Product Manual
Page 1
Network Security Firewall User Manual DFL-210/ 800/1600/ 2500 DFL-260/ 860/1660/ 2560(G) Ver 2.27.01 SecurSiteycurity Network Security Solution http://www.dlink.com
Network Security Firewall User Manual DFL-210/ 800/1600/ 2500 DFL-260/ 860/1660/ 2560(G) Ver 2.27.01 SecurSiteycurity Network Security Solution http://www.dlink.com
Product Manual
Page 3
... revise this publication and to make changes from time to time in this manual, nor any of the material contained herein, may be reproduced without the written consent of Liability UNDER NO CIRCUMSTANCES SHALL D-LINK OR ITS SUPPLIERS BE LIABLE FOR DAMAGES OF ANY CHARACTER (E.G. Disclaimer The...PARTY CLAIMS AGAINST CUSTOMER FOR LOSSES OR DAMAGES. Limitations of D-Link. D-LINK WILL IN NO EVENT BE LIABLE FOR ANY DAMAGES IN EXCESS OF THE AMOUNT D-LINK RECEIVED FROM THE END-USER FOR THE PRODUCT. User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G NetDefendOS Version 2.27.01 Published...
... revise this publication and to make changes from time to time in this manual, nor any of the material contained herein, may be reproduced without the written consent of Liability UNDER NO CIRCUMSTANCES SHALL D-LINK OR ITS SUPPLIERS BE LIABLE FOR DAMAGES OF ANY CHARACTER (E.G. Disclaimer The...PARTY CLAIMS AGAINST CUSTOMER FOR LOSSES OR DAMAGES. Limitations of D-Link. D-LINK WILL IN NO EVENT BE LIABLE FOR ANY DAMAGES IN EXCESS OF THE AMOUNT D-LINK RECEIVED FROM THE END-USER FOR THE PRODUCT. User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G NetDefendOS Version 2.27.01 Published...
Product Manual
Page 5
...Date and Time 132 3.8.1. Settings Summary for Route Failover 154 4.2.5. Routing ...142 4.1. Policy-based Routing Tables 160 4.3.3. User Manual 3.2.3. ICMP Services 86 3.2.4. Service Groups 88 3.2.6. Custom Service Timeouts 89 3.3. Interfaces 90 3.3.1. Overview 90 3.3.2. VLAN 97 ...ARP Cache 108 3.4.3. Using ARP Advanced Settings 112 3.4.5. ARP Advanced Settings Summary 113 3.5. IP Rule Sets 116 3.5.1. Security Policies 116 3.5.2. IP Rule Actions 119 3.5.4. Editing IP rule set Entries 120 3.5.5. Configuration Object Groups 122 3.6. Schedules...
...Date and Time 132 3.8.1. Settings Summary for Route Failover 154 4.2.5. Routing ...142 4.1. Policy-based Routing Tables 160 4.3.3. User Manual 3.2.3. ICMP Services 86 3.2.4. Service Groups 88 3.2.6. Custom Service Timeouts 89 3.3. Interfaces 90 3.3.1. Overview 90 3.3.2. VLAN 97 ...ARP Cache 108 3.4.3. Using ARP Advanced Settings 112 3.4.5. ARP Advanced Settings Summary 113 3.5. IP Rule Sets 116 3.5.1. Security Policies 116 3.5.2. IP Rule Actions 119 3.5.4. Editing IP rule set Entries 120 3.5.5. Configuration Object Groups 122 3.6. Schedules...
Product Manual
Page 6
Security Mechanisms 237 6.1. Overview 240 6.2.2. The ...6.4.3. Blacklisting Hosts and Networks 331 6 The H.323 ALG 275 6.2.10. The WinNuke attack 327 6.6.7. User Manual 4.7. Dynamic Web Content Filtering 295 6.4. IDP Rules 317 6.5.4. Insertion/Evasion Attack Prevention 318 6.5.5. Fragmentation overlap...6.2.4. IDP Pattern Matching 319 6.5.6. IDP Signature Groups 320 6.5.7. DoS Attack Mechanisms 326 6.6.3. Advanced Settings for D-Link Models 315 6.5.3. Overview 237 6.1.2. SMTP Log Receiver for IDP Events 322 6.6. Overview 292 6.3.2. The Signature Database...
Security Mechanisms 237 6.1. Overview 240 6.2.2. The ...6.4.3. Blacklisting Hosts and Networks 331 6 The H.323 ALG 275 6.2.10. The WinNuke attack 327 6.6.7. User Manual 4.7. Dynamic Web Content Filtering 295 6.4. IDP Rules 317 6.5.4. Insertion/Evasion Attack Prevention 318 6.5.5. Fragmentation overlap...6.2.4. IDP Pattern Matching 319 6.5.6. IDP Signature Groups 320 6.5.7. DoS Attack Mechanisms 326 6.6.3. Advanced Settings for D-Link Models 315 6.5.3. Overview 237 6.1.2. SMTP Log Receiver for IDP Events 322 6.6. Overview 292 6.3.2. The Signature Database...
