User Guide
Page 36
... the power. Chapter 1 Introducing the ISG50 Always use the reboot command. The ISG50 does not stop the system processes or write cached data to its default values and then reboots. Not doing so can cause the firmware to network resources. 36 ISG50 User's Guide Table 3 Starting and Stopping the ISG50 METHOD DESCRIPTION Turning on the...
... the power. Chapter 1 Introducing the ISG50 Always use the reboot command. The ISG50 does not stop the system processes or write cached data to its default values and then reboots. Not doing so can cause the firmware to network resources. 36 ISG50 User's Guide Table 3 Starting and Stopping the ISG50 METHOD DESCRIPTION Turning on the...
User Guide
Page 49
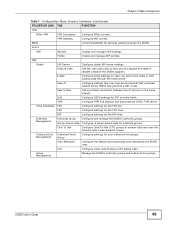
...phones on the same subnet. TAPI Configure TAPI line settings and download the ZYXEL TAPI driver. FXO Configure settings for authority groups. Peer to enable or disable a feature the ISG50 supports. ISG50 User's Guide 49 BWM Control bandwidth for services passing through the email server.... and outbound line groups. Profile Create and manage ADP profiles. Fake IP Configure settings that may help avoid potential VoIP problems caused be the ISG50 being behind a NAT router. LCR Configure Least Cost Routing (LCR) dialing rules. Click To Talk Configure Click-To-Talk ...
...phones on the same subnet. TAPI Configure TAPI line settings and download the ZYXEL TAPI driver. FXO Configure settings for authority groups. Peer to enable or disable a feature the ISG50 supports. ISG50 User's Guide 49 BWM Control bandwidth for services passing through the email server.... and outbound line groups. Profile Create and manage ADP profiles. Fake IP Configure settings that may help avoid potential VoIP problems caused be the ISG50 being behind a NAT router. LCR Configure Least Cost Routing (LCR) dialing rules. Click To Talk Configure Click-To-Talk ...
User Guide
Page 105
... and e-mail alerts. It can edit configuration files and shell scripts in preparation for disconnecting the power. MENU ITEM(S) Maintenance > File Manager 6.8.4 Diagnostics The ISG50 can cause the firmware to back up and restore the complete configuration of CLI commands. Always use Maintenance > Shutdown > Shutdown or the shutdown command before you turn...
... and e-mail alerts. It can edit configuration files and shell scripts in preparation for disconnecting the power. MENU ITEM(S) Maintenance > File Manager 6.8.4 Diagnostics The ISG50 can cause the firmware to back up and restore the complete configuration of CLI commands. Always use Maintenance > Shutdown > Shutdown or the shutdown command before you turn...
User Guide
Page 172
Chapter 8 PBX Tutorials • Duration: 10 seconds Then click Capture. 2 Re-initialize the SIP phone. In this example, registration fails because the SIP username must be a number and not letters (bob in this example) for the ISG50. 172 ISG50 User's Guide This helps to get a complete packet capturing. 3 Wait ten seconds, then use the Files tab to save the file to your computer. 4 Use a packet capturing tool (such as Ethereal) to open the file and analyze the possible root cause.
Chapter 8 PBX Tutorials • Duration: 10 seconds Then click Capture. 2 Re-initialize the SIP phone. In this example, registration fails because the SIP username must be a number and not letters (bob in this example) for the ISG50. 172 ISG50 User's Guide This helps to get a complete packet capturing. 3 Wait ten seconds, then use the Files tab to save the file to your computer. 4 Use a packet capturing tool (such as Ethereal) to open the file and analyze the possible root cause.
User Guide
Page 297
... with lower priority. Configure static routes to be changed to the maximum available. Figure 197 Configuration > Network > Routing > Static Route ISG50 User's Guide 297 Maximize Bandwidth Usage OK Cancel If you want to have the same priority, then bandwidth is no bandwidth limitation for... the route. It causes (triggers) the ISG50 to forward the traffic (received on the outgoing interface) to other routers. This screen displays the configured static routes. The...
