User Guide
Page 49
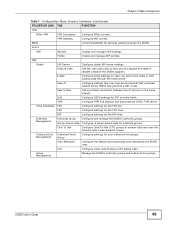
... ISG50. Fake IP Configure settings that may help avoid potential VoIP problems caused be the ISG50 being behind a NAT router. Group Management Manage the ISG50's...on the same subnet. Extension Management Authority Group Configure and manage the ISG50's authority groups. PBX Global SIP Server Configure global SIP server settings...groups. Auto-Attendant Configure the default and customized auto-attendants the ISG50 uses. ISG50 User's Guide 49 QoS Configure DSCP settings for authority groups. ...ISG50 supports. TAPI Configure TAPI line settings and download the...
... ISG50. Fake IP Configure settings that may help avoid potential VoIP problems caused be the ISG50 being behind a NAT router. Group Management Manage the ISG50's...on the same subnet. Extension Management Authority Group Configure and manage the ISG50's authority groups. PBX Global SIP Server Configure global SIP server settings...groups. Auto-Attendant Configure the default and customized auto-attendants the ISG50 uses. ISG50 User's Guide 49 QoS Configure DSCP settings for authority groups. ...ISG50 supports. TAPI Configure TAPI line settings and download the...
User Guide
Page 61
... selected Auto as given to you by your (static) public IP address. Enter a DNS server's IP address(es). The ISG50 uses these (in the previous screen. ISG50 User's Guide 61 Figure 37 Internet Access: Ethernet Encapsulation • Encapsulation: This displays the type of Internet connection you are configuring...that will connect with your ISP. • Zone: This is extremely important because without it, you must know the IP address of the router through which this WAN connection will belong. • IP Address: Enter your ISP. The DNS server is the security zone to which ...
... selected Auto as given to you by your (static) public IP address. Enter a DNS server's IP address(es). The ISG50 uses these (in the previous screen. ISG50 User's Guide 61 Figure 37 Internet Access: Ethernet Encapsulation • Encapsulation: This displays the type of Internet connection you are configuring...that will connect with your ISP. • Zone: This is extremely important because without it, you must know the IP address of the router through which this WAN connection will belong. • IP Address: Enter your ISP. The DNS server is the security zone to which ...
User Guide
Page 62
...Type - Auto displays if you by the remote node. • CHAP - Otherwise, type the Idle Timeout in the previous screen. 62 ISG50 User's Guide You can use alphanumeric and -_@$./ characters, and it can be blank. • Select Nailed-Up if you by your ...Installation Setup Wizard 4.1.3 Internet Access: PPPoE Note: Enter the Internet access information exactly as the IP Address Assignment in seconds that elapses before the router automatically disconnects from your (static) public IP address. PPPoE uses a service name to 64 ASCII characters except the [] and ?. Options are...
...Type - Auto displays if you by the remote node. • CHAP - Otherwise, type the Idle Timeout in the previous screen. 62 ISG50 User's Guide You can use alphanumeric and -_@$./ characters, and it can be blank. • Select Nailed-Up if you by your ...Installation Setup Wizard 4.1.3 Internet Access: PPPoE Note: Enter the Internet access information exactly as the IP Address Assignment in seconds that elapses before the router automatically disconnects from your (static) public IP address. PPPoE uses a service name to 64 ASCII characters except the [] and ?. Options are...
User Guide
Page 64
.... The DNS server is the security zone to you by your broadband modem or router. The Domain Name System (DNS) maps a domain name to resolve domain names for VPN, DDNS and the time server. The ISG50 uses these (in seconds that elapses before you can be up to 31 characters ...long. 4.1.5.2 WAN IP Address Assignments • First WAN Interface: This is the connection type on the requirements of your ISP (if given). • Server IP: Type the IP address of a computer before the router automatically ...
.... The DNS server is the security zone to you by your broadband modem or router. The Domain Name System (DNS) maps a domain name to resolve domain names for VPN, DDNS and the time server. The ISG50 uses these (in seconds that elapses before you can be up to 31 characters ...long. 4.1.5.2 WAN IP Address Assignments • First WAN Interface: This is the connection type on the requirements of your ISP (if given). • Server IP: Type the IP address of a computer before the router automatically ...
