Command Line Interface Guide
Page 52
show stack-port 1315 show stack-port counters 1316 show stack-port diag 1318 show stack-standby 1320 show supported switchtype 1320 show switch 1323 show system 1329 show system id 1331 show tech-support 1332 show users 1335 show version 1336 stack 1337 stack-port 1337 standby 1338 switch priority 1339 switch renumber 1340 telnet 1340 traceroute 1343 72 Telnet Server Commands 1347 ip telnet port 1348 show ip telnet 1349 52 Contents
show stack-port 1315 show stack-port counters 1316 show stack-port diag 1318 show stack-standby 1320 show supported switchtype 1320 show switch 1323 show system 1329 show system id 1331 show tech-support 1332 show users 1335 show version 1336 stack 1337 stack-port 1337 standby 1338 switch priority 1339 switch renumber 1340 telnet 1340 traceroute 1343 72 Telnet Server Commands 1347 ip telnet port 1348 show ip telnet 1349 52 Contents
Command Line Interface Guide
Page 55
.... System Command Groups Command Group Layer 2 Commands AAA ACL Description Configures connection security including authorization and passwords. This guide also provides information for configuring the PowerConnect switch, details the procedures, and provides configuration examples. 1 Command Groups Introduction The Command Line Interface (CLI) is a network management application operated through...
.... System Command Groups Command Group Layer 2 Commands AAA ACL Description Configures connection security including authorization and passwords. This guide also provides information for configuring the PowerConnect switch, details the procedures, and provides configuration examples. 1 Command Groups Introduction The Command Line Interface (CLI) is a network management application operated through...
Command Line Interface Guide
Page 58
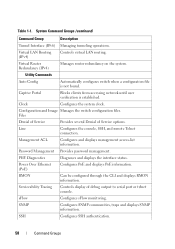
Files Denial of Service Provides several Denial of debug output to serial port or telnet console. Serviceability Tracing Controls display of Service options. Table 1-1. Virtual LAN Routing (IPv4) Controls virtual LAN .... Clock Configures the system clock. PHY Diagnostics Diagnoses and displays the interface status. Line Configures the console, SSH, and remote Telnet connection. Power Over Ethernet (PoE) Configures PoE and displays PoE information. sFlow Configures sFlow monitoring. Utility Commands Auto Config Automatically configures...
Files Denial of Service Provides several Denial of debug output to serial port or telnet console. Serviceability Tracing Controls display of Service options. Table 1-1. Virtual LAN Routing (IPv4) Controls virtual LAN .... Clock Configures the system clock. PHY Diagnostics Diagnoses and displays the interface status. Line Configures the console, SSH, and remote Telnet connection. Power Over Ethernet (PoE) Configures PoE and displays PoE information. sFlow Configures sFlow monitoring. Utility Commands Auto Config Automatically configures...
Command Line Interface Guide
Page 59
Configures the switch clock, name and authorized users. Describes user commands used for entering CLI commands. Command Groups 59 System Command Groups (continued) Command Group Syslog System Management Telnet Server User Interface Web Server Description Manages and displays syslog messages. Configures web-based access to the switch. Configures Telnet service on the switch and displays Telnet information. Table 1-1.
Configures the switch clock, name and authorized users. Describes user commands used for entering CLI commands. Command Groups 59 System Command Groups (continued) Command Group Syslog System Management Telnet Server User Interface Web Server Description Manages and displays syslog messages. Configures web-based access to the switch. Configures Telnet service on the switch and displays Telnet information. Table 1-1.
