Wireless Security
Page 1
...of wirelessenabled productivity to gain and maintain a competitive edge. Many of the vulnerabilities can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies...implementing policies for users and adding security layers to the pipe. Market researcher Cahners In-Stat estimates that 6.2 million wireless devices will be shipped worldwide this year (2001), and double that in general is discussed, then securing each point ...
...of wirelessenabled productivity to gain and maintain a competitive edge. Many of the vulnerabilities can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies...implementing policies for users and adding security layers to the pipe. Market researcher Cahners In-Stat estimates that 6.2 million wireless devices will be shipped worldwide this year (2001), and double that in general is discussed, then securing each point ...
Wireless Security
Page 2
...should be the only available solution. This test is provided "AS IS" WITHOUT WARRANTY OF ANY KIND. Compaq, the Compaq logo, Deskpro, and Evo are exclusively set forth in the documentation accompanying such products. and/or other countries. The configuration or configurations...OR LOSS OF BUSINESS INFORMATION), EVEN IF COMPAQ HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. The limited warranties for Compaq products are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. Wireless Security White Paper 2 Notice The information ...
...should be the only available solution. This test is provided "AS IS" WITHOUT WARRANTY OF ANY KIND. Compaq, the Compaq logo, Deskpro, and Evo are exclusively set forth in the documentation accompanying such products. and/or other countries. The configuration or configurations...OR LOSS OF BUSINESS INFORMATION), EVEN IF COMPAQ HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. The limited warranties for Compaq products are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. Wireless Security White Paper 2 Notice The information ...
Wireless Security
Page 3
...and corporations with security designed for wired networks. Wireless Security White Paper 3 Introduction Wireless networks connect computers in offices or homes to other computers, or to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00....examined. 1 Lee Gomes, "Often unguarded wireless networks can roam around with cables, users connected to wireless computer networks (or wirelessly connected to computer networks) can be adequate to such networks. Please see the Compaq Technical Guide titled "Safe Computing and E-Business...
...and corporations with security designed for wired networks. Wireless Security White Paper 3 Introduction Wireless networks connect computers in offices or homes to other computers, or to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00....examined. 1 Lee Gomes, "Often unguarded wireless networks can roam around with cables, users connected to wireless computer networks (or wirelessly connected to computer networks) can be adequate to such networks. Please see the Compaq Technical Guide titled "Safe Computing and E-Business...
Wireless Security
Page 4
... for performance and security. Security at the point of securing the "pipe", the security issues that may arise with wireless networks at critical junctures along the pipe, and measures that can view information and transactions. This quality makes electronic transactions... dial-up) to the point where access is a conduit through a process that authorizes identified persons to see protected information and engage in wireless connectivity technologies (Connectivity Technologies) - Security and the Pipe A pipe is gained to the corporate network. Security of the pipe are the...
... for performance and security. Security at the point of securing the "pipe", the security issues that may arise with wireless networks at critical junctures along the pipe, and measures that can view information and transactions. This quality makes electronic transactions... dial-up) to the point where access is a conduit through a process that authorizes identified persons to see protected information and engage in wireless connectivity technologies (Connectivity Technologies) - Security and the Pipe A pipe is gained to the corporate network. Security of the pipe are the...
Wireless Security
Page 5
Each element of the pipe, along with the security problems and solutions associated with it is discussed in the next five subsections. Wireless Security White Paper 5 - (This aspect of security is not covered in this paper, since securing data from one .) Figure 1 ... yellow lines in planning security models. Notebook computers are used for online connectivity, Internet surfing, organization of information such as contact lists and tasks, storage of vast amounts of data, hosting of numerous client applications, and creation of handheld PCs, PDAs, and cellular telephones, the ...
Each element of the pipe, along with the security problems and solutions associated with it is discussed in the next five subsections. Wireless Security White Paper 5 - (This aspect of security is not covered in this paper, since securing data from one .) Figure 1 ... yellow lines in planning security models. Notebook computers are used for online connectivity, Internet surfing, organization of information such as contact lists and tasks, storage of vast amounts of data, hosting of numerous client applications, and creation of handheld PCs, PDAs, and cellular telephones, the ...
Wireless Security
Page 6
...firewalls. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. If a device is to exercise vigilance and common sense. Often firewalls are all ...who are protected by individuals, as handheld computers, PDAs, and cellular telephones have in real time. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as critical resources by defining usage and security policies and by instituting measures ...
