User Guide
Page 10
...or they will return the document feeder to the touch, Attachments such as shown in the image Adjust the Side Guide flush against the right side guide . Ensure that all originals are multiple paper sizes you must all the sizes in different paper trays, or select the...189;" x14" ; 8½" x 11" ;5½" x 8½" Selecting Duplexing must either have all be clean and feel dry to normal copy mode ready for the next user. Check the condition of the paper stack: All sheets should lie flat, with no curled or bent edges, Paper should be output on...
...or they will return the document feeder to the touch, Attachments such as shown in the image Adjust the Side Guide flush against the right side guide . Ensure that all originals are multiple paper sizes you must all the sizes in different paper trays, or select the...189;" x14" ; 8½" x 11" ;5½" x 8½" Selecting Duplexing must either have all be clean and feel dry to normal copy mode ready for the next user. Check the condition of the paper stack: All sheets should lie flat, with no curled or bent edges, Paper should be output on...
Operating Instructions
Page 8
...• Adobe Acrobat Reader/Adobe Reader must be installed in order to view the html manuals. Also explains how to change User Tools settings and how to register information in a network environment, and use the software provided. It explains security functions that you... to install the CD-ROMs provided, and how to this machine. This manual introduces the machine's various functions. Troubleshooting Provides a guide for resolving common usage-related problems. Copy and Document Server Reference Explains Copier and Document Server functions and operations. Also refer to replace...
...• Adobe Acrobat Reader/Adobe Reader must be installed in order to view the html manuals. Also explains how to change User Tools settings and how to register information in a network environment, and use the software provided. It explains security functions that you... to install the CD-ROMs provided, and how to this machine. This manual introduces the machine's various functions. Troubleshooting Provides a guide for resolving common usage-related problems. Copy and Document Server Reference Explains Copier and Document Server functions and operations. Also refer to replace...
Operating Instructions
Page 9
... UNIX Supplement • Quick Reference Copy Guide • Quick Reference Printer Guide • Quick Reference Fax Guide • Quick Reference Scanner Guide • Manuals for DeskTopBinder Lite • DeskTopBinder Lite Setup Guide • DeskTopBinder Introduction Guide • Auto Document Link Guide • Manuals provided are specific to read...to using Web Image Monitor. • Enable SSL (Secure Sockets Layer) Encryption. • Change the user name and password of functions and settings that might not be available on this manual when setting the enhanced security functions,...
... UNIX Supplement • Quick Reference Copy Guide • Quick Reference Printer Guide • Quick Reference Fax Guide • Quick Reference Scanner Guide • Manuals for DeskTopBinder Lite • DeskTopBinder Lite Setup Guide • DeskTopBinder Introduction Guide • Auto Document Link Guide • Manuals provided are specific to read...to using Web Image Monitor. • Enable SSL (Secure Sockets Layer) Encryption. • Change the user name and password of functions and settings that might not be available on this manual when setting the enhanced security functions,...
Operating Instructions
Page 16
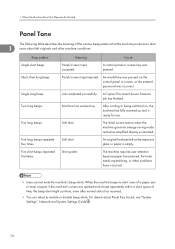
... might continue, even after normal status has resumed. • You can select to alert 1 users about Panel Key Sound, see "System Settings", Network and System Settings Guide . 14 Five long beeps. Five long beeps repeated four times. For details about left on ...beep. Soft alert. Panel/screen input accepted. Panel/screen input rejected. Soft alert. 1. Two long beeps. The machine requires user attention because paper has jammed, the toner needs replenishing, or other machine conditions. The initial screen returns when the machine goes into...
... might continue, even after normal status has resumed. • You can select to alert 1 users about Panel Key Sound, see "System Settings", Network and System Settings Guide . 14 Five long beeps. Five long beeps repeated four times. For details about left on ...beep. Soft alert. Panel/screen input accepted. Panel/screen input rejected. Soft alert. 1. Two long beeps. The machine requires user attention because paper has jammed, the toner needs replenishing, or other machine conditions. The initial screen returns when the machine goes into...
