User Guide
Page 15
... ...213 15.3 VPN Certificates ...215 15.3.1 Import Certificate ...216 Chapter 16 VPN...217 16.1 Overview ...217 16.1.1 What You Can Do in the VPN Screens 217 16.1.2 What You Need to Know About IPSec VPN 218 16.1.3 Before You Begin 219 16.2 VPN Setup Screen ...220 16.3 The VPN Edit Screen ...222... 16.4 Configuring Advanced Settings 226 16.5 Viewing SA Monitor ...228 16.6 IPSec VPN Technical Reference 229 16.6.1...
... ...213 15.3 VPN Certificates ...215 15.3.1 Import Certificate ...216 Chapter 16 VPN...217 16.1 Overview ...217 16.1.1 What You Can Do in the VPN Screens 217 16.1.2 What You Need to Know About IPSec VPN 218 16.1.3 Before You Begin 219 16.2 VPN Setup Screen ...220 16.3 The VPN Edit Screen ...222... 16.4 Configuring Advanced Settings 226 16.5 Viewing SA Monitor ...228 16.6 IPSec VPN Technical Reference 229 16.6.1...
User Guide
Page 34
... page will show you the active tunnel's status System Monitor 34 P-661HNU-Fx User's Guide VPN Setup Use this screen to configure LAN TCP/IP settings, and other advanced properties. VPN Certificates Use this screen to make your ZyXEL Device. NAT Port Forwarding Use this screen to the outside world. Certificates Local Certificates Use...
... page will show you the active tunnel's status System Monitor 34 P-661HNU-Fx User's Guide VPN Setup Use this screen to configure LAN TCP/IP settings, and other advanced properties. VPN Certificates Use this screen to make your ZyXEL Device. NAT Port Forwarding Use this screen to the outside world. Certificates Local Certificates Use...
User Guide
Page 217
...integrity and authentication at the IP layer. Figure 94 VPN: Example VPN Tunnel X Y 16.1.1 What You Can Do in the VPN Screens • Use the Setup screen (Section 16.2 on page 220) to view the configured VPN policies and add, edit or remove a VPN policy. • Use the Monitor screen (Section 16....5 on page 228) to -site lines. A secure VPN is built around a number of ...
...integrity and authentication at the IP layer. Figure 94 VPN: Example VPN Tunnel X Y 16.1.1 What You Can Do in the VPN Screens • Use the Setup screen (Section 16.2 on page 220) to view the configured VPN policies and add, edit or remove a VPN policy. • Use the Monitor screen (Section 16....5 on page 228) to -site lines. A secure VPN is built around a number of ...
User Guide
Page 218
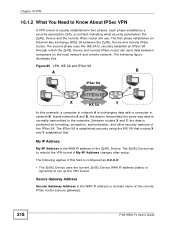
... the remote IPSec router (secure gateway). 218 P-661HNU-Fx User's Guide The second phase uses the IKE SA to rebuild the VPN tunnel if My IP Address changes after setup. Figure 95 VPN: IKE SA and IPSec SA A B IPSec SA X IKE SA Y In this example, a computer in network A is normally ...usually established in two phases. My IP Address My IP Address is protected by tunneling, encryption, authentication, and other security features of the ZyXEL Device. The first phase establishes an Internet Key Exchange (IKE) SA between computers on the local network and remote network. Chapter 16...
... the remote IPSec router (secure gateway). 218 P-661HNU-Fx User's Guide The second phase uses the IKE SA to rebuild the VPN tunnel if My IP Address changes after setup. Figure 95 VPN: IKE SA and IPSec SA A B IPSec SA X IKE SA Y In this example, a computer in network A is normally ...usually established in two phases. My IP Address My IP Address is protected by tunneling, encryption, authentication, and other security features of the ZyXEL Device. The first phase establishes an Internet Key Exchange (IKE) SA between computers on the local network and remote network. Chapter 16...
