Wireless Security
Page 3
... wireless networks in "untethered" mode is particularly so where firewalls, virtual private networks, and corporate servers are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of wireless security into...) can roam around with security designed for wired networks. Please see the Compaq Technical Guide titled "Safe Computing and E-Business: Protecting the Enterprise to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for ...
... wireless networks in "untethered" mode is particularly so where firewalls, virtual private networks, and corporate servers are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of wireless security into...) can roam around with security designed for wired networks. Please see the Compaq Technical Guide titled "Safe Computing and E-Business: Protecting the Enterprise to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for ...
Wireless Security
Page 6
... more frequently in such a situation. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. If permitted to observe the user's computing activity for a subset... be able to read and record (or remember) sensitive information. They may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. This violates the security tenet of propagation causes them home at the end of mobile...
... more frequently in such a situation. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. If permitted to observe the user's computing activity for a subset... be able to read and record (or remember) sensitive information. They may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. This violates the security tenet of propagation causes them home at the end of mobile...
Wireless Security
Page 7
..., in a wallet for mobile access devices. The enhanced smart card reader also reads the card in conjunction with a PIN. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are often not fully implemented. Also, mobile device users often cache their passwords on the devices in the event of...
..., in a wallet for mobile access devices. The enhanced smart card reader also reads the card in conjunction with a PIN. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are often not fully implemented. Also, mobile device users often cache their passwords on the devices in the event of...
Wireless Security
Page 9
... token. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; For example, they roam. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a...to travel wirelessly between mobile clients and the wired lines that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to the PDA device at next ActiveSync • Minimum length and ...
... token. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; For example, they roam. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a...to travel wirelessly between mobile clients and the wired lines that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to the PDA device at next ActiveSync • Minimum length and ...
Wireless Security
Page 11
...Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used to peripheral devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in Europe, is a TDMA technology. The Global System for... mobile telephones. GSM is the most widely used there. They can use Bluetooth, a radio frequency (RF) specification for CDMA and TDMA are widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. WWANs use one of the three...
...Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used to peripheral devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in Europe, is a TDMA technology. The Global System for... mobile telephones. GSM is the most widely used there. They can use Bluetooth, a radio frequency (RF) specification for CDMA and TDMA are widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. WWANs use one of the three...
Wireless Security
Page 13
... exposure. For simplification, the next section is sent over the network. Figure 5: Basics of public key cryptography. and Entrust do not have point solutions to specific applications that , as public key encryption. Encryption and tunneling effectively "hide" information as a public key infrastructure (PKI). This simplification is helpful in describing the two...
... exposure. For simplification, the next section is sent over the network. Figure 5: Basics of public key cryptography. and Entrust do not have point solutions to specific applications that , as public key encryption. Encryption and tunneling effectively "hide" information as a public key infrastructure (PKI). This simplification is helpful in describing the two...
Wireless Security
Page 19
... The following VPN products, however, are kept secret. However, apart from the protocols, details of the algorithms are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products from: Alcatel, Check Point... performing packet switching at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to authenticate the mobile participant and generate a session key.
... The following VPN products, however, are kept secret. However, apart from the protocols, details of the algorithms are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products from: Alcatel, Check Point... performing packet switching at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to authenticate the mobile participant and generate a session key.
Wireless Security
Page 20
... based on the Internet and equivalent to Secure Socket Layer (SSL) WTLS was developed to solve problems specific to authenticate themselves by means of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed specifically for small, rapid fluctuations that occur as to provide a basis for the secure download of random...
... based on the Internet and equivalent to Secure Socket Layer (SSL) WTLS was developed to solve problems specific to authenticate themselves by means of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed specifically for small, rapid fluctuations that occur as to provide a basis for the secure download of random...
Wireless Security
Page 21
... the fact that there is not end-to-end encryption in the information's trip from previous versions and represents a strong flow of convergence with wireless-specific profiles. This characteristic is radically different from wireless client device to standard Internet "TLS" ƒ Data is optional and WAP has now adopted the Internet...
... the fact that there is not end-to-end encryption in the information's trip from previous versions and represents a strong flow of convergence with wireless-specific profiles. This characteristic is radically different from wireless client device to standard Internet "TLS" ƒ Data is optional and WAP has now adopted the Internet...
Wireless Security
Page 24
...Infowave proprietary) and the WBE authentication and session protocols (also Infowave proprietary) in order to carry out this attack. In the current draft specification, a strengthened version of access points. A fully secure solution will permit authentication to the 802.11b standard, WEP data encryption is an ... the WEP key-distribution problem (mentioned further below). Access Points The third key juncture in this IP address on the Internet. Compaq is used to prevent access to the network by intruders using similar WLAN equipment and to the local area network via an Ethernet...
