User Guide
Page 17
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
User Guide
Page 31
... NAS Starter Utility Agent that contains information, such as they display with unique server names. CHAPTER 3 NAS Starter Utility for NSA210 3.1 Overview This chapter describes the NAS Starter Utility for Windows XP, Windows Vista, or Windows 7. Using the initialization wizard ... a backup of the NAS Starter Utility (see Section 4.2.2 on the NSA210. Note: If the NSA210 will uninstall previous versions. The NAS Starter Utility software version number is a NAS Starter Utility available for NSA210. The NAS Starter Utility receives the response packet that always listens and...
... NAS Starter Utility Agent that contains information, such as they display with unique server names. CHAPTER 3 NAS Starter Utility for NSA210 3.1 Overview This chapter describes the NAS Starter Utility for Windows XP, Windows Vista, or Windows 7. Using the initialization wizard ... a backup of the NAS Starter Utility (see Section 4.2.2 on the NSA210. Note: If the NSA210 will uninstall previous versions. The NAS Starter Utility software version number is a NAS Starter Utility available for NSA210. The NAS Starter Utility receives the response packet that always listens and...
User Guide
Page 173
..., files incorrectly deleted or modified, or the NSA malfunctioning. Typical applications for RAID 1 are some suggestions for example). • Use anti-virus software on your data. • Place the NSA behind a hardware-based firewall. It should have two disks of sizes 150 GB and 200 GB respectively...still be available (but at degraded speeds until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for helping to protect your computer to the size of the smallest disk in one disk fails, there is more ...
..., files incorrectly deleted or modified, or the NSA malfunctioning. Typical applications for RAID 1 are some suggestions for example). • Use anti-virus software on your data. • Place the NSA behind a hardware-based firewall. It should have two disks of sizes 150 GB and 200 GB respectively...still be available (but at degraded speeds until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for helping to protect your computer to the size of the smallest disk in one disk fails, there is more ...
User Guide
Page 186
... TLS (Transport Layer Security) or SSL (Secure Sockets Layer) for secure transfers across the Internet. Your FTP client must be set to use Apple's iTunes software on your computer and then copy to the NSA. Chapter 10 Applications FTPES (File Transfer Protocol over Explicit TLS/SSL) File Transfer Protocol over Explicit...
... TLS (Transport Layer Security) or SSL (Secure Sockets Layer) for secure transfers across the Internet. Your FTP client must be set to use Apple's iTunes software on your computer and then copy to the NSA. Chapter 10 Applications FTPES (File Transfer Protocol over Explicit TLS/SSL) File Transfer Protocol over Explicit...
User Guide
Page 219
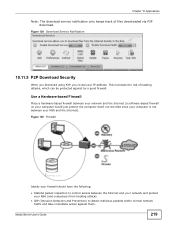
... of files downloaded via P2P download. Media Server User's Guide 219 Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
... of files downloaded via P2P download. Media Server User's Guide 219 Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
User Guide
Page 220
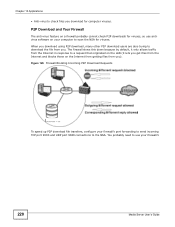
...-virus to check files you download for viruses. When you download using P2P download, many other P2P download users are also trying to use antivirus software on the Internet from getting files from you.
...-virus to check files you download for viruses. When you download using P2P download, many other P2P download users are also trying to use antivirus software on the Internet from getting files from you.
User Guide
Page 222
... 192.168.1.33, and the name of the web-published share is not recommended to publish shares if you may need to use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your website works and looks.
... 192.168.1.33, and the name of the web-published share is not recommended to publish shares if you may need to use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your website works and looks.
User Guide
Page 277
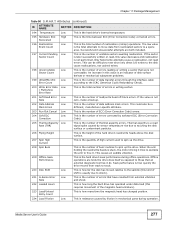
... Cancel Low This is the number of ECC (Error Correction Code) errors. 204 Soft ECC Correction Low This is the number of errors corrected by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of buzz routines to spin up the drive. 208 Spin Buzz...
... Cancel Low This is the number of ECC (Error Correction Code) errors. 204 Soft ECC Correction Low This is the number of errors corrected by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of buzz routines to spin up the drive. 208 Spin Buzz...
User Guide
Page 331
...361 for updated firmware. The NSA notifies you interrupt the upgrade, then the NSA may become unusable. A software restart is faster than turning the NSA off the NSA or perform a software restart. If you at login if a new firmware is logged into the NSA or transferring files to or... from the NSA. Reset Click this field's setting. Periodically Check for Latest Firmware Automatically Select this to have the NSA regularly check ZyXEL's server for your ...
