Product Manual
Page 5
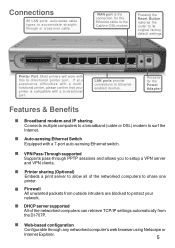
... through PPTP sessions and allows you experience difficulties with a bi-directional port. Auto-sensing Ethernet Switch Equipped with this bi-directional printer port. Firewall All unwanted packets from the DI-707P. Printer sharing (Optional) Embeds a print server to allow all of the networked computers can retrieve TCP/IP settings automatically from outside intruders...
... through PPTP sessions and allows you experience difficulties with a bi-directional port. Auto-sensing Ethernet Switch Equipped with this bi-directional printer port. Firewall All unwanted packets from the DI-707P. Printer sharing (Optional) Embeds a print server to allow all of the networked computers can retrieve TCP/IP settings automatically from outside intruders...
Product Manual
Page 7
...consists of the information moving to and from your network and analyzes each port and forwards the data to all other . The most circumstances, a firewall is the term used . A NIC is called packet filtering. Each computer must have a Network Interface Card (NIC), which communicates the data ...and speeds up for a specific piece of data. A switch is more sophisticated, in order to continue the connection between computers. A firewall can also run specific security functions based on the type of application or type of port that it can determine the destination port for your...
...consists of the information moving to and from your network and analyzes each port and forwards the data to all other . The most circumstances, a firewall is the term used . A NIC is called packet filtering. Each computer must have a Network Interface Card (NIC), which communicates the data ...and speeds up for a specific piece of data. A switch is more sophisticated, in order to continue the connection between computers. A firewall can also run specific security functions based on the type of application or type of port that it can determine the destination port for your...
Product Manual
Page 20
... servers in the LAN (Local Area Network). Using the Configuration Menu Advanced > Virtual Server The DI-707P can be configured as a virtual server so that will be available. 20 The DI-707P firewall feature filters out unrecognized packets to the outside world. If you wish, you can make some ...of ports can be specified with the DI-707P are invisible to protect your LAN network so all computers networked with a...
... servers in the LAN (Local Area Network). Using the Configuration Menu Advanced > Virtual Server The DI-707P can be configured as a virtual server so that will be available. 20 The DI-707P firewall feature filters out unrecognized packets to the outside world. If you wish, you can make some ...of ports can be specified with the DI-707P are invisible to protect your LAN network so all computers networked with a...
Product Manual
Page 26
.... Leaving the field blank sleects all IPs. NameEnter the name of both sources. Using the Configuration Menu Advanced > Firewall Firewall Rules is an advance feature used to deny or allow or deny traffic to pass through the device. ActionSelect Allow or Deny to enter an ... as IP Filters with additional settings. Enabled or DisabledClick Enabled to apply the filter policy or click Disabled to allow traffic from passing through the DI-804HV. Interface Source Choose between a LAN or WAN destination.
.... Leaving the field blank sleects all IPs. NameEnter the name of both sources. Using the Configuration Menu Advanced > Firewall Firewall Rules is an advance feature used to deny or allow or deny traffic to pass through the device. ActionSelect Allow or Deny to enter an ... as IP Filters with additional settings. Enabled or DisabledClick Enabled to apply the filter policy or click Disabled to allow traffic from passing through the DI-804HV. Interface Source Choose between a LAN or WAN destination.
Product Manual
Page 27
If you want the policy to apply to. Port RangeEnter in the port range of the following protocols: TCP, UDP, or ICMP. ScheduleSelect Always, or choose From and enter the time period during which the virtual service will be available 27 If it is only a single port that you want to use all the ports, you can leave the port range empty. Using the Configuration Menu Advanced > Firewall Continued ProtocolSelect one of the TCP/UDP ports that you want the policy applied to, then enter the port number in the Start Port field and leave the End Port field blank.
If you want the policy to apply to. Port RangeEnter in the port range of the following protocols: TCP, UDP, or ICMP. ScheduleSelect Always, or choose From and enter the time period during which the virtual service will be available 27 If it is only a single port that you want to use all the ports, you can leave the port range empty. Using the Configuration Menu Advanced > Firewall Continued ProtocolSelect one of the TCP/UDP ports that you want the policy applied to, then enter the port number in the Start Port field and leave the End Port field blank.
Product Manual
Page 37
... packets and if it packets contain suspecious information, it is a form of the packets transmitted through the DI707P. It carefully inspects all of firewall protection that is preset to allow certain popular applications such as MSN messenger to check if a computer is using the router without making any ... you want to keep UPnP Setting on the Internet will automatically drop those packets. It sends ping packets and listens for replies from the DI-707P when it will not get a reply back from the specific host. UPnP Setting- This may help to restart the unit.