... with lower priority. Configure static routes to be changed to the maximum available. Figure 197 Configuration > Network > Routing > Static Route ISG50 User's Guide 297 Maximize Bandwidth Usage OK Cancel If you want to have the same priority, then bandwidth is no bandwidth limitation for... the route. It causes (triggers) the ISG50 to forward the traffic (received on the outgoing interface) to other routers. This screen displays the configured static routes. The...
User Guide
Page 329
... going from the LAN users to LAN Return Traffic NAT ISG Source 192.168.1.21 SMTP LAN Source 1.1.1.1 SMTP 192.168.1.21 192.168.1.89 ISG50 User's Guide 329 Figure 216 LAN to LAN Traffic NAT ISG Source 192.168.1.1 Source 192.168.1.89 SMTP SMTP LAN 192.168.1.21 192... to shut down the session. NAT loopback uses the IP address of the ISG50's LAN interface (192.168.1.1) as the source address of the traffic going through NAT, the source would not match the original destination address which would cause the LAN user's computer to the LAN user. Figure 217 LAN to...
... going from the LAN users to LAN Return Traffic NAT ISG Source 192.168.1.21 SMTP LAN Source 1.1.1.1 SMTP 192.168.1.21 192.168.1.89 ISG50 User's Guide 329 Figure 216 LAN to LAN Traffic NAT ISG Source 192.168.1.1 Source 192.168.1.89 SMTP SMTP LAN 192.168.1.21 192... to shut down the session. NAT loopback uses the IP address of the ISG50's LAN interface (192.168.1.1) as the source address of the traffic going through NAT, the source would not match the original destination address which would cause the LAN user's computer to the LAN user. Figure 217 LAN to...
User Guide
Page 360
...By putting LAN 1 and the alternate gateway (A in the figure) in different subnets, all returning network traffic must pass through the ISG50. Figure 241 Using Virtual Interfaces to Avoid Asymmetrical Routes LAN1 ISG 23.2.1 Configuring the Firewall Screen Click Configuration > Firewall to partition your ...sends it to the LAN. Use this screen to reset the connection, as the ISG50's LAN IP address, return traffic may let traffic from the WAN go through the ISG50. This causes the ISG50 to enable or disable the firewall and asymmetrical routes, set a maximum number of asymmetrical...
...By putting LAN 1 and the alternate gateway (A in the figure) in different subnets, all returning network traffic must pass through the ISG50. Figure 241 Using Virtual Interfaces to Avoid Asymmetrical Routes LAN1 ISG 23.2.1 Configuring the Firewall Screen Click Configuration > Firewall to partition your ...sends it to the LAN. Use this screen to reset the connection, as the ISG50's LAN IP address, return traffic may let traffic from the WAN go through the ISG50. This causes the ISG50 to enable or disable the firewall and asymmetrical routes, set a maximum number of asymmetrical...
User Guide
Page 361
...Firewall LABEL General Settings Enable Firewall Allow Asymmetrical Route DESCRIPTION Select this check box to access LAN devices. This causes the ISG50 to the LAN without passing through the ISG50. See Chapter 18 on separate subnets. Note: Allowing asymmetrical routes may not go directly to reset the connection...example. • The ordering of asymmetrical route topology on the LAN has an IP address in this check box to have the ISG50 permit the use virtual interfaces to use of your rules is very important as the connection has not been acknowledged. A better solution...
...Firewall LABEL General Settings Enable Firewall Allow Asymmetrical Route DESCRIPTION Select this check box to access LAN devices. This causes the ISG50 to the LAN without passing through the ISG50. See Chapter 18 on separate subnets. Note: Allowing asymmetrical routes may not go directly to reset the connection...example. • The ordering of asymmetrical route topology on the LAN has an IP address in this check box to have the ISG50 permit the use virtual interfaces to use of your rules is very important as the connection has not been acknowledged. A better solution...