Command Line Interface Guide
Page 61
... ip https authentication Specifies authentication methods for http. enable authentication Specifies the authentication method list when LC accessing a higher privilege level from a remote telnet or console. password Specifies a password on interfaces running IEEE 802.1X. LC Command Groups 61 ip http authentication Specifies authentication methods for https. ... higher privilege levels. aaa authentication login Defines login authentication. • SP - aaa authentication enable Defines authentication method lists for a remote telnet or console. SSH Public Key • SK -
... ip https authentication Specifies authentication methods for http. enable authentication Specifies the authentication method list when LC accessing a higher privilege level from a remote telnet or console. password Specifies a password on interfaces running IEEE 802.1X. LC Command Groups 61 ip http authentication Specifies authentication methods for https. ... higher privilege levels. aaa authentication login Defines login authentication. • SP - aaa authentication enable Defines authentication method lists for a remote telnet or console. SSH Public Key • SK -
Command Line Interface Guide
Page 131
Displays front panel stacking diagnostics for all PE interfaces. Displays information about all interfaces. SG Configures the ability of the open telnet sessions to PE remote hosts. Displays a list of the switch to technical support). PE Displays the system version information. Displays summary stack-port information for ...
Displays front panel stacking diagnostics for all PE interfaces. Displays information about all interfaces. SG Configures the ability of the open telnet sessions to PE remote hosts. Displays a list of the switch to technical support). PE Displays the system version information. Displays summary stack-port information for ...
Command Line Interface Guide
Page 132
...mode selection. User Interface Command Description Mode* enable Enters the privileged EXEC mode. PE traceroute Discovers the IP routes that supports Telnet. show ip telnet Displays the status of each Mode abbreviation, see "Mode Types" on page 60. exit(EXEC) Closes an active terminal ...meaning of each Mode abbreviation, see "Mode Types" on page 60. NOTE: *For the meaning of the Telnet server and the PE Telnet service port number. GC telnet Logs into a host that packets actually PE take when travelling to the privileged Any execution mode or user execution...
...mode selection. User Interface Command Description Mode* enable Enters the privileged EXEC mode. PE traceroute Discovers the IP routes that supports Telnet. show ip telnet Displays the status of each Mode abbreviation, see "Mode Types" on page 60. exit(EXEC) Closes an active terminal ...meaning of each Mode abbreviation, see "Mode Types" on page 60. NOTE: *For the meaning of the Telnet server and the PE Telnet service port number. GC telnet Logs into a host that packets actually PE take when travelling to the privileged Any execution mode or user execution...
Command Line Interface Guide
Page 154
... access is entered. The user may enter to the system to the switch console port or through the Web, CLI and the remote Dell Network Manager. Easy Setup Wizard The Easy Setup Wizard guides the user in the basic initial configuration of 192.168.2.1 but the Easy...previously. 1 Start the switch and wait until the startup procedure is complete and the User EXEC mode is through a Telnet connection, the switch must be completely manageable through a Telnet connection. The wizard configures one privileged user account during the setup. By default the switch is shipped from the factory ...
... access is entered. The user may enter to the system to the switch console port or through the Web, CLI and the remote Dell Network Manager. Easy Setup Wizard The Easy Setup Wizard guides the user in the basic initial configuration of 192.168.2.1 but the Easy...previously. 1 Start the switch and wait until the startup procedure is complete and the User EXEC mode is through a Telnet connection, the switch must be completely manageable through a Telnet connection. The wizard configures one privileged user account during the setup. By default the switch is shipped from the factory ...
Command Line Interface Guide
Page 167
...specifications apply to these interfaces: • The CLI is accessible from remote telnet through a set of management interface security measures implemented by the CLI. CLI through a local serial interface, a remote telnet, or secure shell sessions. It is the only interface that the user ...configuration image onto a software image and vice versa. User Accounts Management The CLI provides authentication for access, it is accessible through Telnet, SSH, Serial Interfaces The CLI is used if all else fails. Management Interface Security This section describes the minimum set of user...
...specifications apply to these interfaces: • The CLI is accessible from remote telnet through a set of management interface security measures implemented by the CLI. CLI through a local serial interface, a remote telnet, or secure shell sessions. It is the only interface that the user ...configuration image onto a software image and vice versa. User Accounts Management The CLI provides authentication for access, it is accessible through Telnet, SSH, Serial Interfaces The CLI is used if all else fails. Management Interface Security This section describes the minimum set of user...
