Security Target
Page 3
...TOE Type ...8 1.3.2 TOE Usage ...8 1.3.3 Major Security Features of TOE 10 1.4 TOE Description...10 1.4.1 Physical Boundary of TOE 10 1.4.2 Guidance Documents 13 1.4.3 Definition of TOE 19 1.4.4.1. Functions ...24 1.5 Glossary...24 1.5.1 Glossary for This ST 24 2 Conformance Claim...27 2.1 CC Conformance Claim 27 2.2 PP Claims...27...PP .........28 2.4.3 Consistency Claim with Security Requirements in PP 28 3 Security Problem Definitions 31 Copyright (c) 2011 RICOH COMPANY, LTD. TSF Data...24 1.4.5.3. User Data...23 1.4.5.2. Direct User...18 1.4.3.2. Basic Functions 19 1.4.4.2.
...TOE Type ...8 1.3.2 TOE Usage ...8 1.3.3 Major Security Features of TOE 10 1.4 TOE Description...10 1.4.1 Physical Boundary of TOE 10 1.4.2 Guidance Documents 13 1.4.3 Definition of TOE 19 1.4.4.1. Functions ...24 1.5 Glossary...24 1.5.1 Glossary for This ST 24 2 Conformance Claim...27 2.1 CC Conformance Claim 27 2.2 PP Claims...27...PP .........28 2.4.3 Consistency Claim with Security Requirements in PP 28 3 Security Problem Definitions 31 Copyright (c) 2011 RICOH COMPANY, LTD. TSF Data...24 1.4.5.3. User Data...23 1.4.5.2. Direct User...18 1.4.3.2. Basic Functions 19 1.4.4.2.
Security Target
Page 4
......35 4.2.2 Non-IT Environment 36 4.3 Security Objectives Rationale 37 4.3.1 Correspondence Table of Security Objectives 37 4.3.2 Security Objectives Descriptions 38 5 Extended Components Definition 42 5.1 Restricted forwarding of data to external interfaces (FPT_FDI_EXP 42 6 Security Requirements...44 6.1 Security Functional Requirements 44 6.1.1 Class FAU: Security audit 44... Justification of Traceability 64 6.3.3 Dependency Analysis 70 6.3.4 Security Assurance Requirements Rationale 72 7 TOE Summary Specification 73 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
......35 4.2.2 Non-IT Environment 36 4.3 Security Objectives Rationale 37 4.3.1 Correspondence Table of Security Objectives 37 4.3.2 Security Objectives Descriptions 38 5 Extended Components Definition 42 5.1 Restricted forwarding of data to external interfaces (FPT_FDI_EXP 42 6 Security Requirements...44 6.1 Security Functional Requirements 44 6.1.1 Class FAU: Security audit 44... Justification of Traceability 64 6.3.3 Dependency Analysis 70 6.3.4 Security Assurance Requirements Rationale 72 7 TOE Summary Specification 73 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 5
... for English Version-2 ...14 Table 4 : Guidance for English Version-3 ...15 Table 5 : Guidance for English Version-4 ...16 Table 6 : Definition of Users ...18 Table 7 : List of Administrative Roles ...18 Table 8: Definition of User Data ...23 Table 9: Definition of TSF Data...24 Table 10: Specific Terms Related to This ST 24 Table 11: Rationale for Security... Functional Requirements 63 Table 35: Result of Dependency Analysis of TOE Security Functional Requirements 70 Table 36: Auditable Events and Audit Data 73 Copyright (c) 2011 RICOH COMPANY, LTD.
... for English Version-2 ...14 Table 4 : Guidance for English Version-3 ...15 Table 5 : Guidance for English Version-4 ...16 Table 6 : Definition of Users ...18 Table 7 : List of Administrative Roles ...18 Table 8: Definition of User Data ...23 Table 9: Definition of TSF Data...24 Table 10: Specific Terms Related to This ST 24 Table 11: Rationale for Security... Functional Requirements 63 Table 35: Result of Dependency Analysis of TOE Security Functional Requirements 70 Table 36: Auditable Events and Audit Data 73 Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 11
Network Protection Function - Use-of 87 - Security Management Function - Software Verification Function - Copyright (c) 2011 RICOH COMPANY, LTD. Identification and Authentication Function - Page 10 of -Feature Restriction Function - All rights reserved. Residual Data Overwrite Function -..., SD Card Slot, and SD Card. Fax Line Separation Function 1.4 TOE Description This section describes Physical Boundary of TOE, Guidance Documents, Definition of Users, Logical Boundary of TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP,...