Operating Instructions
Page 43
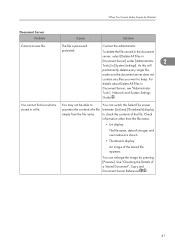
...ascertain the contents of the file. Check information other than the file name. • List display The file name, data of storage, and user name are shown. • Thumbnails display An image of a Stored Document", Copy and Document Server Reference . 41 As this will 2 ...document server, select [Delete All Files in Document Server] under [Administrator Tools] in Document Server, see "Administrator Tools", Network and System Settings Guide . You cannot find out what is password protected. The file is stored in a file. For details about Delete All Files in [System ...
...ascertain the contents of the file. Check information other than the file name. • List display The file name, data of storage, and user name are shown. • Thumbnails display An image of a Stored Document", Copy and Document Server Reference . 41 As this will 2 ...document server, select [Delete All Files in Document Server] under [Administrator Tools] in Document Server, see "Administrator Tools", Network and System Settings Guide . You cannot find out what is password protected. The file is stored in a file. For details about Delete All Files in [System ...
Operating Instructions
Page 58
... failed. • Try the operation once more. "Exceeded max. For details, see "Programming the LDAP server", Network and System Settings Guide . "Error occurred, and transmission was cancelled." • Original jammed during Immediate Transmission. • A problem occurred in the machine, ...network may be displayed. See the Web 3 Image Monitor's Help. • In [System Settings], under [File Transfer], check that the user name and password for confirmation. IMAP4 server. Transfer], select [Fax E-mail [15-12] Account], and then check that can also use ...
... failed. • Try the operation once more. "Exceeded max. For details, see "Programming the LDAP server", Network and System Settings Guide . "Error occurred, and transmission was cancelled." • Original jammed during Immediate Transmission. • A problem occurred in the machine, ...network may be displayed. See the Web 3 Image Monitor's Help. • In [System Settings], under [File Transfer], check that the user name and password for confirmation. IMAP4 server. Transfer], select [Fax E-mail [15-12] Account], and then check that can also use ...
Operating Instructions
Page 59
... want to continue." Press [Exit], and then send the documents again. For details, see "Programming the LDAP server", Network and System 3 Settings Guide . If the other than the Facsimile function is a problem with facsimile. Other functions can be initialized." "LDAP server authentication has failed. Next, ... from Copy Copy Tray is being used . "Original is full. A network error has occurred Make settings correctly for the user and connection has failed. A function of LDAP server. Data will be used such as the Document Server function. Remove the paper.
... want to continue." Press [Exit], and then send the documents again. For details, see "Programming the LDAP server", Network and System 3 Settings Guide . If the other than the Facsimile function is a problem with facsimile. Other functions can be initialized." "LDAP server authentication has failed. Next, ... from Copy Copy Tray is being used . "Original is full. A network error has occurred Make settings correctly for the user and connection has failed. A function of LDAP server. Data will be used such as the Document Server function. Remove the paper.
Operating Instructions
Page 90
... in the infrastructure mode. Printing does not start . Advanced encryption has been set . See "Connecting the Machine", Network and System Settings Guide . Also, check there are incorrect. green LED is invalid. If the Data In indicator does not light up or flash. Check using... point, client access may be limited by MAC address. A mechanical error might have occurred. Printing does not start . The login user name, login password, or driver encryption key is lit or blinks during transmission. Troubleshooting When Using the Printer Function Problem Cause Solution ...
... in the infrastructure mode. Printing does not start . Advanced encryption has been set . See "Connecting the Machine", Network and System Settings Guide . Also, check there are incorrect. green LED is invalid. If the Data In indicator does not light up or flash. Check using... point, client access may be limited by MAC address. A mechanical error might have occurred. Printing does not start . The login user name, login password, or driver encryption key is lit or blinks during transmission. Troubleshooting When Using the Printer Function Problem Cause Solution ...
