Design Guide
Page 3
... 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (MFP Models Only 54 2-3-1 Overview of Scanner Operations 54 2-3-2 Data Flow Security Considerations 54 2-3-3 Protection of Data when Performing Scanning and Sending Operations 55 2-3-4... Protection of Document Server Documents 56 2-3-5 Protection of Sending Results and Status Information 57 2-3-6 Protection of the Scanner Features Settings 57 2-3-7 Data Stored in the Job Log 58 2-3-8 Terminology ...58 2-4 FAX (MFP Models Only 59 2-4-1 ...
... 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (MFP Models Only 54 2-3-1 Overview of Scanner Operations 54 2-3-2 Data Flow Security Considerations 54 2-3-3 Protection of Data when Performing Scanning and Sending Operations 55 2-3-4... Protection of Document Server Documents 56 2-3-5 Protection of Sending Results and Status Information 57 2-3-6 Protection of the Scanner Features Settings 57 2-3-7 Data Stored in the Job Log 58 2-3-8 Terminology ...58 2-4 FAX (MFP Models Only 59 2-4-1 ...
Design Guide
Page 4
... of Operations 77 4-1-1 Installation...78 4-1-2 Overview of SDK Application Functions 79 4-2 Data Flow...80 4-2-1 Scanning Functions: Sending Data Over the Network with the Copier and Scanner Page 4 of Copy Data Security Operations 74 3-2-2 Data Flow...75 4. Optional Features...73 3-1 @Remote...73 3-1-1 Overview of @Remote Operations 73 3-1-2 Data Security Considerations 73 3-2 The...
... of Operations 77 4-1-1 Installation...78 4-1-2 Overview of SDK Application Functions 79 4-2 Data Flow...80 4-2-1 Scanning Functions: Sending Data Over the Network with the Copier and Scanner Page 4 of Copy Data Security Operations 74 3-2-2 Data Flow...75 4. Optional Features...73 3-1 @Remote...73 3-1-1 Overview of @Remote Operations 73 3-1-2 Data Security Considerations 73 3-2 The...
Design Guide
Page 11
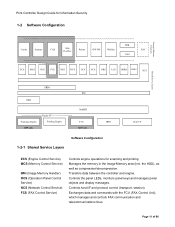
... Memory Handler) OCS (Operation Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service Layers...
... Memory Handler) OCS (Operation Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service Layers...
Design Guide
Page 12
... Activates the scanning engine, which then sends the data to managing hardware resources, this module mediates control of the printer engine, scanner engine and memory resources during the authentication process, as well as a FAX via the host I /F. diagnostics, firmware update,... Also contains a printer language processing subsystem (e.g. Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which is then printed out from the printing engine. counters). Print Controller Design Guide for...
... Activates the scanning engine, which then sends the data to managing hardware resources, this module mediates control of the printer engine, scanner engine and memory resources during the authentication process, as well as a FAX via the host I /F. diagnostics, firmware update,... Also contains a printer language processing subsystem (e.g. Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which is then printed out from the printing engine. counters). Print Controller Design Guide for...
Design Guide
Page 22
... by the MFP/LP), and to a value from the server. The same NTLM Authentication process is performed for environments that do this, however, the Printer/Scanner option must be installed.To protect against the password policy. The communication path can be encrypted using an encryption key specified by that user exceeds...
... by the MFP/LP), and to a value from the server. The same NTLM Authentication process is performed for environments that do this, however, the Printer/Scanner option must be installed.To protect against the password policy. The communication path can be encrypted using an encryption key specified by that user exceeds...
Design Guide
Page 32
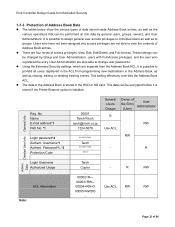
... Info. There are not able to groups. User Administrators are separate from the Address Book ACL, it is stored if the Printer/Scanner option is possible to assign general user access privileges to individual users as well as to view the contents of Address Book entries....able to prohibit all users registered in the ACL from programming new destinations in the HDD or SD card. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 ACL Information Note: Taroh Copier - R RW ... 00002=R--- 00003...
... Info. There are not able to groups. User Administrators are separate from the Address Book ACL, it is stored if the Printer/Scanner option is possible to assign general user access privileges to individual users as well as to view the contents of Address Book entries....able to prohibit all users registered in the ACL from programming new destinations in the HDD or SD card. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 ACL Information Note: Taroh Copier - R RW ... 00002=R--- 00003...
Design Guide
Page 40
... Transmission of LAN FAX file stored in HDD Printer Printing out of LAN FAX transmission file stored in HDD File printed out with Remote Print Scanner Desk Top Editor For Production Forwarding Forwarding + storage to HDD Storage of scanned image Forwarding of stored file Restoring a previously downloaded file from Desk Top...