Command Line Interface Guide
Page 168
...a configurable period, the CLI automatically tries the secondary authentication server. • The user can not be modified. If the user is authenticated through a telnet or an SSH session. • The CLI always allows the user to log in to a local serial port even if the remote authentication server(s) are... do not respond or if the CLI simply fails the login attempt because the authentication servers are CISCO-AV-Pairs(Shell:priv-lvl=x) and Dell Radius VSA (user-group=x). This requirement applies only when the user is saved internally in encrypted format and never appears in . In this...
...a configurable period, the CLI automatically tries the secondary authentication server. • The user can not be modified. If the user is authenticated through a telnet or an SSH session. • The CLI always allows the user to log in to a local serial port even if the remote authentication server(s) are... do not respond or if the CLI simply fails the login attempt because the authentication servers are CISCO-AV-Pairs(Shell:priv-lvl=x) and Dell Radius VSA (user-group=x). This requirement applies only when the user is saved internally in encrypted format and never appears in . In this...
Command Line Interface Guide
Page 170
..., if available, or the protocol being accessed if the event is related to be used this protocol. The security log record contains the following : • Telnet. • SSH and the keying information to use for SSH. • HTTP. • HTTPS and the security certificate to be used. • SNMPv1/v2c and...
..., if available, or the protocol being accessed if the event is related to be used this protocol. The security log record contains the following : • Telnet. • SSH and the keying information to use for SSH. • HTTP. • HTTPS and the security certificate to be used. • SNMPv1/v2c and...
Command Line Interface Guide
Page 190
... listed authentication methods that follow this command. Default Configuration The default enable list is used with the aaa authentication enable command are used by console, telnet, and SSH and only contains the method none. Uses no aaa authentication enable {default|list-name} • default - To return to the default configuration, use...
... listed authentication methods that follow this command. Default Configuration The default enable list is used with the aaa authentication enable command are used by console, telnet, and SSH and only contains the method none. Uses no aaa authentication enable {default|list-name} • default - To return to the default configuration, use...
Command Line Interface Guide
Page 192
"defaultList" is any character string used by the console and only contains the method none. Create a list by telnet and SSH and only contains the method local. For example, if none is down. Specify at least one from the following example configures authentication login. ...
"defaultList" is any character string used by the console and only contains the method none. Create a list by telnet and SSH and only contains the method local. For example, if none is down. Specify at least one from the following example configures authentication login. ...
Command Line Interface Guide
Page 194
... default enable password Use the enable password command in Line Configuration mode to specify the authentication method list when accessing a higher privilege level from a remote telnet or console. Syntax enable authentication {default|list-name} no user guidelines. Example The following example specifies the default authentication method when accessing a higher privilege level...
... default enable password Use the enable password command in Line Configuration mode to specify the authentication method list when accessing a higher privilege level from a remote telnet or console. Syntax enable authentication {default|list-name} no user guidelines. Example The following example specifies the default authentication method when accessing a higher privilege level...
Command Line Interface Guide
Page 197
... error, not if it fails. Example The following table: Keyword local none radius tacacs Source or destination Uses the local username database for a line (console, telnet, or SSH). If none is specified as an authentication method after radius, no form of all RADIUS servers for authentication. • method1 [method2...] - Syntax login...
... error, not if it fails. Example The following table: Keyword local none radius tacacs Source or destination Uses the local username database for a line (console, telnet, or SSH). If none is specified as an authentication method after radius, no form of all RADIUS servers for authentication. • method1 [method2...] - Syntax login...
