Command Line Interface Guide
Page 53
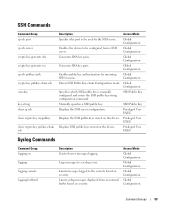
... Group logging on the device. Limits messages logged to be used by the SSH server. Global Configuration Enables the device to the console based on severity. Global Configuration Enters SSH Public Key-chain Configuration mode. Privileged User EXEC Displays the SSH public keys stored on logging logging console logging buffered Description Controls error messages...
... Group logging on the device. Limits messages logged to be used by the SSH server. Global Configuration Enables the device to the console based on severity. Global Configuration Enters SSH Public Key-chain Configuration mode. Privileged User EXEC Displays the SSH public keys stored on logging logging console logging buffered Description Controls error messages...
Command Line Interface Guide
Page 63
... the system to automatically switch to be displayed before the username and password login prompts. Enters SSH Public Key-chain configuration mode. Command Modes 63 Command Modes GC (Global Configuration) Mode Command aaa authentication enable aaa authentication login aaa authentication dot1x arp arp timeout asset-tag banner exec banner login banner motd...
... the system to automatically switch to be displayed before the username and password login prompts. Enters SSH Public Key-chain configuration mode. Command Modes 63 Command Modes GC (Global Configuration) Mode Command aaa authentication enable aaa authentication login aaa authentication dot1x arp arp timeout asset-tag banner exec banner login banner motd...
Command Line Interface Guide
Page 64
...Specifies authentication methods for https Configures the active certificate for incoming SSH sessions. 64 Command Modes Enables public key authentication for HTTPS. Sets a local password to control access to complete unqualified host names. Enables GVRP globally. Enters the Interface Configuration mode to -address ...https authentication ip https certificate ip https server ip https port ip igmp snooping (Global) ip name-server ip ssh port ip ssh pubkey-auth Enables 802.1x globally. Specifies the TCP port for http. Specifies the port to be configured from a browser. Enters...
...Specifies authentication methods for https Configures the active certificate for incoming SSH sessions. 64 Command Modes Enables public key authentication for HTTPS. Sets a local password to control access to complete unqualified host names. Enables GVRP globally. Enters the Interface Configuration mode to -address ...https authentication ip https certificate ip https server ip https port ip igmp snooping (Global) ip name-server ip ssh port ip ssh pubkey-auth Enables 802.1x globally. Specifies the TCP port for http. Specifies the port to be configured from a browser. Enters...
Command Line Interface Guide
Page 65
Configures the system LACP priority. Controls error messages logging. Enables jumbo frames for a remote telnet or console. Improves RADIUS response times when servers are unavailable. ip ssh server ipv6 default-gateway ipv6 host ipv6 icmp error-interval ipv6 neighbor lacp system-priority...server. Specifies the login authentication method list for the device. Logs messages to the console based on severity. Enables the egress queues to be configured from a SSH server. Specifies a RADIUS server host. Defines a static host name-to be expedite queues. Configures the rate...
Configures the system LACP priority. Controls error messages logging. Enables jumbo frames for a remote telnet or console. Improves RADIUS response times when servers are unavailable. ip ssh server ipv6 default-gateway ipv6 host ipv6 icmp error-interval ipv6 neighbor lacp system-priority...server. Specifies the login authentication method list for the device. Logs messages to the console based on severity. Enables the egress queues to be configured from a SSH server. Specifies a RADIUS server host. Defines a static host name-to be expedite queues. Configures the rate...
Command Line Interface Guide
Page 71
...protocol migration process on all interfaces or on an interface. reload Reloads the operating system. show crypto key mypubkey Displays the SSH public keys stored on the device. Displays Multicast MAC address table information. show banner Displays the banners configuration. show bridge ...from a source to User EXEC mode. show bridge address-table Displays dynamically created entries in all 802.1X-enabled ports or the specified 802.1X-enabled port. show dot1x users Displays 802.1X statistics for a specified interface. dot1x re-authenticate Manually initiates a re...
