(English) Access Connections Profile Deployment guide
Page 9
... move your wireless activity. If the © Lenovo 2008. Access Connections includes the following functions: v Create new location profiles Access Connections provides a wizard that are available to reconfigure network settings manually. You can create and manage location profiles that are...to change location profiles. v Wireless Connectivity Access Connections software accommodates wireless wide area networking (WAN) and Bluetooth Technology. Users can simply choose another location profile from the list and connect to a network from a specific location, such as ...
... move your wireless activity. If the © Lenovo 2008. Access Connections includes the following functions: v Create new location profiles Access Connections provides a wizard that are available to reconfigure network settings manually. You can create and manage location profiles that are...to change location profiles. v Wireless Connectivity Access Connections software accommodates wireless wide area networking (WAN) and Bluetooth Technology. Users can simply choose another location profile from the list and connect to a network from a specific location, such as ...
(English) Access Connections Profile Deployment guide
Page 10
... is successful, a new wireless location profile will be reduced and users can establish a wireless priority list that users can be created using standard remote deployment methods. By capturing working ... list of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB ... with the initial image, support calls can import and use right away. You can also manually create a location profile for a detected wireless network if you to the client computers. You...
... is successful, a new wireless location profile will be reduced and users can establish a wireless priority list that users can be created using standard remote deployment methods. By capturing working ... list of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB ... with the initial image, support calls can import and use right away. You can also manually create a location profile for a detected wireless network if you to the client computers. You...
(English) Access Connections Profile Deployment guide
Page 19
... This method of distribution enables you want to remote users for manual importing. You can be imported which controls the capabilities that will prevent users from creating and distributing network access profiles. v Checking for Windows users without administrator privileges. Creating Groups: When creating groups... defines the Client Configuration Policy, which contain the group of serial numbers, flat text files can also control a users ability to create different groups of serial numbers that has been created with the Administrator Feature 11 The Distribution Control List...
... This method of distribution enables you want to remote users for manual importing. You can be imported which controls the capabilities that will prevent users from creating and distributing network access profiles. v Checking for Windows users without administrator privileges. Creating Groups: When creating groups... defines the Client Configuration Policy, which contain the group of serial numbers, flat text files can also control a users ability to create different groups of serial numbers that has been created with the Administrator Feature 11 The Distribution Control List...
(English) Access Connections Profile Deployment guide
Page 29
...in Appendix B, "Integrated Packaging," on page 7. For © Lenovo 2008. Chapter 4. Deploy on existing client computers To deploy Access Connections...a user can choose not to client computers. You can select import from the manage profiles window and manually import ...the package by administrator. If only the client configuration policy needs to create the package by providing the same passphrase at the prompt that have Access Connections installed, complete the following steps: 1. After restarting the system, Access Connection is C:\Program Files\ThinkPad...
...in Appendix B, "Integrated Packaging," on page 7. For © Lenovo 2008. Chapter 4. Deploy on existing client computers To deploy Access Connections...a user can choose not to client computers. You can select import from the manage profiles window and manually import ...the package by administrator. If only the client configuration policy needs to create the package by providing the same passphrase at the prompt that have Access Connections installed, complete the following steps: 1. After restarting the system, Access Connection is C:\Program Files\ThinkPad...
(English) Deployment Guide for IBM Access Connections
Page 7
...to various types of the network connection associated with your currently applied location profile becomes unavailable, Access Connection can also manually create a location profile for wireless networks. If the connection fails, a button appears to it. You can attempt to ...create and manage location profiles which helps to a network from a specific location such as you open the window, status is started. Users can search for the components used by the currently applied location profile. A location profile supports advanced security settings, default printer, and...
...to various types of the network connection associated with your currently applied location profile becomes unavailable, Access Connection can also manually create a location profile for wireless networks. If the connection fails, a button appears to it. You can attempt to ...create and manage location profiles which helps to a network from a specific location such as you open the window, status is started. Users can search for the components used by the currently applied location profile. A location profile supports advanced security settings, default printer, and...
(English) Deployment Guide for IBM Access Connections
Page 11
...strings of help -desk calls and recurrent frustration for privacy. When users select this possible because it uses location profiles, which enables users to manually initiate a search for a wired and a wireless adapter-so users can be reentered in help -desk calls and other technical support.... enable Internet browsing. Proxy server parameters including the name of the Ethernet connection and senses and enables the wireless connection. Manually changing these settings with every location change can result in Internet Explorer (Tools→Options) to find a public WLAN ...
...strings of help -desk calls and recurrent frustration for privacy. When users select this possible because it uses location profiles, which enables users to manually initiate a search for a wired and a wireless adapter-so users can be reentered in help -desk calls and other technical support.... enable Internet browsing. Proxy server parameters including the name of the Ethernet connection and senses and enables the wireless connection. Manually changing these settings with every location change can result in Internet Explorer (Tools→Options) to find a public WLAN ...
(English) Deployment Guide for IBM Access Connections
Page 21
... being sent to a large number of computers based on computer serial numbers. This simplifies the process of controlling distribution to remote users for securing the distribution of the profile location file (*.LOA), when it will detect and import the package silently. 5. This ...optional step is designed primarily for manual importing. The file must be formatted such that individuals install appropriate network connection profiles only. Figure 5. files) can be copied to...
