WGT624v3 Reference Manual
Page 16
... strong data encryption and authentication based on a pre-shared key. • Wireless access can be turned off -limits. • Logs security incidents. Support for firmware upgrade. 802.11g Wireless Networking The WGT624 v3 wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to you specify as blocked incoming traffic, port...
... strong data encryption and authentication based on a pre-shared key. • Wireless access can be turned off -limits. • Logs security incidents. Support for firmware upgrade. 802.11g Wireless Networking The WGT624 v3 wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to you specify as blocked incoming traffic, port...
WGT624v3 Reference Manual
Page 33
...: This field determines which the wireless interface is not listed, please check with another nearby access point. • Mode: Select the desired wireless mode. This field displays the region of up to 32 alphanumeric characters. The default is NETGEAR, but NETGEAR strongly recommends that fails, select ...legal to access this can be used. - This value is not the same as NETGEAr. • Region: Select your wireless card's documentation to see what method to change your country or region is intended. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note...
...: This field determines which the wireless interface is not listed, please check with another nearby access point. • Mode: Select the desired wireless mode. This field displays the region of up to 32 alphanumeric characters. The default is NETGEAR, but NETGEAR strongly recommends that fails, select ...legal to access this can be used. - This value is not the same as NETGEAr. • Region: Select your wireless card's documentation to see what method to change your country or region is intended. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note...
WGT624v3 Reference Manual
Page 34
... four keys will automatically be identical on all PCs and Access Points in your network in the selected key box. These values must be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level... group of printable characters in the Passphrase box and click the Generate button to 63 characters in length. 3-12 Configuring the Internet and Wireless Settings 202-10090-01, April 2005 Reference Manual for your network. • Automatic Key Generation (Passphrase): Enter a word or group ...
... four keys will automatically be identical on all PCs and Access Points in your network in the selected key box. These values must be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level... group of printable characters in the Passphrase box and click the Generate button to 63 characters in length. 3-12 Configuring the Internet and Wireless Settings 202-10090-01, April 2005 Reference Manual for your network. • Automatic Key Generation (Passphrase): Enter a word or group ...
WGT624v3 Reference Manual
Page 117
... are 1, 2, 5.5, 6, 9, 12, 18, 24, 36, 48, and 54 Mbps. Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. As a result, wireless clients can further extend the wireless network coverage. Wireless Networking Overview The WGT624 v3 wireless router conforms to 5.5, 2, and 1 Mbps when the radio signal is weak or when interference...
... are 1, 2, 5.5, 6, 9, 12, 18, 24, 36, 48, and 54 Mbps. Infrastructure Mode With a wireless Access Point, you can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. As a result, wireless clients can further extend the wireless network coverage. Wireless Networking Overview The WGT624 v3 wireless router conforms to 5.5, 2, and 1 Mbps when the radio signal is weak or when interference...
WGT624v3 Reference Manual
Page 118
... but may still be referred to as SSID. In this configuration, network packets are not encrypted. In an ad hoc wireless network with no Access Point involved in the various Windows operating systems. Some vendors also refer to ad hoc networking as network name. The ESSID is ...is one another, this configuration. each other node. Authentication and WEP Data Encryption The absence of the wireless local area network. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are within range...
... but may still be referred to as SSID. In this configuration, network packets are not encrypted. In an ad hoc wireless network with no Access Point involved in the various Windows operating systems. Some vendors also refer to ad hoc networking as network name. The ESSID is ...is one another, this configuration. each other node. Authentication and WEP Data Encryption The absence of the wireless local area network. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are within range...
WGT624v3 Reference Manual
Page 119
... in range. 3. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The access point associates with the network. The access point authenticates the station. 6. The station sends an authentication request to the access point. 5. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are described below. Reference Manual for messages from...
... in range. 3. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The access point associates with the network. The access point authenticates the station. 6. The station sends an authentication request to the access point. 5. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are described below. Reference Manual for messages from...
WGT624v3 Reference Manual
Page 120
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The station associates with either the 802.11 network or Ethernet network. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the access point. 4. If the decrypted text...
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The station associates with either the 802.11 network or Ethernet network. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the access point. 4. If the decrypted text...
