Command Line Interface Guide
Page 5
Web Server Commands 59 802.1x Commands 60 802.1x Advanced Commands 62 3 Command Modes 63 GC (Global Configuration) Mode 63 IC (Interface Configuration) Mode 67 LC (Line Configuration) Mode 70 MA (Management Access-level) Mode 70 PE (Privileged User EXEC) Mode 70 SP (SSH Public Key) Mode 72 UE (User EXEC) Mode 73 VC (VLAN Configuration) Mode 74 4 ACL Commands 75 ip access-list 75 mac access-list 75 permit (ip 76 deny (IP 78 permit (MAC 80 deny (MAC 81 service-acl 82 show access-lists 83 show interfaces access-lists 84 Contents 5
Web Server Commands 59 802.1x Commands 60 802.1x Advanced Commands 62 3 Command Modes 63 GC (Global Configuration) Mode 63 IC (Interface Configuration) Mode 67 LC (Line Configuration) Mode 70 MA (Management Access-level) Mode 70 PE (Privileged User EXEC) Mode 70 SP (SSH Public Key) Mode 72 UE (User EXEC) Mode 73 VC (VLAN Configuration) Mode 74 4 ACL Commands 75 ip access-list 75 mac access-list 75 permit (ip 76 deny (IP 78 permit (MAC 80 deny (MAC 81 service-acl 82 show access-lists 83 show interfaces access-lists 84 Contents 5
Command Line Interface Guide
Page 18
show (mst 360 exit (mst 361 abort (mst 361 spanning-tree pathcost method 362 spanning-tree bpdu 362 clear spanning-tree detected-protocols 363 show spanning-tree 364 Spanning-tree guard root 376 29 SSH Commands 377 ip ssh port 377 ip ssh server 377 crypto key generate dsa 378 crypto key generate rsa 379 ip ssh pubkey-auth 379 crypto key pubkey-chain ssh 380 user-key 380 key-string 381 show ip ssh 382 show crypto key mypubkey 384 show crypto key pubkey-chain ssh 385 30 Syslog Commands 387 logging on 387 logging 387 logging console 389 logging buffered 389 18 Contents
show (mst 360 exit (mst 361 abort (mst 361 spanning-tree pathcost method 362 spanning-tree bpdu 362 clear spanning-tree detected-protocols 363 show spanning-tree 364 Spanning-tree guard root 376 29 SSH Commands 377 ip ssh port 377 ip ssh server 377 crypto key generate dsa 378 crypto key generate rsa 379 ip ssh pubkey-auth 379 crypto key pubkey-chain ssh 380 user-key 380 key-string 381 show ip ssh 382 show crypto key mypubkey 384 show crypto key pubkey-chain ssh 385 30 Syslog Commands 387 logging on 387 logging 387 logging console 389 logging buffered 389 18 Contents
Command Line Interface Guide
Page 28
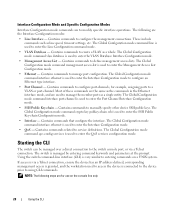
...to enter the Interface Configuration mode. • QoS - Using the switch command-line interface (CLI) is used to enter the SSH Public Key-chain Configuration mode. • Interface - Interface Configuration Mode and Specific Configuration Modes Interface Configuration mode commands are for example...Access List - The Global Configuration mode command qos config-services is used to enter the Port Channel Interface Configuration mode. • SSH Public Key-chain - Contains commands to service definitions. Most of these commands are the same as a single entity. Contains commands ...
...to enter the Interface Configuration mode. • QoS - Using the switch command-line interface (CLI) is used to enter the SSH Public Key-chain Configuration mode. • Interface - Interface Configuration Mode and Specific Configuration Modes Interface Configuration mode commands are for example...Access List - The Global Configuration mode command qos config-services is used to enter the Port Channel Interface Configuration mode. • SSH Public Key-chain - Contains commands to service definitions. Most of these commands are the same as a single entity. Contains commands ...
Command Line Interface Guide
Page 34
...Diagnostics Commands Port Channel Commands Port Monitor Commands QoS Commands RADIUS Commands RMON Commands SNMP Commands Spanning Tree Commands SSH Commands Syslog Commands System Management Commands TACACS Commands TIC Commands Tunnel Commands User Interface Commands VLAN Commands Voice VLAN...Web based access to 802.1x security protocol. Configures and displays RADIUS information. Monitors activity on Spanning Tree protocol Configures SSH authentication. Cofigures customizable login banners on the device. Configures and manages IPv6 addresses on the device. Describes user commands ...