User Guide
Page 220
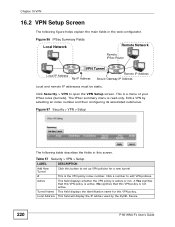
...Gateway IP Address Local and remote IP addresses must be static. The IPSec summary menu is active or not. Chapter 16 VPN 16.2 VPN Setup Screen The following table describes the fields in the web configurator. Tunnel Name This field displays the identification name for a ...selecting an index number and then configuring its associated submenus. This is active. Figure 97 Security > VPN > Setup The following figure helps explain the main fields in this VPN policy. Click Security > VPN to open the VPN Setup screen. Edit a VPN by the ZyXEL Device. 220 P-661HNU-Fx User's Guide
...Gateway IP Address Local and remote IP addresses must be static. The IPSec summary menu is active or not. Chapter 16 VPN 16.2 VPN Setup Screen The following table describes the fields in the web configurator. Tunnel Name This field displays the identification name for a ...selecting an index number and then configuring its associated submenus. This is active. Figure 97 Security > VPN > Setup The following figure helps explain the main fields in this VPN policy. Click Security > VPN to open the VPN Setup screen. Edit a VPN by the ZyXEL Device. 220 P-661HNU-Fx User's Guide
User Guide
Page 221
... the screen where you 're making the VPN connection IPSec Algorithm This field displays the encryption algorithm used for an SA. Click this to save your settings to the ZyXEL Device. Chapter 16 VPN Table 57 Security > VPN > Setup (continued) LABEL DESCRIPTION Remote Address This field... will display the Secure Gateway Address of the IPSec router with which you can edit the VPN configuration. Modify Click the Edit icon...
... the screen where you 're making the VPN connection IPSec Algorithm This field displays the encryption algorithm used for an SA. Click this to save your settings to the ZyXEL Device. Chapter 16 VPN Table 57 Security > VPN > Setup (continued) LABEL DESCRIPTION Remote Address This field... will display the Secure Gateway Address of the IPSec router with which you can edit the VPN configuration. Modify Click the Edit icon...
User Guide
Page 222
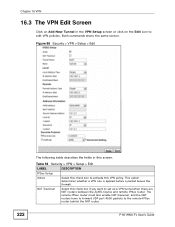
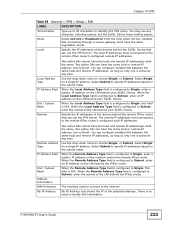
... 222 The following table describes the fields in the VPN Setup screen or click on the Edit icon to activate this screen. Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION IPSec Setup Active Select this check box to edit VPN policies. NAT Traversal Select this check box if you want to the remote ...Screen Click on Add New Tunnel in this VPN policy. The remote IPSec router must also enable NAT traversal, and the NAT routers have to forward UDP port 4500 packets to set up a VPN tunnel when there are NAT routers between the ZyXEL Device and remote IPSec router. Both commands ...
... 222 The following table describes the fields in the VPN Setup screen or click on the Edit icon to activate this screen. Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION IPSec Setup Active Select this check box to edit VPN policies. NAT Traversal Select this check box if you want to the remote ...Screen Click on Add New Tunnel in this VPN policy. The remote IPSec router must also enable NAT traversal, and the NAT routers have to forward UDP port 4500 packets to set up a VPN tunnel when there are NAT routers between the ZyXEL Device and remote IPSec router. Both commands ...
User Guide
Page 223
...to the remote IPSec router's configured remote IP addresses. You can use the VPN tunnel. The interface used to connect to the internet My IP Address only shows the IP of the LAN behind your ZyXEL Device. Local Address Type IP Address Start End / Subnet Mask Remote Two ... Address Type field is configured to Subnet, enter the subnet of the devices behind your ZyXEL Device. Select Subnet to specify IP addresses based on the subnet mask. Chapter 16 VPN Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION Tunnel Name Type up to 32 characters to identify this information....