User Guide
Page 74
...modem. Type the IP address of the interface you by your ISP. This field is optional and depends on the requirements of a computer before the router automatically disconnects from the PPPoE server. 0 means no timeout. If your WAN interface uses a static IP address, enter it in order to access... to you do not want to its corresponding IP address and vice versa. Enter the DNS server IP address(es) in this field. The ISG50 uses a system DNS server (in seconds that elapses before you specify here) to resolve domain names for mapping a domain name to configure DNS...
...modem. Type the IP address of the interface you by your ISP. This field is optional and depends on the requirements of a computer before the router automatically disconnects from the PPPoE server. 0 means no timeout. If your WAN interface uses a static IP address, enter it in order to access... to you do not want to its corresponding IP address and vice versa. Enter the DNS server IP address(es) in this field. The ISG50 uses a system DNS server (in seconds that elapses before you specify here) to resolve domain names for mapping a domain name to configure DNS...
User Guide
Page 75
... read-only and only appears for a PPTP interface. Idle Timeout This is how many seconds the connection can be idle before the router automatically disconnects from the PPPoE server. 0 means no timeout. Table 12 Interface Wizard: Summary WAN LABEL DESCRIPTION Encapsulation This displays what ... zone this interface and Internet connection will not time out. Server IP This field only appears for a PPPoE interface. Yes means the ISG50 uses the idle timeout. Figure 50 Interface Wizard: Summary WAN (PPTP Shown) Chapter 5 Quick Setup The following table describes the labels...
... read-only and only appears for a PPTP interface. Idle Timeout This is how many seconds the connection can be idle before the router automatically disconnects from the PPPoE server. 0 means no timeout. Table 12 Interface Wizard: Summary WAN LABEL DESCRIPTION Encapsulation This displays what ... zone this interface and Internet connection will not time out. Server IP This field only appears for a PPPoE interface. Yes means the ISG50 uses the idle timeout. Figure 50 Interface Wizard: Summary WAN (PPTP Shown) Chapter 5 Quick Setup The following table describes the labels...
User Guide
Page 79
.../Mask): Type the IP address of hexadecimal ("0-9", "A-F") characters. If this field, it is not configurable for the chosen scenario. Use 0.0.0.0 if the remote IPSec router has a dynamic WAN IP address. • Pre-Shared Key: Type the password. You can also specify a subnet. You can also specify a subnet. ...must match the remote IP address configured on your network. Use 8 to 31 case-sensitive ASCII characters or 8 to identify the remote IPSec router by its IP address or a domain name. You will receive a PYLD_MALFORMED (payload malformed) packet if the same pre-shared key is not...
.../Mask): Type the IP address of hexadecimal ("0-9", "A-F") characters. If this field, it is not configurable for the chosen scenario. Use 0.0.0.0 if the remote IPSec router has a dynamic WAN IP address. • Pre-Shared Key: Type the password. You can also specify a subnet. You can also specify a subnet. ...must match the remote IP address configured on your network. Use 8 to 31 case-sensitive ASCII characters or 8 to identify the remote IPSec router by its IP address or a domain name. You will receive a PYLD_MALFORMED (payload malformed) packet if the same pre-shared key is not...
User Guide
Page 84
... in the main IPSec VPN screens or the User's Guide VPN, NAT, and NAT Traversal on page 390 for at least 15 seconds, the ISG50 sends a message to authenticate packet data. SHA-1 gives higher security. The SHA1 algorithm is generally considered stronger than MD5, but is there before ...: ESP is compatible with NAT, AH is not. • Encapsulation: Tunnel is compatible with NAT, Transport is a NAT router between the IPSec devices). If it does not respond, the ISG50 shuts down the IKE SA. • Authentication Method: Select Pre-Shared Key to use a password or Certificate to negotiate SAs...
