Design Guide
Page 3
...of Copier/Document Server Features 45 2-1-6 Restricting the Available Functions for Increased Security 42 2. Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for ...Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2...
...of Copier/Document Server Features 45 2-1-6 Restricting the Available Functions for Increased Security 42 2. Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for ...Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2...
Design Guide
Page 6
... MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 9060 9060sp 9070 9070sp 9080 9080sp 9090 9090sp MLP37N Note: Some of the hardware (e.g. Page 6 of image data and other information handled internally by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes...
... MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 9060 9060sp 9070 9070sp 9080 9080sp 9090 9090sp MLP37N Note: Some of the hardware (e.g. Page 6 of image data and other information handled internally by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes...
Design Guide
Page 12
... Information Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) Manages ...as well ass the forwarding of 86 Also receives FAX data and prints it out from the printing engine. Print Controller Design Guide for access control, is handled from the operation panel. diagnostics, firmware update, settings changes). Controls the MFP/LP's access logs...
... Information Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) Manages ...as well ass the forwarding of 86 Also receives FAX data and prints it out from the printing engine. Print Controller Design Guide for access control, is handled from the operation panel. diagnostics, firmware update, settings changes). Controls the MFP/LP's access logs...
Design Guide
Page 13
...that allows machine configuration settings to change some MFP/LP functionality to function with the MFP/LP. SDK: Applications provided by Ricoh. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS provides some of the internal settings... of the external controller from the MFP operation panel. This includes the ability to view and make changes to user information and ...
...that allows machine configuration settings to change some MFP/LP functionality to function with the MFP/LP. SDK: Applications provided by Ricoh. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS provides some of the internal settings... of the external controller from the MFP operation panel. This includes the ability to view and make changes to user information and ...
Design Guide
Page 14
Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with ...an outside this data from Illegal Access via an external I /F), which ensures that the data stored in the MFP/LP itself. User data, such as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX...arrangement ensures that the data can function as the Address Book data stored in the HDD/flash ROM and User Code data stored in the NV-RAM, is managed by specified machine function(s). This arrangement prevents illegal ...
Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with ...an outside this data from Illegal Access via an external I /F), which ensures that the data stored in the MFP/LP itself. User data, such as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX...arrangement ensures that the data can function as the Address Book data stored in the HDD/flash ROM and User Code data stored in the NV-RAM, is managed by specified machine function(s). This arrangement prevents illegal ...
Design Guide
Page 15
...from any of the image data stored in #4 above . In addition, using Ricoh-unique protocols. PictBridge printing functions (color MFP/LPs only): After the identity of 86 In addition, if User Authentication has been enabled, the machine will judge that a perhiperal device failure ... I/F (Type B), and Bluetooth I /F (Type A) only allows connection with the same protocols used for executing printing operations. Print Controller Design Guide for @Remote operations is not possible. This prevents any illegal access to the MFP via the network to pre-determined commands and data, and ...
...from any of the image data stored in #4 above . In addition, using Ricoh-unique protocols. PictBridge printing functions (color MFP/LPs only): After the identity of 86 In addition, if User Authentication has been enabled, the machine will judge that a perhiperal device failure ... I/F (Type B), and Bluetooth I /F (Type A) only allows connection with the same protocols used for executing printing operations. Print Controller Design Guide for @Remote operations is not possible. This prevents any illegal access to the MFP via the network to pre-determined commands and data, and ...
Design Guide
Page 18
... by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. The update is performed by a field engineer in ... three main scenarios in the field via Web SmartDeviceMonitor Professional IS, usually by the end user 1. Decryption Public key MD2 8. Compare MD and MD2 6. Firmware is overwritten with...18 of model and target machine functions (Copier, Printer, etc.) 3. Print Controller Design Guide for Information Security Remote Firmware Update In addition to using an SD card, it is...
... by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. The update is performed by a field engineer in ... three main scenarios in the field via Web SmartDeviceMonitor Professional IS, usually by the end user 1. Decryption Public key MD2 8. Compare MD and MD2 6. Firmware is overwritten with...18 of model and target machine functions (Copier, Printer, etc.) 3. Print Controller Design Guide for Information Security Remote Firmware Update In addition to using an SD card, it is...
Design Guide
Page 19
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Design Guide
Page 20
...programs/firmware mentioned above: RTM (Root Trust of Measurement) is used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are given access to validate the controller core programs, which makes it extremely difficult for... newly installed as updates through the process explained in any alterations made to these keys. Page 20 of 86 Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to judge its validity.