WGT624v3 Reference Manual
Page 121
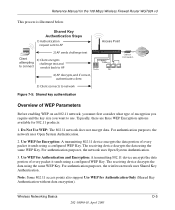
...: Some 802.11 access points also support Use WEP for Encryption: A transmitting 802.11 device encrypts the data portion of encryption you require and the key size you want to connect sends it sends using a configured WEP Key. For authentication purposes, the wireless network uses Shared Key... device decrypts the data using the same WEP Key. Typically, there are three WEP Encryption options available for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. The receiving device decrypts the data using the same WEP Key. Reference Manual for 802.11 ...
...: Some 802.11 access points also support Use WEP for Encryption: A transmitting 802.11 device encrypts the data portion of encryption you require and the key size you want to connect sends it sends using a configured WEP Key. For authentication purposes, the wireless network uses Shared Key... device decrypts the data using the same WEP Key. Typically, there are three WEP Encryption options available for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. The receiving device decrypts the data using the same WEP Key. Reference Manual for 802.11 ...
WGT624v3 Reference Manual
Page 122
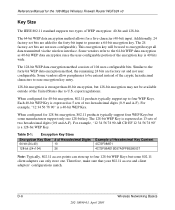
... for 40-bit encryption, 802.11 products typically support up to ease encryption key entry. 128-bit encryption is 40 bits wide. D-6 Wireless Networking Basics 202-10090-01, April 2005 This encryption key will be entered instead of two hexadecimal digits (0-9 and A-F). The 128-bit WEP... 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. The 128-bit WEP Key is a 40-bit WEP Key. The 24 factory-set and not user configurable. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11...
... for 40-bit encryption, 802.11 products typically support up to ease encryption key entry. 128-bit encryption is 40 bits wide. D-6 Wireless Networking Basics 202-10090-01, April 2005 This encryption key will be entered instead of two hexadecimal digits (0-9 and A-F). The 128-bit WEP... 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. The 128-bit WEP Key is a 40-bit WEP Key. The 24 factory-set and not user configurable. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11...
WGT624v3 Reference Manual
Page 123
...-10090-01, April 2005 The two devices will utilize frequency spectrum 12.5 MHz above and below . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on the network must have different default WEP Keys as long as its default key ... the 802.11 client adapters on all 802.11 devices that are listed in the same general vicinity will roam between access points, then all of the 802.11 access points and all of channel cross-talk, and provide a noticeable performance increase over networks with each other words, the AP...
...-10090-01, April 2005 The two devices will utilize frequency spectrum 12.5 MHz above and below . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on the network must have different default WEP Keys as long as its default key ... the 802.11 client adapters on all 802.11 devices that are listed in the same general vicinity will roam between access points, then all of the 802.11 access points and all of channel cross-talk, and provide a noticeable performance increase over networks with each other words, the AP...
WGT624v3 Reference Manual
Page 125
...Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on client and access point products. NETGEAR... is stronger than a day and decode the encrypted messages. For details on a particular wireless LAN must use the same encryption key. With 802.11 WEP,...
...Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on client and access point products. NETGEAR... is stronger than a day and decode the encrypted messages. For details on a particular wireless LAN must use the same encryption key. With 802.11 WEP,...
WGT624v3 Reference Manual
Page 126
...The RADIUS server holds (or has access to) user credentials (for example, user names and passwords) and authenticates wireless users before they gain access to WPA2 (IEEE 802.11i)? Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to..., Probe Response, and (Re) Association Requests. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Temporal Key Integrity Protocol (TKIP) - D-10 202-10090-01, April 2005 Wireless Networking Basics The following security features are secure IBSS (Ad-Hoc mode), ...
...The RADIUS server holds (or has access to) user credentials (for example, user names and passwords) and authenticates wireless users before they gain access to WPA2 (IEEE 802.11i)? Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to..., Probe Response, and (Re) Association Requests. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Temporal Key Integrity Protocol (TKIP) - D-10 202-10090-01, April 2005 Wireless Networking Basics The following security features are secure IBSS (Ad-Hoc mode), ...
WGT624v3 Reference Manual
Page 127
... key management in the Beacon frames is used for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in order to decide which in possession of its weaknesses. • Data integrity. Rather, the supplicant must use . For example, if the access point is used to wrap WEP in the information elements to...
... key management in the Beacon frames is used for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in order to decide which in possession of its weaknesses. • Data integrity. Rather, the supplicant must use . For example, if the access point is used to wrap WEP in the information elements to...