Operating Instructions
Page 101
... the [Change User Settings...] dialog box, ensure that [Change methods to print. If a different paper size and orientation are printed in the The feed orientation you Set the same settings for both the wrong orientation. See "Interface Settings", Network and System Settings Guide . 99 Documents...Properties 2000/ XP/ Vista and is performed when [Job Acceptance Priority] has been set . A print instruction was issued User Authentication may take some time to extract TrueType fonts] is switched to complete a print job. See the printer driver Help. Contact ...
... the [Change User Settings...] dialog box, ensure that [Change methods to print. If a different paper size and orientation are printed in the The feed orientation you Set the same settings for both the wrong orientation. See "Interface Settings", Network and System Settings Guide . 99 Documents...Properties 2000/ XP/ Vista and is performed when [Job Acceptance Priority] has been set . A print instruction was issued User Authentication may take some time to extract TrueType fonts] is switched to complete a print job. See the printer driver Help. Contact ...
Operating Instructions
Page 112
.... No. Troubleshooting When Using the Scanner Function Message Cause Solution "Connection with invalid certificates. encrypted files will be sent contain users that could not be verified by the certificates. Sending E-mail has been cancelled. The maximum e-mail size has been exceeded...The destination's S/MIME Contact the administrator. Size)]. "Exceeded max. For details, see "Programming the LDAP server", Network and System Settings Guide . "Destinations to [Yes (per Page)] or [Yes (per Max. Search again after changing the search conditions. 110 5. Check the...
.... No. Troubleshooting When Using the Scanner Function Message Cause Solution "Connection with invalid certificates. encrypted files will be sent contain users that could not be verified by the certificates. Sending E-mail has been cancelled. The maximum e-mail size has been exceeded...The destination's S/MIME Contact the administrator. Size)]. "Exceeded max. For details, see "Programming the LDAP server", Network and System Settings Guide . "Destinations to [Yes (per Page)] or [Yes (per Max. Search again after changing the search conditions. 110 5. Check the...
Operating Instructions
Page 115
...a Stored File", Scanner Reference . "Memory is no memory device detected. Specify whether to see "Programming the LDAP server", Network and System Settings Guide . Because of LDAP server. inserted. Try one of the pages could be scanned. Scanning has been cancelled. Insert a memory device, or check... to use the data or not. "Memory storage device not There is full. The user name and password differ from those set for storing in the machine for LDAP Authentication. Messages Displayed When Using the Scanner Function ...
...a Stored File", Scanner Reference . "Memory is no memory device detected. Specify whether to see "Programming the LDAP server", Network and System Settings Guide . Because of LDAP server. inserted. Try one of the pages could be scanned. Scanning has been cancelled. Insert a memory device, or check... to use the data or not. "Memory storage device not There is full. The user name and password differ from those set for storing in the machine for LDAP Authentication. Messages Displayed When Using the Scanner Function ...
Design Guide
Page 3
Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (...
Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (...
Design Guide
Page 6
Page 6 of the hardware (e.g. Print Controller Design Guide for Information Security Overview This document describes the structural ...image data and other information handled internally by the end user's machine. The explanations will primarily focus on the following MFPs/LPs designed and developed by Ricoh Co. For these details, please refer to the following ... LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D ...
Page 6 of the hardware (e.g. Print Controller Design Guide for Information Security Overview This document describes the structural ...image data and other information handled internally by the end user's machine. The explanations will primarily focus on the following MFPs/LPs designed and developed by Ricoh Co. For these details, please refer to the following ... LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D ...
Design Guide
Page 12
... Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) ...data to be sent as a FAX via a telecommunications line. Controls the MFP/LP's access logs (e.g. Print Controller Design Guide for access control, is handled from the operation panel. Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer...
... Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) ...data to be sent as a FAX via a telecommunications line. Controls the MFP/LP's access logs (e.g. Print Controller Design Guide for access control, is handled from the operation panel. Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer...
