User Guide
Page 17
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
User Guide
Page 31
...in the NSA. You can be used on the same network as host name, IP, and so on the NSA210. Media Server User's Guide 31 The NAS Starter Utility software version number is 2.02. Click Help to identify each NSA in the process. This enables you have a ...NSA221, NSA310, NSA320 or NSA325, it . CHAPTER 3 NAS Starter Utility for NSA210 3.1 Overview This chapter describes the NAS Starter Utility for...
...in the NSA. You can be used on the same network as host name, IP, and so on the NSA210. Media Server User's Guide 31 The NAS Starter Utility software version number is 2.02. Click Help to identify each NSA in the process. This enables you have a ...NSA221, NSA310, NSA320 or NSA325, it . CHAPTER 3 NAS Starter Utility for NSA210 3.1 Overview This chapter describes the NAS Starter Utility for...
User Guide
Page 173
... for the NSA). For example, if you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example). • Use anti-virus software on your computer to protect your data will still be available (but at degraded speeds until you 're using a RAID 1 volume...
... for the NSA). For example, if you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example). • Use anti-virus software on your computer to protect your data will still be available (but at degraded speeds until you 're using a RAID 1 volume...
User Guide
Page 186
The NSA streams files to use Apple's iTunes software on the NSA. The NSA can download iTunes from www.apple.com. You can function as in a home network. Your FTP client must be set ...
The NSA streams files to use Apple's iTunes software on the NSA. The NSA can download iTunes from www.apple.com. You can function as in a home network. Your FTP client must be set ...
User Guide
Page 219
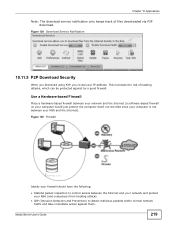
... immediate action against by a good firewall. Media Server User's Guide 219 Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
... immediate action against by a good firewall. Media Server User's Guide 219 Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
User Guide
Page 220
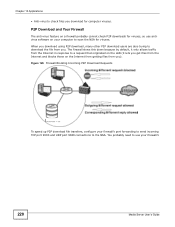
..., it lets you get files from the Internet and blocks those on the Internet from getting files from you ). You probably need to use antivirus software on a firewall probably cannot check P2P downloads for viruses, so use your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089...
..., it lets you get files from the Internet and blocks those on the Internet from getting files from you ). You probably need to use antivirus software on a firewall probably cannot check P2P downloads for viruses, so use your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089...
User Guide
Page 222
... others could "web publish" it in a FamilyPhotos share, you "publish" shares (containing folders and files) on firewalls. Note: The NSA does not use HTML editing software (not included) to create an index.html or index.htm file to know and enter a user name and password. Additionally, you can use any security...
... others could "web publish" it in a FamilyPhotos share, you "publish" shares (containing folders and files) on firewalls. Note: The NSA does not use HTML editing software (not included) to create an index.html or index.htm file to know and enter a user name and password. Additionally, you can use any security...
User Guide
Page 277
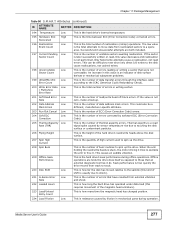
... Cancel Low This is the number of ECC (Error Correction Code) errors. 204 Soft ECC Correction Low This is the number of errors corrected by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of data address mark errors. When the arm holding the read...
... Cancel Low This is the number of ECC (Error Correction Code) errors. 204 Soft ECC Correction Low This is the number of errors corrected by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of data address mark errors. When the arm holding the read...
User Guide
Page 331
...upgrade. Click Apply to save this to make sure that no one is faster than turning the NSA off the NSA or perform a software restart. Before shutting down or restarting, check the System Status > Active Sessions screen to refresh the screen. Reset Click this field's ... Periodically Check for updated firmware. Check for Latest Firmware Now Click this to have the NSA regularly check ZyXEL's server for Latest Firmware Automatically Select this screen. A software restart is logged into the NSA or transferring files to upload the new firmware. Table 120 Maintenance > FW...
