User Guide
Page 25
...adding one device at a time. See Chapter 5 on page 79. 1.5.1 Using the WPS/WLAN Button By default, the wireless network on the ZyXEL Device is a wireless Access Point (AP) for over Internet calls high priority, and/or limit bandwidth devoted to the boss's excessive file downloading. 1.5 Wireless... Access The ZyXEL Device is turned on inconvenient Ethernet cables. To turn it off, simply press the WPS/WLAN button on top of traffic ...
...adding one device at a time. See Chapter 5 on page 79. 1.5.1 Using the WPS/WLAN Button By default, the wireless network on the ZyXEL Device is a wireless Access Point (AP) for over Internet calls high priority, and/or limit bandwidth devoted to the boss's excessive file downloading. 1.5 Wireless... Access The ZyXEL Device is turned on inconvenient Ethernet cables. To turn it off, simply press the WPS/WLAN button on top of traffic ...
User Guide
Page 45
...WPA2-PSK DoNotStealMyWirelessNetwork 802.11b+g+n ADSL Router Series User's Guide 45 When prompted for a key, use his notebook to access the Internet. In the client, choose the AP with the SSID configured here. Chapter 4 Tutorials 4.4 Setting Up a...ZyXEL Device. The wireless client can access the Internet through the AP. Thomas has to configure the wireless network settings on page 50). 4.4.1 Configuring the Wireless Network Settings This example uses the following parameters to set up a wireless network. In this wireless network, the ZyXEL Device serves as an access point...
...WPA2-PSK DoNotStealMyWirelessNetwork 802.11b+g+n ADSL Router Series User's Guide 45 When prompted for a key, use his notebook to access the Internet. In the client, choose the AP with the SSID configured here. Chapter 4 Tutorials 4.4 Setting Up a...ZyXEL Device. The wireless client can access the Internet through the AP. Thomas has to configure the wireless network settings on page 50). 4.4.1 Configuring the Wireless Network Settings This example uses the following parameters to set up a wireless network. In this wireless network, the ZyXEL Device serves as an access point...
User Guide
Page 123
...configure your wireless network. • Setting up multiple wireless networks. • Using a MAC (Media Access Control) address filter to restrict access to the wireless network. • Performing other ZyXEL access points. • Use the Scheduling screen (see Section 8.6 on page 136) to configure the dates/...times to set up your ZyXEL Device. • Use the WPS screen (see Section 8.4 on page 133) to enable or disable WPS,...
...configure your wireless network. • Setting up multiple wireless networks. • Using a MAC (Media Access Control) address filter to restrict access to the wireless network. • Performing other ZyXEL access points. • Use the Scheduling screen (see Section 8.6 on page 136) to configure the dates/...times to set up your ZyXEL Device. • Use the WPS screen (see Section 8.4 on page 133) to enable or disable WPS,...
User Guide
Page 125
... to the wireless LAN and you change the wireless settings of your ZyXEL Device. Click Network > Wireless LAN to activate wireless LAN. Wireless devices associating to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you will lose your wireless connection... when you are allowed or denied to access the ZyXEL Device using a site survey tool. Select this check box...
... to the wireless LAN and you change the wireless settings of your ZyXEL Device. Click Network > Wireless LAN to activate wireless LAN. Wireless devices associating to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you will lose your wireless connection... when you are allowed or denied to access the ZyXEL Device using a site survey tool. Select this check box...
User Guide
Page 137
...of two ways. • An "infrastructure" type of wireless clients, access points and bridges. • A wireless client is a radio connected to a user's computer. • An access point is a radio that relays communications between access points and wireless clients, extending a network's range. Wireless clients connect to ... to exchange information. Chapter 8 Wireless LAN 8.8 Wireless LAN Technical Reference This section discusses wireless LANs in order to the access points. • An "ad-hoc" type of network is one or more information, see the appendix. 8.8.1 Wireless Network ...
...of two ways. • An "infrastructure" type of wireless clients, access points and bridges. • A wireless client is a radio connected to a user's computer. • An access point is a radio that relays communications between access points and wireless clients, extending a network's range. Wireless clients connect to ... to exchange information. Chapter 8 Wireless LAN 8.8 Wireless LAN Technical Reference This section discusses wireless LANs in order to the access points. • An "ad-hoc" type of network is one or more information, see the appendix. 8.8.1 Wireless Network ...
