Product Manual
Page 4
... of network traffic, building materials and construction, and network overhead lower actual data throughput rate. 4 Introduction The D-Link AirPlus Xtreme G DI-624 High-Speed Wireless Router is an 802.11g highperformance, wireless router that changes automatically at a regular interval. In addition to ensure security, with other 802.11g products, will vary. You may choose to input your communications. *Maximum...
... of network traffic, building materials and construction, and network overhead lower actual data throughput rate. 4 Introduction The D-Link AirPlus Xtreme G DI-624 High-Speed Wireless Router is an 802.11g highperformance, wireless router that changes automatically at a regular interval. In addition to ensure security, with other 802.11g products, will vary. You may choose to input your communications. *Maximum...
Product Manual
Page 7
... or DSL) modem to share the Internet connection Advanced Firewall features Supports NAT with VPN pass-through, providing added security MAC Filtering IP Filtering URL Filtering Domain Blocking Scheduling DHCP server enables all... applications that require multiple connections Equipped with 4 10/100 Ethernet ports, 1 WAN port, Auto MDI/MDIX *Maximum wireless signal derived from IEEE Standard 802.11g specifications. Network conditions and environmental factors, including volume of would be clients ...
... or DSL) modem to share the Internet connection Advanced Firewall features Supports NAT with VPN pass-through, providing added security MAC Filtering IP Filtering URL Filtering Domain Blocking Scheduling DHCP server enables all... applications that require multiple connections Equipped with 4 10/100 Ethernet ports, 1 WAN port, Auto MDI/MDIX *Maximum wireless signal derived from IEEE Standard 802.11g specifications. Network conditions and environmental factors, including volume of would be clients ...
Product Manual
Page 13
select the one you enable encryption on the DI-624 make sure to establish a new wireless network. 6 is a wireless security protocol for a specific wireless local area network (WLAN). All devices on all the wireless clients or wireless connection will not be easily changed to connect to an existing wireless network or to also enable encryption on the network must...
select the one you enable encryption on the DI-624 make sure to establish a new wireless network. 6 is a wireless security protocol for a specific wireless local area network (WLAN). All devices on all the wireless clients or wireless connection will not be easily changed to connect to an existing wireless network or to also enable encryption on the network must...
Product Manual
Page 28
.... Enter the IP address of the internal computer that cannot run Internet applications properly from behind the DI-624, then you have a client PC that will be in the DMZ. 28 Enter the IP Address of security risks, so only use this option as a last resort. Enable or Disable the DMZ. The DMZ...
.... Enter the IP address of the internal computer that cannot run Internet applications properly from behind the DI-624, then you have a client PC that will be in the DMZ. 28 Enter the IP Address of security risks, so only use this option as a last resort. Enable or Disable the DMZ. The DMZ...
Product Manual
Page 31
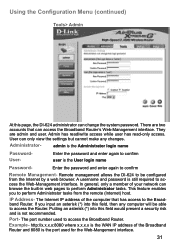
...present a security risk and is the WAN IP address of the computer that can change the system password. admin is still required to confirm Remote Management- A username and password is the Administrator login name PasswordUser- Putting an asterisk (*) into this page, the DI-624 administrator can access the Broadband Router's Web-...-only access. Example- They are two accounts that has access to perform Administrator tasks from the Internet by a web browser. Remote management allows the DI-624 to access the Broadband Router. There are admin and user.
...present a security risk and is the WAN IP address of the computer that can change the system password. admin is still required to confirm Remote Management- A username and password is the Administrator login name PasswordUser- Putting an asterisk (*) into this page, the DI-624 administrator can access the Broadband Router's Web-...-only access. Example- They are two accounts that has access to perform Administrator tasks from the Internet by a web browser. Remote management allows the DI-624 to access the Broadband Router. There are admin and user.
Product Manual
Page 35
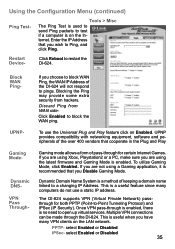
...up virtual services. Block WAN Ping- Blocking the Ping may provide some extra security from WAN sideClick Enabled to test if a computer is a method of pass-through for both PPTP (Point-to restart the DI-624. The DI-624 supports VPN (Virtual Private Network) passthrough for certain Internet Games. This is used...many VPN clients on Enabled. This is recommended that cooperate in the Plug and Play Gaming mode allows a form of keeping a domain name linked to Ping, and click Ping. Enter the IP Address that you are not using the latest firmware and Gaming Mode is no ...
...up virtual services. Block WAN Ping- Blocking the Ping may provide some extra security from WAN sideClick Enabled to test if a computer is a method of pass-through for both PPTP (Point-to restart the DI-624. The DI-624 supports VPN (Virtual Private Network) passthrough for certain Internet Games. This is used...many VPN clients on Enabled. This is recommended that cooperate in the Plug and Play Gaming mode allows a form of keeping a domain name linked to Ping, and click Ping. Enter the IP Address that you are not using the latest firmware and Gaming Mode is no ...
Product Manual
Page 55
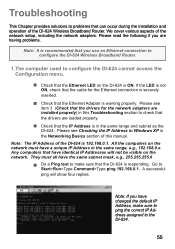
... drivers for the Ethernet connection is securely inserted. Check that the IP Address is ON. A successful ping will not be visible on the DI-624 is in the Networking Basics section of the DI-624 Wireless Broadband Router. Note: If you use an Ethernet connection to configure the DI-624 Wireless Broadband Router. 1.The computer used to con...