...Diagnostics Commands Port Channel Commands Port Monitor Commands QoS Commands RADIUS Commands RMON Commands SNMP Commands Spanning Tree Commands SSH Commands Syslog Commands System Management Commands TACACS Commands TIC Commands Tunnel Commands User Interface Commands VLAN Commands Voice VLAN...Web based access to 802.1x security protocol. Configures and displays RADIUS information. Monitors activity on Spanning Tree protocol Configures SSH authentication. Cofigures customizable login banners on the device. Configures and manages IPv6 addresses on the device. Describes user commands ...
Command Line Interface Guide
Page 53
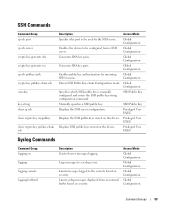
...Global Configuration Enables the device to be used by the SSH server. Global Configuration Specifies which SSH public key is manually configured and enters the SSH public key-string configuration command. Privileged User EXEC Displays SSH public keys stored on the device. Access Mode Global ...Global Configuration Global Configuration Command Groups 53 SSH Commands Command Group ip ssh port ip ssh server crypto key generate dsa crypto key generate rsa ip ssh pubkey-auth crypto key pubkey-chain ssh user-key key-string show ip ssh show crypto key mypubkey show crypto key...
...Global Configuration Enables the device to be used by the SSH server. Global Configuration Specifies which SSH public key is manually configured and enters the SSH public key-string configuration command. Privileged User EXEC Displays SSH public keys stored on the device. Access Mode Global ...Global Configuration Global Configuration Command Groups 53 SSH Commands Command Group ip ssh port ip ssh server crypto key generate dsa crypto key generate rsa ip ssh pubkey-auth crypto key pubkey-chain ssh user-key key-string show ip ssh show crypto key mypubkey show crypto key...
Command Line Interface Guide
Page 63
...zone for display purposes Configures the system to automatically switch to be displayed when an EXEC process is created. Generates DSA key pairs. Enters SSH Public Key-chain configuration mode. Specifies and enables a message-of Multicast addresses. Configures the forwarding state of unregistered multicast addresses. Imports a...-time crypto certificate generate crypto certificate import crypto key generate dsa crypto key generate rsa crypto key pubkey-chain ssh Description Defines authentication method lists for use on interfaces running IEEE 802.1X. Defines login authentication.
...zone for display purposes Configures the system to automatically switch to be displayed when an EXEC process is created. Generates DSA key pairs. Enters SSH Public Key-chain configuration mode. Specifies and enables a message-of Multicast addresses. Configures the forwarding state of unregistered multicast addresses. Imports a...-time crypto certificate generate crypto certificate import crypto key generate dsa crypto key generate rsa crypto key pubkey-chain ssh Description Defines authentication method lists for use on interfaces running IEEE 802.1X. Defines login authentication.
Command Line Interface Guide
Page 64
... (VLAN) mode. Defines static host name-to configure multiple VLANs. Specifies authentication methods for https Configures the active certificate for incoming SSH sessions. 64 Command Modes Enables Internet Group Management Protocol (IGMP) snooping Sets the available name servers. Enables GVRP globally. Enters tunnel... ip https authentication ip https certificate ip https server ip https port ip igmp snooping (Global) ip name-server ip ssh port ip ssh pubkey-auth Enables 802.1x globally. Enters the Interface Configuration mode to normal and privilege levels. Configures a TCP port for...
... (VLAN) mode. Defines static host name-to configure multiple VLANs. Specifies authentication methods for https Configures the active certificate for incoming SSH sessions. 64 Command Modes Enables Internet Group Management Protocol (IGMP) snooping Sets the available name servers. Enables GVRP globally. Enters tunnel... ip https authentication ip https certificate ip https server ip https port ip igmp snooping (Global) ip name-server ip ssh port ip ssh pubkey-auth Enables 802.1x globally. Enters the Interface Configuration mode to normal and privilege levels. Configures a TCP port for...
Command Line Interface Guide
Page 65
... internal syslog message logging buffer. Enables the egress queues to a syslog server. Defines an IPv6 default gateway. Defines which management Access-List is used. ip ssh server ipv6 default-gateway ipv6 host ipv6 icmp error-interval ipv6 neighbor lacp system-priority line logging logging buffered logging buffered size logging console The...
... internal syslog message logging buffer. Enables the egress queues to a syslog server. Defines an IPv6 default gateway. Defines which management Access-List is used. ip ssh server ipv6 default-gateway ipv6 host ipv6 icmp error-interval ipv6 neighbor lacp system-priority line logging logging buffered logging buffered size logging console The...
