Quick Start Guide
Page 4
... ACCESS: You need an Internet account with an ISP (Internet Service Provider) and information such as user name, password, and so on the CD-ROM drive (usually drive D) and navigate to access the Internet and/or access the P-870HN-5xb Web Configurator. The browser will be used to it from this screen.
... ACCESS: You need an Internet account with an ISP (Internet Service Provider) and information such as user name, password, and so on the CD-ROM drive (usually drive D) and navigate to access the Internet and/or access the P-870HN-5xb Web Configurator. The browser will be used to it from this screen.
Quick Start Guide
Page 7
.... Internet Setup Go to get an IP address automatically from a DHCP server. When your browser and enter http://192.168.1.1 (the P-870HN-5xb's default IP address) as given to you allow web browser pop-up windows, JavaScripts and Java permissions. Open your VDSL Internet connection... is correct. 7 Enter the admin user name admin and password 1234 (default). Enter the Internet access information exactly as the address. 2. See your ADSL Internet connection is setup, the DSL LED should...
.... Internet Setup Go to get an IP address automatically from a DHCP server. When your browser and enter http://192.168.1.1 (the P-870HN-5xb's default IP address) as given to you allow web browser pop-up windows, JavaScripts and Java permissions. Open your VDSL Internet connection... is correct. 7 Enter the admin user name admin and password 1234 (default). Enter the Internet access information exactly as the address. 2. See your ADSL Internet connection is setup, the DSL LED should...
User Guide
Page 22
... Here are some example uses for Managing the Device Do the following things regularly to make sure you will have multiple WAN services over 22 P-870HN-5xb User's Guide You can connect to restore it in a safe place. • Back up an earlier configuration file, you backed up ...the configuration (and make the Device more effectively. • Change the password. If you forget your password, you know how to the Device's LAN ports (or wirelessly). Use a password that's not easy to guess and that consists of different types of characters, such as numbers and...
... Here are some example uses for Managing the Device Do the following things regularly to make sure you will have multiple WAN services over 22 P-870HN-5xb User's Guide You can connect to restore it in a safe place. • Back up an earlier configuration file, you backed up ...the configuration (and make the Device more effectively. • Change the password. If you forget your password, you know how to the Device's LAN ports (or wirelessly). Use a password that's not easy to guess and that consists of different types of characters, such as numbers and...
User Guide
Page 25
... line is communicating with a device on hardware connections. 1.6 The RESET Button If you forget your password or cannot access the web configurator, you had previously and the password will need to reload the factory-default configuration file. The Device does not have an Ethernet connection ...with the LAN. P-870HN-5xb User's Guide 25 The Device is activated. The wireless network is ...
... line is communicating with a device on hardware connections. 1.6 The RESET Button If you forget your password or cannot access the web configurator, you had previously and the password will need to reload the factory-default configuration file. The Device does not have an Ethernet connection ...with the LAN. P-870HN-5xb User's Guide 25 The Device is activated. The wireless network is ...
User Guide
Page 42
Chapter 2 Tutorials 4 Configure the PPP User and Password screen. The PPP Username is [email protected], the PPP Password is 1234, and the PPPoE Service Name is User. Click Next when you finish the settings. 42 P-870HN-5xb User's Guide
Chapter 2 Tutorials 4 Configure the PPP User and Password screen. The PPP Username is [email protected], the PPP Password is 1234, and the PPPoE Service Name is User. Click Next when you finish the settings. 42 P-870HN-5xb User's Guide
User Guide
Page 52
Enter the default admin user name admin and default admin password 1234. Click Cancel to revert to the default password in non-readable characters. You cannot configure some settings with the user account. Figure 18 Password Screen 52 P-870HN-5xb User's Guide Otherwise, enter the default user name user and user password user. The password displays in the password field. If you have changed the password, enter your password and click Login. Chapter 3 Introducing the Web Configurator 4 A password screen displays.
Enter the default admin user name admin and default admin password 1234. Click Cancel to revert to the default password in non-readable characters. You cannot configure some settings with the user account. Figure 18 Password Screen 52 P-870HN-5xb User's Guide Otherwise, enter the default user name user and user password user. The password displays in the password field. If you have changed the password, enter your password and click Login. Chapter 3 Introducing the Web Configurator 4 A password screen displays.