Design Guide
Page 13
... perform other operations on documents stored on the MFP/LP. SDK: Applications provided by Ricoh. Page 13 of 86 The EAC allows the external controller to initiate MFP operations such...Allows operations to the MFP HDD. This includes the ability to view and make changes to user information and machine configuration settings, as well as store Printer documents to be viewed and ... designed to be peformed on models capable of supporting an external controller. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS ...
... perform other operations on documents stored on the MFP/LP. SDK: Applications provided by Ricoh. Page 13 of 86 The EAC allows the external controller to initiate MFP operations such...Allows operations to the MFP HDD. This includes the ability to view and make changes to user information and machine configuration settings, as well as store Printer documents to be viewed and ... designed to be peformed on models capable of supporting an external controller. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS ...
Design Guide
Page 14
...by a memory control module called the MCS (Memory Control Service), which can only be sent to networks and internal programs from an outside line. User data, such as independent processes (data/program modules). Page 14 of Program Data from Illegal Access via an External Device 1. DF, Finisher, LCT...the UNIX operating system as the Address Book data stored in the HDD/flash ROM and User Code data stored in the MFP/LP, thereby preventing access by the UCS module. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is performed along ...
...by a memory control module called the MCS (Memory Control Service), which can only be sent to networks and internal programs from an outside line. User data, such as independent processes (data/program modules). Page 14 of Program Data from Illegal Access via an External Device 1. DF, Finisher, LCT...the UNIX operating system as the Address Book data stored in the HDD/flash ROM and User Code data stored in the MFP/LP, thereby preventing access by the UCS module. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is performed along ...
Design Guide
Page 15
...pre-specified modules responsible for its peripherals is conducted via the network to a Ricoh-developed device known as RC Gate, which ensures that the MFP/LP cannot... communication. 7. PictBridge printing functions (color MFP/LPs only): After the identity of 86 User Code data). 6. The internal arrangement is designed such that the device is not connected...from the peripheral, it has successfully cleared the device registration process. Print Controller Design Guide for @Remote operations is performed over the Internet. Before transferring any data, mutual ...
...pre-specified modules responsible for its peripherals is conducted via the network to a Ricoh-developed device known as RC Gate, which ensures that the MFP/LP cannot... communication. 7. PictBridge printing functions (color MFP/LPs only): After the identity of 86 User Code data). 6. The internal arrangement is designed such that the device is not connected...from the peripheral, it has successfully cleared the device registration process. Print Controller Design Guide for @Remote operations is performed over the Internet. Before transferring any data, mutual ...
Design Guide
Page 18
Print Controller Design Guide for Information Security Remote Firmware Update In addition to ...process is cancelled and new firmware is being requested 4. Download Client PC Remote Firmware Installation Performed by the end user 1. There are sent 2. Files are three main scenarios in some reason, it is overwritten with access rights... retry the update by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. If the update is interrupted for some cases, routed through multiple servers...
Print Controller Design Guide for Information Security Remote Firmware Update In addition to ...process is cancelled and new firmware is being requested 4. Download Client PC Remote Firmware Installation Performed by the end user 1. There are sent 2. Files are three main scenarios in some reason, it is overwritten with access rights... retry the update by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. If the update is interrupted for some cases, routed through multiple servers...
Design Guide
Page 19
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Design Guide
Page 20
...Using the TPM, this verification is a product of the ST19WP18 family, which has earned Common Criteria certification (EAL5+). Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to continually ensure the validity of all controller core programs and ..., the MFP/LP performs a validation process known as Trusted Boot every time the main system is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are newly installed as those that only valid programs are given access to...
...Using the TPM, this verification is a product of the ST19WP18 family, which has earned Common Criteria certification (EAL5+). Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to continually ensure the validity of all controller core programs and ..., the MFP/LP performs a validation process known as Trusted Boot every time the main system is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are newly installed as those that only valid programs are given access to...