User Guide
Page 60
...HDD, the Aficio MP 6001/MP 7001/ • MP 8001/MP 9001 Series' have the ability to forward all incoming faxes directly to an administrator's email • address or folder, or you can still be extracted from specific senders directly to the • Fax Option Type 9001. LAN Fax software is now automated...printed on both sides of the • main units. This removes • customer resistance to switching from existing LAN-Fax solutions to Ricoh's, as the primary task of manually • re-entering address book entries is available with the Printer/Scanner Unit Type 9001 and ...
...HDD, the Aficio MP 6001/MP 7001/ • MP 8001/MP 9001 Series' have the ability to forward all incoming faxes directly to an administrator's email • address or folder, or you can still be extracted from specific senders directly to the • Fax Option Type 9001. LAN Fax software is now automated...printed on both sides of the • main units. This removes • customer resistance to switching from existing LAN-Fax solutions to Ricoh's, as the primary task of manually • re-entering address book entries is available with the Printer/Scanner Unit Type 9001 and ...
Operating Instructions
Page 8
..., data tampering, or information leakage. Facsimile Reference Explains Facsimile functions and operations. It explains security functions that you can use to prevent unauthorized use the software provided. Security Reference This manual is for resolving common usage-related problems. Copy and Document Server Reference Explains Copier and Document Server functions and operations...
..., data tampering, or information leakage. Facsimile Reference Explains Facsimile functions and operations. It explains security functions that you can use to prevent unauthorized use the software provided. Security Reference This manual is for resolving common usage-related problems. Copy and Document Server Reference Explains Copier and Document Server functions and operations...
Operating Instructions
Page 9
... be available on this manual when setting the enhanced security functions, or user and administrator authentication. Be sure to read this machine. • The following software products are specific to set up and use PostScript 3.
... be available on this manual when setting the enhanced security functions, or user and administrator authentication. Be sure to read this machine. • The following software products are specific to set up and use PostScript 3.
Operating Instructions
Page 106
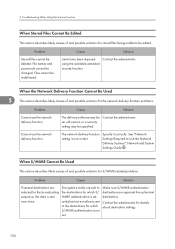
Problem Stored files cannot be changed. Cause Solution The delivery software may be edited. See "Network Settings Required to be specified. Encrypted e-mails are sent to the destinations for which S/MIME authentication is not correct. When ...
Problem Stored files cannot be changed. Cause Solution The delivery software may be edited. See "Network Settings Required to be specified. Encrypted e-mails are sent to the destinations for which S/MIME authentication is not correct. When ...
Design Guide
Page 2
Internal System Configuration 7 1-1 Hardware Configuration 7 1-1-1 MFP ...7 1-1-2 LP ...9 1-2 Software Configuration 11 1-2-1 Shared Service Layers 11 1-2-2 Principal Machine Functions 12 1-3 Data Security ...14 1-3-1 External I/F ...14 1-3-2 Protection of Program Data from Illegal Access via an External ...
Internal System Configuration 7 1-1 Hardware Configuration 7 1-1-1 MFP ...7 1-1-2 LP ...9 1-2 Software Configuration 11 1-2-1 Shared Service Layers 11 1-2-2 Principal Machine Functions 12 1-3 Data Security ...14 1-3-1 External I/F ...14 1-3-2 Protection of Program Data from Illegal Access via an External ...
Design Guide
Page 6
...LD370sp LD380 LD380sp LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro ...Ricoh MFP/LPs. Page 6 of 86 For these details, please refer to as the information security of image data and other information handled internally by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software...
...LD370sp LD380 LD380sp LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro ...Ricoh MFP/LPs. Page 6 of 86 For these details, please refer to as the information security of image data and other information handled internally by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software...
Design Guide
Page 8
Page 8 of the software installed on the hardware platform, which includes checking for any illegal alterations. Print Controller Design Guide for Information Security • Serial communication between the external ...
Page 8 of the software installed on the hardware platform, which includes checking for any illegal alterations. Print Controller Design Guide for Information Security • Serial communication between the external ...
Design Guide
Page 10
... firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations. Page 10 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes...
... firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations. Page 10 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes...
Design Guide
Page 11
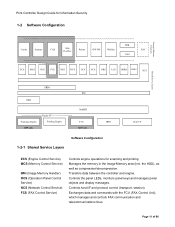
..., monitors panel keys and manages panel objects and display messages. Principal Machine Functions Print Controller Design Guide for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS...S Shared Service Layers SRM libc IMH Engine I/F Scanning Engine Printing Engine MFP only NetBSD FCU MFP only HDD Software Configuration 1-2-1 Shared Service Layers Host I /F and protocol control (transport, session). Manages the memory in the Image Memory area (incl.
..., monitors panel keys and manages panel objects and display messages. Principal Machine Functions Print Controller Design Guide for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS...S Shared Service Layers SRM libc IMH Engine I/F Scanning Engine Printing Engine MFP only NetBSD FCU MFP only HDD Software Configuration 1-2-1 Shared Service Layers Host I /F and protocol control (transport, session). Manages the memory in the Image Memory area (incl.
Design Guide
Page 14
.... 3. Data transfer between modules is Unix socket-based, whereby communication is managed by specified machine function(s). This arrangement ensures that the data can function as software for connection of 86 All of the above principal machine functions, as well as a two-way parallel interface when using a USB cable. • Standard IEEE...
.... 3. Data transfer between modules is Unix socket-based, whereby communication is managed by specified machine function(s). This arrangement ensures that the data can function as software for connection of 86 All of the above principal machine functions, as well as a two-way parallel interface when using a USB cable. • Standard IEEE...
Design Guide
Page 20
Page 20 of 86 Covering the range of software from boot programs to validate the controller core programs, which include the MFP/LP operating system, BIOS, and boot loader. Trusted Boot employs two methods ...
Page 20 of 86 Covering the range of software from boot programs to validate the controller core programs, which include the MFP/LP operating system, BIOS, and boot loader. Trusted Boot employs two methods ...
Design Guide
Page 27
...on the HDD), the image data itself remains in MFP/LP memory both permanently and temporarily. The HDD stores data such as optional software stored on the operation panel, however the machine will continue functioning normally. Even in the unlikely event that data reconstruction is not possible..., the NVRAM stores data such as User Tools settings, while the FCU stores FAX reception image data. National Security Agency The Ricoh randomized value method, a Ricoh-original method which ensure that the HDD were removed from the MFP/LP, a third party would not be enough to completely ...
...on the HDD), the image data itself remains in MFP/LP memory both permanently and temporarily. The HDD stores data such as optional software stored on the operation panel, however the machine will continue functioning normally. Even in the unlikely event that data reconstruction is not possible..., the NVRAM stores data such as User Tools settings, while the FCU stores FAX reception image data. National Security Agency The Ricoh randomized value method, a Ricoh-original method which ensure that the HDD were removed from the MFP/LP, a third party would not be enough to completely ...
Design Guide
Page 55
...side, the password necessary for changing the document's access level, and other cases, the MFP Scanner is automatically set the MFP or related software to perform the following operations: - In all other security settings associated with the driver. 2-3-3 Protection of Data when Performing Scanning and Sending.... Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must be done using the "Restrict use the TWAIN V4 driver. This makes it is necessary to use of destinations" setting ...
...side, the password necessary for changing the document's access level, and other cases, the MFP Scanner is automatically set the MFP or related software to perform the following operations: - In all other security settings associated with the driver. 2-3-3 Protection of Data when Performing Scanning and Sending.... Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must be done using the "Restrict use the TWAIN V4 driver. This makes it is necessary to use of destinations" setting ...