... Transmission of LAN FAX file stored in HDD Printer Printing out of LAN FAX transmission file stored in HDD File printed out with Remote Print Scanner Desk Top Editor For Production Forwarding Forwarding + storage to HDD Storage of scanned image Forwarding of stored file Restoring a previously downloaded file from Desk Top...
Design Guide
Page 54
...viewed directly from a network-connected client PC, after which the image is sent back to the TWAIN driver. • Access to the Scanner function itself (SMTP authentication). • When sending image data to pre-programmed e-mail addresses, folders and forwarding servers only. the data .... • Operational log entries are created for both scanning and forwarding jobs. Use of User Authentication, the Available Functions settings for the Scanner function to receive any illegal data from an external interface. • When sending image data to an SMTP server, it is possible to ...
...viewed directly from a network-connected client PC, after which the image is sent back to the TWAIN driver. • Access to the Scanner function itself (SMTP authentication). • When sending image data to pre-programmed e-mail addresses, folders and forwarding servers only. the data .... • Operational log entries are created for both scanning and forwarding jobs. Use of User Authentication, the Available Functions settings for the Scanner function to receive any illegal data from an external interface. • When sending image data to an SMTP server, it is possible to ...
Design Guide
Page 55
... 86 If this user is either able to obtain shared Address Book data only (Basic Authentication disabled, all other cases, the MFP Scanner is automatically set the necessary authentication information in the authentication tool that it is possible to set the MFP or related software to retrieve...by unauthorized senders. - By requiring the operator to select from an LDAP server or entered manually. • In order for the MFP Scanner to an SMTP server or folder (Basic Authentication). Require user ID and password authentication before data is forwarded to retrieve the address book data...
... 86 If this user is either able to obtain shared Address Book data only (Basic Authentication disabled, all other cases, the MFP Scanner is automatically set the necessary authentication information in the authentication tool that it is possible to set the MFP or related software to retrieve...by unauthorized senders. - By requiring the operator to select from an LDAP server or entered manually. • In order for the MFP Scanner to an SMTP server or folder (Basic Authentication). Require user ID and password authentication before data is forwarded to retrieve the address book data...
Design Guide
Page 56
... privileges can interrupt a scanning job in from DeskTopBinder or Desk Top Editor For Production. However since User Administrators cannot use the Scanner function, they are not able to the access privileges settings. Users who have View privileges for all functions including previewing, sending,... forwarding, but cannot delete or make any data. Even when all registered documents. However since User Administrators cannot use the Scanner function, they are not even able to individual documents when scanning them for storage in which one operator can select the ...
... privileges can interrupt a scanning job in from DeskTopBinder or Desk Top Editor For Production. However since User Administrators cannot use the Scanner function, they are not able to the access privileges settings. Users who have View privileges for all functions including previewing, sending,... forwarding, but cannot delete or make any data. Even when all registered documents. However since User Administrators cannot use the Scanner function, they are not even able to individual documents when scanning them for storage in which one operator can select the ...
Design Guide
Page 57
...the sending results log is automatically printed out when the maximum number of entries has been reached. With a setting of the Scanner Features Settings • When User Authentication or Administrator Authentication is enabled, users and administrators must be authenticated before they performed. ...assign a password to a document once the password check for that document fails. Additionally, when the Document Lock feature in Scanner Features. Only the Document Administrator can only be deleted by Network Administrators, it is entered. This prevents operations from the Page...
...the sending results log is automatically printed out when the maximum number of entries has been reached. With a setting of the Scanner Features Settings • When User Authentication or Administrator Authentication is enabled, users and administrators must be authenticated before they performed. ...assign a password to a document once the password check for that document fails. Additionally, when the Document Lock feature in Scanner Features. Only the Document Administrator can only be deleted by Network Administrators, it is entered. This prevents operations from the Page...
Design Guide
Page 59
... through the network to send the file to the other party's machine via a telecommunications line or network I /F. Conversely, the MFP will be issued from the scanner engine to its destination via a telecommunications line as with a JPEG or PDF file attached, the file will only accept incoming FAX data that conforms to...
... through the network to send the file to the other party's machine via a telecommunications line or network I /F. Conversely, the MFP will be issued from the scanner engine to its destination via a telecommunications line as with a JPEG or PDF file attached, the file will only accept incoming FAX data that conforms to...
Design Guide
Page 61
... possible to register a list of unauthorized senders, so that the MFP only accepts incoming data from these senders. • For more details, please refer to 2.3 Scanner (MFP Models Only). 2-4-3 Protection of the Journal and Documents in the MFP. • It is possible to assign access restrictions to individual Document Server documents...