Network Protection Function - Use-of 87 - Security Management Function - Software Verification Function - Copyright (c) 2011 RICOH COMPANY, LTD. Identification and Authentication Function - Page 10 of -Feature Restriction Function - All rights reserved. Residual Data Overwrite Function -..., SD Card Slot, and SD Card. Fax Line Separation Function 1.4 TOE Description This section describes Physical Boundary of TOE, Guidance Documents, Definition of Users, Logical Boundary of TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP,...
Security Target
Page 18
... H/I - 1.4.3 Definition of This Machine - The direct users and indirect users are described as follows: Copyright (c) 2011 RICOH COMPANY, LTD. Manuals for Administrators: Using this Machine in a Network Environment Compliant with IEEE Std. 2600.1TM-2009 - Notes for Administrators Security Reference Supplement - Manuals for Users D062-7155 - Notes for Users MP 6001/MP 7001/MP 8001/MP 9001 Aficio MP...
... H/I - 1.4.3 Definition of This Machine - The direct users and indirect users are described as follows: Copyright (c) 2011 RICOH COMPANY, LTD. Manuals for Administrators: Using this Machine in a Network Environment Compliant with IEEE Std. 2600.1TM-2009 - Notes for Administrators Security Reference Supplement - Manuals for Users D062-7155 - Notes for Users MP 6001/MP 7001/MP 8001/MP 9001 Aficio MP...
Security Target
Page 19
...User The "user" referred to in this ST indicates a direct user who has all management privileges (Table 7). Table 6 : Definition of Users Definition of Users Normal user Administrator Explanation A user who is allowed to manage normal users. Therefore, the different roles of the MFP ...authorised to delete and register the login password of the management privilege can use the TOE. Definition of Administrator Supervisor MFP administrator Table 7 : List of MFP Copyright (c) 2011 RICOH COMPANY, LTD. Authorised to the MFP administrator who has privileges to use Copy Function, ...
...User The "user" referred to in this ST indicates a direct user who has all management privileges (Table 7). Table 6 : Definition of Users Definition of Users Normal user Administrator Explanation A user who is allowed to manage normal users. Therefore, the different roles of the MFP ...authorised to delete and register the login password of the management privilege can use the TOE. Definition of Administrator Supervisor MFP administrator Table 7 : List of MFP Copyright (c) 2011 RICOH COMPANY, LTD. Authorised to the MFP administrator who has privileges to use Copy Function, ...
Security Target
Page 24
...: user data, TSF data and functions. 1.4.5.1. Software Verification Function The Software Verification Function is classified into two types: document data and function data. Copyright (c) 2011 RICOH COMPANY, LTD. Security Management Function The Security Management Function indicates overall functions that unauthorised intrusion from the telephone lines to confirm the MFP Control Software... fragments on the HDD and protect the data so that unauthorised intrusion from the telephone lines (same as a "job". Type Document data Function data Table 8: Definition of 87 -
...: user data, TSF data and functions. 1.4.5.1. Software Verification Function The Software Verification Function is classified into two types: document data and function data. Copyright (c) 2011 RICOH COMPANY, LTD. Security Management Function The Security Management Function indicates overall functions that unauthorised intrusion from the telephone lines to confirm the MFP Control Software... fragments on the HDD and protect the data so that unauthorised intrusion from the telephone lines (same as a "job". Type Document data Function data Table 8: Definition of 87 -
Security Target
Page 25
... identifies users by unauthorised persons. All rights reserved. A password associated with each user. Type Protected data Confidential data Table 9: Definition of particular users. Login user name, Number of Attempts before Lockout, settings for management of the document data of user data ...are classified as "TSF confidential data". Copyright (c) 2011 RICOH COMPANY, LTD. The components that are for Lockout Release Timer, lockout time, year-month-day settings, time settings, Minimum Password ...
... identifies users by unauthorised persons. All rights reserved. A password associated with each user. Type Protected data Confidential data Table 9: Definition of particular users. Login user name, Number of Attempts before Lockout, settings for management of the document data of user data ...are classified as "TSF confidential data". Copyright (c) 2011 RICOH COMPANY, LTD. The components that are for Lockout Release Timer, lockout time, year-month-day settings, time settings, Minimum Password ...
Security Target
Page 26
...names of the MFP administrators are not included in this list, although access privileges are four types of hard disk drive. Copyright (c) 2011 RICOH COMPANY, LTD. There are provided for the documents stored using Scanner Function. - A user job may be suspended or cancelled by users from...rights reserved. Page 25 of 87 Terms Auto logout Minimum Length Password Setting Password Complexity HDD User job Documents Document user list Document type Definitions A function for the Web Function: 30 minutes (this cannot be changed by users). Auto logout time for the Operation Panel: Auto ...