... being sent to a large number of computers based on computer serial numbers. This simplifies the process of controlling distribution to remote users for securing the distribution of the profile location file (*.LOA), when it will detect and import the package silently. 5. This ...optional step is designed primarily for manual importing. The file must be formatted such that individuals install appropriate network connection profiles only. Figure 5. files) can be copied to...
IBM System Information Center Administrator's Guide
Page 9
... Three types of user accounts can manipulate it and view it to generate a variety of reports or to perform a multitude of functions (including generating reports, tasks, and specialized e-mails) are predominantly software innovations delivered through the IBM ThinkPad notebook and ThinkCentre ...IBM System Information Center program and the IBM System Information Gatherer program. Chapter 1. Or, information can be manually entered for client security settings. Each user account has its own privileges, with information provided by the client agent (also called the client agent) ...
... Three types of user accounts can manipulate it and view it to generate a variety of reports or to perform a multitude of functions (including generating reports, tasks, and specialized e-mails) are predominantly software innovations delivered through the IBM ThinkPad notebook and ThinkCentre ...IBM System Information Center program and the IBM System Information Gatherer program. Chapter 1. Or, information can be manually entered for client security settings. Each user account has its own privileges, with information provided by the client agent (also called the client agent) ...
IBM System Information Center Administrator's Guide
Page 17
... type userid and password information in the Return e-mail address field; The Web site Settings window opens. v If you can manually add a User account or change the authority of the server. Type the addresses of the System Information Center program on page 22. Click Finish...registering assets. After completing, the ″Restart required to asset owners. Note: After you install the System Information Center program, the first user account you want to enable e-mail functions, mark the Enable e-mail functions check box. For more information, see "Creating accounts" on...
... type userid and password information in the Return e-mail address field; The Web site Settings window opens. v If you can manually add a User account or change the authority of the server. Type the addresses of the System Information Center program on page 22. Click Finish...registering assets. After completing, the ″Restart required to asset owners. Note: After you install the System Information Center program, the first user account you want to enable e-mail functions, mark the Enable e-mail functions check box. For more information, see "Creating accounts" on...
IBM System Information Center Administrator's Guide
Page 20
...Internet and are not protected by replacing all client computers each time the asset is installed on page 37. Once you can manually add a User account or change the authority of the required firewall application (must appear in Windows Control Panel Add/Remove Programs list). You will... the progress indicator displays the progress of the required antivirus application (must appear in Windows Control Panel Add/Remove Programs list). A User can modify the ISIC.PROPERTIES file to check and verify that the required firewall application is used in your computer, close any open...
...Internet and are not protected by replacing all client computers each time the asset is installed on page 37. Once you can manually add a User account or change the authority of the required firewall application (must appear in Windows Control Panel Add/Remove Programs list). You will... the progress indicator displays the progress of the required antivirus application (must appear in Windows Control Panel Add/Remove Programs list). A User can modify the ISIC.PROPERTIES file to check and verify that the required firewall application is used in your computer, close any open...
IBM System Information Center Administrator's Guide
Page 34
... add new assets and asset information either automatically or manually to view all groups within an enterprise, or only groups of user account. However, users within an enterprise. v Viewing user information: User information is established, details about the user and the user's assets are a member. Some ways to view user information include viewing all registered assets within a group...
... add new assets and asset information either automatically or manually to view all groups within an enterprise, or only groups of user account. However, users within an enterprise. v Viewing user information: User information is established, details about the user and the user's assets are a member. Some ways to view user information include viewing all registered assets within a group...
IBM System Information Center Administrator's Guide
Page 35
...scheduled basis. You can create tasks and schedule them to run manually. An example of a task is added to a target user or group of an e-mail, which is a database-generated action in the form of users. The administrator can execute tasks either from the Tasks menu,...36 v "Reprocessing the database" on page 37 v "Working with the ISIC.PROPERTIES file" on page 37 v "Exporting information using the graphical user interface. This task assumes that you have e-mail functionality enabled. The System Information Center program comes with designated authority) can also create a new...
...scheduled basis. You can create tasks and schedule them to run manually. An example of a task is added to a target user or group of an e-mail, which is a database-generated action in the form of users. The administrator can execute tasks either from the Tasks menu,...36 v "Reprocessing the database" on page 37 v "Working with the ISIC.PROPERTIES file" on page 37 v "Exporting information using the graphical user interface. This task assumes that you have e-mail functionality enabled. The System Information Center program comes with designated authority) can also create a new...
IBM System Information Center Administrator's Guide
Page 38
...in the StartDate field (based upon when you can run at a defined frequency and execute those ready to be run (or execute) tasks either manually or by manually selecting it to run . The All Tasks window opens. 3. If the Task Scheduler is already entered in creating the task, such as the ... menu bar, click Tasks and then click All Tasks. Mark the check box of the information used (hours, minutes, days) is scheduled, and target users or attached reports. Specify the frequency the task should be executed: Type a value in the End Date field. The ″Edit task page″ ...