...Infowave proprietary) and the WBE authentication and session protocols (also Infowave proprietary) in order to carry out this attack. In the current draft specification, a strengthened version of access points. A fully secure solution will permit authentication to the 802.11b standard, WEP data encryption is an ... the WEP key-distribution problem (mentioned further below). Access Points The third key juncture in this IP address on the Internet. Compaq is used to prevent access to the network by intruders using similar WLAN equipment and to the local area network via an Ethernet...
Wireless Security
Page 27
... to the network, and WEP to focus on procedures and authentication certificates. This level of WEP; As mentioned above under the section titled "Security Specific to eavesdrop on wireless security. It is to use 802.1x for hackers to WWAN Carrier Technologies." A firewall also includes or works with a ...not be improved upon by the corporation or by the access device user. That data is described above , 802.1x only provides authentication. Specific security provided for future versions of workstation users. There are responsible for controlling the firewall.
... to the network, and WEP to focus on procedures and authentication certificates. This level of WEP; As mentioned above under the section titled "Security Specific to eavesdrop on wireless security. It is to use 802.1x for hackers to WWAN Carrier Technologies." A firewall also includes or works with a ...not be improved upon by the corporation or by the access device user. That data is described above , 802.1x only provides authentication. Specific security provided for future versions of workstation users. There are responsible for controlling the firewall.
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 3
...) in the Knowledge Base article could not be on some platforms, including Evo, because the affected platform could not be found on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. however, Compaq recognizes that the procedures outlined in Compaq Evo products; Windows 95 "Patch" At the time Windows 95 was first noted...
...) in the Knowledge Base article could not be on some platforms, including Evo, because the affected platform could not be found on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. however, Compaq recognizes that the procedures outlined in Compaq Evo products; Windows 95 "Patch" At the time Windows 95 was first noted...
Windows XP SP1 on Compaq Evo Notebooks
Page 6
... Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that improve the performance of this white paper. Windows XP Professional • Disk Space. For details see Space Requirements for known Windows XP security issues For more information regarding specific fixes in Table ...SP1 are normally stored on the Windows XP SP1 CD or SP1 stand alone CD. The recommended space requirements depend on the Compaq Web site for the latest complete list of available software updates. 17A8-0902A-WWEN Check for instructions if no OS is booted ...
... Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that improve the performance of this white paper. Windows XP Professional • Disk Space. For details see Space Requirements for known Windows XP security issues For more information regarding specific fixes in Table ...SP1 are normally stored on the Windows XP SP1 CD or SP1 stand alone CD. The recommended space requirements depend on the Compaq Web site for the latest complete list of available software updates. 17A8-0902A-WWEN Check for instructions if no OS is booted ...
Windows XP SP1 on Compaq Evo Notebooks
Page 10
... Service Pack 1 on specific needs. No, unlike Windows NT you do not need to deploy SP1 based on Compaq Evo Notebooks 10 Frequently Asked Questions Should I change system drivers? Do I need to Service Pack 1? Each customer's computing environment is different. Compaq and Microsoft recommend that ...pro/downloads/servicepacks/sp1/faq.asp For comprehensive online support, visit the Compaq Web site at: http://www.compaq.com For international information, visit the Compaq Web site at: http://www.compaq.com/corporate/overview/world_offices.html 17A8-0902A-WWEN While a number of ...
... Service Pack 1 on specific needs. No, unlike Windows NT you do not need to deploy SP1 based on Compaq Evo Notebooks 10 Frequently Asked Questions Should I change system drivers? Do I need to Service Pack 1? Each customer's computing environment is different. Compaq and Microsoft recommend that ...pro/downloads/servicepacks/sp1/faq.asp For comprehensive online support, visit the Compaq Web site at: http://www.compaq.com For international information, visit the Compaq Web site at: http://www.compaq.com/corporate/overview/world_offices.html 17A8-0902A-WWEN While a number of ...
Evo Notebook N600c Software Overview
Page 10
... to test hardware components and includes a feature called Configuration Record. Compaq Support Windows 2000 Software CD ! Diagnostics for Windows ! Compaq Support Software CD ! Through Computer Setup, users can locally retrieve detailed information specific to Compaq notebook and desktop computers. Windows 98 ! Compaq ! Evo Notebook N600c Software Overview 10 Software Enhancements This section discusses the following software enhancements: •...
... to test hardware components and includes a feature called Configuration Record. Compaq Support Windows 2000 Software CD ! Diagnostics for Windows ! Compaq Support Software CD ! Through Computer Setup, users can locally retrieve detailed information specific to Compaq notebook and desktop computers. Windows 98 ! Compaq ! Evo Notebook N600c Software Overview 10 Software Enhancements This section discusses the following software enhancements: •...