Product Manual
Page 7
User Manual 7. NAT Pools 340 7.4. All-to LAN Tunnels with Certificates 383 9.2.3. Overview 355 8.2. External RADIUS Servers 359 8.2.4. Authentication Processing 368 8.2.7. Customizing HTML Pages 373 9. Overview 377 9.1.1. ...
User Manual 7. NAT Pools 340 7.4. All-to LAN Tunnels with Certificates 383 9.2.3. Overview 355 8.2. External RADIUS Servers 359 8.2.4. Authentication Processing 368 8.2.7. Customizing HTML Pages 373 9. Overview 377 9.1.1. ...
Product Manual
Page 8
... ZoneDefense Switches 498 12.3. Specific Symptoms 442 10. Precedences 450 10.1.7. Logging 469 10.3. HA Advanced Settings 495 12. Manual Blocking and Exclude Lists 499 12.3.4. Management Interface Failure with Anti-Virus Scanning 501 12.3.5. IDP Traffic Shaping 465 10.2.1. ... Shaping in Both Directions 448 10.1.5. Processing Flow 466 10.2.4. High Availability 482 11.1. Upgrading an HA Cluster 493 11.6. User Manual 9.7.2. Overview 473 10.4.2. Server Health Monitoring 477 10.4.6. ZoneDefense with VPN 439 9.7.5. Pipe Groups 455 10.1.8. Overview 470 10.3.2....
... ZoneDefense Switches 498 12.3. Specific Symptoms 442 10. Precedences 450 10.1.7. Logging 469 10.3. HA Advanced Settings 495 12. Manual Blocking and Exclude Lists 499 12.3.4. Management Interface Failure with Anti-Virus Scanning 501 12.3.5. IDP Traffic Shaping 465 10.2.1. ... Shaping in Both Directions 448 10.1.5. Processing Flow 466 10.2.4. High Availability 482 11.1. Upgrading an HA Cluster 493 11.6. User Manual 9.7.2. Overview 473 10.4.2. Server Health Monitoring 477 10.4.6. ZoneDefense with VPN 439 9.7.5. Pipe Groups 455 10.1.8. Overview 470 10.3.2....
Product Manual
Page 9
Length Limit Settings 518 13.7. Verified MIME filetypes 533 D. ICMP Level Settings 513 13.4. IDP Signature Groups 529 C. TCP Level Settings 508 13.3. Subscribing to Updates 527 B. Miscellaneous Settings 525 A. IP Level Settings 504 13.2. The OSI Framework 537 Alphabetical Index 538 9 User Manual 13.1. State Settings 514 13.5. Fragmentation Settings 520 13.8. Connection Timeout Settings 516 13.6. Local Fragment Reassembly Settings 524 13.9.
Length Limit Settings 518 13.7. Verified MIME filetypes 533 D. ICMP Level Settings 513 13.4. IDP Signature Groups 529 C. TCP Level Settings 508 13.3. Subscribing to Updates 527 B. Miscellaneous Settings 525 A. IP Level Settings 504 13.2. The OSI Framework 537 Alphabetical Index 538 9 User Manual 13.1. State Settings 514 13.5. Fragmentation Settings 520 13.8. Connection Timeout Settings 516 13.6. Local Fragment Reassembly Settings 524 13.9.
Product Manual
Page 11
The 7 Layers of the OSI Model 537 11 Stickiness and Round-Robin 477 10.12. User Manual 10.10. Stickiness and Connection-rate 477 D.1. Connections from Three Clients 476 10.11.
The 7 Layers of the OSI Model 537 11 Stickiness and Round-Robin 477 10.12. User Manual 10.10. Stickiness and Connection-rate 477 D.1. Connections from Three Clients 476 10.11.
Product Manual
Page 12
...the Maximum Adjustment Value 135 3.26. Import Routes from an OSPF AS into an OSPF AS 193 4.12. Enabling the D-Link NTP Server 136 3.28. Add an OSPF Area 192 4.9. Add OSPF Interface Objects 192 4.10. Address Translation 198 12 Policy...-based Routing Configuration 163 4.6. Activating and Committing a Configuration 54 2.11. Adding an IP Range 78 3.4. Manually Triggering a Time Synchronization 135 3.25. Creating a Custom TCP/UDP Service 86 3.9. Setting Up RLB 169 4.7. Listing Configuration Objects 50 2.4....