Command Line Interface Guide
Page 201
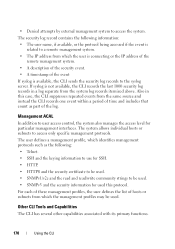
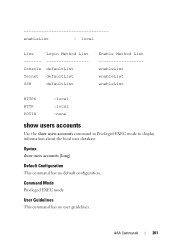
AAA Commands 201 enableList : local Line Login Method List Console defaultList Telnet defaultList SSH defaultList Enable Method List enableList enableList enableList HTTPS HTTP DOT1X :local :local :none show users accounts Use the show users accounts [long] Default Configuration This command has no user guidelines. Syntax show users accounts command in Privileged EXEC mode to display information about the local user database. Command Mode Privileged EXEC mode User Guidelines This command has no default configuration.
AAA Commands 201 enableList : local Line Login Method List Console defaultList Telnet defaultList SSH defaultList Enable Method List enableList enableList enableList HTTPS HTTP DOT1X :local :local :none show users accounts Use the show users accounts [long] Default Configuration This command has no user guidelines. Syntax show users accounts command in Privileged EXEC mode to display information about the local user database. Command Mode Privileged EXEC mode User Guidelines This command has no default configuration.
Command Line Interface Guide
Page 203
... 2005 08:29:29 Robert HTTP 172.16.0.8 Jan 19 2005 08:42:31 John SSH 172.16.0.1 Jan 19 2005 08:49:52 Betty Telnet 172.16.1.7 username Use the username command in Global Configuration mode to add a new user to suspend that user's access. (Range: 0-15) • encrypted - Level...
... 2005 08:29:29 Robert HTTP 172.16.0.8 Jan 19 2005 08:42:31 John SSH 172.16.0.1 Jan 19 2005 08:49:52 Betty Telnet 172.16.1.7 username Use the username command in Global Configuration mode to add a new user to suspend that user's access. (Range: 0-15) • encrypted - Level...
Command Line Interface Guide
Page 206
... the ACL rule is specified by the parameter list-name. Refers to be one of the following keywords: domain, echo, ftp, ftpdata, http, smtp, snmp, telnet, tftp, and www. • log - Allows all protocols. • eq - Destination IP address. • dstmask - Source IP mask. • dstip - access-list Use the access...
... the ACL rule is specified by the parameter list-name. Refers to be one of the following keywords: domain, echo, ftp, ftpdata, http, smtp, snmp, telnet, tftp, and www. • log - Allows all protocols. • eq - Destination IP address. • dstmask - Source IP mask. • dstip - access-list Use the access...
Command Line Interface Guide
Page 370
... the command format. A rule may be specified using the keyword 'any' to the list of the following keywords: domain, echo, efts, ftpdata, http, smtp, snmp, telnet, tftp, and www. 370 IPv6 Access List Commands Syntax {permit | deny} {every | {{icmp | igmp | ipv6 | tcp | udp | number} {any | source ipv6 prefix/prefix length} [eq...
... the command format. A rule may be specified using the keyword 'any' to the list of the following keywords: domain, echo, efts, ftpdata, http, smtp, snmp, telnet, tftp, and www. 370 IPv6 Access List Commands Syntax {permit | deny} {every | {{icmp | igmp | ipv6 | tcp | udp | number} {any | source ipv6 prefix/prefix length} [eq...
Command Line Interface Guide
Page 465
... the specified class definition a match condition based on the destination IPv6 address of a packet. User Guidelines There are : domain, echo, ftp, ftpdata, http, smtp,snmp, telnet, tftp, and www. • port-number - Syntax match dstl4port {portkey|port-number} • portkey - QoS Commands 465 Specifies one layer 4 port number. Specifies a layer 4 port...
... the specified class definition a match condition based on the destination IPv6 address of a packet. User Guidelines There are : domain, echo, ftp, ftpdata, http, smtp,snmp, telnet, tftp, and www. • port-number - Syntax match dstl4port {portkey|port-number} • portkey - QoS Commands 465 Specifies one layer 4 port number. Specifies a layer 4 port...