...361 for updated firmware. The NSA notifies you interrupt the upgrade, then the NSA may become unusable. A software restart is faster than turning the NSA off the NSA or perform a software restart. If you at login if a new firmware is logged into the NSA or transferring files to or... from the NSA. Reset Click this field's setting. Periodically Check for Latest Firmware Automatically Select this to have the NSA regularly check ZyXEL's server for your ...
User Guide
Page 332
... on user access to shut down the system and restart it again later. Chapter 18 Maintenance Screens Click Maintenance > Shutdown to have the device perform a software restart. Table 122 Log Classes LOG CATEGORY DESCRIPTION Users This log class shows information on shares being created or deleted. Table 121 Maintenance > Shutdown LABEL...
... on user access to shut down the system and restart it again later. Chapter 18 Maintenance Screens Click Maintenance > Shutdown to have the device perform a software restart. Table 122 Log Classes LOG CATEGORY DESCRIPTION Users This log class shows information on shares being created or deleted. Table 121 Maintenance > Shutdown LABEL...
User Guide
Page 341
...Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of ways to protect your NSA is located The following sections ...describe these methods in each situation. See Section 8.6.3 on page 171 for more detail. Use anti-virus software on your NSA configurations such as a fire or earthquake occurs where your data on RAID. 19.3 Configuration File Backup and Restoration Use the...
...Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of ways to protect your NSA is located The following sections ...describe these methods in each situation. See Section 8.6.3 on page 171 for more detail. Use anti-virus software on your NSA configurations such as a fire or earthquake occurs where your data on RAID. 19.3 Configuration File Backup and Restoration Use the...
User Guide
Page 346
...'s allow list or lower your NSA. If you enable jumbo frames on your network and you may have to configure your software firewall or other security software to allow UDP port 50127 traffic from the NSA. Press the RESET button until they are all connected and each a unique name. After... the second beep, continue pressing the button for example). • Use the NAS Starter Utility to discover your software firewall or anti-virus scanner's security level. If you release the button. You can access it to allow UDP port 50127 traffic from the NSA...
...'s allow list or lower your NSA. If you enable jumbo frames on your network and you may have to configure your software firewall or other security software to allow UDP port 50127 traffic from the NSA. Press the RESET button until they are all connected and each a unique name. After... the second beep, continue pressing the button for example). • Use the NAS Starter Utility to discover your software firewall or anti-virus scanner's security level. If you release the button. You can access it to allow UDP port 50127 traffic from the NSA...
User Guide
Page 354
This does not include the applications you can install using media client software, you may not display in the list on your computer. I published a folder with the media server function, but the media client does not play some ....2 on page 362 for the file formats that are not supported on the media server may not support the file's format. Since the media client software uses your computer. 3 The media client may not display in Section 4.5.2 on your computer's installed codecs, files do not display in the list. iTunes does...
This does not include the applications you can install using media client software, you may not display in the list on your computer. I published a folder with the media server function, but the media client does not play some ....2 on page 362 for the file formats that are not supported on the media server may not support the file's format. Since the media client software uses your computer. 3 The media client may not display in Section 4.5.2 on your computer's installed codecs, files do not display in the list. iTunes does...
User Guide
Page 365
APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your computer. Windows Vista/XP/2000, Mac OS 9/ OS X, and all of using a dynamic IP, make sure ...
APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your computer. Windows Vista/XP/2000, Mac OS 9/ OS X, and all of using a dynamic IP, make sure ...
User Guide
Page 403
...possible by ICQ. If this service is logged on the Protocol. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. ESP User-Defined 50 (IPSEC_TUNNEL) The IPSEC ESP (Encapsulation Security Protocol) tunneling protocol uses this service. FINGER TCP 79 Finger is the... (Internet Assigned Number Authority) web site. • Name: This is the type of the applications that matches web names (for example www.zyxel.com) to RFC 1700 for further information about port numbers. • If the Protocol is TCP, UDP, or TCP/UDP, this is ...
...possible by ICQ. If this service is logged on the Protocol. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. ESP User-Defined 50 (IPSEC_TUNNEL) The IPSEC ESP (Encapsulation Security Protocol) tunneling protocol uses this service. FINGER TCP 79 Finger is the... (Internet Assigned Number Authority) web site. • Name: This is the type of the applications that matches web names (for example www.zyxel.com) to RFC 1700 for further information about port numbers. • If the Protocol is TCP, UDP, or TCP/UDP, this is ...