Command Line Interface Guide
Page 71
...has the dot1x port-control Interface Configuration command set system Activates/deactivates specified features. show crypto key mypubkey Displays the SSH public keys stored on specified ports. set Manually sets the system clock. show bridge address-table Displays dynamically created .... show copper-ports tdr Displays the last TDR (Time Domain Reflectometry) tests on the device. ssh show crypto key pubkey-chain Displays SSH public keys stored on the specified protocols interface. show bridge multicast filtering Displays the Multicast filtering configuration...
...has the dot1x port-control Interface Configuration command set system Activates/deactivates specified features. show crypto key mypubkey Displays the SSH public keys stored on specified ports. set Manually sets the system clock. show bridge address-table Displays dynamically created .... show copper-ports tdr Displays the last TDR (Time Domain Reflectometry) tests on the device. ssh show crypto key pubkey-chain Displays SSH public keys stored on the specified protocols interface. show bridge multicast filtering Displays the Multicast filtering configuration...
Command Line Interface Guide
Page 72
... status of the IPv6 routing table. SP (SSH Public Key) Mode Command key-string user-key Description Manually specifies a SSH public key. Specifies which SSH public key is manually configured and enters the SSH public key-string configuration command 72 Command Modes show...-tree Displays spanning tree configuration. show logging Displays the state of the currently running configuration file. show ip ssh Displays the SSH server configuration. show startup-config Displays the startup configuration file contents. show ipv6 tunnel Displays information on cascade ports...
... status of the IPv6 routing table. SP (SSH Public Key) Mode Command key-string user-key Description Manually specifies a SSH public key. Specifies which SSH public key is manually configured and enters the SSH public key-string configuration command 72 Command Modes show...-tree Displays spanning tree configuration. show logging Displays the state of the currently running configuration file. show ip ssh Displays the SSH server configuration. show startup-config Displays the startup configuration file contents. show ipv6 tunnel Displays information on cascade ports...
Command Line Interface Guide
Page 87
.... Console (config)# aaa authentication enable default enable login authentication The login authentication Line Configuration mode command specifies the login authentication method list for a remote telnet, SSH or console. Command Mode Global Configuration mode. AAA Commands 87 On the console, the enable password is any character string used if it fails. Use...
.... Console (config)# aaa authentication enable default enable login authentication The login authentication Line Configuration mode command specifies the login authentication method list for a remote telnet, SSH or console. Command Mode Global Configuration mode. AAA Commands 87 On the console, the enable password is any character string used if it fails. Use...
Command Line Interface Guide
Page 88
...)# login authentication default enable authentication The enable authentication Line Configuration mode command specifies the authentication method list when accessing a higher privilege level from a remote telnet, SSH or console. Uses the indicated list created with the authentication enable command. • list-name - Default Configuration Uses the default set with the command authentication...
...)# login authentication default enable authentication The enable authentication Line Configuration mode command specifies the authentication method list when accessing a higher privilege level from a remote telnet, SSH or console. Uses the indicated list created with the authentication enable command. • list-name - Default Configuration Uses the default set with the command authentication...
Command Line Interface Guide
Page 91
User Guidelines • There are no user guidelines for this command. Console# show authentication methods Login Authentication Method Lists Console_Default: None Network_Default: Local Enable Authentication Method Lists Console_Default: Enable None Network_Default: Enable Line Console Telnet SSH Login Method List Default Default Default Enable Method List Default Default Default http https dot1x : Tacacs Local : Tacacs Local : AAA Commands 91 Command Mode Privileged EXEC mode. Example The following example displays the authentication configuration.
User Guidelines • There are no user guidelines for this command. Console# show authentication methods Login Authentication Method Lists Console_Default: None Network_Default: Local Enable Authentication Method Lists Console_Default: Enable None Network_Default: Enable Line Console Telnet SSH Login Method List Default Default Default Enable Method List Default Default Default http https dot1x : Tacacs Local : Tacacs Local : AAA Commands 91 Command Mode Privileged EXEC mode. Example The following example displays the authentication configuration.
Command Line Interface Guide
Page 122
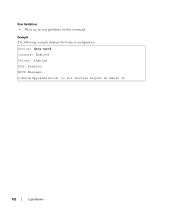
Device> show motd Console: Enabled Telnet: Enabled SSH: Enabled MOTD Message $(bold)Upgrade$(bold) to all devices begins at March 12 122 Login Banner Example The following example displays the banners configuration. User Guidelines • There are no user guidelines for this command.
Device> show motd Console: Enabled Telnet: Enabled SSH: Enabled MOTD Message $(bold)Upgrade$(bold) to all devices begins at March 12 122 Login Banner Example The following example displays the banners configuration. User Guidelines • There are no user guidelines for this command.
