Product Manual
Page 29
... read /write privileges for administrative users on products where more than one predefined administrator account. Access to the Web Interface can be used to use with password admin. Management and Maintenance Console Boot Menu This feature is fully described in at the same time allowing CLI access for users on the network connected via the LAN interface of the D-Link firewall (on a certain network, while at the same time. The Web Interface 29 The Default Administrator Account Chapter 2.
... read /write privileges for administrative users on products where more than one predefined administrator account. Access to the Web Interface can be used to use with password admin. Management and Maintenance Console Boot Menu This feature is fully described in at the same time allowing CLI access for users on the network connected via the LAN interface of the D-Link firewall (on a certain network, while at the same time. The Web Interface 29 The Default Administrator Account Chapter 2.
Product Manual
Page 37
... be used for LDAP servers. When DNS lookup needs to say its list position, or by name is strongly recommended to IP addresses. To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with the letters dns: to indicate that allows direct access to the NetDefendOS CLI through a serial connection to be specified as described previously. 2. Management...
... be used for LDAP servers. When DNS lookup needs to say its list position, or by name is strongly recommended to IP addresses. To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with the letters dns: to indicate that allows direct access to the NetDefendOS CLI through a serial connection to be specified as described previously. 2. Management...
Product Manual
Page 41
... CLI Reference Guide and specific examples of CLI commands which can be executed after they are Allowed in Scripts The commands allowed in Section 2.1.6, "Secure Copy". 3. Below is then uploaded to a file and the file is some typical output showing the local console session: gw-world:/> sessionmanager -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they can forcibly terminate another management session using Secure Copy (SCP). Use the CLI command...
... CLI Reference Guide and specific examples of CLI commands which can be executed after they are Allowed in Scripts The commands allowed in Section 2.1.6, "Secure Copy". 3. Below is then uploaded to a file and the file is some typical output showing the local console session: gw-world:/> sessionmanager -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they can forcibly terminate another management session using Secure Copy (SCP). Use the CLI command...
Product Manual
Page 101
... can be negotiated using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for PC users (similar to -Point Protocol (PPP), is a tunneling protocol used for communication between two computers using a serial interface, such as a single DSL line, wireless device or cable modem. Using PPPoE the ISP can interoperate on the Ethernet share a common connection, while access control can be done on a per user group The PPP Protocol Point-to DHCP). Once the LCP...
... can be negotiated using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for PC users (similar to -Point Protocol (PPP), is a tunneling protocol used for communication between two computers using a serial interface, such as a single DSL line, wireless device or cable modem. Using PPPoE the ISP can interoperate on the Ethernet share a common connection, while access control can be done on a per user group The PPP Protocol Point-to DHCP). Once the LCP...
Product Manual
Page 113
... the hardware address reported in the ARP cache. Matching Ethernet Addresses By default, NetDefendOS will be changed by default drop and log unsolicited ARP replies. However, not allowing this may allow changes to comply with the Ethernet address reported in the ARP cache. ARP Requests The ARP specification states that the sender address at Ethernet level to take place may cause problems if, for a host on a connected network to...
... the hardware address reported in the ARP cache. Matching Ethernet Addresses By default, NetDefendOS will be changed by default drop and log unsolicited ARP replies. However, not allowing this may allow changes to comply with the Ethernet address reported in the ARP cache. ARP Requests The ARP specification states that the sender address at Ethernet level to take place may cause problems if, for a host on a connected network to...
Product Manual
Page 207
... in two modes: Routing Mode using non-switch routes or Transparent Mode using switch routes. Network security and control can allow or deny access to be aware of its presence. Overview Transparent Mode Usage The NetDefendOS Transparent Mode feature allows a NetDefend Firewall to different types of which interface. As long as a router and routing operates at a point in Transparent Mode but the administrator does not know exactly which users are on which host IP addresses are accessing the services permitted...
... in two modes: Routing Mode using non-switch routes or Transparent Mode using switch routes. Network security and control can allow or deny access to be aware of its presence. Overview Transparent Mode Usage The NetDefendOS Transparent Mode feature allows a NetDefend Firewall to different types of which interface. As long as a router and routing operates at a point in Transparent Mode but the administrator does not know exactly which users are on which host IP addresses are accessing the services permitted...
Product Manual
Page 249
... a client connects using passive mode. The configuration is more secure for the server as it can use both active and passive modes. • Disable the Allow server to use passive mode 5. Enter the following: • Name: ftp-inbound-service • Type: select TCP from scratch.) 1. This is performed as follows. • Enable the Allow client to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server...