User Guide
Page 433
...effect. Any rights not expressly granted by ZyXEL to you are disclaimed. 2.Ownership You have the right to make one backup copy of the Software and Documentation solely for "NSA210, NSA 221, NSA310, NSA320, and NSA325" WARNING: ZyXEL Communications Corp. Any other entity is ...strictly forbidden and is distributed (the "Software"), including any other use the program with ZyXEL. APPENDIX E Open Source Licences End...
...effect. Any rights not expressly granted by ZyXEL to you are disclaimed. 2.Ownership You have the right to make one backup copy of the Software and Documentation solely for "NSA210, NSA 221, NSA310, NSA320, and NSA325" WARNING: ZyXEL Communications Corp. Any other entity is ...strictly forbidden and is distributed (the "Software"), including any other use the program with ZyXEL. APPENDIX E Open Source Licences End...
User Guide
Page 434
... remove any proprietary notice of ZyXEL or any of its software and products. 5.Confidentiality You acknowledge that the Software contains third party software, ZyXEL has no warranty (express, implied or statutory) whatsoever with the Software, and to use the Software, or any part thereof. ...TO THE MAXIMUM EXTENT PERMITTED BY LAW, ZyXEL DISCLAIMS ALL WARRANTIES OF ANY KIND,...
... remove any proprietary notice of ZyXEL or any of its software and products. 5.Confidentiality You acknowledge that the Software contains third party software, ZyXEL has no warranty (express, implied or statutory) whatsoever with the Software, and to use the Software, or any part thereof. ...TO THE MAXIMUM EXTENT PERMITTED BY LAW, ZyXEL DISCLAIMS ALL WARRANTIES OF ANY KIND,...
User Guide
Page 435
...appropriate court or Commercial Arbitration Association sitting in your possession or under your control. ZyXEL's TOTAL AGGREGATE LIABILITY WITH RESPECT TO ITS OBLIGATIONS UNDER THIS AGREEMENT OR OTHERWISE WITH RESPECT TO THE SOFTWARE AND DOCUMENTATION OR OTHERWISE SHALL BE EQUAL TO THE PURCHASE PRICE, BUT SHALL ...governed by you without regard to certify in writing that you agree to destroy or return to ZyXEL all copies of this License Agreement at any of the terms of the Software and Documentation in ROC, Taiwan if the parties agree to confidentiality, proprietary rights, and non-...
...appropriate court or Commercial Arbitration Association sitting in your possession or under your control. ZyXEL's TOTAL AGGREGATE LIABILITY WITH RESPECT TO ITS OBLIGATIONS UNDER THIS AGREEMENT OR OTHERWISE WITH RESPECT TO THE SOFTWARE AND DOCUMENTATION OR OTHERWISE SHALL BE EQUAL TO THE PURCHASE PRICE, BUT SHALL ...governed by you without regard to certify in writing that you agree to destroy or return to ZyXEL all copies of this License Agreement at any of the terms of the Software and Documentation in ROC, Taiwan if the parties agree to confidentiality, proprietary rights, and non-...
User Guide
Page 436
... and data used in examples herein are in possession of such. GNU LESSER GENERAL PUBLIC LICENSE Version 2.1, February 1999 Copyright (C) 1991, 1999 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA Everyone is the first released version of the Lesser GPL. It also... at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete machine-...
... and data used in examples herein are in possession of such. GNU LESSER GENERAL PUBLIC LICENSE Version 2.1, February 1999 Copyright (C) 1991, 1999 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA Everyone is the first released version of the Lesser GPL. It also... at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete machine-...
User Guide
Page 437
... wish to make sure that we insist that you receive source code or can do these things. Most GNU software, including some specially designated software packages--typically libraries--of the original library. It also provides other authors who decide to use in order to permit...statically or using a shared library, the combination of the two is legally speaking a combined work, a derivative of the Free Software Foundation and other free software developers Less of it does Less to protect the user's freedom than the ordinary General Public License. Therefore, we gave you must...
... wish to make sure that we insist that you receive source code or can do these things. Most GNU software, including some specially designated software packages--typically libraries--of the original library. It also provides other authors who decide to use in order to permit...statically or using a shared library, the combination of the two is legally speaking a combined work, a derivative of the Free Software Foundation and other free software developers Less of it does Less to protect the user's freedom than the ordinary General Public License. Therefore, we gave you must...