WGT624v3 Reference Manual
Page 128
...Layer Security (EAP-TTLS), defines how the authentication takes place. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that ...(EAP). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using 802.1x, the EAP type, such...
...Layer Security (EAP-TTLS), defines how the authentication takes place. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that ...(EAP). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using 802.1x, the EAP type, such...
WGT624v3 Reference Manual
Page 129
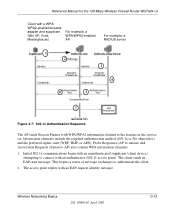
... the service set. The access point replies with an EAP-request identity message. Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win...
... the service set. The access point replies with an EAP-request identity message. Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win...
WGT624v3 Reference Manual
Page 130
...'s identity. The important part to know at this point is that is synchronized between the wireless client and the wireless access point (AP). For the global encryption key, WPA includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. If configured to upgrade an 802.1x-compliant access point. In typical 802.1x implementations, the client...
...'s identity. The important part to know at this point is that is synchronized between the wireless client and the wireless access point (AP). For the global encryption key, WPA includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. If configured to upgrade an 802.1x-compliant access point. In typical 802.1x implementations, the client...
WGT624v3 Reference Manual
Page 131
... of the NIC's hardware in both the station and the access point. Wireless Networking Basics 202-10090-01, April 2005 D-15 Michael also provides replay protection. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to... Michael specifies a new algorithm that calculates an 8-byte message integrity check (MIC) using the calculation facilities available on existing wireless devices. TKIP is a pragmatic compromise that allows organizations to deploy better security while AES capable equipment is appended to change ...
... of the NIC's hardware in both the station and the access point. Wireless Networking Basics 202-10090-01, April 2005 D-15 Michael also provides replay protection. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to... Michael specifies a new algorithm that calculates an 8-byte message integrity check (MIC) using the calculation facilities available on existing wireless devices. TKIP is a pragmatic compromise that allows organizations to deploy better security while AES capable equipment is appended to change ...
WGT624v3 Reference Manual
Page 132
... as integrity, are maintained. WPA/WPA2 is completely invulnerable. If the access point receives two data packets that the global encryption key is susceptible to lose network connectivity for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? Product Support for WPA/WPA2 Starting in...and has to -end network security strategy. wireless Wi-Fi certified products will have one year to maintain their Wi-Fi certification approved before August, 2003 will support the WPA standard. This is a definite step forward in August, 2003, NETGEAR, Inc. All other , then the ...
... as integrity, are maintained. WPA/WPA2 is completely invulnerable. If the access point receives two data packets that the global encryption key is susceptible to lose network connectivity for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? Product Support for WPA/WPA2 Starting in...and has to -end network security strategy. wireless Wi-Fi certified products will have one year to maintain their Wi-Fi certification approved before August, 2003 will support the WPA standard. This is a definite step forward in August, 2003, NETGEAR, Inc. All other , then the ...
WGT624v3 Reference Manual
Page 133
... Basics 202-10090-01, April 2005 D-17 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must obtain an updated network adapter driver that supports WPA. Changes to Wireless Network Adapters Wireless networking software in the adapter, and possibly in the OS or client application, must be updated to support the...
... Basics 202-10090-01, April 2005 D-17 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must obtain an updated network adapter driver that supports WPA. Changes to Wireless Network Adapters Wireless networking software in the adapter, and possibly in the OS or client application, must be updated to support the...
WGT624v3 Reference Manual
Page 135
...layer in 802.11 to communicate information on geographic requirements. The purpose of 11d is to add features and restrictions to allow access points to promote worldwide use of 802.11 WLANs. Equipment manufacturers do not want to systems operating in the 5 GHz frequency range ...several standards operating in different radio frequencies: 802.11b is a standard for wireless LANs operating in the 2.4 GHz spectrum with a bandwidth of 54 Mbps. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Glossary Use the list below to find definitions for technical terms used ...
...layer in 802.11 to communicate information on geographic requirements. The purpose of 11d is to add features and restrictions to allow access points to promote worldwide use of 802.11 WLANs. Equipment manufacturers do not want to systems operating in the 5 GHz frequency range ...several standards operating in different radio frequencies: 802.11b is a standard for wireless LANs operating in the 2.4 GHz spectrum with a bandwidth of 54 Mbps. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Glossary Use the list below to find definitions for technical terms used ...