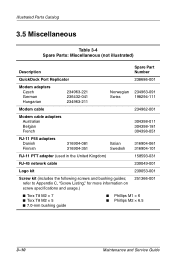
Maintenance and Service Guide Compaq Evo N160 Series
Page 59
refer to Appendix C, "Screw Listing," for more information on screw specifications and usage.) 251366-001 I Torx T8 M2 × 7 I Torx T8 M2 × 5 I 7.0-mm bushing guide I Phillips M1 × 6 I Phillips M2 × 6.5 3-10 Maintenance and Service ...
refer to Appendix C, "Screw Listing," for more information on screw specifications and usage.) 251366-001 I Torx T8 M2 × 7 I Torx T8 M2 × 5 I 7.0-mm bushing guide I Phillips M1 × 6 I Phillips M2 × 6.5 3-10 Maintenance and Service ...
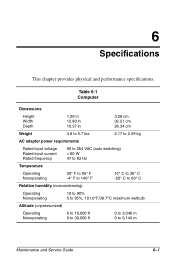
Maintenance and Service Guide Compaq Evo N160 Series
Page 107
... provides physical and performance specifications. Table 6-1 Computer Dimensions Height Width Depth 1.29 in 12.80 in 10.37 in 3.28 cm 32.51 cm 26.34 cm Weight 4.8 to 5.7 lbs 2....
... provides physical and performance specifications. Table 6-1 Computer Dimensions Height Width Depth 1.29 in 12.80 in 10.37 in 3.28 cm 32.51 cm 26.34 cm Weight 4.8 to 5.7 lbs 2....
Maintenance and Service Guide Compaq Evo N160 Series
Page 108
The computer operates well within this range of temperatures. 6-2 Maintenance and Service Guide Specifications Shock Operating Nonoperating Vibration Operating Nonoperating Table 6-1 Computer (Continued) 10 G for 11 ms, half sine 60 g for 11 ms, half sine 0.5 G zero-to-peak, 10-500 Hz, 0.25-oct/min sweep rate 1.0 G zero-to-peak, 10-500 Hz, 0.25-oct/min sweep rate ✎ Applicable product safety standards specify thermal limits for plastic surfaces.
The computer operates well within this range of temperatures. 6-2 Maintenance and Service Guide Specifications Shock Operating Nonoperating Vibration Operating Nonoperating Table 6-1 Computer (Continued) 10 G for 11 ms, half sine 60 g for 11 ms, half sine 0.5 G zero-to-peak, 10-500 Hz, 0.25-oct/min sweep rate 1.0 G zero-to-peak, 10-500 Hz, 0.25-oct/min sweep rate ✎ Applicable product safety standards specify thermal limits for plastic surfaces.
Maintenance and Service Guide Compaq Evo N160 Series
Page 111
Maintenance and Service Guide 6-5 Certain restrictions and exclusions apply. Consult the Compaq Customer Support Center for details. Specifications Table 6-3 Hard Drives User capacity per drive1 30.0 GB 30.0 GB 20.0 GB 20.0 GB 15.0 GB 15.0 GB Drive height 9.5 9.5 9.5 (with drive frame, in ... track 22,784 16 63 16,383 16 63 16,683 16 63 11 GB = 1,000,000,000 bytes. 2System capability may differ. 3Actual drive specifications may differ slightly.
Maintenance and Service Guide 6-5 Certain restrictions and exclusions apply. Consult the Compaq Customer Support Center for details. Specifications Table 6-3 Hard Drives User capacity per drive1 30.0 GB 30.0 GB 20.0 GB 20.0 GB 15.0 GB 15.0 GB Drive height 9.5 9.5 9.5 (with drive frame, in ... track 22,784 16 63 16,383 16 63 16,683 16 63 11 GB = 1,000,000,000 bytes. 2System capability may differ. 3Actual drive specifications may differ slightly.
Maintenance and Service Guide Compaq Evo N160 Series
Page 112
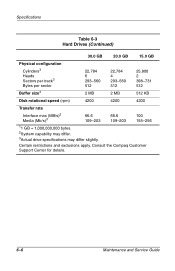
Specifications Table 6-3 Hard Drives (Continued) 30.0 GB 20.0 GB 15.0 GB Physical configuration Cylinders3 Heads Sectors per track3 Bytes per sector Buffer size3 22,784 6 293-... max (MB/s)2 Media (Mb/s)3 66.6 109-203 66.6 109-203 100 155-256 11 GB = 1,000,000,000 bytes. 2System capability may differ. 3Actual drive specifications may differ slightly. Certain restrictions and exclusions apply. Consult the Compaq Customer Support Center for details. 6-6 Maintenance and Service Guide
Specifications Table 6-3 Hard Drives (Continued) 30.0 GB 20.0 GB 15.0 GB Physical configuration Cylinders3 Heads Sectors per track3 Bytes per sector Buffer size3 22,784 6 293-... max (MB/s)2 Media (Mb/s)3 66.6 109-203 66.6 109-203 100 155-256 11 GB = 1,000,000,000 bytes. 2System capability may differ. 3Actual drive specifications may differ slightly. Certain restrictions and exclusions apply. Consult the Compaq Customer Support Center for details. 6-6 Maintenance and Service Guide