...to the remote IPSec router's configured remote IP addresses. You can use the VPN tunnel. The interface used to connect to the internet My IP Address only shows the IP of the LAN behind your ZyXEL Device. Local Address Type IP Address Start End / Subnet Mask Remote Two ... Address Type field is configured to Subnet, enter the subnet of the devices behind your ZyXEL Device. Select Subnet to specify IP addresses based on the subnet mask. Chapter 16 VPN Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION Tunnel Name Type up to 32 characters to identify this information....
User Guide
Page 224
...in the local Content field or use 0.0.0.0. The domain name or e-mail address is a NAT router between VPN connection requests that you are truncated. Chapter 16 VPN Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION Secure Gateway Type the WAN IP address or the URL (up to 31 characters)... of the IPSec Address router with dynamic WAN IP addresses. The ZyXEL Device automatically uses the IP address in...
...in the local Content field or use 0.0.0.0. The domain name or e-mail address is a NAT router between VPN connection requests that you are truncated. Chapter 16 VPN Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION Secure Gateway Type the WAN IP address or the URL (up to 31 characters)... of the IPSec Address router with dynamic WAN IP addresses. The ZyXEL Device automatically uses the IP address in...
User Guide
Page 225
... IKE key management. Click Apply to the Secure Gateway Address field description). Chapter 16 VPN Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION Content The configuration of the peer content depends on both ends. If you want the ZyXEL Device to identify the remote IPSec router. Click Back to return to 31 ASCII characters...
... IKE key management. Click Apply to the Secure Gateway Address field description). Chapter 16 VPN Table 58 Security > VPN > Setup > Edit LABEL DESCRIPTION Content The configuration of the peer content depends on both ends. If you want the ZyXEL Device to identify the remote IPSec router. Click Back to return to 31 ASCII characters...
User Guide
Page 226
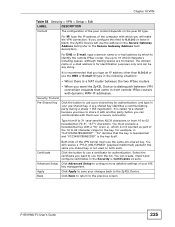
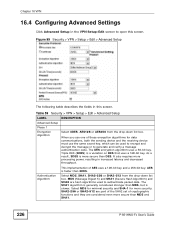
...implementation of these encryption algorithms for more processing power, resulting in increased latency and decreased throughput. Figure 99 Security > VPN > Setup > Edit > Advanced Setup The following table describes the fields in this screen. As a result, 3DES is slower. Select MD5, SHA1, ...and SHA1 (Secure Hash Algorithm) and SHA2 are considered even more secure than 3DES. Table 59 Security > VPN > Setup > Edit > Advanced Setup LABEL DESCRIPTION Advanced Setup Phase 1 Encryption Algorithm Select 3DES, AES128 or AES256 from the drop-down list box. SHA2-256 or SHA2...
...implementation of these encryption algorithms for more processing power, resulting in increased latency and decreased throughput. Figure 99 Security > VPN > Setup > Edit > Advanced Setup The following table describes the fields in this screen. As a result, 3DES is slower. Select MD5, SHA1, ...and SHA1 (Secure Hash Algorithm) and SHA2 are considered even more secure than 3DES. Table 59 Security > VPN > Setup > Edit > Advanced Setup LABEL DESCRIPTION Advanced Setup Phase 1 Encryption Algorithm Select 3DES, AES128 or AES256 from the drop-down list box. SHA2-256 or SHA2...
User Guide
Page 227
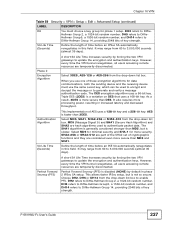
... and they are temporarily disconnected. However, every time the VPN tunnel renegotiates, all users accessing remote resources are considered even more security. This allows faster IPSec setup, but is disabled (NONE) by forcing the two VPN gateways to Diffie- DH2 refers to authenticate packet data....providing 2048 bits of key strength. It may range from the drop-down list box to enable PFS. Chapter 16 VPN Table 59 Security > VPN > Setup > Edit > Advanced Setup (continued) LABEL DESCRIPTION DH You must use one of these encryption algorithms for more secure than 3DES. As a ...
