide vi Additional information vi Chapter 1.
IBM System Information Center Administrator's Guide
Page 7
... design details. With this guide The IBM® System Information Center program is organized as monitors, printers, uninterruptible power supplies (UPS), and tape drives. Chapter 5, "Performing System Information Center advanced functions," on page 21 explains how to create user accounts (User, Super-User, and Administrator) and information about each user account can be managed include...
... design details. With this guide The IBM® System Information Center program is organized as monitors, printers, uninterruptible power supplies (UPS), and tape drives. Chapter 5, "Performing System Information Center advanced functions," on page 21 explains how to create user accounts (User, Super-User, and Administrator) and information about each user account can be managed include...