...upgrade. Click Apply to save this to make sure that no one is faster than turning the NSA off the NSA or perform a software restart. Before shutting down or restarting, check the System Status > Active Sessions screen to refresh the screen. Reset Click this field's ... Periodically Check for updated firmware. Check for Latest Firmware Now Click this to have the NSA regularly check ZyXEL's server for Latest Firmware Automatically Select this screen. A software restart is logged into the NSA or transferring files to upload the new firmware. Table 120 Maintenance > FW...
User Guide
Page 332
... or deleted. Shares This log class shows information on the operation of the NSA's built-in services. Shutdown Click this to have the device perform a software restart. Figure 215 Maintenance > Shutdown > Confirm Shutdown 18.9 Technical Reference This section provides technical background information on the topics discussed in this chapter. 18.9.1 Log...
... or deleted. Shares This log class shows information on the operation of the NSA's built-in services. Shutdown Click this to have the device perform a software restart. Figure 215 Maintenance > Shutdown > Confirm Shutdown 18.9 Technical Reference This section provides technical background information on the topics discussed in this chapter. 18.9.1 Log...
User Guide
Page 341
Use anti-virus software on your computer to another NSA or external USB hard drive. Hard drive malfunction. Back up the NSA configuration file before saving them onto the ... 19 Protecting Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of your NSA configurations such as a fire or earthquake occurs where your NSA is using...
Use anti-virus software on your computer to another NSA or external USB hard drive. Hard drive malfunction. Back up the NSA configuration file before saving them onto the ... 19 Protecting Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of your NSA configurations such as a fire or earthquake occurs where your NSA is using...
User Guide
Page 346
... and each a unique name. I cannot access the NSA anymore. If you could see Section 1.1.4 on a previous attempt but I was able to your software firewall's allow UDP port 50127 traffic from the NSA. Chapter 20 Troubleshooting The NAS Starter Utility discovered my NSA but the status is 'nsa' followed... in a network that does not support them, you will hear three quick beeps after you will have several NSAs connected to your software firewall or other security software to the default setting. 346 Media Server User's Guide Alternatively you may have to allow list or lower your...
... and each a unique name. I cannot access the NSA anymore. If you could see Section 1.1.4 on a previous attempt but I was able to your software firewall's allow UDP port 50127 traffic from the NSA. Chapter 20 Troubleshooting The NAS Starter Utility discovered my NSA but the status is 'nsa' followed... in a network that does not support them, you will hear three quick beeps after you will have several NSAs connected to your software firewall or other security software to the default setting. 346 Media Server User's Guide Alternatively you may have to allow list or lower your...
User Guide
Page 354
... put on the NSA. 1 Make sure the files are not supported on page 63. See Section 21.2 on the media client. Since the media client software uses your computer's installed codecs, files do not display in the list on page 362 for the file formats that the media server supports. 2 If... not play if the required codec is enabled. 354 Media Server User's Guide This does not include the applications you can install using media client software, you have installed the application and can use the Package Management screen (Chapter 11 on the media server may not display in the list. See...
... put on the NSA. 1 Make sure the files are not supported on page 63. See Section 21.2 on the media client. Since the media client software uses your computer's installed codecs, files do not display in the list on page 362 for the file formats that the media server supports. 2 If... not play if the required codec is enabled. 354 Media Server User's Guide This does not include the applications you can install using media client software, you have installed the application and can use the Package Management screen (Chapter 11 on the media server may not display in the list. See...
User Guide
Page 365
... in the same subnet. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your network. If you manually assign IP information instead of using a dynamic IP, make sure that your...
... in the same subnet. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your network. If you manually assign IP information instead of using a dynamic IP, make sure that your...
User Guide
Page 403
... or create a different one, if you like. • Protocol: This is logged on the Protocol. a client/server protocol for example www.zyxel.com) to find out if a user is the type of IP protocol used by ICQ. If this service or the situations in e- Please...TCP 5190 AOL's Internet Messenger service. BOOTP_SERVER UDP 67 DHCP Server. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. AUTH TCP 113 Authentication protocol used as a listening port by the service. HTTPS TCP 443 HTTPS is a secured http session often used ....
