WGT624v3 Reference Manual
Page 9
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features ...Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10090-01, April 2005
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features ...Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10090-01, April 2005
WGT624v3 Reference Manual
Page 16
.... 802.11g Wireless Networking The WGT624 v3 wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your email address or email pager whenever a significant event occurs. 2-2 Introduction 202-10090-01, April 2005 Its firewall features include: ... logins. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be turned off -limits...
.... 802.11g Wireless Networking The WGT624 v3 wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your email address or email pager whenever a significant event occurs. 2-2 Introduction 202-10090-01, April 2005 Its firewall features include: ... logins. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be turned off -limits...
WGT624v3 Reference Manual
Page 33
...(SSID) to a different value. g only: Only 802.11g wireless stations can be legal to operate the router in a region other than the region shown here. Auto 108 Mbps: All 802.11g, 802.11b and NETGEAR 108 Mbps wireless stations can be used. Disable: no data encryption - WEP (Wired.... The default is not listed, please check with another nearby access point. • Mode: Select the desired wireless mode. Note: If you notice interference problems with your network. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure to follow these guidelines can be used....
...(SSID) to a different value. g only: Only 802.11g wireless stations can be legal to operate the router in a region other than the region shown here. Auto 108 Mbps: All 802.11g, 802.11b and NETGEAR 108 Mbps wireless stations can be used. Disable: no data encryption - WEP (Wired.... The default is not listed, please check with another nearby access point. • Mode: Select the desired wireless mode. Note: If you notice interference problems with your network. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure to follow these guidelines can be used....
WGT624v3 Reference Manual
Page 34
... key boxes will be identical on all PCs and Access Points in your network in the Passphrase box and click the Generate button to automatically configure the WEP Key(s). The Passphrase must be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level...
... key boxes will be identical on all PCs and Access Points in your network in the Passphrase box and click the Generate button to automatically configure the WEP Key(s). The Passphrase must be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level...
WGT624v3 Reference Manual
Page 117
... unlicensed radio spectrum at 2.5GHz. Wireless Networking Overview The WGT624 v3 wireless router conforms to another . This mode provides wireless connectivity to multiple wireless network devices within a fixed range or area of one access point, it will automatically back down from one Access Point domain to the Institute of Wireless networking. On an 802.11b or g wireless link, data is encoded using...
... unlicensed radio spectrum at 2.5GHz. Wireless Networking Overview The WGT624 v3 wireless router conforms to another . This mode provides wireless connectivity to multiple wireless network devices within a fixed range or area of one access point, it will automatically back down from one Access Point domain to the Institute of Wireless networking. On an 802.11b or g wireless link, data is encoded using...
WGT624v3 Reference Manual
Page 118
... Basic Service Set Identification (BSSID) is the easiest and least expensive way to set up a wireless network. thus, there is used . There is usually broadcast in the air from an access point. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are directly sent...
... Basic Service Set Identification (BSSID) is the easiest and least expensive way to set up a wireless network. thus, there is used . There is usually broadcast in the air from an access point. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are directly sent...
WGT624v3 Reference Manual
Page 119
....11 Station can associate with the access point or communicate with any available Access Point within range, regardless of authentication: Open System and Shared Key. • Open System Authentication allows any access points that the station and the access point have the same WEP Key to authenticate. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. With Shared...
....11 Station can associate with the access point or communicate with any available Access Point within range, regardless of authentication: Open System and Shared Key. • Open System Authentication allows any access points that the station and the access point have the same WEP Key to authenticate. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. With Shared...
WGT624v3 Reference Manual
Page 120
... default key to encrypt the challenge text, and sends the encrypted text to the station's default key. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The station sends an authentication request to the station. 3. The access point authenticates the station. 3. The access point compares the decrypted text with the original challenge text. This process is illustrated below...
... default key to encrypt the challenge text, and sends the encrypted text to the station's default key. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The station sends an authentication request to the station. 3. The access point authenticates the station. 3. The access point compares the decrypted text with the original challenge text. This process is illustrated below...