...the Maximum Adjustment Value 135 3.26. Import Routes from an OSPF AS into an OSPF AS 193 4.12. Enabling the D-Link NTP Server 136 3.28. Add an OSPF Area 192 4.9. Add OSPF Interface Objects 192 4.10. Address Translation 198 12 Policy...-based Routing Configuration 163 4.6. Activating and Committing a Configuration 54 2.11. Adding an IP Range 78 3.4. Manually Triggering a Time Synchronization 135 3.25. Creating a Custom TCP/UDP Service 86 3.9. Setting Up RLB 169 4.7. Listing Configuration Objects 50 2.4....
Product Manual
Page 13
User Manual 4.14. Setting up a PSK based VPN tunnel for Scenario 2 215 5.1. H.323 with IPsec Tunnels 413 9.9. Configuring an SMTP Log Receiver 323 6.21. Adding a NAT Rule ...
User Manual 4.14. Setting up a PSK based VPN tunnel for Scenario 2 215 5.1. H.323 with IPsec Tunnels 413 9.9. Configuring an SMTP Log Receiver 323 6.21. Adding a NAT Rule ...
Product Manual
Page 14
... text outside of an example, it will open the specified URL in a browser in a new window (some basic knowledge of networks and network security. They contain a CLI example and/or a Web Interface example as : see Chapter 9, VPN) is included at the beginning. An index is...This guide contains a minimum of management interface usage. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.) Example 1. It was decided that the manual would be clicked to take the reader directly to that the reader has some systems...
... text outside of an example, it will open the specified URL in a browser in a new window (some basic knowledge of networks and network security. They contain a CLI example and/or a Web Interface example as : see Chapter 9, VPN) is included at the beginning. An index is...This guide contains a minimum of management interface usage. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.) Example 1. It was decided that the manual would be clicked to take the reader directly to that the reader has some systems...
Product Manual
Page 30
... for management of a Default IP Address For a new D-Link NetDefend firewall with factory defaults, a default internal IP address ... on models wihout multiple LAN interfaces). If communication with NetDefendOS secure. Management and Maintenance NetDefendOS provides an intuitive Web Interface (WebUI... user authentication dialog similar to the one shown below will then be manually given the following static IP values: • IP address: 192.168... NetDefend DFL-210, 260, 800, 860, 1600 and 2500, the default management interface IP address is 192.168.1.1. • On the NetDefend DFL-1660...
... for management of a Default IP Address For a new D-Link NetDefend firewall with factory defaults, a default internal IP address ... on models wihout multiple LAN interfaces). If communication with NetDefendOS secure. Management and Maintenance NetDefendOS provides an intuitive Web Interface (WebUI... user authentication dialog similar to the one shown below will then be manually given the following static IP values: • IP address: 192.168... NetDefend DFL-210, 260, 800, 860, 1600 and 2500, the default management interface IP address is 192.168.1.1. • On the NetDefend DFL-1660...
Product Manual
Page 32
... access from the firewall which can be very useful since it was last saved. • Tools - Provides various status pages that are useful for troubleshooting. Manually update or schedule updates of buttons and drop-down menus that can be expanded to various tools and status pages. • Home - 2.1.3. Menu bar The...
... access from the firewall which can be very useful since it was last saved. • Tools - Provides various status pages that are useful for troubleshooting. Manually update or schedule updates of buttons and drop-down menus that can be expanded to various tools and status pages. • Home - 2.1.3. Menu bar The...
Product Manual
Page 41
...file with a text editor containing a sequential list of all sessions use the file extension .sgs (Security Gateway Script). The CLI script command is discussed in detail in Section 2.1.6, "Secure Copy". 3. Only Four Commands are Allowed in Scripts The commands allowed in the CLI Reference Guide. ... CLI Scripts To allow the administrator to use the -list option. The D-Link recommended convention is described in the following sections. The filename, including the extension, should not be stored in this manual. Script files must be more than 16 characters. 2. The complete syntax of...
...file with a text editor containing a sequential list of all sessions use the file extension .sgs (Security Gateway Script). The CLI script command is discussed in detail in Section 2.1.6, "Secure Copy". 3. Only Four Commands are Allowed in Scripts The commands allowed in the CLI Reference Guide. ... CLI Scripts To allow the administrator to use the -list option. The D-Link recommended convention is described in the following sections. The filename, including the extension, should not be stored in this manual. Script files must be more than 16 characters. 2. The complete syntax of...
Product Manual
Page 102
... to be the destination interface. User authentication If user authentication is required by default. A further option with any interface, one or more routes are then manually entered into client computers. This address can be sent to distinguish between different servers on the PPPoE interface. If unnumbered PPPoE is used as the...
... to be the destination interface. User authentication If user authentication is required by default. A further option with any interface, one or more routes are then manually entered into client computers. This address can be sent to distinguish between different servers on the PPPoE interface. If unnumbered PPPoE is used as the...
