WGR614v9 Setup Manual
Page 19
... through your computers for wireless connectivity. 9. Getting to match the router's new settings. 8. If they have the same wireless network name (SSID) as the router. Router Setup Manual Figure 12 3. Select Wireless Settings under Setup on the main menu. 5. Check that the default SSID (service set identification key) is NETGEAR. Do one of your wireless connection when you will...
... through your computers for wireless connectivity. 9. Getting to match the router's new settings. 8. If they have the same wireless network name (SSID) as the router. Router Setup Manual Figure 12 3. Select Wireless Settings under Setup on the main menu. 5. Check that the default SSID (service set identification key) is NETGEAR. Do one of your wireless connection when you will...
WGR614v6 Reference Manual
Page 5
... Formats 1-1 How to Use This Manual 1-2 How to Print this Manual 1-3 Chapter 2 Introduction Key Features ...2-1 802.11g Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto...Router's Front Panel 2-6 The Router's Rear Panel 2-7 Chapter 3 Configuring the Internet and Wireless Settings Initial Configuration ...3-2 Logging Into Your Router 3-3 Changing Your Configuration 3-5 Internet Settings ...3-5 Wireless Settings ...3-9 Default Factory Settings 3-11 How to Bypass the Configuration Assistant 3-12 NETGEAR...
... Formats 1-1 How to Use This Manual 1-2 How to Print this Manual 1-3 Chapter 2 Introduction Key Features ...2-1 802.11g Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto...Router's Front Panel 2-6 The Router's Rear Panel 2-7 Chapter 3 Configuring the Internet and Wireless Settings Initial Configuration ...3-2 Logging Into Your Router 3-3 Changing Your Configuration 3-5 Internet Settings ...3-5 Wireless Settings ...3-9 Default Factory Settings 3-11 How to Bypass the Configuration Assistant 3-12 NETGEAR...
WGR614v6 Reference Manual
Page 9
... Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP Data Encryption D-2 802.11 Authentication D-3 Open System Authentication D-3 Shared Key Authentication D-4 Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are...
... Name: Extended Service Set Identification (ESSID D-2 Authentication and WEP Data Encryption D-2 802.11 Authentication D-3 Open System Authentication D-3 Shared Key Authentication D-4 Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are...
WGR614v6 Reference Manual
Page 15
... you with 4-port switch connects your purchase of the NETGEAR 54 Mbps Wireless Router WGR614 v6. The WGR614 v6 router provides the following features: • 802.11g wireless networking, with the ability to operate in 802.11 b-only, 802.11g-only, or 802.11b+g.... Introduction 2-1 202-10099-01, April 2005 This chapter describes the features of the NETGEAR® 54 Mbps Wireless Router WGR614 v6. With minimum setup, you from hackers. Key Features The 54 Mbps Wireless Router WGR614 v6 with multiple Web content filtering options, plus browsing activity reporting and instant alerts via...
... you with 4-port switch connects your purchase of the NETGEAR 54 Mbps Wireless Router WGR614 v6. The WGR614 v6 router provides the following features: • 802.11g wireless networking, with the ability to operate in 802.11 b-only, 802.11g-only, or 802.11b+g.... Introduction 2-1 202-10099-01, April 2005 This chapter describes the features of the NETGEAR® 54 Mbps Wireless Router WGR614 v6. With minimum setup, you from hackers. Key Features The 54 Mbps Wireless Router WGR614 v6 with multiple Web content filtering options, plus browsing activity reporting and instant alerts via...
WGR614v6 Reference Manual
Page 16
... against hacker attacks. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by MAC address. • Wireless network name broadcast can be generated manually or by...
... against hacker attacks. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by MAC address. • Wireless network name broadcast can be generated manually or by...
WGR614v6 Reference Manual
Page 24
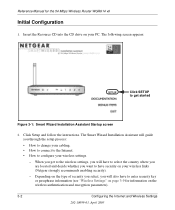
... to enter security key or passphrase information (see "Wireless Settings" on page 3-9 for the 54 Mbps Wireless Router WGR614 v6 Initial Configuration 1. The Smart Wizard Installation Assistant will guide you will have to select the country where you are located and decide whether you want to have to configure your wireless links (Netgear strongly recommends enabling security...
... to enter security key or passphrase information (see "Wireless Settings" on page 3-9 for the 54 Mbps Wireless Router WGR614 v6 Initial Configuration 1. The Smart Wizard Installation Assistant will guide you will have to select the country where you are located and decide whether you want to have to configure your wireless links (Netgear strongly recommends enabling security...
