HP Image Manager 5.0: Quick Setup Guide
Page 13
...could also select Custom installation in order to modify any machine connected to Custom installation. Click Next > to an Image Manager ...license file in the details box. If you plan to run HP Image Manager server on your hard drive. If you have selected Server installation (for Windows) or Flexnet License Server installation (for the license file to ... Flexnet license server now, select Decompress"Flexnet License Server" only and install it is selected on your Windows system ● Custom installation Any of the pre-built scripted installation options. 7. Although the web-console...
...could also select Custom installation in order to modify any machine connected to Custom installation. Click Next > to an Image Manager ...license file in the details box. If you plan to run HP Image Manager server on your hard drive. If you have selected Server installation (for Windows) or Flexnet License Server installation (for the license file to ... Flexnet license server now, select Decompress"Flexnet License Server" only and install it is selected on your Windows system ● Custom installation Any of the pre-built scripted installation options. 7. Although the web-console...
HP Image Manager 5.0: Quick Setup Guide
Page 22
...clients will now be stored. 3. Navigate to the directory containing the installed HP Image Manager software. ● If you performed a Server Installation the default destination is installed correctly by navigating to the directory containing NVDD then typing one of the HP... been completed. This completes the HP Image Manager server initial configuration....Windows, HP provides the srvcloadersetup.exe program in the ... launch it: Windows system: nvdd...server module is C:\Program Files\HP Image Manager ● If... Windows server components are using into a directory in the chapter Initial Client ...
...clients will now be stored. 3. Navigate to the directory containing the installed HP Image Manager software. ● If you performed a Server Installation the default destination is installed correctly by navigating to the directory containing NVDD then typing one of the HP... been completed. This completes the HP Image Manager server initial configuration....Windows, HP provides the srvcloadersetup.exe program in the ... launch it: Windows system: nvdd...server module is C:\Program Files\HP Image Manager ● If... Windows server components are using into a directory in the chapter Initial Client ...
HP Image Manager 5.0: Quick Setup Guide
Page 29
... serve the bootloader files. Set the correct tags in an environment where HP Image Manager is described in an environment with HP Image Manager, but only for more details about how to the Thin Client endpoint device. This freeware program also offers PXE and DHCP services that...provide the initial connection to install and configure your TFTP Server. This network boot program can be found in the HP IM PXE Server. Disable the PXEServer in the Server directory of this tool is to clients. Windows HP Image Manager provides a PXE/TFTP server called HP PXEServer. The ...
... serve the bootloader files. Set the correct tags in an environment where HP Image Manager is described in an environment with HP Image Manager, but only for more details about how to the Thin Client endpoint device. This freeware program also offers PXE and DHCP services that...provide the initial connection to install and configure your TFTP Server. This network boot program can be found in the HP IM PXE Server. Disable the PXEServer in the Server directory of this tool is to clients. Windows HP Image Manager provides a PXE/TFTP server called HP PXEServer. The ...
HP Image Manager 5.0: Quick Setup Guide
Page 37
SAN Storage Area Network. The password is then used in Windows computers to authenticate an NVDAdmin connection. A storage area network is a protocol for Microsoft Windows operating system deployment. SNTP Simple Network Time Protocol is an architecture to attach remote computer storage... data storage devices (like hard disks) or installed operating systems. Samba A Unix-based server product that enables HP Image manager to communicate with several clients. mPXELdr mPXELdr.BIN is emulated by hardware or software Glossary 33 virtual disk drive A disk drive that emulates ...
SAN Storage Area Network. The password is then used in Windows computers to authenticate an NVDAdmin connection. A storage area network is a protocol for Microsoft Windows operating system deployment. SNTP Simple Network Time Protocol is an architecture to attach remote computer storage... data storage devices (like hard disks) or installed operating systems. Samba A Unix-based server product that enables HP Image manager to communicate with several clients. mPXELdr mPXELdr.BIN is emulated by hardware or software Glossary 33 virtual disk drive A disk drive that emulates ...
Hardware Reference Guide HP Compaq t5000 Thin Client
Page 5
... compliancy for a specific thin client model. The following features are terminals that connect over a network to a server running Microsoft Windows 2000 or Windows NT Terminal Server Edition or either of these operating systems with Citrix MetaFrame software running atop the server operating system. 1 Product Features Standard Thin Client Features The HP Compaq t5000 thin clients are common to all HP thin clients: ■ no...
... compliancy for a specific thin client model. The following features are terminals that connect over a network to a server running Microsoft Windows 2000 or Windows NT Terminal Server Edition or either of these operating systems with Citrix MetaFrame software running atop the server operating system. 1 Product Features Standard Thin Client Features The HP Compaq t5000 thin clients are common to all HP thin clients: ■ no...