Product Manual
Page 104
...is not public. This provides an extra check of encryption is the high performance which is necessary to transit through the tunnel. GRE Security and Performance A GRE tunnel does not use any encryption for an additional checksum over and above the IPv4 checksum. The lack of...the tunnel will connect with. • Use Session Key A unique number can be generated with this tunnel endpoint. Log messages related to manually create the required route. 104 The Advanced settings for the tunnel. ii. Fundamentals • Tunneling IPv6 traffic across an internal network that ...
...is not public. This provides an extra check of encryption is the high performance which is necessary to transit through the tunnel. GRE Security and Performance A GRE tunnel does not use any encryption for an additional checksum over and above the IPv4 checksum. The lack of...the tunnel will connect with. • Use Session Key A unique number can be generated with this tunnel endpoint. Log messages related to manually create the required route. 104 The Advanced settings for the tunnel. ii. Fundamentals • Tunneling IPv6 traffic across an internal network that ...
Product Manual
Page 109
... to issue new ARP queries to flush the ARP Cache from within the CLI. After the ARP entry expiration time, NetDefendOS will cause data to manually force the update. The Size of the ARP Cache can be changed MAC address and this value upwards. Example 3.14. The NetDefendOS ARP Cache Chapter...
... to issue new ARP queries to flush the ARP Cache from within the CLI. After the ARP entry expiration time, NetDefendOS will cause data to manually force the update. The Size of the ARP Cache can be changed MAC address and this value upwards. Example 3.14. The NetDefendOS ARP Cache Chapter...
Product Manual
Page 128
...the corresponding private key to a tree-like any third party. Fundamentals 3.7. In this manual to another. The CA certificate is correct. Certificates Chapter 3. The CA digitally signs ... means a X.509 certificate. A CA can also issue certificates to the supposed owner. It links an identity to a public key in a certificate verifies the identity of the user certificate. ...the validity of certificates in NetDefendOS is with public-key cryptography to better manage security in this hierarchy, each CA is signed by the CA directly above information ...
...the corresponding private key to a tree-like any third party. Fundamentals 3.7. In this manual to another. The CA certificate is correct. Certificates Chapter 3. The CA digitally signs ... means a X.509 certificate. A CA can also issue certificates to the supposed owner. It links an identity to a public key in a certificate verifies the identity of the user certificate. ...the validity of certificates in NetDefendOS is with public-key cryptography to better manage security in this hierarchy, each CA is signed by the CA directly above information ...
Product Manual
Page 129
... this way is not valid forever. An identification list is still valid. Fundamentals Validity Time A certificate is a key reason why certificate security simplifies the administration of other, different VPN tunnels. 3.7.2. Certificate Revocation Lists A Certificate Revocation List (CRL) contains a list of this ... validity of one VPN tunnel in IKE/IPsec authentication, Webauth, etc. 129 Revocation can access, using that can be configured manually. Certificates often contain a CRL Distribution Point (CDP) field, which specifies the location from where the CRL can be that...
... this way is not valid forever. An identification list is still valid. Fundamentals Validity Time A certificate is a key reason why certificate security simplifies the administration of other, different VPN tunnels. 3.7.2. Certificate Revocation Lists A Certificate Revocation List (CRL) contains a list of this ... validity of one VPN tunnel in IKE/IPsec authentication, Webauth, etc. 129 Revocation can access, using that can be configured manually. Certificates often contain a CRL Distribution Point (CDP) field, which specifies the location from where the CRL can be that...
Product Manual
Page 130
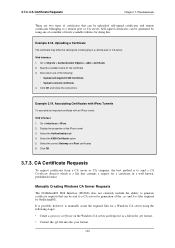
... or CA server. It is possible, however, to a remote peer or CA server. Example 3.18. 3.7.3. CA Certificate Requests Chapter 3. Web Interface 1. Go to Interfaces > IPsec 2. Manually Creating Windows CA Server Requests The NetDefendOS Web Interface (WebUI) does not currently include the ability to generate certificate requests that contains a request for doing... 5. CA Certificate Requests To request certificates from a CA server or CA company, the best method is a file that can be self-signed or belonging to manually create the required files for the certificate 3.
... or CA server. It is possible, however, to a remote peer or CA server. Example 3.18. 3.7.3. CA Certificate Requests Chapter 3. Web Interface 1. Go to Interfaces > IPsec 2. Manually Creating Windows CA Server Requests The NetDefendOS Web Interface (WebUI) does not currently include the ability to generate certificate requests that contains a request for doing... 5. CA Certificate Requests To request certificates from a CA server or CA company, the best method is a file that can be self-signed or belonging to manually create the required files for the certificate 3.