... possible to register a list of unauthorized senders, so that the MFP only accepts incoming data from these senders. • For more details, please refer to 2.3 Scanner (MFP Models Only). 2-4-3 Protection of the Journal and Documents in the MFP. • It is possible to assign access restrictions to individual Document Server documents...
Design Guide
Page 64
... For Production. In addition, it is possible to change a portion of the System Settings that were stored using the Copier, FAX and Scanner functions or those stored using the Scanner function to be forwarded to , deleted, and changed from one . Page 64 of NetFile Operations • NetFile operates via communication with a password...
... For Production. In addition, it is possible to change a portion of the System Settings that were stored using the Copier, FAX and Scanner functions or those stored using the Scanner function to be forwarded to , deleted, and changed from one . Page 64 of NetFile Operations • NetFile operates via communication with a password...
Design Guide
Page 65
...a Document Server file - Page 65 of pre-issued User Authentication Tickets, users can access the contents from DeskTopBinder on a Scanner Document Server file - Print Controller Design Guide for Information Security Transferring Job Log and Access Log Data to Web SmartDeviceMonitor Professional... Professional IS, it is possible to Web SmartDeviceMonitor Professional IS whenever any individual print job sent from DeskTopBinder on a Scanner Document Server file - A sending/forwarding job is initiated. However with an administrator-level User Account in section 1.9, ...
...a Document Server file - Page 65 of pre-issued User Authentication Tickets, users can access the contents from DeskTopBinder on a Scanner Document Server file - Print Controller Design Guide for Information Security Transferring Job Log and Access Log Data to Web SmartDeviceMonitor Professional... Professional IS, it is possible to Web SmartDeviceMonitor Professional IS whenever any individual print job sent from DeskTopBinder on a Scanner Document Server file - A sending/forwarding job is initiated. However with an administrator-level User Account in section 1.9, ...
Design Guide
Page 70
... session hijacks: The session ID is randomized, which makes it is disabled, it very difficult for third parties to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. In addition, the session ID is given an expiration date, minimizing any settings can be changed by...
... session hijacks: The session ID is randomized, which makes it is disabled, it very difficult for third parties to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. In addition, the session ID is given an expiration date, minimizing any settings can be changed by...
Design Guide
Page 71
... the specific operations requested. Additionally, it is possible to limit the conditions under which WebDocBox sends commands to perform the remote operations. When transmitting stored Scanner files as e-mail attachments, using the same ACL mentioned in accordance with no additional access attempts from the Web browser, after which remote operations can...
... the specific operations requested. Additionally, it is possible to limit the conditions under which WebDocBox sends commands to perform the remote operations. When transmitting stored Scanner files as e-mail attachments, using the same ACL mentioned in accordance with no additional access attempts from the Web browser, after which remote operations can...
Design Guide
Page 74
...to the access log, along with vertical line pattern: If a user then attempts to make a copy of the relevant MFP functions: Copier, Scanner, and FAX. Detection, replacing image with the date, time and username. Then, on the printout, the original image is installed on that copying... of Copy Data Security Operations The Copy Data Security feature acts to discourage unauthorized copying of the selected pattern on the original image. non-Ricoh products) on which to the Document Server. Detecting the pattern if a copy is attempted, and then replacing the image with a vertical ...
...to the access log, along with vertical line pattern: If a user then attempts to make a copy of the relevant MFP functions: Copier, Scanner, and FAX. Detection, replacing image with the date, time and username. Then, on the printout, the original image is installed on that copying... of Copy Data Security Operations The Copy Data Security feature acts to discourage unauthorized copying of the selected pattern on the original image. non-Ricoh products) on which to the Document Server. Detecting the pattern if a copy is attempted, and then replacing the image with a vertical ...
Design Guide
Page 80
For an overview of the MFP Copier and Scanner. The Image Library is a static library, and is converted to TIFF format and then sent to its destination. The image data is read out of HDD memory and then converted from Ricoh-original format to Unix FFS (Fast File System) format. With FAX... HDD when "Store Incoming Faxes" is able to access the file and retrieve it is contained within the SD card along with the Copier and Scanner (MFP models only) DSDK applications are initiated (e.g. When sending a scanned image stored in the MFP HDD, and then transfer them to DeskTopBinder or Desk...
For an overview of the MFP Copier and Scanner. The Image Library is a static library, and is converted to TIFF format and then sent to its destination. The image data is read out of HDD memory and then converted from Ricoh-original format to Unix FFS (Fast File System) format. With FAX... HDD when "Store Incoming Faxes" is able to access the file and retrieve it is contained within the SD card along with the Copier and Scanner (MFP models only) DSDK applications are initiated (e.g. When sending a scanned image stored in the MFP HDD, and then transfer them to DeskTopBinder or Desk...