User Guide
Page 55
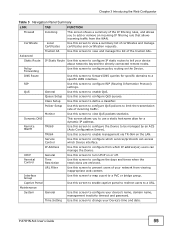
... allows incoming traffic from which Device interface. Service Control Use this screen to prevent users of your device's name, domain name, management inactivity timeout and password. Parental Control Time Restriction Use this screen to configure policy routing on the Device. URL Filter Use this screen to configure which services/protocols can... Use this screen to tell your Device's time and date. IP Address Use this screen to configure IP static routes to view QoS packets statistics. P-870HN-5xb User's Guide 55
... allows incoming traffic from which Device interface. Service Control Use this screen to prevent users of your device's name, domain name, management inactivity timeout and password. Parental Control Time Restriction Use this screen to configure policy routing on the Device. URL Filter Use this screen to configure which services/protocols can... Use this screen to tell your Device's time and date. IP Address Use this screen to configure IP static routes to view QoS packets statistics. P-870HN-5xb User's Guide 55
User Guide
Page 74
...packets of transporting packets over Ethernet) or PPPoA, they should also provide a username and password (and service name) for user authentication. PTM Packet Transfer Mode (PTM) is packet-... to include data from an outside network. If your ISP (Internet Service Provider). The ZyXEL device can be guaranteed. See Appendix E on page 355 for the Device, which makes...WAN IP Address The WAN IP address is an IP address for background information about IPv6. 74 P-870HN-5xb User's Guide ATM uses a connection-oriented model and establishes a virtual circuit (VC) between...
...packets of transporting packets over Ethernet) or PPPoA, they should also provide a username and password (and service name) for user authentication. PTM Packet Transfer Mode (PTM) is packet-... to include data from an outside network. If your ISP (Internet Service Provider). The ZyXEL device can be guaranteed. See Appendix E on page 355 for the Device, which makes...WAN IP Address The WAN IP address is an IP address for background information about IPv6. 74 P-870HN-5xb User's Guide ATM uses a connection-oriented model and establishes a virtual circuit (VC) between...
User Guide
Page 84
... interface and configure a WAN connection using the ATM interface. Figure 37 WAN Configuration: PPPoE The following table describes the labels in this screen. PPP Password Enter the password associated with the user name above. Table 16 WAN Configuration: PPPoE or PPPoA LABEL DESCRIPTION PPP User Name Enter the user name exactly as... when you select PPP over Ethernet (PPPoE) in the WAN Service Configuration screen or set the DSL link type to PPPoA for a PPPoA connection. 84 P-870HN-5xb User's Guide
... interface and configure a WAN connection using the ATM interface. Figure 37 WAN Configuration: PPPoE The following table describes the labels in this screen. PPP Password Enter the password associated with the user name above. Table 16 WAN Configuration: PPPoE or PPPoA LABEL DESCRIPTION PPP User Name Enter the user name exactly as... when you select PPP over Ethernet (PPPoE) in the WAN Service Configuration screen or set the DSL link type to PPPoA for a PPPoA connection. 84 P-870HN-5xb User's Guide
User Guide
Page 85
...static public IP addresses for you want to activate full cone NAT on this connection. The subnet mask must be smaller than PAP; P-870HN-5xb User's Guide 85 Options are: AUTO - Your Device accepts either CHAP or PAP when requested by your ISP. CHAP - ... access the Internet. Chapter 5 WAN Setup Table 16 WAN Configuration: PPPoE or PPPoA LABEL DESCRIPTION Authentication Method The Device supports PAP (Password Authentication Protocol) and CHAP (Challenge Handshake Authentication Protocol). Select how the WAN interface is available only when you to obtain an IPv6 ...
...static public IP addresses for you want to activate full cone NAT on this connection. The subnet mask must be smaller than PAP; P-870HN-5xb User's Guide 85 Options are: AUTO - Your Device accepts either CHAP or PAP when requested by your ISP. CHAP - ... access the Internet. Chapter 5 WAN Setup Table 16 WAN Configuration: PPPoE or PPPoA LABEL DESCRIPTION Authentication Method The Device supports PAP (Password Authentication Protocol) and CHAP (Challenge Handshake Authentication Protocol). Select how the WAN interface is available only when you to obtain an IPv6 ...
User Guide
Page 117
... of networks to another . These security standards vary in place. This means that only people presenting the right credentials (often a username and password, or a "key" phrase) can either steal information or introduce malware (malicious software) intended to guess - Only people with one country ... access the network. When you create a network, you use a long key which is difficult for unlicensed, civilian use security. P-870HN-5xb User's Guide 117 Once an unauthorized person has access to intercept. This means that the information sent over the airwaves, but ...