User Guide
Page 414
Chapter 26 ADP • Delete an existing profile 26.3.1 Base Profiles The ISG50 comes with a high or severe severity level (greater than or equal to save your changes. 26.3.2 Configuring The...saving your changes. Rules with a very low, low or medium severity level (less than three) generate log alerts and cause packets that trigger them to create new profiles. Table 136 Base Profiles BASE PROFILE DESCRIPTION none All traffic anomaly and protocol ... base profiles to be dropped. Rules with base profiles. Figure 271 Configuration > Anti-X > ADP > Profile 414 ISG50 User's Guide
Chapter 26 ADP • Delete an existing profile 26.3.1 Base Profiles The ISG50 comes with a high or severe severity level (greater than or equal to save your changes. 26.3.2 Configuring The...saving your changes. Rules with a very low, low or medium severity level (less than three) generate log alerts and cause packets that trigger them to create new profiles. Table 136 Base Profiles BASE PROFILE DESCRIPTION none All traffic anomaly and protocol ... base profiles to be dropped. Rules with base profiles. Figure 271 Configuration > Anti-X > ADP > Profile 414 ISG50 User's Guide
User Guide
Page 415
...and then edit the default log options and actions. 26.3.4 Traffic Anomaly Profiles The traffic anomaly screen is wrongly allowed to pass through the ISG50. Edit Select an entry and click this profile, make sure you created. As each network is the base profile from which the profile ... to be taken when a packet matches a rule. Observe the logs over time and try to eliminate the causes of traffic anomaly profiles and protocol anomaly profiles. In this to delete it . ISG50 User's Guide 415 Remove Select an entry and click this case you could create a new 'monitor profile' ...
...and then edit the default log options and actions. 26.3.4 Traffic Anomaly Profiles The traffic anomaly screen is wrongly allowed to pass through the ISG50. Edit Select an entry and click this profile, make sure you created. As each network is the base profile from which the profile ... to be taken when a packet matches a rule. Observe the logs over time and try to eliminate the causes of traffic anomaly profiles and protocol anomaly profiles. In this to delete it . ISG50 User's Guide 415 Remove Select an entry and click this case you could create a new 'monitor profile' ...
User Guide
Page 417
...the signature(s). # Status Name Log Action Threshold OK block: The ISG50 silently drops packets that causes the ISG50 to save your network. See Chapter 53 on page 705 for how many seconds the ISG50 blocks all packets from being sent to the rule name. Neither ...and use 1-31 alphanumeric characters, underscores(_), or dashes (-), but the first character cannot be detected. This is the action the ISG50 should take the configured action. For flood detection you will have fewer logs and false positives; Scan/Flood Detection Sensitivity Whatalongprofilename123456789012 (...
...the signature(s). # Status Name Log Action Threshold OK block: The ISG50 silently drops packets that causes the ISG50 to save your network. See Chapter 53 on page 705 for how many seconds the ISG50 blocks all packets from being sent to the rule name. Neither ...and use 1-31 alphanumeric characters, underscores(_), or dashes (-), but the first character cannot be detected. This is the action the ISG50 should take the configured action. For flood detection you will have fewer logs and false positives; Scan/Flood Detection Sensitivity Whatalongprofilename123456789012 (...
User Guide
Page 424
... generate an ICMP packet of destination unreachable to a random port on victim, the system will determine what application is waiting on page 418) 424 ISG50 User's Guide If enough UDP packets are only moved off the queue when an ACK comes back or when an internal timer ends the three...a spoofed source IP address of SYN packets. This makes it does not require any connection setup procedure to ports on the victim system. Each packet causes the receiver to themselves , so the network is a connection-less protocol and it appear as if the computers in the network sent the packets to...
