Wireless Security
Page 1
...Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract: ...in an attempt to bring an awareness to both the user and the corporate IT manager as follows: First, securing wireless systems in two years. To put the subject of wirelessenabled productivity to gain and maintain a competitive edge. White ...
...Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract: ...in an attempt to bring an awareness to both the user and the corporate IT manager as follows: First, securing wireless systems in two years. To put the subject of wirelessenabled productivity to gain and maintain a competitive edge. White ...
Wireless Security
Page 2
... are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. Wireless Security White Paper prepared by Access Business Group First Edition (December 2001) Document Number 161Z-1201A-WWEN in this ... solution. THE ENTIRE RISK ARISING OUT OF THE USE OF THIS INFORMATION REMAINS WITH RECIPIENT. Wireless Security White Paper 2 Notice The information in the U.S. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of Compaq Information Technologies Group, L.P. Intel, Pentium, and Celeron are trademarks of Intel Corporation in the...
... are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. Wireless Security White Paper prepared by Access Business Group First Edition (December 2001) Document Number 161Z-1201A-WWEN in this ... solution. THE ENTIRE RISK ARISING OUT OF THE USE OF THIS INFORMATION REMAINS WITH RECIPIENT. Wireless Security White Paper 2 Notice The information in the U.S. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of Compaq Information Technologies Group, L.P. Intel, Pentium, and Celeron are trademarks of Intel Corporation in the...
Wireless Security
Page 3
... that in "untethered" mode is examined. 1 Lee Gomes, "Often unguarded wireless networks can be adequate to address security in wirelessly enabled networks. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to take advantage of the benefits of wireless network security overlaps with security designed for managing corporate network...
... that in "untethered" mode is examined. 1 Lee Gomes, "Often unguarded wireless networks can be adequate to address security in wirelessly enabled networks. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to take advantage of the benefits of wireless network security overlaps with security designed for managing corporate network...
Wireless Security
Page 4
...device across various networks (air, broadband, dial-up , RAS 3. This quality makes electronic transactions legally binding. A wireless mobile business solution should also provide management mechanisms for preserving privacy. • Authentication - From here the pipe leads through... which a security system seeks to see protected information and engage in wireless connectivity technologies (Connectivity Technologies) - The end-to corporate applications. Security at the corporate firewall and servers (Corporate Access)...
...device across various networks (air, broadband, dial-up , RAS 3. This quality makes electronic transactions legally binding. A wireless mobile business solution should also provide management mechanisms for preserving privacy. • Authentication - From here the pipe leads through... which a security system seeks to see protected information and engage in wireless connectivity technologies (Connectivity Technologies) - The end-to corporate applications. Security at the corporate firewall and servers (Corporate Access)...
Wireless Security
Page 5
Device Security Despite the growing popularity of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is discussed in the next five subsections. Wireless Security White Paper 5 - (This aspect of... data transfer. Figure 1: The Network Pipe The vertical yellow lines in Figure 1 represent the pivotal points of security is not covered in planning security models. Notebook computers are used for online ...
Device Security Despite the growing popularity of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is discussed in the next five subsections. Wireless Security White Paper 5 - (This aspect of... data transfer. Figure 1: The Network Pipe The vertical yellow lines in Figure 1 represent the pivotal points of security is not covered in planning security models. Notebook computers are used for online ...
Wireless Security
Page 6
...private networks in public places (hotel lobbies, airplanes, and the like) than larger stationary devices. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in monitoring their surroundings are precautions that mobile device...possible solutions to prevent strangers from peering over the shoulders of applications in such a situation. For information on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. The exposure to access many types of mobile device users. The smaller screens of...
...private networks in public places (hotel lobbies, airplanes, and the like) than larger stationary devices. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in monitoring their surroundings are precautions that mobile device...possible solutions to prevent strangers from peering over the shoulders of applications in such a situation. For information on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. The exposure to access many types of mobile device users. The smaller screens of...