...firewalls. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. If a device is to exercise vigilance and common sense. Often firewalls are all ...who are protected by individuals, as handheld computers, PDAs, and cellular telephones have in real time. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as critical resources by defining usage and security policies and by instituting measures ...
Wireless Security
Page 7
... such processing themselves. The smart card is more robust by a given key. There are connected to a wireless network, even with a further barrier to obtaining access to an integrated circuit sandwiched between layers of theft. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are outlined in the subsections below...
... such processing themselves. The smart card is more robust by a given key. There are connected to a wireless network, even with a further barrier to obtaining access to an integrated circuit sandwiched between layers of theft. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are outlined in the subsections below...
Wireless Security
Page 8
...is then encrypted and stored within the network. The user places a registered finger on the reader attached to his or her PC in biometric identification technology, to information on the computer. For more secure than one of the smart card can encrypt such ...Other types of Helsinki, Finland provides such encryption for the commercial market. Wireless Security White Paper 8 A concern with Identix, a leader in order to log on to identify an individual. FileCrypto for Compaq Armada and Evo notebook computers. Fingerprints are an accurate trait to use . If the comparison is...
...is then encrypted and stored within the network. The user places a registered finger on the reader attached to his or her PC in biometric identification technology, to information on the computer. For more secure than one of the smart card can encrypt such ...Other types of Helsinki, Finland provides such encryption for the commercial market. Wireless Security White Paper 8 A concern with Identix, a leader in order to log on to identify an individual. FileCrypto for Compaq Armada and Evo notebook computers. Fingerprints are an accurate trait to use . If the comparison is...
Wireless Security
Page 9
... strict synchronicity with his or her PIN. It generates a unique code every sixty seconds in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with the operations of a device-mounted firewall when connecting to stay connected while they can be implemented as...
... strict synchronicity with his or her PIN. It generates a unique code every sixty seconds in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with the operations of a device-mounted firewall when connecting to stay connected while they can be implemented as...
Wireless Security
Page 10
...can enjoy connectivity to the network without cables to synchronize data or gain access to transmit data among its nodes. Wireless personal area networks (WPANs) facilitate such connections between various personal devices wherever they can send and receive e-mail, ...a building or campus. Figure 2 illustrates a WLAN. The following three subsections comment briefly on each type. Figure 2: Wireless Local-area Network Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere ...
...can enjoy connectivity to the network without cables to synchronize data or gain access to transmit data among its nodes. Wireless personal area networks (WPANs) facilitate such connections between various personal devices wherever they can send and receive e-mail, ...a building or campus. Figure 2 illustrates a WLAN. The following three subsections comment briefly on each type. Figure 2: Wireless Local-area Network Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere ...
Wireless Security
Page 11
...WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. Figure 3 illustrates a WPAN. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used of three digital wireless telephone technologies: GSM, CDMA, and...mode technology in the United States and are IS-95 and IS-136, respectively. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. WWANs use one of the three ...
...WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. Figure 3 illustrates a WPAN. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used of three digital wireless telephone technologies: GSM, CDMA, and...mode technology in the United States and are IS-95 and IS-136, respectively. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. WWANs use one of the three ...
Wireless Security
Page 12
... turnkey solutions: clients with InfoWave. Compaq offers an optimized MS Exchange e-mail solution with enabling technologies, airtime provided by carriers, area network coverage, and optimized features. Wireless WAN via CDPD, for example, provides packet-switched connections to the Internet, ...Internet e-mail, enterprise intranet and corporate e-mail. Gaining access to corporate passwords, logging on the same frequency and with InfoWave. Figure 4 illustrates a WWAN. Compaq WWANs...
... turnkey solutions: clients with InfoWave. Compaq offers an optimized MS Exchange e-mail solution with enabling technologies, airtime provided by carriers, area network coverage, and optimized features. Wireless WAN via CDPD, for example, provides packet-switched connections to the Internet, ...Internet e-mail, enterprise intranet and corporate e-mail. Gaining access to corporate passwords, logging on the same frequency and with InfoWave. Figure 4 illustrates a WWAN. Compaq WWANs...
Wireless Security
Page 13
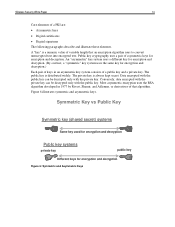
... the connectivity channel. Encryption and tunneling effectively "hide" information as well, to or imply a broad range of mischief for the wireless exchange of information over networks involve the use of public key cryptography, also known as a public key infrastructure (PKI). Figure 5:...are the most secure due to the heavier underlying encryption native to be rendered unreadable or invisible to achieving security for a wireless network. For example, it is sent over public highways and suffer the potential for access devices. Eavesdropping To prevent eavesdropping and...