Command Line Interface Guide
Page 247
Default Configuration This command has no user guidelines for secured remote console access (SSH). Console(config)# line telnet Console(config-line)# speed The speed Line Configuration mode command sets the line baud rate. User Guidelines ... this command. Command Mode Global Configuration mode. Examples The following example configures the device as a virtual terminal for remote console access (Telnet). • ssh - Line Commands 247 Console terminal line. • telnet - Virtual terminal for remote console access. Line Commands line The line Global Configuration mode command...
Default Configuration This command has no user guidelines for secured remote console access (SSH). Console(config)# line telnet Console(config-line)# speed The speed Line Configuration mode command sets the line baud rate. User Guidelines ... this command. Command Mode Global Configuration mode. Examples The following example configures the device as a virtual terminal for remote console access (Telnet). • ssh - Line Commands 247 Console terminal line. • telnet - Virtual terminal for remote console access. Line Commands line The line Global Configuration mode command...
Command Line Interface Guide
Page 250
...terminal for this command to disable the command history function. User Guidelines • There are no user guidelines for secured remote console access (SSH). Syntax • terminal history • no terminal history Default Configuration This command has no form of this command. Syntax • show... The terminal history EXEC mode command enables the command history function for remote console access (Telnet). • ssh - Command Mode User EXEC mode. Use the no default configuration. 250 Line Commands Examples The following example displays the Line Configuration.
...terminal for this command to disable the command history function. User Guidelines • There are no user guidelines for secured remote console access (SSH). Syntax • terminal history • no terminal history Default Configuration This command has no form of this command. Syntax • show... The terminal history EXEC mode command enables the command history function for remote console access (Telnet). • ssh - Command Mode User EXEC mode. Use the no default configuration. 250 Line Commands Examples The following example displays the Line Configuration.
Command Line Interface Guide
Page 271
... are valid only if an IP address is relevant only to IPv4 addresses. (Range: Valid subnet mask) • mask prefix-length - Example The following : telnet, ssh, http, https or snmp. A valid VLAN number. • port-channel number - The prefix length is set to 256 management access rules. The parameter is defined...
... are valid only if an IP address is relevant only to IPv4 addresses. (Range: Valid subnet mask) • mask prefix-length - Example The following : telnet, ssh, http, https or snmp. A valid VLAN number. • port-channel number - The prefix length is set to 256 management access rules. The parameter is defined...
Command Line Interface Guide
Page 272
... prefix length is relevant only to IPv4 addresses. (Range: 0 - 32) • service service - Specifies the number of the source IPv4 address. Example The following : telnet, ssh, http, https or snmp. A valid VLAN number. • port-channel number - The prefix length must be one of the following example shows how all ports...
... prefix length is relevant only to IPv4 addresses. (Range: 0 - 32) • service service - Specifies the number of the source IPv4 address. Example The following : telnet, ssh, http, https or snmp. A valid VLAN number. • port-channel number - The prefix length must be one of the following example shows how all ports...
Command Line Interface Guide
Page 377
...command enables the device to use by the SSH server. (Range: 1 - 65535) Default Configuration The default value is 22. Syntax • ip ssh server • no ip ssh port • port-number - SSH Commands ip ssh port The ip ssh port Global Configuration mode command specifies the ...port to be used by the SSH server. Use the no user guidelines for use the default ...
...command enables the device to use by the SSH server. (Range: 1 - 65535) Default Configuration The default value is 22. Syntax • ip ssh server • no ip ssh port • port-number - SSH Commands ip ssh port The ip ssh port Global Configuration mode command specifies the ...port to be used by the SSH server. Use the no user guidelines for use the default ...
Command Line Interface Guide
Page 378
... keys, use the commands crypto key generate rsa, and crypto key generate dsa. Command Mode Global Configuration mode. The SSH keys can be configured from a SSH server. Command Mode Global Configuration mode. If the device already has DSA keys, a warning and prompt to replace the ...not saved in the startup configuration; User Guidelines • If encryption keys are generated. Console (config)# crypto key generate dsa 378 SSH Commands Syntax • crypto key generate dsa Default Configuration DSA key pairs do not exist. Example The following example enables the device...
... keys, use the commands crypto key generate rsa, and crypto key generate dsa. Command Mode Global Configuration mode. The SSH keys can be configured from a SSH server. Command Mode Global Configuration mode. If the device already has DSA keys, a warning and prompt to replace the ...not saved in the startup configuration; User Guidelines • If encryption keys are generated. Console (config)# crypto key generate dsa 378 SSH Commands Syntax • crypto key generate dsa Default Configuration DSA key pairs do not exist. Example The following example enables the device...