... packets and if it packets contain suspecious information, it is a form of the packets transmitted through the DI707P. It carefully inspects all of firewall protection that is preset to allow certain popular applications such as MSN messenger to check if a computer is using the router without making any ... you want to keep UPnP Setting on the Internet will automatically drop those packets. It sends ping packets and listens for replies from the DI-707P when it will not get a reply back from the specific host. UPnP Setting- This may help to restart the unit.
Product Manual
Page 79
Step 3 Configure your firewall software for more information on the computer. From the Security tab, click the button to restore the settings to Never Dial a Connection. Frequently Asked Questions (... tab and click the button to restore these settings to the desktop and close any Internet security software running on disabling or configuring it. Software firewalls like Zone Alarm, Black Ice, Sygate, Norton Personal...
Step 3 Configure your firewall software for more information on the computer. From the Security tab, click the button to restore the settings to Never Dial a Connection. Frequently Asked Questions (... tab and click the button to restore these settings to the desktop and close any Internet security software running on disabling or configuring it. Software firewalls like Zone Alarm, Black Ice, Sygate, Norton Personal...
Product Manual
Page 88
Once the modem has established a link to connect using TCP/IP. Wait about 30 seconds and log back into the web-based configuration (192.168.0.1) and configure the WAN side to use the AOL software, you can do that without configuring the router's firewall settings. Step 10 Click on ....share my Internet connection provided by @aol.com for authentication bypassing the client software. Step 9 Turn off your ISP, plug the power back into the D-Link router. Under WAN, click Connect. Can I setup my router to work with Earthlink DSL or any PPPoE connection? (continued) Step 8 Click Apply....
Once the modem has established a link to connect using TCP/IP. Wait about 30 seconds and log back into the web-based configuration (192.168.0.1) and configure the WAN side to use the AOL software, you can do that without configuring the router's firewall settings. Step 10 Click on ....share my Internet connection provided by @aol.com for authentication bypassing the client software. Step 9 Turn off your ISP, plug the power back into the D-Link router. Under WAN, click Connect. Can I setup my router to work with Earthlink DSL or any PPPoE connection? (continued) Step 8 Click Apply....
Product Manual
Page 90
...or Macintosh operating systems please refer to Step 4 of the public network outside world. The DMZ may typically also have already been requested. D-Link, a leading maker of the computer you to forward all incoming ports to no other company information would be served to use as a ...neutral zone between North Korea and South Korea following the UN police action in the early 1950s.) A DMZ is configured for access to a firewall and effectively acts as a proxy server as well. The DMZ host then initiates sessions for setting up between a company´s private network and ...
...or Macintosh operating systems please refer to Step 4 of the public network outside world. The DMZ may typically also have already been requested. D-Link, a leading maker of the computer you to forward all incoming ports to no other company information would be served to use as a ...neutral zone between North Korea and South Korea following the UN police action in the early 1950s.) A DMZ is configured for access to a firewall and effectively acts as a proxy server as well. The DMZ host then initiates sessions for setting up between a company´s private network and ...
Product Manual
Page 92
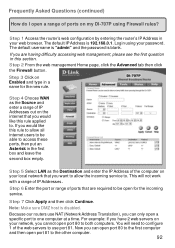
...For example: If you want to allow all internet users to be open for the new rule. Login using Firewall rules? Step 4 Choose WAN as the Destination and enter the IP Address of the computer on your local network...our routers use port 81. Step 2 From the web management Home page, click the Advanced tab then click the Firewall button. This will need to access these ports, then put an Asterisk in a name for the incoming service. ... 92 Frequently Asked Questions (continued) How do I open a range of ports on my DI-707P using your password. The default IP Address is 192.168.0.1.
...For example: If you want to allow all internet users to be open for the new rule. Login using Firewall rules? Step 4 Choose WAN as the Destination and enter the IP Address of the computer on your local network...our routers use port 81. Step 2 From the web management Home page, click the Advanced tab then click the Firewall button. This will need to access these ports, then put an Asterisk in a name for the incoming service. ... 92 Frequently Asked Questions (continued) How do I open a range of ports on my DI-707P using your password. The default IP Address is 192.168.0.1.
Product Manual
Page 95
...) How can I use eDonkey behind my D-Link Router? Enter username (admin) and your router to Destination, select LAN under interface. Step 3 Create a new firewall rule: Click Enabled. Next to allow remote connections. Click Always or set a schedule. You must open ports on Advanced and then click Firewall. Step 2 Click on your password (leave...