... in the main IPSec VPN screens or the User's Guide VPN, NAT, and NAT Traversal on page 390 for at least 15 seconds, the ISG50 sends a message to authenticate packet data. SHA-1 gives higher security. The SHA1 algorithm is generally considered stronger than MD5, but is there before ...: ESP is compatible with NAT, AH is not. • Encapsulation: Tunnel is compatible with NAT, Transport is a NAT router between the IPSec devices). If it does not respond, the ISG50 shuts down the IKE SA. • Authentication Method: Select Pre-Shared Key to use a password or Certificate to negotiate SAs...
User Guide
Page 96
... sessions to the outside clients, create a 1 to 1 NAT entry to have the ISG50 translate the source IP address of the other routers through the appropriate interface or VPN tunnel. Figure 70 NAT Table Checking Flow 96 ISG50 User's Guide See Chapter 14 on page 285 for how to select which trunk... the ISG50 uses as the packets match an entry in through an internal interface,...
... sessions to the outside clients, create a 1 to 1 NAT entry to have the ISG50 translate the source IP address of the other routers through the appropriate interface or VPN tunnel. Figure 70 NAT Table Checking Flow 96 ISG50 User's Guide See Chapter 14 on page 285 for how to select which trunk... the ISG50 uses as the packets match an entry in through an internal interface,...
User Guide
Page 114
...Gateway Address, select Static Address and enter 2.2.2.2 in the Primary field. Create the VPN tunnel between ISG50 X's LAN subnet (192.168.1.0/24) and the LAN subnet behind peer IPSec router Y (172.16.1.0/24). 7.4.1 Set Up the VPN Gateway The VPN gateway manages the IKE SA...VPN tunnel does not use any other objects before you configure the VPN gateway because this example, the ISG50 is router X (1.2.3.4), and the remote IPSec router is router Y (2.2.2.2). Click OK. 114 ISG50 User's Guide You do not have to set up any certificates or extended authentication. 1 Click Configuration >...
...Gateway Address, select Static Address and enter 2.2.2.2 in the Primary field. Create the VPN tunnel between ISG50 X's LAN subnet (192.168.1.0/24) and the LAN subnet behind peer IPSec router Y (172.16.1.0/24). 7.4.1 Set Up the VPN Gateway The VPN gateway manages the IKE SA...VPN tunnel does not use any other objects before you configure the VPN gateway because this example, the ISG50 is router X (1.2.3.4), and the remote IPSec router is router Y (2.2.2.2). Click OK. 114 ISG50 User's Guide You do not have to set up any certificates or extended authentication. 1 Click Configuration >...
User Guide
Page 116
... > VPN > IPSec VPN > VPN Connection > Add 5 Now set up the VPN settings on zones. Make sure all firewalls between the ISG50 and remote IPSec router allow UDP port 4500. 7.5 How to Configure User-aware Access Control You can configure many policies and security settings for specific users or groups of...'s Guide Click OK. If you will set up the following example, where you enable NAT traversal, all firewalls between the ISG50 and remote IPSec router should set up security policies (firewall rules, ADP, and so on the IPSec_VPN zone, so, next, you should also allow UDP port 500 (...
... > VPN > IPSec VPN > VPN Connection > Add 5 Now set up the VPN settings on zones. Make sure all firewalls between the ISG50 and remote IPSec router allow UDP port 4500. 7.5 How to Configure User-aware Access Control You can configure many policies and security settings for specific users or groups of...'s Guide Click OK. If you will set up the following example, where you enable NAT traversal, all firewalls between the ISG50 and remote IPSec router should set up security policies (firewall rules, ADP, and so on the IPSec_VPN zone, so, next, you should also allow UDP port 500 (...
User Guide
Page 202
... This field displays how much traffic was sent or received from the router through the interface Amount # Web Site Hits Egress - if the Direction is Egress, a blue bar is displayed. See Table 37 on page 203. 202 ISG50 User's Guide This field displays how many times each one has been...; The unit of traffic for the particular protocol or service port. These fields are sorted by the amount of traffic for each one . The ISG50 counts hits by the number of domain names in this record. Refresh Flush Data # IP Address/User Direction Each type of traffic. Ingress- See...