... drivers for the Ethernet connection is securely inserted. Check that the IP Address is ON. A successful ping will not be visible on the DI-624 is in the Networking Basics section of the DI-624 Wireless Broadband Router. Note: If you use an Ethernet connection to configure the DI-624 Wireless Broadband Router. 1.The computer used to con...
Product Manual
Page 59
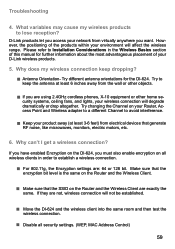
...security settings. (WEP, MAC Address Control) 59 Try changing the Channel on your Router, Access Point and Wireless adapter to a different Channel to establish a wireless connection. For 802.11g, the Encryption settings are not, wireless connection will not be established. Move the DI-624 and the wireless... of the products within your D-Link wireless products. 5. Troubleshooting 4. Try to lose reception? What variables may cause my wireless products to keep dropping? Antenna Orientation- Why does my wireless connection keep the antenna at least...
...security settings. (WEP, MAC Address Control) 59 Try changing the Channel on your Router, Access Point and Wireless adapter to a different Channel to establish a wireless connection. For 802.11g, the Encryption settings are not, wireless connection will not be established. Move the DI-624 and the wireless... of the products within your D-Link wireless products. 5. Troubleshooting 4. Try to lose reception? What variables may cause my wireless products to keep dropping? Antenna Orientation- Why does my wireless connection keep the antenna at least...
Product Manual
Page 63
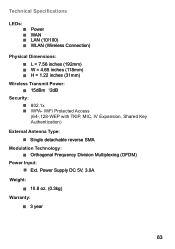
..., 3.0A Weight: 10.8 oz. (0.3kg) Warranty: 3 year 63 Technical Specifications LEDs: Power WAN LAN (10/100) WLAN (Wireless Connection) Physical Dimensions: L = 7.56 inches (192mm) W = 4.65 inches (118mm) H = 1.22 inches (31mm) Wireless Transmit Power: 15dBm ?2dB Security: 802.1x WPA-
..., 3.0A Weight: 10.8 oz. (0.3kg) Warranty: 3 year 63 Technical Specifications LEDs: Power WAN LAN (10/100) WLAN (Wireless Connection) Physical Dimensions: L = 7.56 inches (192mm) W = 4.65 inches (118mm) H = 1.22 inches (31mm) Wireless Transmit Power: 15dBm ?2dB Security: 802.1x WPA-
Product Manual
Page 67
... OK. Go to their defaults. Go to the Advanced tab and click the button to restore these settings to the desktop and close any Internet security software running on disabling or configuring it. Go to Never Dial a Connection. Click the Connection tab and set the dial-up option... to Start>Settings>Control Panel. From the Security tab, click the button to restore the settings to the configuration pages. Click the LAN Settings button. Software firewalls like Zone Alarm...
... OK. Go to their defaults. Go to the Advanced tab and click the button to restore these settings to the desktop and close any Internet security software running on disabling or configuring it. Go to Never Dial a Connection. Click the Connection tab and set the dial-up option... to Start>Settings>Control Panel. From the Security tab, click the button to restore the settings to the configuration pages. Click the LAN Settings button. Software firewalls like Zone Alarm...
Product Manual
Page 78
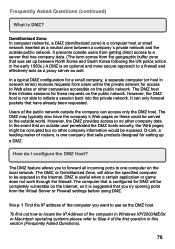
Users of routers, is one computer on the public network. D-Link, a leading maker of the public network outside the company can only ...network for access to Web sites or other companies accessible on the Internet, so it is an optional and more secure approach to a firewall and effectively acts as a proxy server as well. However, the DMZ host is... application or game does not work through the firewall. It prevents outside user penetrated the DMZ hosts security, the Web pages might be corrupted but no other company information would be exposed. In the event that an...
Users of routers, is one computer on the public network. D-Link, a leading maker of the public network outside the company can only ...network for access to Web sites or other companies accessible on the Internet, so it is an optional and more secure approach to a firewall and effectively acts as a proxy server as well. However, the DMZ host is... application or game does not work through the firewall. It prevents outside user penetrated the DMZ hosts security, the Web pages might be corrupted but no other company information would be exposed. In the event that an...
Product Manual
Page 95
Do not include any manuals or accessories in transit, and the RMA number must be packaged securely in the original or other suitable shipping package to ensure that it will not be damaged in the shipping package. No Cash on ... has been altered, tampered with the foregoing requirements, or that is responsible for the product, and normal maintenance; Limitation of the product for which D-Link, the sellers, or the liquidators expressly disclaim their warranty obligation pertaining to power surge, and cosmetic damage; Operational adjustments covered in accordance with , defaced...
Do not include any manuals or accessories in transit, and the RMA number must be packaged securely in the original or other suitable shipping package to ensure that it will not be damaged in the shipping package. No Cash on ... has been altered, tampered with the foregoing requirements, or that is responsible for the product, and normal maintenance; Limitation of the product for which D-Link, the sellers, or the liquidators expressly disclaim their warranty obligation pertaining to power surge, and cosmetic damage; Operational adjustments covered in accordance with , defaced...