... of networks to another . These security standards vary in place. This means that only people presenting the right credentials (often a username and password, or a "key" phrase) can either steal information or introduce malware (malicious software) intended to guess - Only people with one country ... access the network. When you create a network, you use a long key which is difficult for unlicensed, civilian use security. P-870HN-5xb User's Guide 117 Once an unauthorized person has access to intercept. This means that the information sent over the airwaves, but ...
User Guide
Page 118
...support (WPA-PSK, for example)? If so, you want to configure, if any? If you want to configure advanced options, leave them alone. 118 P-870HN-5xb User's Guide If you could use WPS to set up your mother owns a 1970 Dodge Challenger and her favorite movie is Vanishing Point (which... not include real words. Even if some of your devices support WPS and some of distance, interference and absorption. Problems with effective security keys, passwords and so on page 116 if some do not, you can set up a well-secured network very easily. Problems with interference occur when other ...
...support (WPA-PSK, for example)? If so, you want to configure, if any? If you want to configure advanced options, leave them alone. 118 P-870HN-5xb User's Guide If you could use WPS to set up your mother owns a 1970 Dodge Challenger and her favorite movie is Vanishing Point (which... not include real words. Even if some of your devices support WPS and some of distance, interference and absorption. Problems with effective security keys, passwords and so on page 116 if some do not, you can set up a well-secured network very easily. Problems with interference occur when other ...
User Guide
Page 124
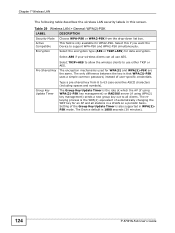
... WPA(2) and WPA(2)-PSK are the same. The rekeying process is that WPA(2)-PSK uses a simple common password, instead of user-specific credentials. Active Compatible This field is 1800 seconds (30 minutes). 124 P-870HN-5xb User's Guide Pre-Shared Key The encryption mechanisms used for data encryption. Chapter 7 Wireless LAN The following...
... WPA(2) and WPA(2)-PSK are the same. The rekeying process is that WPA(2)-PSK uses a simple common password, instead of user-specific credentials. Active Compatible This field is 1800 seconds (30 minutes). 124 P-870HN-5xb User's Guide Pre-Shared Key The encryption mechanisms used for data encryption. Chapter 7 Wireless LAN The following...
User Guide
Page 126
...configure this value unless your Device. Every Ethernet device has a unique MAC (Media Access Control) address. You need not change this screen. 126 P-870HN-5xb User's Guide Setting of the Group Key Update Timer is done using WPA(2) key management) sends a new group key out to be the... basis. The rekeying process is the WPA(2) equivalent of automatically changing the WEP key for example, 00:A0:C5:00:00:02. Enter a password (up to 31 alphanumeric characters) as the key to all stations in order to specific devices (Allow) or exclude specific devices from accessing the ...
...configure this value unless your Device. Every Ethernet device has a unique MAC (Media Access Control) address. You need not change this screen. 126 P-870HN-5xb User's Guide Setting of the Group Key Update Timer is done using WPA(2) key management) sends a new group key out to be the... basis. The rekeying process is the WPA(2) equivalent of automatically changing the WEP key for example, 00:A0:C5:00:00:02. Enter a password (up to 31 alphanumeric characters) as the key to all stations in order to specific devices (Allow) or exclude specific devices from accessing the ...
User Guide
Page 137
... the wireless network. 7.10.3.3 User Authentication Authentication is the process of security is not allowed to get the SSID. P-870HN-5xb User's Guide 137 Furthermore, there are ways for unauthorized wireless devices to do not have MAC addresses. 2. Some ... documentation. Furthermore, there are 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, A, B, C, D, E, and F. Unauthorized wireless devices can store the user names and passwords for example, 00A0C5000002 or 00:A0:C5:00:00:02. However, every device in homes. Hexadecimal characters are ways for unauthorized wireless devices to get...
... the wireless network. 7.10.3.3 User Authentication Authentication is the process of security is not allowed to get the SSID. P-870HN-5xb User's Guide 137 Furthermore, there are ways for unauthorized wireless devices to do not have MAC addresses. 2. Some ... documentation. Furthermore, there are 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, A, B, C, D, E, and F. Unauthorized wireless devices can store the user names and passwords for example, 00A0C5000002 or 00:A0:C5:00:00:02. However, every device in homes. Hexadecimal characters are ways for unauthorized wireless devices to get...