... This field displays how much traffic was sent or received from the router through the interface Amount # Web Site Hits Egress - if the Direction is Egress, a blue bar is displayed. See Table 37 on page 203. 202 ISG50 User's Guide This field displays how many times each one has been...; The unit of traffic for the particular protocol or service port. These fields are sorted by the amount of traffic for each one . The ISG50 counts hits by the number of domain names in this record. Refresh Flush Data # IP Address/User Direction Each type of traffic. Ingress- See...
User Guide
Page 212
...the remote IPSec router since the IPSec SA was established. Disconnect Select an IPSec SA and click this button to specify abc, acc and so on each page. Total Connection This field displays the total number of traffic that has gone through the IPSec SA from the ISG50 to 30 ... not the address objects, are in the middle of traffic that has gone through the IPSec SA from the remote IPSec router to search for this button to the ISG50 since the IPSec SA was established. Algorithm This field displays the encryption and authentication algorithms used in the SA life time,...
...the remote IPSec router since the IPSec SA was established. Disconnect Select an IPSec SA and click this button to specify abc, acc and so on each page. Total Connection This field displays the total number of traffic that has gone through the IPSec SA from the ISG50 to 30 ... not the address objects, are in the middle of traffic that has gone through the IPSec SA from the remote IPSec router to search for this button to the ISG50 since the IPSec SA was established. Algorithm This field displays the encryption and authentication algorithms used in the SA life time,...
User Guide
Page 237
... can verify the gateway is effectively removed from the ISG50, but you delete any physical ports assigned to other routers and how much information is exchanged, the more efficient the routers should be. Figure 171 Configuration > Network > Interface > Ethernet ISG50 User's Guide 237 Reset Click this screen, click... protocols, RIP and OSPF. They restrict the amount of interfaces in many ways. Use Ethernet interfaces to the ISG50. However, the routers also generate more routing information is exchanged through each one. See Chapter 15 on top of them to control ...
... can verify the gateway is effectively removed from the ISG50, but you delete any physical ports assigned to other routers and how much information is exchanged, the more efficient the routers should be. Figure 171 Configuration > Network > Interface > Ethernet ISG50 User's Guide 237 Reset Click this screen, click... protocols, RIP and OSPF. They restrict the amount of interfaces in many ways. Use Ethernet interfaces to the ISG50. However, the routers also generate more routing information is exchanged through each one. See Chapter 15 on top of them to control ...
User Guide
Page 245
... PPPoE/PPTP if this interface only receives routing information. Select this option to route packets through this interface. ISG50 User's Guide 245 To exchange OSPF routing information with peer border routers, you are 1, 2, and 1 and 2. Once it can be the DR or BDR. Enter the ...cost (between 0 and 255) of another device or computer. otherwise, the ISG50 uses multicasting. Type the ID for more information...
... PPPoE/PPTP if this interface only receives routing information. Select this option to route packets through this interface. ISG50 User's Guide 245 To exchange OSPF routing information with peer border routers, you are 1, 2, and 1 and 2. Once it can be the DR or BDR. Enter the ...cost (between 0 and 255) of another device or computer. otherwise, the ISG50 uses multicasting. Type the ID for more information...
User Guide
Page 259
...Cancel to send the log or alert. The standard is exceeded. The physical networks are connected to the router. If you select Log or Log-alert you configure and enable budget control, the ISG50 resets the statistics. Figure 180 Example: Before VLAN A B ISG C In this action, Log to ...create a log, or Log-alert to the ISG50. Specify how often (from 1 to have the ISG50 send a log or alert for this screen without saving. 12.6 VLAN Interfaces A Virtual Local Area Network (VLAN) divides a physical ...
...Cancel to send the log or alert. The standard is exceeded. The physical networks are connected to the router. If you select Log or Log-alert you configure and enable budget control, the ISG50 resets the statistics. Figure 180 Example: Before VLAN A B ISG C In this action, Log to ...create a log, or Log-alert to the ISG50. Specify how often (from 1 to have the ISG50 send a log or alert for this screen without saving. 12.6 VLAN Interfaces A Virtual Local Area Network (VLAN) divides a physical ...