User Guide
Page 138
.... It stands for unlicensed, civilian use the same SSID. In this wireless network, devices A and B use the access point (AP) to use security compatible with the Internet. When you create a network, you must use . Your ZyXEL Device is the name of wireless networking, these basic guidelines. • Every device in the same wireless...
.... It stands for unlicensed, civilian use the same SSID. In this wireless network, devices A and B use the access point (AP) to use security compatible with the Internet. When you create a network, you must use . Your ZyXEL Device is the name of wireless networking, these basic guidelines. • Every device in the same wireless...
User Guide
Page 142
... to associate with each other . When Intra-BSS traffic blocking is enabled, wireless station A and B can access the wired network and communicate with each other. The ZyXEL Device's MBSSID (Multiple Basic Service Set IDentifier) function allows you need to use different BSSIDs to use different keys... well as the cost of buying extra APs, there is traffic between a wireless station and a wired network client go through one access point to provide several BSSs simultaneously. You can use different APs to different SSIDs. If two wireless devices have the same keys, they ...
... to associate with each other . When Intra-BSS traffic blocking is enabled, wireless station A and B can access the wired network and communicate with each other. The ZyXEL Device's MBSSID (Multiple Basic Service Set IDentifier) function allows you need to use different BSSIDs to use different keys... well as the cost of buying extra APs, there is traffic between a wireless station and a wired network client go through one access point to provide several BSSs simultaneously. You can use different APs to different SSIDs. If two wireless devices have the same keys, they ...
User Guide
Page 143
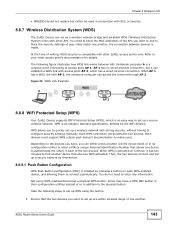
At the time of writing, WDS security is compatible with other access point's documentation for details. Figure 55 WDS Link Example WDS A AP 1 AP 2 8.8.8 WiFi Protected Setup (WPS) Your ZyXEL Device supports WiFi Protected Setup (WPS), which is activated on a device, it can either press... connection works between APs. You need to enter any information. Refer to your other ZyXEL access points only. AP 1 has no wired Internet connection, but rather be used in conjunction with access point AP 2, which has a wired Internet connection. Chapter 8 Wireless LAN • MBSSID...
At the time of writing, WDS security is compatible with other access point's documentation for details. Figure 55 WDS Link Example WDS A AP 1 AP 2 8.8.8 WiFi Protected Setup (WPS) Your ZyXEL Device supports WiFi Protected Setup (WPS), which is activated on a device, it can either press... connection works between APs. You need to enter any information. Refer to your other ZyXEL access points only. AP 1 has no wired Internet connection, but rather be used in conjunction with access point AP 2, which has a wired Internet connection. Chapter 8 Wireless LAN • MBSSID...
User Guide
Page 144
... the device, or in the WPS section of the AP's configuration interface. However, you need to make sure that the connection is established between an access point or wireless router (referred to the second device. it will be displayed either on each other. it cannot be static (it does not matter which... you see the device's User's Guide for how to do this. 3 Look for how to log into the configuration interfaces of each device. for the ZyXEL Device, see Section 8.5 on page 134). 3 Press the button on the other , allowing it to find the WPS PIN - If you can connect, WPS was...
... the device, or in the WPS section of the AP's configuration interface. However, you need to make sure that the connection is established between an access point or wireless router (referred to the second device. it will be displayed either on each other. it cannot be static (it does not matter which... you see the device's User's Guide for how to do this. 3 Look for how to log into the configuration interfaces of each device. for the ZyXEL Device, see Section 8.5 on page 134). 3 Press the button on the other , allowing it to find the WPS PIN - If you can connect, WPS was...
User Guide
Page 146
...the security settings it becomes "configured". It will be the registrar in all subsequent WPS connections in subsequent WPS connections, but a configured access point can be the registrar if necessary. Note that it supports both functions). All WPS-certified APs can no longer act as an enrollee, ...you want to a WPS-enabled access point. If the registrar is active (two minutes). Once a WPS-enabled device has connected to another device using WPS, it transmits to act ...