... or create a different one, if you like. • Protocol: This is logged on the Protocol. a client/server protocol for example www.zyxel.com) to find out if a user is the type of IP protocol used by ICQ. If this service or the situations in e- Please...TCP 5190 AOL's Internet Messenger service. BOOTP_SERVER UDP 67 DHCP Server. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. AUTH TCP 113 Authentication protocol used as a listening port by the service. HTTPS TCP 443 HTTPS is a secured http session often used ....
User Guide
Page 433
...PARTY. 1.Grant of License for Personal Use ZyXEL Communications Corp. ("ZyXEL") grants you a non-exclusive, non-sublicense, nontransferable license to you have a license to use of the Software by ZyXEL, and all times with which this license ...is a violation of the license granted hereunder. Any rights not expressly granted by ZyXEL to use only, for "NSA210, NSA 221, NSA310, NSA320, and NSA325" WARNING: ZyXEL...
...PARTY. 1.Grant of License for Personal Use ZyXEL Communications Corp. ("ZyXEL") grants you a non-exclusive, non-sublicense, nontransferable license to you have a license to use of the Software by ZyXEL, and all times with which this license ...is a violation of the license granted hereunder. Any rights not expressly granted by ZyXEL to use only, for "NSA210, NSA 221, NSA310, NSA320, and NSA325" WARNING: ZyXEL...
User Guide
Page 434
... this License Agreement to those persons employed by their compliance with the applicable license terms of the Software package, access to certain third party software as a convenience. To the extent that the Software contains third party software, ZyXEL has no warranty (express, implied or statutory) whatsoever with respect to its licensors from the object code...
... this License Agreement to those persons employed by their compliance with the applicable license terms of the Software package, access to certain third party software as a convenience. To the extent that the Software contains third party software, ZyXEL has no warranty (express, implied or statutory) whatsoever with respect to its licensors from the object code...
User Guide
Page 435
... for any time by the laws of Republic of China without the prior written consent of the Software and Documentation in ROC, Taiwan if the parties agree to ZyXEL all copies of ZyXEL. You may terminate this License Agreement for any disputes arising out of this License Agreement at any..., BUSINESS INTERRUPTION, OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF THE USE OF OR INABILITY TO USE THE SOFTWARE OR PROGRAM, OR FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. This License Agreement, the rights granted hereunder, the...
... for any time by the laws of Republic of China without the prior written consent of the Software and Documentation in ROC, Taiwan if the parties agree to ZyXEL all copies of ZyXEL. You may terminate this License Agreement for any disputes arising out of this License Agreement at any..., BUSINESS INTERRUPTION, OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF THE USE OF OR INABILITY TO USE THE SOFTWARE OR PROGRAM, OR FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. This License Agreement, the rights granted hereunder, the...
User Guide
Page 436
... Programs that we are fictitious unless otherwise noted. This Product includes cups, libgcgi, libgphoto2, libraw1394, pam_mount, wxWidgets, wxWidgets and flac software under the open source code licenses which allows you if we distributed to you to reasonably effect the intention of the parties. It also... at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete...
... Programs that we are fictitious unless otherwise noted. This Product includes cups, libgcgi, libgphoto2, libraw1394, pam_mount, wxWidgets, wxWidgets and flac software under the open source code licenses which allows you if we distributed to you to reasonably effect the intention of the parties. It also... at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete...
User Guide
Page 437
... work, a derivative of the original library. You can use it too, but we suggest you can change it. When we speak of free software, we Media Server User's Guide 437 that you first think carefully about whether this license or the ordinary General Public License is the better strategy... which gives you must give the recipients all its criteria of freedom. Also, if the library is quite different from a patent holder. Finally, software patents pose a constant threat to the existence of any patent license obtained for a version of the library must make sure that you are informed ...
... work, a derivative of the original library. You can use it too, but we suggest you can change it. When we speak of free software, we Media Server User's Guide 437 that you first think carefully about whether this license or the ordinary General Public License is the better strategy... which gives you must give the recipients all its criteria of freedom. Also, if the library is quite different from a patent holder. Finally, software patents pose a constant threat to the existence of any patent license obtained for a version of the library must make sure that you are informed ...