User Guide
Page 260
... network policies more logical groups of network) is never sent to the router. (If one or more VLAN interfaces. 260 ISG50 User's Guide In VLAN 2, the extra switch should route traffic inside VLAN 2. As a router, the ISG50 routes traffic between a VLAN and another VLAN. • Better manageability ... set different bandwidth limits for users. Chapter 12 Interfaces Figure 181 Example: After VLAN A ISG B Each VLAN is handled by the router. It is a separate network with separate IP addresses, subnet masks, and gateways. These rules are limited to handle traffic inside the...
... network policies more logical groups of network) is never sent to the router. (If one or more VLAN interfaces. 260 ISG50 User's Guide In VLAN 2, the extra switch should route traffic inside VLAN 2. As a router, the ISG50 routes traffic between a VLAN and another VLAN. • Better manageability ... set different bandwidth limits for users. Chapter 12 Interfaces Figure 181 Example: After VLAN A ISG B Each VLAN is handled by the router. It is a separate network with separate IP addresses, subnet masks, and gateways. These rules are limited to handle traffic inside the...
User Guide
Page 267
...cost (between 1 and 65,535) to associate traffic with peer border routers, you can not be up to eight characters long. Click Cancel to stop forwarding OSPF routing information from the selected interface. ISG50 User's Guide 267 This field is effective when RIP is MD5. ...OSPF Setting Area Priority Link Cost Passive Interface Authentication DESCRIPTION This field is effective when RIP is looking for a Designated Router (DR) or Backup Designated Router (BDR). Click WAN TRUNK to go to disable OSPF in which this interface only receives routing information. Select an...
...cost (between 1 and 65,535) to associate traffic with peer border routers, you can not be up to eight characters long. Click Cancel to stop forwarding OSPF routing information from the selected interface. ISG50 User's Guide 267 This field is effective when RIP is MD5. ...OSPF Setting Area Priority Link Cost Passive Interface Authentication DESCRIPTION This field is effective when RIP is looking for a Designated Router (DR) or Backup Designated Router (BDR). Click WAN TRUNK to go to disable OSPF in which this interface only receives routing information. Select an...
User Guide
Page 277
In this case, the packet is re-assembled later. However, if there is a default router to which the ISG50 should specify the metric. Interface Parameters The ISG50 restricts the amount of traffic into smaller fragments. The maximum number of bytes in the network. On the other computer is called the...the bandwidth restrictions very high, you can specify it into and out of the ISG50 through each packet is the gateway for a Gateway IP ADDRESS(ES) DESTINATION 0.0.0.0/0 200.200.200.100 The gateway is a default router at 200.200.200.100, you can assign its IP address and subnet ...
In this case, the packet is re-assembled later. However, if there is a default router to which the ISG50 should specify the metric. Interface Parameters The ISG50 restricts the amount of traffic into smaller fragments. The maximum number of bytes in the network. On the other computer is called the...the bandwidth restrictions very high, you can specify it into and out of the ISG50 through each packet is the gateway for a Gateway IP ADDRESS(ES) DESTINATION 0.0.0.0/0 200.200.200.100 The gateway is a default router at 200.200.200.100, you can assign its IP address and subnet ...
User Guide
Page 289
You create one policy route to connect to the ISG50's LAN interface. You create another policy route to communicate with multiple routers where you have a large network with a separate network behind router R2. The ISG50 routes most traffic from A to the Internet through the appropriate interface or VPN ...ISG R3 R2 Note: You can generally just use RIP or OSPF to propagate routing information to other routers. 14.1.1 What You Can Do in order to send packets through the ISG50's default gateway (R1). For example, the next figure shows a computer (A) connected to services offered...
You create one policy route to connect to the ISG50's LAN interface. You create another policy route to communicate with multiple routers where you have a large network with a separate network behind router R2. The ISG50 routes most traffic from A to the Internet through the appropriate interface or VPN ...ISG R3 R2 Note: You can generally just use RIP or OSPF to propagate routing information to other routers. 14.1.1 What You Can Do in order to send packets through the ISG50's default gateway (R1). For example, the next figure shows a computer (A) connected to services offered...