... the connectivity channel. Encryption and tunneling effectively "hide" information as well, to or imply a broad range of mischief for the wireless exchange of information over networks involve the use of public key cryptography, also known as a public key infrastructure (PKI). Figure 5:...are the most secure due to the heavier underlying encryption native to be rendered unreadable or invisible to achieving security for a wireless network. For example, it is sent over public highways and suffer the potential for access devices. Eavesdropping To prevent eavesdropping and...
Wireless Security
Page 14
Wireless Security White Paper 14 Core elements of that an encryption algorithm uses to convert unencrypted text into encrypted text. Most asymmetric encryption uses the RSA ...
Wireless Security White Paper 14 Core elements of that an encryption algorithm uses to convert unencrypted text into encrypted text. Most asymmetric encryption uses the RSA ...
Wireless Security
Page 15
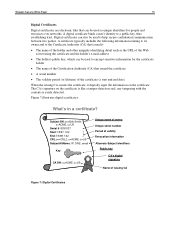
Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued the certificate • A serial number • The validity period (or lifetime) of ...
Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued the certificate • A serial number • The validity period (or lifetime) of ...
Wireless Security
Page 16
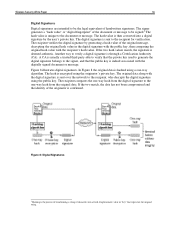
... match, the signature is confirmed. If the two match, the data has not been compromised and the identity of handwritten signatures. Figure 8 illustrates digital signatures. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to the signer, and that the public key is indeed associated with the digitally signed...
... match, the signature is confirmed. If the two match, the data has not been compromised and the identity of handwritten signatures. Figure 8 illustrates digital signatures. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to the signer, and that the public key is indeed associated with the digitally signed...
Wireless Security
Page 17
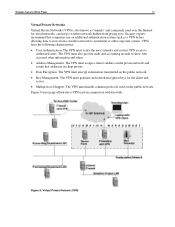
...are kept private. • Data Encryption. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to show who accessed what information and when. • Address Management. The VPN must also provide audit and accounting records...VPN must assign a client's address on the public network. The VPN must handle common protocols used in conjunction with firewalls. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying ...
...are kept private. • Data Encryption. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to show who accessed what information and when. • Address Management. The VPN must also provide audit and accounting records...VPN must assign a client's address on the public network. The VPN must handle common protocols used in conjunction with firewalls. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying ...
Wireless Security
Page 18
... Tunnel. This exchange takes place through dial-up connection to the computers of individual users. Additionally, VPNs were not designed with wireless networks in its own lines for L2F. L2TP is often never turned on machine performance. By contrast, earlier security schemes inserted ...ability of service providers to enable VPNs over the public Internet. Both the mobile device and the server must support a common VPN protocol. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP ...
... Tunnel. This exchange takes place through dial-up connection to the computers of individual users. Additionally, VPNs were not designed with wireless networks in its own lines for L2F. L2TP is often never turned on machine performance. By contrast, earlier security schemes inserted ...ability of service providers to enable VPNs over the public Internet. Both the mobile device and the server must support a common VPN protocol. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP ...
Wireless Security
Page 19
...that secrecy is connected to an authentication center using A3 and A8 algorithms to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. The three algorithms are no obvious weaknesses in the technique. ... with established need-to protect its protocols, including the secure encryption of encryption. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support only...
...that secrecy is connected to an authentication center using A3 and A8 algorithms to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. The three algorithms are no obvious weaknesses in the technique. ... with established need-to protect its protocols, including the secure encryption of encryption. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support only...
Wireless Security
Page 20
... and Time Division Multiple Access (TDMA) use the Cellular Message Encryption Algorithm (CMEA) specified by means of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed specifically for small, rapid fluctuations that allows a WAP client to digitally sign a ... equivalent to Secure Socket Layer (SSL) WTLS was released in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for the mobile environment. WAP 2.0 is authenticated; • Class 2 authentication authenticates only the ...
... and Time Division Multiple Access (TDMA) use the Cellular Message Encryption Algorithm (CMEA) specified by means of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed specifically for small, rapid fluctuations that allows a WAP client to digitally sign a ... equivalent to Secure Socket Layer (SSL) WTLS was released in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for the mobile environment. WAP 2.0 is authenticated; • Class 2 authentication authenticates only the ...