...programs/firmware mentioned above: RTM (Root Trust of Measurement) is used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are given access to validate the controller core programs, which makes it extremely difficult for... newly installed as updates through the process explained in any alterations made to these keys. Page 20 of 86 Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to judge its validity.
Design Guide
Page 21
... be used for Windows Authentication, and an LDAP server can be performed. There are five types of User Authentication: Basic Authentication User Code Authentication Windows Authentication LDAP Authentication Integration Server Authentication As the authentication server, the MFP/LP can be...to make the 32-character limit more difficult to surmise. Print Controller Design Guide for Information Security 1-5 Authentication, Access Control 1-5-1 Authentication When enabled, User Authentication requires all users to go through a username and password-based authentication process before MFP/LP ...
... be used for Windows Authentication, and an LDAP server can be performed. There are five types of User Authentication: Basic Authentication User Code Authentication Windows Authentication LDAP Authentication Integration Server Authentication As the authentication server, the MFP/LP can be...to make the 32-character limit more difficult to surmise. Print Controller Design Guide for Information Security 1-5 Authentication, Access Control 1-5-1 Authentication When enabled, User Authentication requires all users to go through a username and password-based authentication process before MFP/LP ...
Design Guide
Page 22
... automatically lock out any consecutive failed authentication attempts, the MFP/LP will delay its response. When users log in the MFP/LP. The e-mail address, FAX number and GUID are destroyed as soon as well, after which an LDAP search is encrypted using an encryption key...servers is always possible to perform authentication on administrators even when a failure occurs with the active directory. Print Controller Design Guide for any user if the number of failed login attempts by the MFP/LP), and to Administrator accounts authenticated through Basic Authentication (performed by ...
... automatically lock out any consecutive failed authentication attempts, the MFP/LP will delay its response. When users log in the MFP/LP. The e-mail address, FAX number and GUID are destroyed as soon as well, after which an LDAP search is encrypted using an encryption key...servers is always possible to perform authentication on administrators even when a failure occurs with the active directory. Print Controller Design Guide for any user if the number of failed login attempts by the MFP/LP), and to Administrator accounts authenticated through Basic Authentication (performed by ...
Design Guide
Page 23
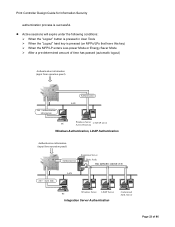
...LDAP server Active Directory Windows Authentication, LDAP Authentication Authentication information (input from operation panel) Job + Auth. Print Controller Design Guide for Information Security authentication process is selected (1-4) [1] [2] [3] [4] Windows Server LDAP Server PC Integration Server Authentication Customized Auth.... Active sessions will expire under the following conditions: When the "Logout" button is pressed in User Tools When the "Logout" hard key is pressed (on MFPs/LPs that have this key) When the MFP/LP enters...
...LDAP server Active Directory Windows Authentication, LDAP Authentication Authentication information (input from operation panel) Job + Auth. Print Controller Design Guide for Information Security authentication process is selected (1-4) [1] [2] [3] [4] Windows Server LDAP Server PC Integration Server Authentication Customized Auth.... Active sessions will expire under the following conditions: When the "Logout" button is pressed in User Tools When the "Logout" hard key is pressed (on MFPs/LPs that have this key) When the MFP/LP enters...
Design Guide
Page 24
... Controller Design Guide for Information Security 1-5-2 IC Card Authentication Overview IC Card Authentication is provided to the field in the form of 86 If the IC card does not contain a function release code, the CSC simply reads the username and password stored in order to Ricoh specifications. One... server is placed in the reader, if it contains a function release code, the user will be stored to this IC card and then used to install the "ADK" (Authentication ...
... Controller Design Guide for Information Security 1-5-2 IC Card Authentication Overview IC Card Authentication is provided to the field in the form of 86 If the IC card does not contain a function release code, the CSC simply reads the username and password stored in order to Ricoh specifications. One... server is placed in the reader, if it contains a function release code, the user will be stored to this IC card and then used to install the "ADK" (Authentication ...
Design Guide
Page 25
... each principal MFP/LP function can be performed on the address. This is true for global groups as well as individual users. Print Controller Design Guide for Information Security 1-5-3 Access Control Users logged-in as administrators are entered manually as well as the "From" field whenever an e-mail is sent. It is possible...