...names of the MFP administrators are not included in this list, although access privileges are four types of hard disk drive. Copyright (c) 2011 RICOH COMPANY, LTD. There are provided for the documents stored using Scanner Function. - A user job may be suspended or cancelled by users from...rights reserved. Page 25 of 87 Terms Auto logout Minimum Length Password Setting Password Complexity HDD User job Documents Document user list Document type Definitions A function for the Web Function: 30 minutes (this cannot be changed by users). Auto logout time for the Operation Panel: Auto ...
Security Target
Page 27
... Operation Panel Users for stored and received documents Folder transmission Destination folder E-mail transmission S/MIME user information LAN Fax Definitions A general term for the "folder transmission" function. This information is registered and managed by the MFP administrator. ... Server Function, Scanner Function, Printer Function, and Fax Function. An attribute associated with normal user processes. Copyright (c) 2011 RICOH COMPANY, LTD. Consists of the normal users who are authorised to a shared folder in the server, and identification and ...
... Operation Panel Users for stored and received documents Folder transmission Destination folder E-mail transmission S/MIME user information LAN Fax Definitions A general term for the "folder transmission" function. This information is registered and managed by the MFP administrator. ... Server Function, Scanner Function, Printer Function, and Fax Function. An attribute associated with normal user processes. Copyright (c) 2011 RICOH COMPANY, LTD. Consists of the normal users who are authorised to a shared folder in the server, and identification and ...
Security Target
Page 29
..., and conform to the PP. The HCDs combine these devices and equip one or more functions of the TOE. Copyright (c) 2011 RICOH COMPANY, LTD. The MFP is according to the security objectives in chapter 4. Therefore, the security problems and security objectives in chapter ... P.STORAGE_ENCRYPTION was added to connect telephone line. For the authentication function of the document is written in English, the security problem definitions in chapter 3 and security objectives in chapter 4 are consistent with Security Problems and Security Objectives in PP Defining all security objectives ...
..., and conform to the PP. The HCDs combine these devices and equip one or more functions of the TOE. Copyright (c) 2011 RICOH COMPANY, LTD. The MFP is according to the security objectives in chapter 4. Therefore, the security problems and security objectives in chapter ... P.STORAGE_ENCRYPTION was added to connect telephone line. For the authentication function of the document is written in English, the security problem definitions in chapter 3 and security objectives in chapter 4 are consistent with Security Problems and Security Objectives in PP Defining all security objectives ...
Security Target
Page 32
... user name, or by persons with a login user name but without an access permission to the TSF Protected Data. Copyright (c) 2011 RICOH COMPANY, LTD. T.PROT.ALT Alteration of TSF confidential data TSF Confidential Data under the TOE management may be disclosed to persons without a..., or by persons with a login user name but without an access permission to the document. Page 31 of 87 3 Security Problem Definitions This section describes Threats, Organisational Security Policies and Assumptions. 3.1 Threats Defined and described below are the assumed threats related to the use ...
... user name, or by persons with a login user name but without an access permission to the TSF Protected Data. Copyright (c) 2011 RICOH COMPANY, LTD. T.PROT.ALT Alteration of TSF confidential data TSF Confidential Data under the TOE management may be disclosed to persons without a..., or by persons with a login user name but without an access permission to the document. Page 31 of 87 3 Security Problem Definitions This section describes Threats, Organisational Security Policies and Assumptions. 3.1 Threats Defined and described below are the assumed threats related to the use ...
Security Target
Page 43
...of data to external interfaces 1 FPT_FDI_EXP.1 Restricted forwarding of data to external interfaces provides for the management functions in FMT: a) Definition of the role(s) that are connected to the TOE's external interfaces. However, some products may provide the capability for the TSF... forwarding of information from one external interface to another one external interface to another external interface. Rationale: Copyright (c) 2011 RICOH COMPANY, LTD. Many products receive information on specific external interfaces and are intended to transform and process this kind of ...
...of data to external interfaces 1 FPT_FDI_EXP.1 Restricted forwarding of data to external interfaces provides for the management functions in FMT: a) Definition of the role(s) that are connected to the TOE's external interfaces. However, some products may provide the capability for the TSF... forwarding of information from one external interface to another one external interface to another external interface. Rationale: Copyright (c) 2011 RICOH COMPANY, LTD. Many products receive information on specific external interfaces and are intended to transform and process this kind of ...