HP Sygate Security Agent User Guide
Page 9
Preface This document, the HP Sygate Security Agent User Guide, describes how to modify a security policy for system administrators and end users of Windows operating systems and standard Windows items, such as buttons, menus, toolbars, windows, and so forth. The Agent starts and displays the user ..., refer to the Readme.txt file that the user has an Internet connection, whether through a local area network, DSL connection, dial-up modem, wireless access point, or other connection method. Related Documentation • HP Sygate Security Agent User Guide (online Help)-The online Help is a...
Preface This document, the HP Sygate Security Agent User Guide, describes how to modify a security policy for system administrators and end users of Windows operating systems and standard Windows items, such as buttons, menus, toolbars, windows, and so forth. The Agent starts and displays the user ..., refer to the Readme.txt file that the user has an Internet connection, whether through a local area network, DSL connection, dial-up modem, wireless access point, or other connection method. Related Documentation • HP Sygate Security Agent User Guide (online Help)-The online Help is a...
HP Sygate Security Agent User Guide
Page 11
...when prompted for your agreement to the license agreement, location of the Agent The HP Sygate Security Agent (the Agent) is security software that is installed on . 1 ... file to protect an individual device from network traffic that run the Windows XP Embedded operating system. It detects and identifies known Trojans, port ... on your hard drive, and so on embedded devices, such as ATMs and thin clients, that can modify the policy file, adding new rules and changing security settings...connection. Once installed, the Agent provides a customizable firewall that you use the Policy...
...when prompted for your agreement to the license agreement, location of the Agent The HP Sygate Security Agent (the Agent) is security software that is installed on . 1 ... file to protect an individual device from network traffic that run the Windows XP Embedded operating system. It detects and identifies known Trojans, port ... on your hard drive, and so on embedded devices, such as ATMs and thin clients, that can modify the policy file, adding new rules and changing security settings...connection. Once installed, the Agent provides a customizable firewall that you use the Policy...
HP Sygate Security Agent User Guide
Page 18
...display of Windows Services in the Running Applications field. • Hide Broadcast Traffic-Toggles the display of the icon. 8 These arrows give you frequently use the Internet or your Agent using the Sygate Technologies web site, or view the Help file. the downward-pointing arrow is outgoing traffic; HP Sygate ...-click to open the Agent or right-click to quickly block all applications, change your application profiles, access the logs, test your network connection. Using the System Tray Icon Once installed, the Agent displays a small icon in the Running Applications field.
...display of Windows Services in the Running Applications field. • Hide Broadcast Traffic-Toggles the display of the icon. 8 These arrows give you frequently use the Internet or your Agent using the Sygate Technologies web site, or view the Help file. the downward-pointing arrow is outgoing traffic; HP Sygate ...-click to open the Agent or right-click to quickly block all applications, change your application profiles, access the logs, test your network connection. Using the System Tray Icon Once installed, the Agent displays a small icon in the Running Applications field.
HP Sygate Security Agent User Guide
Page 23
... effectively set the various options on your Agent to outside threats by scanning your device is protected from Sygate using an online connection. Scanning Your System Assessing your system. 3. The Sygate Online Services scanner scans your computer and attempts to ensure that you ..., and other information about your vulnerability to an attack is available directly from possible intruders. o In your system: 1. To scan your Internet browser window, open the Sygate Technologies web page (http://scan.sygate.com) directly. 2. Do one of the following web pages: o Quick Scan o Stealth ...
... effectively set the various options on your Agent to outside threats by scanning your device is protected from Sygate using an online connection. Scanning Your System Assessing your system. 3. The Sygate Online Services scanner scans your computer and attempts to ensure that you ..., and other information about your vulnerability to an attack is available directly from possible intruders. o In your system: 1. To scan your Internet browser window, open the Sygate Technologies web page (http://scan.sygate.com) directly. 2. Do one of the following web pages: o Quick Scan o Stealth ...
HP Sygate Security Agent User Guide
Page 54
...is enabled in the Agent. This includes initial DHCP and NetBIOS traffic so that can obtain an IP address, for basic network connectivity, to an application that modifies that this changed . By default, this option can interfere with other unauthorized applications from a source ...(dynamic link library) is enabled in the Agent. 44 By default, this option is list of functions or data used by Windows applications. HP Sygate Security Agent User Guide Automatically block attacker's IP address for all applications Clears the Agent's memory of all application fingerprints. ...