... and they are temporarily disconnected. However, every time the VPN tunnel renegotiates, all users accessing remote resources are considered even more security. This allows faster IPSec setup, but is disabled (NONE) by forcing the two VPN gateways to Diffie- DH2 refers to authenticate packet data....providing 2048 bits of key strength. It may range from the drop-down list box to enable PFS. Chapter 16 VPN Table 59 Security > VPN > Setup > Edit > Advanced Setup (continued) LABEL DESCRIPTION DH You must use one of these encryption algorithms for more secure than 3DES. As a ...
User Guide
Page 228
Chapter 16 VPN Table 59 Security > VPN > Setup > Edit > Advanced Setup (continued) LABEL DESCRIPTION DPD Active Select DPD (Dead Peer Protection) if you want the ZyXEL Device to make sure the remote IPSec router is outbound traffic but no inbound traffic, the SA times out automatically after...to return to the previous screen. 16.5 Viewing SA Monitor Click Security > VPN > Monitor to the VPN screen. Figure 100 Security > VPN > Monitor The following table describes the fields in this screen to have the ZyXEL Device renegotiate an IPSec SA when the SA lifetime expires, even if there ...
Chapter 16 VPN Table 59 Security > VPN > Setup > Edit > Advanced Setup (continued) LABEL DESCRIPTION DPD Active Select DPD (Dead Peer Protection) if you want the ZyXEL Device to make sure the remote IPSec router is outbound traffic but no inbound traffic, the SA times out automatically after...to return to the previous screen. 16.5 Viewing SA Monitor Click Security > VPN > Monitor to the VPN screen. Figure 100 Security > VPN > Monitor The following table describes the fields in this screen to have the ZyXEL Device renegotiate an IPSec SA when the SA lifetime expires, even if there ...
User Guide
Page 237
... IP addresses. DiffieHellman is used within IKE SA setup to a single ZyXEL Device at headquarters has a static public IP address. DH2) Diffie-Hellman groups are supported. It is called "pre-shared" because you can complete negotiation and establish a VPN tunnel. Chapter 16 VPN The two ZyXEL Devices in this example cannot complete their negotiation because...
... IP addresses. DiffieHellman is used within IKE SA setup to a single ZyXEL Device at headquarters has a static public IP address. DH2) Diffie-Hellman groups are supported. It is called "pre-shared" because you can complete negotiation and establish a VPN tunnel. Chapter 16 VPN The two ZyXEL Devices in this example cannot complete their negotiation because...
User Guide
Page 399
... 155, 191, 291 definitions 194 how it works 195 IPSec 230 traversal 231 what it does 195 negotiation mode 234 Network Address Translation, see also VPN ISP 88 ITU-T G.992.1 264 MAC filter 205 managing the device good habits 26 using FTP. Index Internet Assigned Numbers Authority, see IANA Internet Key... Provider, see ISP IP address 84, 155 default 29 ping 261 WAN 88 IP Address Assignment 108 IP multicasting 276 IP pool 146 IP pool setup 155 IPSec 217 algorithms 229 architecture 229 NAT 230 see NAT network map 33 O M MAC 83, 205 MAC address 147 filter 129 MAC address filtering...
... 155, 191, 291 definitions 194 how it works 195 IPSec 230 traversal 231 what it does 195 negotiation mode 234 Network Address Translation, see also VPN ISP 88 ITU-T G.992.1 264 MAC filter 205 managing the device good habits 26 using FTP. Index Internet Assigned Numbers Authority, see IANA Internet Key... Provider, see ISP IP address 84, 155 default 29 ping 261 WAN 88 IP Address Assignment 108 IP multicasting 276 IP pool 146 IP pool setup 155 IPSec 217 algorithms 229 architecture 229 NAT 230 see NAT network map 33 O M MAC 83, 205 MAC address 147 filter 129 MAC address filtering...