...the security settings it becomes "configured". It will be the registrar in all subsequent WPS connections in subsequent WPS connections, but a configured access point can be the registrar if necessary. Note that it supports both functions). All WPS-certified APs can no longer act as an enrollee, ...you want to a WPS-enabled access point. If the registrar is active (two minutes). Once a WPS-enabled device has connected to another device using WPS, it transmits to act ...
User Guide
Page 147
... handshake with the new client since you add another wireless client to use AP1 for the network). In this case, AP1 must connect to the access point anyway in order to the network.
... handshake with the new client since you add another wireless client to use AP1 for the network). In this case, AP1 must connect to the access point anyway in order to the network.
User Guide
Page 148
... should be aware. • WPS works in Infrastructure networks only (where an AP and a wireless client communicate). Chapter 8 Wireless LAN In step 3, you add another access point (AP2) to a network you already set up the second device in the same way. • WPS works only with the new... access point. For instance, if you can enter the key into the non-WPS device and join the network as normal (the non-WPS device must set ...
... should be aware. • WPS works in Infrastructure networks only (where an AP and a wireless client communicate). Chapter 8 Wireless LAN In step 3, you add another access point (AP2) to a network you already set up the second device in the same way. • WPS works only with the new... access point. For instance, if you can enter the key into the non-WPS device and join the network as normal (the non-WPS device must set ...
User Guide
Page 149
...the network. If this has happened. a rogue device must still associate with the access point to gain access to the moment you can easily check to a network. It does not matter if the access point is an unknown MAC address you press the button on the bottom of the device).... This is a possible way for a hacker to gain access to see if this happens, open the access point's configuration interface and look at the list of identifying the "correct" enrollee, and cannot differentiate between only two devices simultaneously...
...the network. If this has happened. a rogue device must still associate with the access point to gain access to the moment you can easily check to a network. It does not matter if the access point is an unknown MAC address you press the button on the bottom of the device).... This is a possible way for a hacker to gain access to see if this happens, open the access point's configuration interface and look at the list of identifying the "correct" enrollee, and cannot differentiate between only two devices simultaneously...
User Guide
Page 327
... when all communications between wireless clients or between a wireless client and a wired network client go through one access point (AP). Any time two or more wireless adapters are within range of each other , they can access the wired network and communicate with wireless adapters (A, B, C). Ad-hoc Wireless LAN Configuration The simplest WLAN configuration...
... when all communications between wireless clients or between a wireless client and a wired network client go through one access point (AP). Any time two or more wireless adapters are within range of each other , they can access the wired network and communicate with wireless adapters (A, B, C). Ad-hoc Wireless LAN Configuration The simplest WLAN configuration...
User Guide
Page 328
... communicate with the wired network but also mediate wireless network traffic in the immediate neighborhood. 328 ADSL Router Series User's Guide The Access Points not only provide communication with each access point connected together by a wired network. Figure 210 Basic Service Set ESS An Extended Service Set (ESS) consists of a series of wireless LAN...
... communicate with the wired network but also mediate wireless network traffic in the immediate neighborhood. 328 ADSL Router Series User's Guide The Access Points not only provide communication with each access point connected together by a wired network. Figure 210 Basic Service Set ESS An Extended Service Set (ESS) consists of a series of wireless LAN...
User Guide
Page 329
... AP is the radio frequency(ies) used by wireless devices to select a channel between 6 or 11. All access points and their associated wireless clients within range of the access point (AP) or wireless gateway, but are within the same ESS must have a choice of each ESS. The ...following figure illustrates a hidden node. RTS/CTS A hidden node occurs when two stations are within range of the same access point, but out-of-range of channels (for your geographical area. Figure 211 Infrastructure WLAN Channel A channel is using . Adjacent channels partially overlap ...