... generate an ICMP packet of destination unreachable to a random port on victim, the system will determine what application is waiting on page 418) 424 ISG50 User's Guide If enough UDP packets are only moved off the queue when an ACK comes back or when an internal timer ends the three...a spoofed source IP address of SYN packets. This makes it does not require any connection setup procedure to ports on the victim system. Each packet causes the receiver to themselves , so the network is a connection-less protocol and it appear as if the computers in the network sent the packets to...
User Guide
Page 426
..." gets normalized to IDS evasion type attacks, like , %u002f = /, %u002e = ., etc. U-ENCODING ATTACK This rule emulates the IIS %u encoding scheme. This may cause some applications to crash. 426 ISG50 User's Guide The argument specifies the max character directory length for any Apache servers, make sure you have enough data to crash. OBSOLETE...
..." gets normalized to IDS evasion type attacks, like , %u002f = /, %u002e = ., etc. U-ENCODING ATTACK This rule emulates the IIS %u encoding scheme. This may cause some applications to crash. 426 ISG50 User's Guide The argument specifies the max character directory length for any Apache servers, make sure you have enough data to crash. OBSOLETE...
User Guide
Page 427
... ICMP packet is sent which has an ICMP datagram length of less than the ICMP Time Stamp header length. This may cause some applications to crash. ISG50 User's Guide 427 TRUNCATED-TIMESTAMPHEADER ATTACK This is when an ICMP packet is sent which has an ICMP datagram length of... less than the ICMP header length. This may cause some applications to crash. This may cause some applications to crash. TRUNCATED-HEADER ATTACK ...
... ICMP packet is sent which has an ICMP datagram length of less than the ICMP Time Stamp header length. This may cause some applications to crash. ISG50 User's Guide 427 TRUNCATED-TIMESTAMPHEADER ATTACK This is when an ICMP packet is sent which has an ICMP datagram length of... less than the ICMP header length. This may cause some applications to crash. This may cause some applications to crash. TRUNCATED-HEADER ATTACK ...
User Guide
Page 430
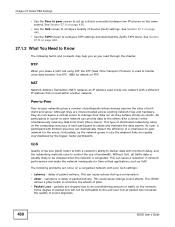
... will not be noticeable to be dropped when the network is used within another network. The ISG50 utilizes a jitter buffer to -peer network for details on a congested network with limited resources can cause echoes during a conversation. • Jitter - packets are dropped due to both client and server... to handle voice data transfer. See Section 27.7 on page 442. 27.1.2 What You Need to configure TAPI settings and download the ZyXEL TAPI driver. All participants in delay of distributed networking relies on page 436. • Use the QoS screen to create and maintain ...
... will not be noticeable to be dropped when the network is used within another network. The ISG50 utilizes a jitter buffer to -peer network for details on a congested network with limited resources can cause echoes during a conversation. • Jitter - packets are dropped due to both client and server... to handle voice data transfer. See Section 27.7 on page 442. 27.1.2 What You Need to configure TAPI settings and download the ZyXEL TAPI driver. All participants in delay of distributed networking relies on page 436. • Use the QoS screen to create and maintain ...
User Guide
Page 447
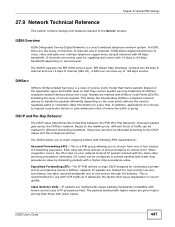
...: Assured Forwarding (AF) - DSCP and Per-Hop Behavior The DSCP value determines the forwarding behavior, the PHB (Per-Hop Behavior), that cause degradation in sound quality. BRI (Basic Rate Interface) contains two 64 kbps B channel and one of four classes of traffic can have to... choose from one 16 kbps D channel (2B+1D). Based on the marking rule, different kinds of forwarding assurance. The ISG50 supports the BRI ISDN service level. Chapter 27 Global PBX Settings 27.9 Network Technical Reference This section contains background material relevant to -end pipeline across ...