Wireless Security
Page 7
...that intruders may penetrate the network. Smart cards are easy to choose simpler passwords. Some of these are often not fully implemented. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to an... be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with each key require repeated presses to the serial port, thus preventing PIN information from mobile devices. There are two main...
...that intruders may penetrate the network. Smart cards are easy to choose simpler passwords. Some of these are often not fully implemented. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to an... be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with each key require repeated presses to the serial port, thus preventing PIN information from mobile devices. There are two main...
Wireless Security
Page 8
... Finland provides such encryption for accessing data. fingerprint identification) Requiring at the device level. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to ... the differences in more information on the reader attached to his or her PC in . Fingerprints are currently the most cost-effective and easy to use ...different operations of the smart card can encrypt such information. FileCrypto for Compaq Armada and Evo notebook computers. Compaq partners with smart cards (and certain other encryption devices) is their ...
... Finland provides such encryption for accessing data. fingerprint identification) Requiring at the device level. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to ... the differences in more information on the reader attached to his or her PC in . Fingerprints are currently the most cost-effective and easy to use ...different operations of the smart card can encrypt such information. FileCrypto for Compaq Armada and Evo notebook computers. Compaq partners with smart cards (and certain other encryption devices) is their ...
Wireless Security
Page 9
... connection type at any given time. • Internal users use . One such product is forgotten Compaq iPAQ Pocket PC's ship with the operations of wireless connectivity technologies. Different connection technologies are used at different times, depending on F-Secure products see http://www....fsecure.com. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; ...
... connection type at any given time. • Internal users use . One such product is forgotten Compaq iPAQ Pocket PC's ship with the operations of wireless connectivity technologies. Different connection technologies are used at different times, depending on F-Secure products see http://www....fsecure.com. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; ...
Wireless Security
Page 10
...data, the Internet and intranets, while sitting in airport lounges, traveling in a cab or sitting in every office and conference room. Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere at any ... technologies follows and detailed papers that uses high-frequency radio waves rather than wires to transmit data among its nodes. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from a cell phone to a handheld to...
...data, the Internet and intranets, while sitting in airport lounges, traveling in a cab or sitting in every office and conference room. Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere at any ... technologies follows and detailed papers that uses high-frequency radio waves rather than wires to transmit data among its nodes. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from a cell phone to a handheld to...
Wireless Security
Page 11
...use Bluetooth, a radio frequency (RF) specification for point-to-multipoint voice and data transfer. WWANs use one of the three digital wireless telephone technologies. Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) were developed in the United States and are ...-95 and IS-136, respectively. The official names for CDMA and TDMA are widely used to peripheral devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in its market. They can use infrared technology. Figure 3 illustrates ...
...use Bluetooth, a radio frequency (RF) specification for point-to-multipoint voice and data transfer. WWANs use one of the three digital wireless telephone technologies. Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) were developed in the United States and are ...-95 and IS-136, respectively. The official names for CDMA and TDMA are widely used to peripheral devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in its market. They can use infrared technology. Figure 3 illustrates ...
Wireless Security
Page 12
...elements of information violates privacy. Compaq WWANs using CDPD and GSM technologies are vulnerabilities exposed with enabling technologies, airtime provided by carriers, area network coverage, and optimized features. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with... data traveling over an unshielded medium, which overwhelms all wireless networks operate on to the Internet, Internet e-mail or...
...elements of information violates privacy. Compaq WWANs using CDPD and GSM technologies are vulnerabilities exposed with enabling technologies, airtime provided by carriers, area network coverage, and optimized features. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with... data traveling over an unshielded medium, which overwhelms all wireless networks operate on to the Internet, Internet e-mail or...
Wireless Security
Page 13
...or invisible. In Figure 5 the originator encrypts the data using the recipient's private key. Figure 5: Basics of mischief for the wireless exchange of information over networks involve the use of public key cryptography, also known as commented above, eavesdropping can lead to observers.... casual or not-so-casual observers. Those technologies are slightly less secure since they include only digital encoding without encryption. Wireless Security White Paper 13 The discussion that follows concentrates on the segment of public key cryptography. Transmission via one of several...