...protocol migration process on all interfaces or on an interface. reload Reloads the operating system. show crypto key mypubkey Displays the SSH public keys stored on the device. Displays Multicast MAC address table information. show banner Displays the banners configuration. show bridge ...from a source to User EXEC mode. show bridge address-table Displays dynamically created entries in all 802.1X-enabled ports or the specified 802.1X-enabled port. show dot1x users Displays 802.1X statistics for a specified interface. dot1x re-authenticate Manually initiates a re...
Command Line Interface Guide
Page 87
... authentication Line Configuration mode command specifies the login authentication method list for a remote telnet, SSH or console. Syntax • login authentication {default | list-name} • no form of this list. If no password is set , only the enable password is checked. The method argument identifies the list of authentication are used only...
... authentication Line Configuration mode command specifies the login authentication method list for a remote telnet, SSH or console. Syntax • login authentication {default | list-name} • no form of this list. If no password is set , only the enable password is checked. The method argument identifies the list of authentication are used only...
Command Line Interface Guide
Page 88
... the no form of this command. User Guidelines • There are no enable authentication • default - User Guidelines • Changing login authentication from a remote telnet, SSH or console. Console (config)# line console Console (config-line)# login authentication default enable authentication The enable authentication Line Configuration mode command specifies the authentication method list when accessing...
... the no form of this command. User Guidelines • There are no enable authentication • default - User Guidelines • Changing login authentication from a remote telnet, SSH or console. Console (config)# line console Console (config-line)# login authentication default enable authentication The enable authentication Line Configuration mode command specifies the authentication method list when accessing...
Command Line Interface Guide
Page 91
Command Mode Privileged EXEC mode. User Guidelines • There are no user guidelines for this command. Example The following example displays the authentication configuration. Console# show authentication methods Login Authentication Method Lists Console_Default: None Network_Default: Local Enable Authentication Method Lists Console_Default: Enable None Network_Default: Enable Line Console Telnet SSH Login Method List Default Default Default Enable Method List Default Default Default http https dot1x : Tacacs Local : Tacacs Local : AAA Commands 91
Command Mode Privileged EXEC mode. User Guidelines • There are no user guidelines for this command. Example The following example displays the authentication configuration. Console# show authentication methods Login Authentication Method Lists Console_Default: None Network_Default: Local Enable Authentication Method Lists Console_Default: Enable None Network_Default: Enable Line Console Telnet SSH Login Method List Default Default Default Enable Method List Default Default Default http https dot1x : Tacacs Local : Tacacs Local : AAA Commands 91
Command Line Interface Guide
Page 122
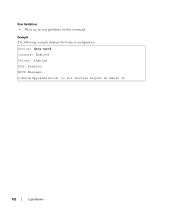
Example The following example displays the banners configuration. User Guidelines • There are no user guidelines for this command. Device> show motd Console: Enabled Telnet: Enabled SSH: Enabled MOTD Message $(bold)Upgrade$(bold) to all devices begins at March 12 122 Login Banner
Example The following example displays the banners configuration. User Guidelines • There are no user guidelines for this command. Device> show motd Console: Enabled Telnet: Enabled SSH: Enabled MOTD Message $(bold)Upgrade$(bold) to all devices begins at March 12 122 Login Banner
Command Line Interface Guide
Page 250
... the current terminal session. User Guidelines • There are no user guidelines for remote console access (Telnet). • ssh - Use the no default configuration. 250 Line Commands Syntax • terminal history • no terminal history Default Configuration This... (config)# line console Console(config-line)# exec-timeout 20 terminal history The terminal history EXEC mode command enables the command history function for secured remote console access (SSH). Syntax • show line User EXEC mode command displays line parameters. Default Configuration Default value is console...
... the current terminal session. User Guidelines • There are no user guidelines for remote console access (Telnet). • ssh - Use the no default configuration. 250 Line Commands Syntax • terminal history • no terminal history Default Configuration This... (config)# line console Console(config-line)# exec-timeout 20 terminal history The terminal history EXEC mode command enables the command history function for secured remote console access (SSH). Syntax • show line User EXEC mode command displays line parameters. Default Configuration Default value is console...
Command Line Interface Guide
Page 377
... mode command specifies the port to be used by the SSH server as 8080. Console (config)# ip ssh port 8080 ip ssh server The ip ssh server Global Configuration mode command enables the device to be configured from a SSH server. Syntax • ip ssh server • no ip ssh port • port-number - Use the no form of...