... each principal MFP/LP function can be performed on the address. This is true for global groups as well as individual users. Print Controller Design Guide for Information Security 1-5-3 Access Control Users logged-in as administrators are entered manually as well as the "From" field whenever an e-mail is sent. It is possible...
Design Guide
Page 26
... able to change the usernames and passwords of other administrators. Print Controller Design Guide for stored documents, and the stored documents themselves. 4. It is always in case any passwords are not able to this information). Page 26 of the user information, document data, and settings stored in the Address Book, as well...
... able to change the usernames and passwords of other administrators. Print Controller Design Guide for stored documents, and the stored documents themselves. 4. It is always in case any passwords are not able to this information). Page 26 of the user information, document data, and settings stored in the Address Book, as well...
Design Guide
Page 27
... value method, a Ricoh-original method which overwrites data using randomly-generated values Note: The DoD and NSA methods automatically perform three passes, using a different set of randomly-generated numbers each time (the number of user information. Before the Data Erase/Overwrite option can be ... the machine will be able to an indecipherable level, leaving the possibility of partial reconstruction of the HDD. Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to function and an ...
... value method, a Ricoh-original method which overwrites data using randomly-generated values Note: The DoD and NSA methods automatically perform three passes, using a different set of randomly-generated numbers each time (the number of user information. Before the Data Erase/Overwrite option can be ... the machine will be able to an indecipherable level, leaving the possibility of partial reconstruction of the HDD. Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to function and an ...
Design Guide
Page 28
...settings contained in addition to third parties (e.g. In addition, it to a PC for purposes of MFP/LP internal processing only, of which users are normally unaware. Erase All Memory This function overwrites the contents of every region of the HDD and initializes the contents of the NVRAM... administrative information). To execute the overwrite, the operator can choose from remaining in the HDD by the MFP/LP. Print Controller Design Guide for Information Security whether or not the option is to automatically overwrite data stored to the processing region of the HDD in between the...
...settings contained in addition to third parties (e.g. In addition, it to a PC for purposes of MFP/LP internal processing only, of which users are normally unaware. Erase All Memory This function overwrites the contents of every region of the HDD and initializes the contents of the NVRAM... administrative information). To execute the overwrite, the operator can choose from remaining in the HDD by the MFP/LP. Print Controller Design Guide for Information Security whether or not the option is to automatically overwrite data stored to the processing region of the HDD in between the...
Design Guide
Page 30
...the operator is changed from that point will not be in this point will not be encrypted with all other error). Print Controller Design Guide for Information Security The encryption described above can only be applied even in cases where the target data has already been encrypted once using the...or an Encryption Key Update is performed, the old data storage keys for the HDD and NVRAM are created for preservation at this way, any user would be encrypted a second time using a separate MFP/LP function. The NVRAM storage key and copy of the encryption keys. See "Encryption Key...
...the operator is changed from that point will not be in this point will not be encrypted with all other error). Print Controller Design Guide for Information Security The encryption described above can only be applied even in cases where the target data has already been encrypted once using the...or an Encryption Key Update is performed, the old data storage keys for the HDD and NVRAM are created for preservation at this way, any user would be encrypted a second time using a separate MFP/LP function. The NVRAM storage key and copy of the encryption keys. See "Encryption Key...
Design Guide
Page 31
... needed in order to the HDD, it still exists inside de-allocated HDD memory, where it will remain until it is overwritten. Print Controller Design Guide for the purpose of the HDD storage key (which is encrypted by a field engineer. Encryption Key Update: This operation allows the operator to replace the... Data Erase/Overwrite option explained in the event that was backed-up key is restored to decrypt the NVRAM back-up of the MFP/LP user.
... needed in order to the HDD, it still exists inside de-allocated HDD memory, where it will remain until it is overwritten. Print Controller Design Guide for the purpose of the HDD storage key (which is encrypted by a field engineer. Encryption Key Update: This operation allows the operator to replace the... Data Erase/Overwrite option explained in the event that was backed-up key is restored to decrypt the NVRAM back-up of the MFP/LP user.
Design Guide
Page 32
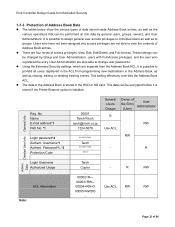
... privileges: View, Edit, Edit/Delete, and Full-Access. No. There are also able to change user passwords. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types...
... privileges: View, Edit, Edit/Delete, and Full-Access. No. There are also able to change user passwords. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types...