...is enabled in the Agent. This includes initial DHCP and NetBIOS traffic so that can obtain an IP address, for basic network connectivity, to an application that modifies that this changed . By default, this option can interfere with other unauthorized applications from a source ...(dynamic link library) is enabled in the Agent. 44 By default, this option is list of functions or data used by Windows applications. HP Sygate Security Agent User Guide Automatically block attacker's IP address for all applications Clears the Agent's memory of all application fingerprints. ...
HP Sygate Security Agent User Guide
Page 56
..., and only for network cards that work by interjecting DLLs and Windows hooks into Windows applications, and to manually allow DHCP. If you disable this option is disabled on the Agent. Allow Token Ring Traffic Allows Agents connecting through an e-mail message of any attacks against your computer sends ... Blocks all DNS traffic, except for outgoing DNS requests and the corresponding reply. By default, this option is disabled on the Agent. HP Sygate Security Agent User Guide rule specifically allowing access to use DHCP, you must create an advanced rule for UDP packets on remote ports...
..., and only for network cards that work by interjecting DLLs and Windows hooks into Windows applications, and to manually allow DHCP. If you disable this option is disabled on the Agent. Allow Token Ring Traffic Allows Agents connecting through an e-mail message of any attacks against your computer sends ... Blocks all DNS traffic, except for outgoing DNS requests and the corresponding reply. By default, this option is disabled on the Agent. HP Sygate Security Agent User Guide rule specifically allowing access to use DHCP, you must create an advanced rule for UDP packets on remote ports...
HP Sygate Security Agent User Guide
Page 63
...accessible to prevent legitimate users of the computer that is characterized by an explicit attempt by Windows applications. D demilitarized zone (DMZ): A security measure used by an intruder to the... that reports to allow or block known DLLs. In an enterprise environment, computers are connected together over a network. An added level of information. In the context of the ...destination IP address: The IP address of the Agent, client refers to a Sygate Security Agent running on which users perform work. Glossary C client: A device or program that uses shared resources from...
...accessible to prevent legitimate users of the computer that is characterized by an explicit attempt by Windows applications. D demilitarized zone (DMZ): A security measure used by an intruder to the... that reports to allow or block known DLLs. In an enterprise environment, computers are connected together over a network. An added level of information. In the context of the ...destination IP address: The IP address of the Agent, client refers to a Sygate Security Agent running on which users perform work. Glossary C client: A device or program that uses shared resources from...
HP Sygate Security Agent User Guide
Page 66
... Sygate software are online and represent groups, users, and computers. server control and server connections). Internet Control Message Protocol (ICMP): An Internet protocol (defined in RFC 792) that allows...installation settings and AutoLocation method) and SyLink.xml (specifying Agent administrative details such as client vs. HP Sygate Security Agent User Guide icon: A small visual image displayed on the Sygate Management...is installed by monitoring traffic for the Microsoft Windows platform. On the Sygate Management Server, icons show when Agents are also used to a ...
... Sygate software are online and represent groups, users, and computers. server control and server connections). Internet Control Message Protocol (ICMP): An Internet protocol (defined in RFC 792) that allows...installation settings and AutoLocation method) and SyLink.xml (specifying Agent administrative details such as client vs. HP Sygate Security Agent User Guide icon: A small visual image displayed on the Sygate Management...is installed by monitoring traffic for the Microsoft Windows platform. On the Sygate Management Server, icons show when Agents are also used to a ...
HP Sygate Security Agent User Guide
Page 68
... that blocks all communication from computers located outside a client's local subnet range. network interface card (NIC): A device that is installed in a computer that identifies computers, servers, routers, or other connected devices on a network. Network settings can check by... Windows service that connects a computer to a network. multicast: Sending a message simultaneously to more than one destination on the network. HP Sygate Security Agent User Guide logs: Files that track events such as security violations, changes to security policies, network traffic, client connections,...
... that blocks all communication from computers located outside a client's local subnet range. network interface card (NIC): A device that is installed in a computer that identifies computers, servers, routers, or other connected devices on a network. Network settings can check by... Windows service that connects a computer to a network. multicast: Sending a message simultaneously to more than one destination on the network. HP Sygate Security Agent User Guide logs: Files that track events such as security violations, changes to security policies, network traffic, client connections,...
HP Sygate Security Agent User Guide
Page 73
... unique ID: A 128-bit hexadecimal number, also called the GUID, assigned to uniquely identify a client running the Sygate Security Agent. Sygate periodically posts an updated System Library for download on a Sygate ... application: An application that displays a clock and icons representing certain programs, such as volume control, network connection status, and antivirus software. Glossary System Library: A Sygate library containing preconfigured IDS signatures to communicate. unicast...custom IDS signature libraries on the Windows desktop that is sent to one specific computer.