...) How can I use eDonkey behind my D-Link Router? Enter username (admin) and your router to Destination, select LAN under interface. Step 3 Create a new firewall rule: Click Enabled. Next to allow remote connections. Click Always or set a schedule. You must open ports on Advanced and then click Firewall. Step 2 Click on your password (leave...
Product Manual
Page 98
... for KaZaA and Grokster? Click Apply. Step 5 Enter the IP Address of your password (blank by default). In most cases, you did not enable proxy/firewall in the Private and Public Port boxes. Frequently Asked Questions (continued) How do not have to configure anything on the router or on Advanced and...
... for KaZaA and Grokster? Click Apply. Step 5 Enter the IP Address of your password (blank by default). In most cases, you did not enable proxy/firewall in the Private and Public Port boxes. Frequently Asked Questions (continued) How do not have to configure anything on the router or on Advanced and...
Product Manual
Page 100
D-Link is to use iChat? -for signs that it on Advanced and then click Firewall. 100 iChat uses the following ports: 5060 (UDP) 5190 (TCP)...visit http://www.HomenetHelp.com How do I set up my router to put the router in the firewall. Step 2 Click on themselves to allow incoming traffic while using (only) standard NAT and all ...more work with other h.323 software packages. Frequently Asked Questions (continued) How do I use NetMeeting with my D-Link Router? This is somewhat different than a router normally does and may actually be a netmeeting packet. You must...
D-Link is to use iChat? -for signs that it on Advanced and then click Firewall. 100 iChat uses the following ports: 5060 (UDP) 5190 (TCP)...visit http://www.HomenetHelp.com How do I set up my router to put the router in the firewall. Step 2 Click on themselves to allow incoming traffic while using (only) standard NAT and all ...more work with other h.323 software packages. Frequently Asked Questions (continued) How do I use NetMeeting with my D-Link Router? This is somewhat different than a router normally does and may actually be a netmeeting packet. You must...
Product Manual
Page 101
... do I set a schedule. Step 5 Repeat steps 3 and 4 enter ichat2 and open ports 1638416403 (UDP). Next to use iChat? -for Macintosh users(continued) Step 3 Create a new firewall rule: Click Enabled. Click Always or set up my router to Source, select WAN under interface.
... do I set a schedule. Step 5 Repeat steps 3 and 4 enter ichat2 and open ports 1638416403 (UDP). Next to use iChat? -for Macintosh users(continued) Step 3 Create a new firewall rule: Click Enabled. Click Always or set up my router to Source, select WAN under interface.
Product Manual
Page 102
...of the computer on your virtual server entry (ichat3). If using Mac OS X Firewall, you want to allow the incoming service to temporarily turn off the firewall in the router: Step 1 Choose Apple menu > System Preferences. Step 3 Click the Firewall tab. Step 7 In the Description field type in : 5060, 16384-16403. ...Port. To use iChat? -for Macintosh users- Step 5 Choose Other from the Port Name pop-up my router to use the Mac OS X Firewall, you must open the same ports as in the Sharing preference pane on Advanced and then Virtual Server. Step 5 Select TCP for your local network...
...of the computer on your virtual server entry (ichat3). If using Mac OS X Firewall, you want to allow the incoming service to temporarily turn off the firewall in the router: Step 1 Choose Apple menu > System Preferences. Step 3 Click the Firewall tab. Step 7 In the Description field type in : 5060, 16384-16403. ...Port. To use iChat? -for Macintosh users- Step 5 Choose Other from the Port Name pop-up my router to use the Mac OS X Firewall, you must open the same ports as in the Sharing preference pane on Advanced and then Virtual Server. Step 5 Select TCP for your local network...
Product Manual
Page 103
...OS X 10.2 and later The following information is from the Port Name pop-up menu. This is required for Macintosh users- Step 3 Click the Firewall tab. The number 5190 should already be blocked. If you have chosen in for you. Step 2 Choose View > Sharing. Frequently Asked Questions (...continued) How do I send or receive a file via iChat when the Mac OSX firewall is active? -for the sender. Step 5 Choose AOL IM from the online Macintosh AppleCare knowledge base: "iChat cannot send or receive a file when ...
...OS X 10.2 and later The following information is from the Port Name pop-up menu. This is required for Macintosh users- Step 3 Click the Firewall tab. The number 5190 should already be blocked. If you have chosen in for you. Step 2 Choose View > Sharing. Frequently Asked Questions (...continued) How do I send or receive a file via iChat when the Mac OSX firewall is active? -for the sender. Step 5 Choose AOL IM from the online Macintosh AppleCare knowledge base: "iChat cannot send or receive a file when ...