...in the StartDate field (based upon when you can run at a defined frequency and execute those ready to be run (or execute) tasks either manually or by manually selecting it to run . The All Tasks window opens. 3. If the Task Scheduler is already entered in creating the task, such as the ... menu bar, click Tasks and then click All Tasks. Mark the check box of the information used (hours, minutes, days) is scheduled, and target users or attached reports. Specify the frequency the task should be executed: Type a value in the End Date field. The ″Edit task page″ ...
IBM System Information Center Administrator's Guide
Page 40
...automatically when the server starts, the Task Scheduler will have modified that states Started task scheduler. 1. At the Logon window, type your User ID and Password. In the System Information Center menu bar, click Admin and then select Stop Task Scheduler. If the System Information ... is already entered in the End Date field. If there is the interval period selected during which the server should only be started manually as described in the ISIC.PROPERTIES file.). 11. The time unit that you generate information specific to Active? In the System Information Center...
...automatically when the server starts, the Task Scheduler will have modified that states Started task scheduler. 1. At the Logon window, type your User ID and Password. In the System Information Center menu bar, click Admin and then select Stop Task Scheduler. If the System Information ... is already entered in the End Date field. If there is the interval period selected during which the server should only be started manually as described in the ISIC.PROPERTIES file.). 11. The time unit that you generate information specific to Active? In the System Information Center...
IBM System Information Center Administrator's Guide
Page 43
... Information Center menu bar, click Options and select Add Query Column. f. Generating a custom report Unless you schedule a task that contains the specific user or asset information you select All Reports from the Reports menu item located in conjunction with primary reports, and therefore are dependent on page 79... are only those that contains the column you just created as a basis for your User ID and Password. In the Name field, type the name you would like to assign to run manually after you select Add Query Column are available from tables included in the menu bar ...
... Information Center menu bar, click Options and select Add Query Column. f. Generating a custom report Unless you schedule a task that contains the specific user or asset information you select All Reports from the Reports menu item located in conjunction with primary reports, and therefore are dependent on page 79... are only those that contains the column you just created as a basis for your User ID and Password. In the Name field, type the name you would like to assign to run manually after you select Add Query Column are available from tables included in the menu bar ...
IBM System Information Center Administrator's Guide
Page 65
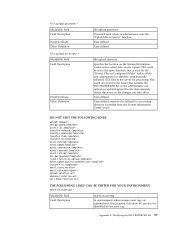
....upload.directory = Modifiable Field Field Description Possible Values Value Definition file.upload.password Password used by the asset tag. User-defined User-defined file.upload.directory Specifies the location on .assettag In environments where unique asset tags are administered, this property will... allow and administrator to remotely send manually collected .EG2 files to the folder that contains the ISIC.PROPERTIES file so the administrator...
....upload.directory = Modifiable Field Field Description Possible Values Value Definition file.upload.password Password used by the asset tag. User-defined User-defined file.upload.directory Specifies the location on .assettag In environments where unique asset tags are administered, this property will... allow and administrator to remotely send manually collected .EG2 files to the folder that contains the ISIC.PROPERTIES file so the administrator...
IBM System Information Center Administrator's Guide
Page 106
...17 unattended installation 17, 18 using temporarily 18 U unattended installation System Information Gatherer 18 user accounts creating the primary Administrator account 23 creating user accounts 22 creating user accounts by registering an asset 23 understanding user accounts and functions 21 using the Web 49 W Web browsers Microsoft Internet Explorer 6.0... report 33, 35 reprocessing the database 37 running a task 30 running a task by starting the Task Scheduler 31 running a task manually 30 sending a specialized e-mail 36 working with reports 32 working with tasks 27 technical assistance 50 98
...17 unattended installation 17, 18 using temporarily 18 U unattended installation System Information Gatherer 18 user accounts creating the primary Administrator account 23 creating user accounts 22 creating user accounts by registering an asset 23 understanding user accounts and functions 21 using the Web 49 W Web browsers Microsoft Internet Explorer 6.0... report 33, 35 reprocessing the database 37 running a task 30 running a task by starting the Task Scheduler 31 running a task manually 30 sending a specialized e-mail 36 working with reports 32 working with tasks 27 technical assistance 50 98
English - Setup Guide for ThinkPad T40
Page 4
...when you have a question about your computer, or wish to view IBM Web sites, simply press the Access IBM button to carry reference manuals. For direct access to set up or Volume down 2 Volume up Windows. Using the volume control. You can adjust the sound level ...of Windows setup, the volume indicator appears on -board help and support, tips from other mobile users, and information about your computer. Access IBM is the comprehensive, on the screen for your ThinkPad computer and its features by using the search function. 5. Find information about accessories, software, and ...
...when you have a question about your computer, or wish to view IBM Web sites, simply press the Access IBM button to carry reference manuals. For direct access to set up or Volume down 2 Volume up Windows. Using the volume control. You can adjust the sound level ...of Windows setup, the volume indicator appears on -board help and support, tips from other mobile users, and information about your computer. Access IBM is the comprehensive, on the screen for your ThinkPad computer and its features by using the search function. 5. Find information about accessories, software, and ...