... AP is the radio frequency(ies) used by wireless devices to select a channel between 6 or 11. All access points and their associated wireless clients within range of the access point (AP) or wireless gateway, but are within the same ESS must have a choice of each ESS. The ...following figure illustrates a hidden node. RTS/CTS A hidden node occurs when two stations are within range of the same access point, but out-of-range of channels (for your geographical area. Figure 211 Infrastructure WLAN Channel A channel is using . Adjacent channels partially overlap ...
User Guide
Page 331
... be fragmented before they reach RTS/CTS size. IEEE 802.11g has several intermediate rate steps between wireless clients, access points and the wired network. Wireless security methods available on the ZyXEL Device are as follows: Table 114 IEEE 802.11g DATA RATE (MBPS) MODULATION 1 DBPSK (Differential Binary Phase ...on the network support it , otherwise the ZyXEL Device uses long preamble. Use long preamble if you are sure all support short preamble. IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or...
... be fragmented before they reach RTS/CTS size. IEEE 802.11g has several intermediate rate steps between wireless clients, access points and the wired network. Wireless security methods available on the ZyXEL Device are as follows: Table 114 IEEE 802.11g DATA RATE (MBPS) MODULATION 1 DBPSK (Differential Binary Phase ...on the network support it , otherwise the ZyXEL Device uses long preamble. Use long preamble if you are sure all support short preamble. IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or...
User Guide
Page 332
...network RADIUS server. • Support for EAP (Extensible Authentication Protocol, RFC 2486) that you want to associate with no changes to the access point or the wireless clients. Some advantages of IEEE 802.1x are connected to the network. • Accounting Keeps track of network devices....standard was designed to support extended authentication as well as providing additional accounting and control features. The access point is the client and the server is based on your ZyXEL Device. The RADIUS server handles the following figure shows the relative effectiveness of IEEE 802.11 ...
...network RADIUS server. • Support for EAP (Extensible Authentication Protocol, RFC 2486) that you want to associate with no changes to the access point or the wireless clients. Some advantages of IEEE 802.1x are connected to the network. • Accounting Keeps track of network devices....standard was designed to support extended authentication as well as providing additional accounting and control features. The access point is the client and the server is based on your ZyXEL Device. The RADIUS server handles the following figure shows the relative effectiveness of IEEE 802.11 ...
User Guide
Page 333
... first have a wired connection to the network and obtain the certificate(s) from the user and then sends another Access-Request message. The access point sends a proper response from a certificate authority (CA). The key is a password, they both know. In order... are exchanged between the access point and the RADIUS server for user authentication: • Access-Request Sent by an access point requesting authentication. • Access-Reject Sent by a RADIUS server rejecting access. • Access-Accept Sent by a RADIUS server allowing access. • Access-Challenge Sent by the ...
... first have a wired connection to the network and obtain the certificate(s) from the user and then sends another Access-Request message. The access point sends a proper response from a certificate authority (CA). The key is a password, they both know. In order... are exchanged between the access point and the RADIUS server for user authentication: • Access-Request Sent by an access point requesting authentication. • Access-Reject Sent by a RADIUS server rejecting access. • Access-Accept Sent by a RADIUS server allowing access. • Access-Challenge Sent by the ...
User Guide
Page 335
... Yes PEAP Yes Optional Yes Yes Strong Moderate Yes LEAP Yes No No Yes Moderate Moderate No WPA and WPA2 Wi-Fi Protected Access (WPA) is a subset of authentication types. Select WEP only when the AP and/or wireless clients do not support WPA2, ...data encryption by the authentication server. AES (Advanced Encryption Standard) is a block cipher that only requires a single (identical) password entered into each access point, wireless gateway and wireless client. WPA2 (IEEE 802.11i) is a wireless security standard that are dynamically generated and distributed by using Temporal Key...
... Yes PEAP Yes Optional Yes Yes Strong Moderate Yes LEAP Yes No No Yes Moderate Moderate No WPA and WPA2 Wi-Fi Protected Access (WPA) is a subset of authentication types. Select WEP only when the AP and/or wireless clients do not support WPA2, ...data encryption by the authentication server. AES (Advanced Encryption Standard) is a block cipher that only requires a single (identical) password entered into each access point, wireless gateway and wireless client. WPA2 (IEEE 802.11i) is a wireless security standard that are dynamically generated and distributed by using Temporal Key...