... mode command specifies the port to be used by the SSH server as 8080. Console (config)# ip ssh port 8080 ip ssh server The ip ssh server Global Configuration mode command enables the device to be configured from a SSH server. Syntax • ip ssh server • no ip ssh port • port-number - Use the no form of...
Command Line Interface Guide
Page 378
...pairs. Console (config)# ip ssh server crypto key generate dsa The ip ssh server Global Configuration mode command generates DSA key pairs. The SSH keys can be configured from a SSH server. Example The following example enables the device to execute. • DSA key size is enabled. User Guidelines • ...displayed with new keys is displayed. • This command is in standby until the keys are generated in the FLASH. To generate SSH server keys, use the commands crypto key generate rsa, and crypto key generate dsa. however, the keys generated by this command ...
...pairs. Console (config)# ip ssh server crypto key generate dsa The ip ssh server Global Configuration mode command generates DSA key pairs. The SSH keys can be configured from a SSH server. Example The following example enables the device to execute. • DSA key size is enabled. User Guidelines • ...displayed with new keys is displayed. • This command is in standby until the keys are generated in the FLASH. To generate SSH server keys, use the commands crypto key generate rsa, and crypto key generate dsa. however, the keys generated by this command ...
Command Line Interface Guide
Page 379
...RSA key pairs. Example The following example generates RSA key pairs. Console (config)# crypto key generate rsa ip ssh pubkey-auth The ip ssh pubkey-auth Global Configuration mode command enables public key authentication for the RSA key is 2048 bits. • This command is displayed. • The... maximum supported size for incoming SSH sessions. Syntax • ip ssh pubkey-auth • no form of time to replace the existing keys with...
...RSA key pairs. Example The following example generates RSA key pairs. Console (config)# crypto key generate rsa ip ssh pubkey-auth The ip ssh pubkey-auth Global Configuration mode command enables public key authentication for the RSA key is 2048 bits. • This command is displayed. • The... maximum supported size for incoming SSH sessions. Syntax • ip ssh pubkey-auth • no form of time to replace the existing keys with...
Command Line Interface Guide
Page 380
... key is used when you need to remove a SSH public key. 380 SSH Commands Use the no form of this command. Example The following example enables public key authentication for this command to manually specify SSH client's public keys. Example The following example enters the SSH Public Key-chain Configuration mode. The mode is manually...
... key is used when you need to remove a SSH public key. 380 SSH Commands Use the no form of this command. Example The following example enables public key authentication for this command to manually specify SSH client's public keys. Example The following example enters the SSH Public Key-chain Configuration mode. The mode is manually...
Command Line Interface Guide
Page 381
... username • username - Specify SSH public key row by OpenSSH. Syntax • key-string row key-string • row - Default Configuration By default, the keys do not exist. RSA key. • dsa - DSA key. Example The following example enables a SSH public key to be up to ...specify the key. SSH Commands 381 Syntax • user-key username {rsa | dsa} • no keys. User Guidelines • Follow this command...
... username • username - Specify SSH public key row by OpenSSH. Syntax • key-string row key-string • row - Default Configuration By default, the keys do not exist. RSA key. • dsa - DSA key. Example The following example enables a SSH public key to be up to ...specify the key. SSH Commands 381 Syntax • user-key username {rsa | dsa} • no keys. User Guidelines • Follow this command...
Command Line Interface Guide
Page 383
...ssh SSH server enabled. SSH Public Key Authentication is enabled. Default Configuration This command has no user guidelines for this command. DSA (DSS) key was generated. Active incoming sessions: IP address SSH Version username Cipher 172.16.0.1 John Brown 2.0 3 DES Auth Code ---------HMAC-SH1 The following example displays the SSH...: Field Description IP address Client address SSH username User name Version SSH version number Cipher Encryption type (3DES, Blowfish, RC4) Auth Code Authentication Code (HMAC-MD5, HMAC-SHA1) SSH Commands 383 Port: 22 RSA key ...