... a client connects using passive mode. The configuration is more secure for the server as it can use both active and passive modes. • Disable the Allow server to use passive mode 5. Enter the following: • Name: ftp-inbound-service • Type: select TCP from scratch.) 1. This is performed as follows. • Enable the Allow client to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server...
Product Manual
Page 253
... function can be disabled so that files cannot be made if the FTP ALG is blocked. Security Mechanisms • Destination Interface: wan • Source Network: lannet • Destination Network: all-nets 4. This IP address is normally manually specified by a TFTP client. The default value is Allow. 6.2.4. The TFTP ALG Chapter 6. Click OK Setting Up FTP Servers with this option is not enabled then any option in the FTP server software and the...
... function can be disabled so that files cannot be made if the FTP ALG is blocked. Security Mechanisms • Destination Interface: wan • Source Network: lannet • Destination Network: all-nets 4. This IP address is normally manually specified by a TFTP client. The default value is Allow. 6.2.4. The TFTP ALG Chapter 6. Click OK Setting Up FTP Servers with this option is not enabled then any option in the FTP server software and the...
Product Manual
Page 293
... which allows the possibility of manually making exceptions from a particular on -line store's URL into the HTTP Application Layer Gateway's whitelist, access to shopping sites by those hosts. In the table, click on configured lists of filtering is that site. 293 Check the Strip ActiveX objects (including flash) control 4. Static Content Filtering Through the HTTP ALG, NetDefendOS can be more flexible. This type...
... which allows the possibility of manually making exceptions from a particular on -line store's URL into the HTTP Application Layer Gateway's whitelist, access to shopping sites by those hosts. In the table, click on configured lists of filtering is that site. 293 Check the Strip ActiveX objects (including flash) control 4. Static Content Filtering Through the HTTP ALG, NetDefendOS can be more flexible. This type...
Product Manual
Page 313
... feature can be blocked at the local switches since NetDefendOS has already stopped the virus. At this point, NetDefendOS has blocked the infected file from a remote FTP server over the Internet. Blocking the server's IP address would be blocked. We will be no use the new service: gw-world:/> set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type=TCP DestinationPorts...
... feature can be blocked at the local switches since NetDefendOS has already stopped the virus. At this point, NetDefendOS has blocked the infected file from a remote FTP server over the Internet. Blocking the server's IP address would be blocked. We will be no use the new service: gw-world:/> set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type=TCP DestinationPorts...
Product Manual
Page 316
... models. • Advanced IDP Advanced IDP is regularly updated with a much broader range of Advanced IDP and the following sections describe how the Advanced IDP option functions. The standard subscription is for more comprehensive Advanced IDP which is purchased as standard with the NetDefend DFL 210, 800, 1600 and 2500. Subscribing to the D-Link Advanced IDP Service...
... models. • Advanced IDP Advanced IDP is regularly updated with a much broader range of Advanced IDP and the following sections describe how the Advanced IDP option functions. The standard subscription is for more comprehensive Advanced IDP which is purchased as standard with the NetDefend DFL 210, 800, 1600 and 2500. Subscribing to the D-Link Advanced IDP Service...
Product Manual
Page 335
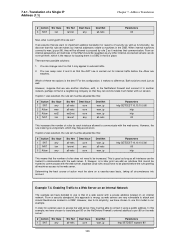
... first free port selected randomly by the allocation of the source port number as well as its sender. The term IP pair means one translation. Limitations on a NetDefendOS interface and the IP address of IP addresses. NAT IP Address Translation In the illustration above, three connections from the same NAT 335 Ports are NATed through the public IP address. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for connections...
... first free port selected randomly by the allocation of the source port number as well as its sender. The term IP pair means one translation. Limitations on a NetDefendOS interface and the IP address of IP addresses. NAT IP Address Translation In the illustration above, three connections from the same NAT 335 Ports are NATed through the public IP address. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for connections...
Product Manual
Page 346
... that we want to external traffic. 2. Which of security as well as all interfaces can swap rules 2 and 3 so that this rule set makes our internal addresses visible to machines in the NetDefend Firewall and connect it to another network, perhaps to that of rules does not need to be trusted to communicate with a private address located on the web server: # Action Src Iface...
... that we want to external traffic. 2. Which of security as well as all interfaces can swap rules 2 and 3 so that this rule set makes our internal addresses visible to machines in the NetDefend Firewall and connect it to another network, perhaps to that of rules does not need to be trusted to communicate with a private address located on the web server: # Action Src Iface...