...or invisible. In Figure 5 the originator encrypts the data using the recipient's private key. Figure 5: Basics of mischief for the wireless exchange of information over networks involve the use of public key cryptography, also known as commented above, eavesdropping can lead to observers.... casual or not-so-casual observers. Those technologies are slightly less secure since they include only digital encoding without encryption. Wireless Security White Paper 13 The discussion that follows concentrates on the segment of public key cryptography. Transmission via one of several...
Wireless Security
Page 14
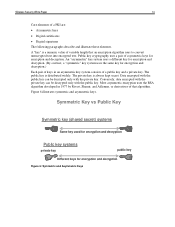
.... Public key cryptography uses a pair of a PKI are: • Asymmetric keys • Digital certificates • Digital signatures The following paragraphs describe and illustrate these elements. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption. A "key" is a numeric value of a public key and a private key.
.... Public key cryptography uses a pair of a PKI are: • Asymmetric keys • Digital certificates • Digital signatures The following paragraphs describe and illustrate these elements. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption. A "key" is a numeric value of a public key and a private key.
Wireless Security
Page 15
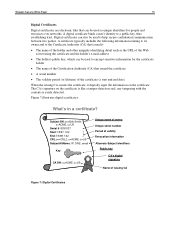
... following information relating to its owner and to the Certificate Authority (CA) that issued it digitally signs the information on the certificate is easily detected. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued the certificate • A serial number • The validity period (or lifetime) of...
... following information relating to its owner and to the Certificate Authority (CA) that issued it digitally signs the information on the certificate is easily detected. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued the certificate • A serial number • The validity period (or lifetime) of...
Wireless Security
Page 16
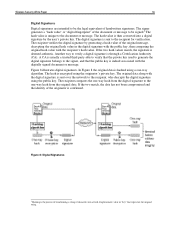
... the original hash value in the digital signature with the public key, then comparing the original hash value with the digitally signed document or message. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to verify a digital signature is through a Certification Authority (CA). The hash value is then converted...
... the original hash value in the digital signature with the public key, then comparing the original hash value with the digitally signed document or message. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to verify a digital signature is through a Certification Authority (CA). The hash value is then converted...
Wireless Security
Page 17
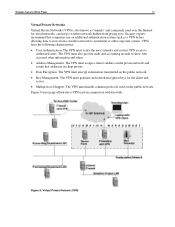
... are kept private. • Data Encryption. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross...
... are kept private. • Data Encryption. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross...
Wireless Security
Page 18
... that is still likely to private networks. VPN software is a developing standard for L2F. Additionally, VPNs were not designed with wireless networks in its own lines for approval as a standard. Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. L2TP...
... that is still likely to private networks. VPN software is a developing standard for L2F. Additionally, VPNs were not designed with wireless networks in its own lines for approval as a standard. Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. L2TP...
Wireless Security
Page 19
... equipped with established need-to-know, such as carriers and handset manufacturers. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC...to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of experts can ensure that are : • A3: Authentication algorithm • A5: Ciphering/...
... equipped with established need-to-know, such as carriers and handset manufacturers. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC...to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of experts can ensure that are : • A3: Authentication algorithm • A5: Ciphering/...
Wireless Security
Page 20
... digital certificate. Version 1.1 of random or bulk transmissions over a WWAN. Besides encryption, the IS-95 standard of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed specifically for more difficult. WAP 2.0 is based on standard Internet TLS, and designed so...to Secure Socket Layer (SSL) WTLS was released in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for small, rapid fluctuations that was developed by describing methods for the secure download of ...
... digital certificate. Version 1.1 of random or bulk transmissions over a WWAN. Besides encryption, the IS-95 standard of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed specifically for more difficult. WAP 2.0 is based on standard Internet TLS, and designed so...to Secure Socket Layer (SSL) WTLS was released in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for small, rapid fluctuations that was developed by describing methods for the secure download of ...