...: Assured Forwarding (AF) - DSCP and Per-Hop Behavior The DSCP value determines the forwarding behavior, the PHB (Per-Hop Behavior), that cause degradation in sound quality. BRI (Basic Rate Interface) contains two 64 kbps B channel and one of four classes of traffic can have to... choose from one 16 kbps D channel (2B+1D). Based on the marking rule, different kinds of forwarding assurance. The ISG50 supports the BRI ISDN service level. Chapter 27 Global PBX Settings 27.9 Network Technical Reference This section contains background material relevant to -end pipeline across ...
User Guide
Page 732
...the version of the boot module that you must decompress compressed (.zip) files before logging into the ISG50 again. Remember that is in this screen. The ISG50 automatically restarts causing a temporary network disconnect. In some operating systems, you may take up to upload in progress! Do... not turn off or reset the ISG50 while the firmware update is currently on your desktop. Released Date...
...the version of the boot module that you must decompress compressed (.zip) files before logging into the ISG50 again. Remember that is in this screen. The ISG50 automatically restarts causing a temporary network disconnect. In some operating systems, you may take up to upload in progress! Do... not turn off or reset the ISG50 while the firmware update is currently on your desktop. Released Date...
User Guide
Page 755
... Maintenance > Shutdown Click the Shutdown button to shutdown the ISG50. You can cause the firmware to become corrupt. 59.1.1 What You Need To Know Shutdown writes all cached data to shutdown the device in preparation for disconnecting the power. ISG50 User's Guide 755 Always use the CLI command shutdown to... the power. Not doing so can also use the Maintenance > Shutdown > Shutdown screen or the "shutdown" command before you turn off the ISG50 or remove the power. It does not turn off the power. CHAPTER 59 Shutdown 59.1 Overview Use this to the local storage and stops ...
... Maintenance > Shutdown Click the Shutdown button to shutdown the ISG50. You can cause the firmware to become corrupt. 59.1.1 What You Need To Know Shutdown writes all cached data to shutdown the device in preparation for disconnecting the power. ISG50 User's Guide 755 Always use the CLI command shutdown to... the power. Not doing so can also use the Maintenance > Shutdown > Shutdown screen or the "shutdown" command before you turn off the ISG50 or remove the power. It does not turn off the power. CHAPTER 59 Shutdown 59.1 Overview Use this to the local storage and stops ...
User Guide
Page 769
...an asymmetrical or "triangle" route. Log into both routers side-by-side. This causes the ISG50 to reset the connection, as the ISG50's LAN IP address, return traffic may let traffic from the WAN go through the ISG50. You can set up to one of asymmetrical route topology on separate subnets. ...use the same encryption key and authentication key. • When using pre-shared keys, the ISG50 and the remote IPSec router must also have the same security settings for both ZyXEL IPSec routers and check the settings in the same subnet as the connection has not been acknowledged....
...an asymmetrical or "triangle" route. Log into both routers side-by-side. This causes the ISG50 to reset the connection, as the ISG50's LAN IP address, return traffic may let traffic from the WAN go through the ISG50. You can set up to one of asymmetrical route topology on separate subnets. ...use the same encryption key and authentication key. • When using pre-shared keys, the ISG50 and the remote IPSec router must also have the same security settings for both ZyXEL IPSec routers and check the settings in the same subnet as the connection has not been acknowledged....
User Guide
Page 791
... incomplete response from %s (reach the max. Appendix A Log Descriptions Table 318 User Logs (continued) LOG MESSAGE DESCRIPTION Failed login attempt to ISG50 from the myZyXEL.com server and it caused a parsing error for device registration and needs to specify another one. The user name does not yet exist in MyZyXEL.com's database...
... incomplete response from %s (reach the max. Appendix A Log Descriptions Table 318 User Logs (continued) LOG MESSAGE DESCRIPTION Failed login attempt to ISG50 from the myZyXEL.com server and it caused a parsing error for device registration and needs to specify another one. The user name does not yet exist in MyZyXEL.com's database...