...ssh SSH server enabled. SSH Public Key Authentication is enabled. Default Configuration This command has no user guidelines for this command. DSA (DSS) key was generated. Active incoming sessions: IP address SSH Version username Cipher 172.16.0.1 John Brown 2.0 3 DES Auth Code ---------HMAC-SH1 The following example displays the SSH...: Field Description IP address Client address SSH username User name Version SSH version number Cipher Encryption type (3DES, Blowfish, RC4) Auth Code Authentication Code (HMAC-MD5, HMAC-SHA1) SSH Commands 383 Port: 22 RSA key ...
Command Line Interface Guide
Page 428
...mode. Virtual terminal for Bob. Example The following example reactivates a locked out user account for remote console access (Telnet). • ssh - Default Configuration This command has no default configuration. Console (config)# aaa login-history file set username active The set username name ...active • name - Example The following example enables writing to login history file. Console# set username bob active set line active The set line {console | telnet |ssh} active • console - Console terminal line. • telnet - Virtual ...
...mode. Virtual terminal for Bob. Example The following example reactivates a locked out user account for remote console access (Telnet). • ssh - Default Configuration This command has no default configuration. Console (config)# aaa login-history file set username active The set username name ...active • name - Example The following example enables writing to login history file. Console# set username bob active set line active The set line {console | telnet |ssh} active • console - Console terminal line. • telnet - Virtual ...
Command Line Interface Guide
Page 430
... after series of a password. 430 TIC Commands History hold time: 365 days Lock-out: Disabled Enable Passwords Level Aging ----- ----- 1 90 15 90 Expiry date ----------Jan 18 2005 Jan 18 2005 Lockout ------1 0 Line Passwords Level ----Console Telnet SSH Aging ----90 90 Expiry date ----------Jan 18 2005 Jan 21 2005 Lockout ------LOCKOUT 0 The following...
... after series of a password. 430 TIC Commands History hold time: 365 days Lock-out: Disabled Enable Passwords Level Aging ----- ----- 1 90 15 90 Expiry date ----------Jan 18 2005 Jan 18 2005 Lockout ------1 0 Line Passwords Level ----Console Telnet SSH Aging ----90 90 Expiry date ----------Jan 18 2005 Jan 21 2005 Lockout ------LOCKOUT 0 The following...
Command Line Interface Guide
Page 431
... is locked out it specifies how many times a user has failed to enter the correct password since the last successful login. If the password is enabled, it specifies "LOCKOUT". The name of users. Console# show users login-history Login Time Jan 18 2004 23:58:17 Jan 19 2004 07:59...:29 Jan 19 2004 08:42:31 Jan 19 2004 08:49:52 Username -------Robert Robert Bob Robert John Betty Protocol -------HTTP HTTP Serial HTTP SSH Telnet Location -------172.16.1.8 172.16.0.8 172.16.0.8 172.16.0.1 172.16.1.7 TIC Commands 431
... is locked out it specifies how many times a user has failed to enter the correct password since the last successful login. If the password is enabled, it specifies "LOCKOUT". The name of users. Console# show users login-history Login Time Jan 18 2004 23:58:17 Jan 19 2004 07:59...:29 Jan 19 2004 08:42:31 Jan 19 2004 08:49:52 Username -------Robert Robert Bob Robert John Betty Protocol -------HTTP HTTP Serial HTTP SSH Telnet Location -------172.16.1.8 172.16.0.8 172.16.0.8 172.16.0.1 172.16.1.7 TIC Commands 431
User's Guide
Page 22
...Assignment (DVA) allows network administrators to automatically assign users to define classification actions and rules for specific ingress ports. The SSH server feature enables an SSH client to that is not tied to establish a secure, encrypted connection with a device. If they are either manually ...defined or learned on page 243. SSH uses RSA Public Key cryptography for validation of users accessing the device. RADIUS Client RADIUS is...
...Assignment (DVA) allows network administrators to automatically assign users to define classification actions and rules for specific ingress ports. The SSH server feature enables an SSH client to that is not tied to establish a secure, encrypted connection with a device. If they are either manually ...defined or learned on page 243. SSH uses RSA Public Key cryptography for validation of users accessing the device. RADIUS Client RADIUS is...