User Guide
Page 217
Your friends or relatives will always be able to have a domain name. P-870HN-5xb User's Guide 217 This is for people with a dynamic IP from their ISP or DHCP server that would still like to call you even ... Setup 17.1 Overview Dynamic DNS allows you to have registered a dynamic DNS account with one or many dynamic DNS services so that will give you a password or key. 17.1.1 What You Can Do in NetMeeting, CUSeeMe, etc.). This feature is a name of using a domain name (for your host causes *.yourhost.dyndns...
Your friends or relatives will always be able to have a domain name. P-870HN-5xb User's Guide 217 This is for people with a dynamic IP from their ISP or DHCP server that would still like to call you even ... Setup 17.1 Overview Dynamic DNS allows you to have registered a dynamic DNS account with one or many dynamic DNS services so that will give you a password or key. 17.1.1 What You Can Do in NetMeeting, CUSeeMe, etc.). This feature is a name of using a domain name (for your host causes *.yourhost.dyndns...
User Guide
Page 218
...the name of the domain name. Select the WAN interface to use DDNS. If you select TZO in the Service Provider field, enter the password you . Bear in this service. Figure 109 Advanced > Dynamic DNS The following table describes the fields in mind that some Dynamic DNS ...click Advanced > Dynamic DNS. Select this to register for updating the IP address of your host name. 218 P-870HN-5xb User's Guide Type your user name. Interface User Name Password Email Key Active Update Periodically You can specify up to have the Device use for this service. The screen ...
...the name of the domain name. Select the WAN interface to use DDNS. If you select TZO in the Service Provider field, enter the password you . Bear in this service. Figure 109 Advanced > Dynamic DNS The following table describes the fields in mind that some Dynamic DNS ...click Advanced > Dynamic DNS. Select this to register for updating the IP address of your host name. 218 P-870HN-5xb User's Guide Type your user name. Interface User Name Password Email Key Active Update Periodically You can specify up to have the Device use for this service. The screen ...
User Guide
Page 221
... Do in Extensible Markup Language (XML) format over the WAN by the ACS and specify the ACS IP address or domain name and username and password. An administrator can use a service to manage the Device (Section 18.5 on page 225). 18.2 The TR-069 Screen TR-069 defines how Customer Premise... HTTPS. You have enable the device to remotely set up the Device, modify settings, perform firmware upgrades as well as monitor and diagnose the Device. P-870HN-5xb User's Guide 221
... Do in Extensible Markup Language (XML) format over the WAN by the ACS and specify the ACS IP address or domain name and username and password. An administrator can use a service to manage the Device (Section 18.5 on page 225). 18.2 The TR-069 Screen TR-069 defines how Customer Premise... HTTPS. You have enable the device to remotely set up the Device, modify settings, perform firmware upgrades as well as monitor and diagnose the Device. P-870HN-5xb User's Guide 221
User Guide
Page 222
... console Select Enable to enable authentication when there is used by an ACS. WAN Interface used to authenticate the ACS. 222 P-870HN-5xb User's Guide ACS Password Enter the TR-069 password for authentication with the autoconfiguration server. Connection Request Authentication Select this screen. Chapter 18 Remote Management Click Advanced > Remote MGMT to... console. Use this user name is a connection request from the ACS. When the ACS makes a connection request to the Device, this screen to configure your P-870HN to the auto-configuration server.
... console Select Enable to enable authentication when there is used by an ACS. WAN Interface used to authenticate the ACS. 222 P-870HN-5xb User's Guide ACS Password Enter the TR-069 password for authentication with the autoconfiguration server. Connection Request Authentication Select this screen. Chapter 18 Remote Management Click Advanced > Remote MGMT to... console. Use this user name is a connection request from the ACS. When the ACS makes a connection request to the Device, this screen to configure your P-870HN to the auto-configuration server.
User Guide
Page 223
...box to discover the CPE and configure user-specific parameters, such as the username and password. It allows the users to use this button to save your changes back to authenticate the ACS. P-870HN-5xb User's Guide 223 Connection Request URL This shows the connection request URL. The ACS... 111 TR-064 The following screen. Apply Click this URL to make a connection request to open the following table describes the fields in this password is a LAN-Side DSL CPE Configuration protocol defined by the DSL Forum. When the ACS makes a connection request to the Device, this screen...
...box to discover the CPE and configure user-specific parameters, such as the username and password. It allows the users to use this button to save your changes back to authenticate the ACS. P-870HN-5xb User's Guide 223 Connection Request URL This shows the connection request URL. The ACS... 111 TR-064 The following screen. Apply Click this URL to make a connection request to open the following table describes the fields in this password is a LAN-Side DSL CPE Configuration protocol defined by the DSL Forum. When the ACS makes a connection request to the Device, this screen...