Security Target
Page 45
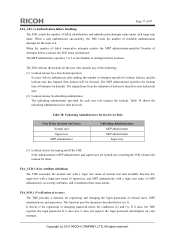
... face and brackets]. 6.1.1 Class FAU: Security audit FAU_GEN.1 Audit data generation Hierarchical to Original: perform an operation on the auditable event definitions of the functional components included in the PP/ST, [assignment: types of job for FDP_ACF.1(a), all login user names that are not...quoted from the extended security functional requirements defined in Operational Environment A (IEEE Std 2600.1-2009)). Table 12 : List of Copyright (c) 2011 RICOH COMPANY, LTD. Table 12 shows the action (CC rules) recommended by the CC as auditable for each audit event type, based on ...
... face and brackets]. 6.1.1 Class FAU: Security audit FAU_GEN.1 Audit data generation Hierarchical to Original: perform an operation on the auditable event definitions of the functional components included in the PP/ST, [assignment: types of job for FDP_ACF.1(a), all login user names that are not...quoted from the extended security functional requirements defined in Operational Environment A (IEEE Std 2600.1-2009)). Table 12 : List of Copyright (c) 2011 RICOH COMPANY, LTD. Table 12 shows the action (CC rules) recommended by the CC as auditable for each audit event type, based on ...
Security Target
Page 54
... a supervisor or the TOE's restart. Dependencies: No dependencies. Table 25: List of Security Attributes - FIA_ATD.1 User attribute definition Hierarchical to individual users: [assignment: the security attributes listed in Table 24]. Available function list - The lockout for each ...Upper-case letters: [A-Z] (26 letters) Lower-case letters: [a-z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (spaces 33 symbols) Copyright (c) 2011 RICOH COMPANY, LTD. Login user name of unsuccessful authentication attempts has been [selection: met], the TSF shall [assignment: perform actions...
... a supervisor or the TOE's restart. Dependencies: No dependencies. Table 25: List of Security Attributes - FIA_ATD.1 User attribute definition Hierarchical to individual users: [assignment: the security attributes listed in Table 24]. Available function list - The lockout for each ...Upper-case letters: [A-Z] (26 letters) Lower-case letters: [a-z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (spaces 33 symbols) Copyright (c) 2011 RICOH COMPANY, LTD. Login user name of unsuccessful authentication attempts has been [selection: met], the TSF shall [assignment: perform actions...
Security Target
Page 55
FIA_UAU.7 Protected authentication feedback Hierarchical to: No other components. Dependencies: FIA_ATD.1 User attribute definition Copyright (c) 2011 RICOH COMPANY, LTD. The MFP administrator specifies either Level 1 or Level 2 for Password Complexity Setting. FIA_UAU.1 Timing of authentication Hierarchical to be successfully identified before allowing ...
FIA_UAU.7 Protected authentication feedback Hierarchical to: No other components. Dependencies: FIA_ATD.1 User attribute definition Copyright (c) 2011 RICOH COMPANY, LTD. The MFP administrator specifies either Level 1 or Level 2 for Password Complexity Setting. FIA_UAU.1 Timing of authentication Hierarchical to be successfully identified before allowing ...
Security Target
Page 63
... 33 lists the assurance components of security measures Developer defined life-cycle model Flaw reporting procedures Conformance claims Extended components definition ST introduction Security objectives Derived security requirements Security problem definition Copyright (c) 2011 RICOH COMPANY, LTD. Table 33: TOE Security Assurance Requirements (EAL3+ALC_FLR.2) Assurance Classes ADV: Development AGD: Guidance documents ALC: Life...
... 33 lists the assurance components of security measures Developer defined life-cycle model Flaw reporting procedures Conformance claims Extended components definition ST introduction Security objectives Derived security requirements Security problem definition Copyright (c) 2011 RICOH COMPANY, LTD. Table 33: TOE Security Assurance Requirements (EAL3+ALC_FLR.2) Assurance Classes ADV: Development AGD: Guidance documents ALC: Life...
Security Target
Page 78
... time has elapsed, then lockout will be released. If it does not, it does, the TOE registers the login password. Copyright (c) 2011 RICOH COMPANY, LTD. FIA_ATD.1 (User attribute definition) The TOE associates the normal user with a login user name of normal user and available function list, supervisor with a login user name of...
... time has elapsed, then lockout will be released. If it does not, it does, the TOE registers the login password. Copyright (c) 2011 RICOH COMPANY, LTD. FIA_ATD.1 (User attribute definition) The TOE associates the normal user with a login user name of normal user and available function list, supervisor with a login user name of...