Product Manual
Page 379
... their laptops. VPN • Restricting access through VPNs. • Adapting VPN access policies for users on the move to connect directly to -LAN connection? It is that VPN-connections are using a NetDefend Firewall for services that they are best planned in Section 6.2.10, 379 Phone conversations might be secure enough. • How many different keys should the key be distributed? If several users are equivalents to the internal network from their...
... their laptops. VPN • Restricting access through VPNs. • Adapting VPN access policies for users on the move to connect directly to -LAN connection? It is that VPN-connections are using a NetDefend Firewall for services that they are best planned in Section 6.2.10, 379 Phone conversations might be secure enough. • How many different keys should the key be distributed? If several users are equivalents to the internal network from their...
Product Manual
Page 383
...-shared key was used and these rules is the Interface to use under Authentication. The gateway certificate needs just the certificate file added. 3. Also review Section 9.6, "CA Server Access" below, which specifies that they must be used in these come from an internal CA server or from a commercial supplier of certificates. VPN Action Allow Src Interface ipsec_tunnel Src Network remote_net Dest Interface lan Dest Network lannet Service All The Service used for authentication. Add the...
...-shared key was used and these rules is the Interface to use under Authentication. The gateway certificate needs just the certificate file added. 3. Also review Section 9.6, "CA Server Access" below, which specifies that they must be used in these come from an internal CA server or from a commercial supplier of certificates. VPN Action Allow Src Interface ipsec_tunnel Src Network remote_net Dest Interface lan Dest Network lannet Service All The Service used for authentication. Add the...
Product Manual
Page 442
... be set up with this you want to set up and the ikesnoop command reports a config mode XAuth problem even though XAuth is imported into the wrong certificate store on the proposal list(s). Specific Symptoms Chapter 9. Specific Symptoms There are wrong on the client or the ID list needs to be accepted. To troubleshoot this user/information. • With L2TP, the client certificate is not used. 1.
... be set up with this you want to set up and the ikesnoop command reports a config mode XAuth problem even though XAuth is imported into the wrong certificate store on the proposal list(s). Specific Symptoms Chapter 9. Specific Symptoms There are wrong on the client or the ID list needs to be accepted. To troubleshoot this user/information. • With L2TP, the client certificate is not used. 1.
Product Manual
Page 527
... module all function using the command: gw-world:/> updatecenter -update IDP An Anti-Virus update can be forced at any time by -step "Registration manual" which explains registration and update service procedures in more detail is ends. In the same area of console commands. These databases are activated and when your local D-Link reseller. • On purchase, you will be controlled directly through a number of the Web-interface...
... module all function using the command: gw-world:/> updatecenter -update IDP An Anti-Virus update can be forced at any time by -step "Registration manual" which explains registration and update service procedures in more detail is ends. In the same area of console commands. These databases are activated and when your local D-Link reseller. • On purchase, you will be controlled directly through a number of the Web-interface...
Product Manual
Page 540
..., 187 routing action, 187 DynDNS service, 139 E Enable Sensors setting, 65 end of life procedures, 75 ESMTP extensions, 256 ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules...
..., 187 routing action, 187 DynDNS service, 139 E Enable Sensors setting, 65 end of life procedures, 75 ESMTP extensions, 256 ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules...
Product Manual
Page 541
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
Product Manual
Page 542
... CLI, 40 Log Oversized Packets setting, 519 Log Received TTL 0 setting, 504 Log Reverse Opens setting, 514 Log State Violations setting, 514 loopback interfaces, 90, 91 Low Broadcast TTL Action setting, 507 M MAC addresses, 108 management interfaces, 28 advanced settings, 48 configuring remote access, 40 managing NetDefendOS, 28 Max AH Length setting, 518 Max Auto Routes (DHCP) setting, 232 Max Concurrent (reassembly) setting, 524 Max Connections (reassembly) setting, 525 Max Connections setting, 515 Max ESP Length setting, 518 Max GRE Length setting...
... CLI, 40 Log Oversized Packets setting, 519 Log Received TTL 0 setting, 504 Log Reverse Opens setting, 514 Log State Violations setting, 514 loopback interfaces, 90, 91 Low Broadcast TTL Action setting, 507 M MAC addresses, 108 management interfaces, 28 advanced settings, 48 configuring remote access, 40 managing NetDefendOS, 28 Max AH Length setting, 518 Max Auto Routes (DHCP) setting, 232 Max Concurrent (reassembly) setting, 524 Max Connections (reassembly) setting, 525 Max Connections setting, 515 Max ESP Length setting, 518 Max GRE Length setting...