WGT624v3 Reference Manual
Page 121
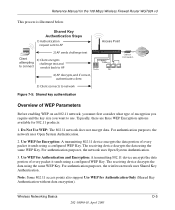
... 802.11 network does not encrypt data. Use WEP for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. The receiving device decrypts the data using a configured WEP Key. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Wireless Networking Basics D-5 202-10090-01, April 2005 For authentication purposes, the...
... 802.11 network does not encrypt data. Use WEP for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. The receiving device decrypts the data using a configured WEP Key. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Wireless Networking Basics D-5 202-10090-01, April 2005 For authentication purposes, the...
WGT624v3 Reference Manual
Page 122
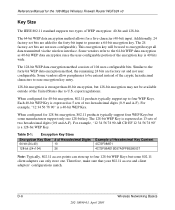
... Keys. Therefore, make sure that your 802.11 access and client adapters' configurations match. Reference Manual for a five-character (40-bit) input. The 64-bit WEP data encryption method allows for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports ... as 40-bit WEP data encryption since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Some vendors allow passphrases to be entered instead of two hexadecimal digits (0-9 and A-F)....
... Keys. Therefore, make sure that your 802.11 access and client adapters' configurations match. Reference Manual for a five-character (40-bit) input. The 64-bit WEP data encryption method allows for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports ... as 40-bit WEP data encryption since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Some vendors allow passphrases to be entered instead of two hexadecimal digits (0-9 and A-F)....
WGT624v3 Reference Manual
Page 123
... must also enter the same keys for the client adapter in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the 802.11 access points and all 802.11 devices that allow the maximum channel separation will communicate as long as the AP's WEP key ...WEP settings. In general, if your mobile clients will utilize frequency spectrum 12.5 MHz above and below . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on all of the 802.11 client adapters on the network must have different default...
... must also enter the same keys for the client adapter in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the 802.11 access points and all 802.11 devices that allow the maximum channel separation will communicate as long as the AP's WEP key ...WEP settings. In general, if your mobile clients will utilize frequency spectrum 12.5 MHz above and below . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on all of the 802.11 client adapters on the network must have different default...
WGT624v3 Reference Manual
Page 125
...108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on existing wireless devices to support WPA. With 802.11 WEP, all access points and client wireless...keys are cumbersome to WEP? The 802.11i standard was optional. NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key. WPA user authentication is ...
...108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on existing wireless devices to support WPA. With 802.11 WEP, all access points and client wireless...keys are cumbersome to WEP? The 802.11i standard was optional. NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key. WPA user authentication is ...
WGT624v3 Reference Manual
Page 126
... to WPA2 (IEEE 802.11i)? WPA/WPA2 addresses most of the known WEP vulnerabilities and is primarily intended for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to allow a migration strategy, but mixing WEP and WPA/WPA2 is communicated through WPA information elements in these elements includes ... support) • Support for specialized 802.11 VoIP phones), as well as enhanced encryption protocols, such as 802.1x and TKIP. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers).
... to WPA2 (IEEE 802.11i)? WPA/WPA2 addresses most of the known WEP vulnerabilities and is primarily intended for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to allow a migration strategy, but mixing WEP and WPA/WPA2 is communicated through WPA information elements in these elements includes ... support) • Support for specialized 802.11 VoIP phones), as well as enhanced encryption protocols, such as 802.1x and TKIP. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers).
WGT624v3 Reference Manual
Page 127
.... WPA/WPA2 features a robust key generation/management system that uses a statically configured pass phrase on both the stations and the access point. Temporal Key Integrity Protocol (TKIP) is used for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in the Beacon frames is used to wrap WEP in possession of each plaintext message to...
.... WPA/WPA2 features a robust key generation/management system that uses a statically configured pass phrase on both the stations and the access point. Temporal Key Integrity Protocol (TKIP) is used for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in the Beacon frames is used to wrap WEP in possession of each plaintext message to...
WGT624v3 Reference Manual
Page 128
...implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Note: For environments with Optional 802.1x Port Based Network Access Control TCP/IP Ports Closed Until ...Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802.1x Figure 4-6: WPA/WPA2 Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624...
...implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Note: For environments with Optional 802.1x Port Based Network Access Control TCP/IP Ports Closed Until ...Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802.1x Figure 4-6: WPA/WPA2 Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624...
WGT624v3 Reference Manual
Page 129
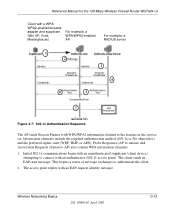
... with an authenticator (802.11 access point). Initial 802.1x communications begin with an unauthenticated supplicant (client device) attempting to authenticate the client. 2. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-... authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10090-01, April 2005 D-13 The client sends an EAP-start message. Probe Responses (AP ...
... with an authenticator (802.11 access point). Initial 802.1x communications begin with an unauthenticated supplicant (client device) attempting to authenticate the client. 2. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-... authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10090-01, April 2005 D-13 The client sends an EAP-start message. Probe Responses (AP ...
WGT624v3 Reference Manual
Page 130
... operating system or application "supplicant" software on the wired side of unicast encryption keys is synchronized between the wireless client and the wireless access point (AP). The client can specify any EAP type without needing to verify the client's identity. Reference Manual for... key used for the 108 Mbps Wireless Firewall Router WGT624 v3 3. For the global encryption key, WPA includes a facility (the Information Element) for the wireless AP to advertise the changed key to change encryption keys as often as a "pass through the use . The access point blocks all other EAP ...
... operating system or application "supplicant" software on the wired side of unicast encryption keys is synchronized between the wireless client and the wireless access point (AP). The client can specify any EAP type without needing to verify the client's identity. Reference Manual for... key used for the 108 Mbps Wireless Firewall Router WGT624 v3 3. For the global encryption key, WPA includes a facility (the Information Element) for the wireless AP to advertise the changed key to change encryption keys as often as a "pass through the use . The access point blocks all other EAP ...
WGT624v3 Reference Manual
Page 131
...Michael also provides replay protection. The MIC field is encrypted together with sequencing rules, and a re-keying mechanism. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to deploy better security while AES capable equipment is being detected by the receiver. ... support will not be required initially for WPA2 One of the NIC's hardware in both the station and the access point. Michael With 802.11 and WEP, data integrity is appended to prevent replay attacks. AES Support for Wi-Fi certification.
...Michael also provides replay protection. The MIC field is encrypted together with sequencing rules, and a re-keying mechanism. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to deploy better security while AES capable equipment is being detected by the receiver. ... support will not be required initially for WPA2 One of the NIC's hardware in both the station and the access point. Michael With 802.11 and WEP, data integrity is appended to prevent replay attacks. AES Support for Wi-Fi certification.
WGT624v3 Reference Manual
Page 132
...WPA2 Starting in WLAN security over WEP and has to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged To support the gradual transition of WEP and WPA/WPA2 clients... support the WPA standard. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? More than that obtained with a non-WPA/WPA2 network, and thus this may just prove that is no single security tactic is not without its vulnerabilities. NETGEAR, Inc.
...WPA2 Starting in WLAN security over WEP and has to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged To support the gradual transition of WEP and WPA/WPA2 clients... support the WPA standard. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? More than that obtained with a non-WPA/WPA2 network, and thus this may just prove that is no single security tactic is not without its vulnerabilities. NETGEAR, Inc.
WGT624v3 Reference Manual
Page 133
... the adapter's WPA capabilities and security configuration to the Wireless Zero Configuration service. For wireless network adapter drivers that supports WPA. Wireless Networking Basics 202-10090-01, April 2005 D-17 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must have their support of WPA/WPA2, wireless APs send the beacon frame with a new 802.11...
... the adapter's WPA capabilities and security configuration to the Wireless Zero Configuration service. For wireless network adapter drivers that supports WPA. Wireless Networking Basics 202-10090-01, April 2005 D-17 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must have their support of WPA/WPA2, wireless APs send the beacon frame with a new 802.11...