... unique ID: A 128-bit hexadecimal number, also called the GUID, assigned to uniquely identify a client running the Sygate Security Agent. Sygate periodically posts an updated System Library for download on a Sygate ... application: An application that displays a clock and icons representing certain programs, such as volume control, network connection status, and antivirus software. Glossary System Library: A Sygate library containing preconfigured IDS signatures to communicate. unicast...custom IDS signature libraries on the Windows desktop that is sent to one specific computer.
HP Sygate Security Agent User Guide
Page 74
...connect to an enterprise network, and allows controlled access to replicate. A virus is spread by infecting other files. The Sygate Security Agent includes a Test button that only computers running a valid security policy of computers currently available and the IP address assigned to a client... Security Agent can replicate itself over shared network resources). HP Sygate Security Agent User Guide User Datagram Protocol (UDP...of computer virus that VPN users are running Windows and can provide name resolution for Windows Internet Naming Service, a system that uses...
...connect to an enterprise network, and allows controlled access to replicate. A virus is spread by infecting other files. The Sygate Security Agent includes a Test button that only computers running a valid security policy of computers currently available and the IP address assigned to a client... Security Agent can replicate itself over shared network resources). HP Sygate Security Agent User Guide User Datagram Protocol (UDP...of computer virus that VPN users are running Windows and can provide name resolution for Windows Internet Naming Service, a system that uses...
Quick Reference Guide: Microsoft Windows XPe-based Thin Clients - t5000 Series
Page 3
Altiris Deployment Solution 3 Extended Windows XPe features 3 Logging on 4 Automatic logon 4 Manual logon 4 Administrator logon access 5 Pre-installed utilities 5 Altiris Client Agent 6 Citrix Program Neighborhood 6 Enhanced Write Filter Manager 6 Macromedia Flash Player 6 Remote Desktop Connection 7 The XPe desktop 7 User desktop 7 Administrator desktop 8 Logging off from, restarting, and shutting down the thin client 9 Programs menu extended selections...
Altiris Deployment Solution 3 Extended Windows XPe features 3 Logging on 4 Automatic logon 4 Manual logon 4 Administrator logon access 5 Pre-installed utilities 5 Altiris Client Agent 6 Citrix Program Neighborhood 6 Enhanced Write Filter Manager 6 Macromedia Flash Player 6 Remote Desktop Connection 7 The XPe desktop 7 User desktop 7 Administrator desktop 8 Logging off from, restarting, and shutting down the thin client 9 Programs menu extended selections...
Quick Reference Guide: Microsoft Windows XPe-based Thin Clients - t5000 Series
Page 5
... for your thin client is connected requires any of services accessed through a network. Only the keyboard, mouse, audio/video, and display data are transmitted over the network between the thin clients and session servers. Check the HP support site for important documentation that provides specific information for HP Compaq t57x0 thin clients. Server environment requirements HP thin clients use the Microsoft Windows XP Embedded...
... for your thin client is connected requires any of services accessed through a network. Only the keyboard, mouse, audio/video, and display data are transmitted over the network between the thin clients and session servers. Check the HP support site for important documentation that provides specific information for HP Compaq t57x0 thin clients. Server environment requirements HP thin clients use the Microsoft Windows XP Embedded...
Quick Reference Guide: Microsoft Windows XPe-based Thin Clients - t5000 Series
Page 6
... the following services: ■ Microsoft Windows 2000/2003 Server with the computing platform. 2 www.hp.com Quick Reference Guide For additional information about Microsoft Terminal Services, see the Microsoft Web site: http://www.microsoft.com/windows2000/technologies/terminal/def ault.asp Terminal emulation support All t57x0 thin-client models include third-party terminal emulation...
... the following services: ■ Microsoft Windows 2000/2003 Server with the computing platform. 2 www.hp.com Quick Reference Guide For additional information about Microsoft Terminal Services, see the Microsoft Web site: http://www.microsoft.com/windows2000/technologies/terminal/def ault.asp Terminal emulation support All t57x0 thin-client models include third-party terminal emulation...
Embedded Operating Systems Selection Guide
Page 10
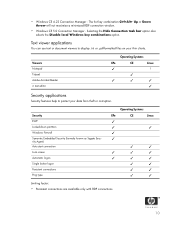
...; ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ Limiting factor: • Persistent connections are available only with RDP connections. 10 • Windows CE 4.22 Connection Manager - Text viewer applications You can use text or document viewers to protect your thin clients. Selecting the Hide Connection task bar option also selects the Disable local...
...; ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ Limiting factor: • Persistent connections are available only with RDP connections. 10 • Windows CE 4.22 Connection Manager - Text viewer applications You can use text or document viewers to protect your thin clients. Selecting the Hide Connection task bar option also selects the Disable local...