WGR614v6 Reference Manual
Page 32
...router. • Name (SSID): Enter a value of up to 32 alphanumeric characters. The options are: - If that you can manually or automatically program the four data encryption keys. b only: All 802.11b wireless stations can be used if they can operate in a region other than the region shown here. For example, NETGEAR...our web site for which operating frequency will be legal to operate the router in 802.11b mode. This field displays the region of "Automatic." Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Note: Failure to follow these guidelines can result in your network....
...router. • Name (SSID): Enter a value of up to 32 alphanumeric characters. The options are: - If that you can manually or automatically program the four data encryption keys. b only: All 802.11b wireless stations can be used if they can operate in a region other than the region shown here. For example, NETGEAR...our web site for which operating frequency will be legal to operate the router in 802.11b mode. This field displays the region of "Automatic." Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Note: Failure to follow these guidelines can result in your network....
WGR614v6 Reference Manual
Page 33
... hexadecimal digits (any of the four keys will automatically be 8 to 64 bit, then each of the four key boxes will be used and enter the matching WEP key information for the 54 Mbps Wireless Router WGR614 v6 • Automatic Key Generation (Passphrase): Enter a word or...configure the WEP Key(s). FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled Configuring the Internet and Wireless Settings 202-...
... hexadecimal digits (any of the four keys will automatically be 8 to 64 bit, then each of the four key boxes will be used and enter the matching WEP key information for the 54 Mbps Wireless Router WGR614 v6 • Automatic Key Generation (Passphrase): Enter a word or...configure the WEP Key(s). FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled Configuring the Internet and Wireless Settings 202-...
WGR614v6 Reference Manual
Page 66
Type the Password (or key) for your dynamic DNS service provider gave you. 5. Under normal circumstances, the router has adequate routing information after it has been configured for unusual cases such as yourhost...Routes to your dynamic DNS account. 6. From the Main Menu of your dynamic DNS provider allows the use of the Router 202-10099-01, April 2005 Type the Host Name (or domain name) that your dynamic DNS account. 7. Click ... interface, under Advanced, click on your configuration. Type the User Name for the 54 Mbps Wireless Router WGR614 v6 2. Reference Manual for your...
Type the Password (or key) for your dynamic DNS service provider gave you. 5. Under normal circumstances, the router has adequate routing information after it has been configured for unusual cases such as yourhost...Routes to your dynamic DNS account. 6. From the Main Menu of your dynamic DNS provider allows the use of the Router 202-10099-01, April 2005 Type the Host Name (or domain name) that your dynamic DNS account. 7. Click ... interface, under Advanced, click on your configuration. Type the User Name for the 54 Mbps Wireless Router WGR614 v6 2. Reference Manual for your...
WGR614v6 Reference Manual
Page 124
.... There is no access points, the Basic Service Set Identification (BSSID) is a thirty-two character (maximum) alphanumeric key identifying the name of the wireless local area network. The ESSID is no structure or fixed points to the network - Authentication and WEP Data Encryption The absence of Service ... sometimes can join any network and receive any other , all devices must be referred to as SSID. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are brought together as the stations are within range ...
.... There is no access points, the Basic Service Set Identification (BSSID) is a thirty-two character (maximum) alphanumeric key identifying the name of the wireless local area network. The ESSID is no structure or fixed points to the network - Authentication and WEP Data Encryption The absence of Service ... sometimes can join any network and receive any other , all devices must be referred to as SSID. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are brought together as the stations are within range ...
WGR614v6 Reference Manual
Page 125
....11 Authentication The 802.11 standard defines several services that govern how two 802.11 devices communicate. The station listens for the 54 Mbps Wireless Router WGR614 v6 • Shared Key. These two authentication procedures are in to authenticate. The station sends an authentication request to the access point. 7. The station sends an authentication...
....11 Authentication The 802.11 standard defines several services that govern how two 802.11 devices communicate. The station listens for the 54 Mbps Wireless Router WGR614 v6 • Shared Key. These two authentication procedures are in to authenticate. The station sends an authentication request to the access point. 7. The station sends an authentication...
WGR614v6 Reference Manual
Page 126
... the access point and joins the network. The station uses its configured WEP Key that corresponds to communicate with either the 802.11 network or Ethernet network. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 2. The station sends an authentication request to the network. If the ...decrypted text does not match the original challenge text (the access point and station do not share the same WEP Key), then the access point will refuse ...
... the access point and joins the network. The station uses its configured WEP Key that corresponds to communicate with either the 802.11 network or Ethernet network. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 2. The station sends an authentication request to the network. If the ...decrypted text does not match the original challenge text (the access point and station do not share the same WEP Key), then the access point will refuse ...
WGR614v6 Reference Manual
Page 127
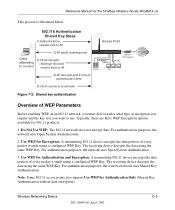
... Encryption: A transmitting 802.11 device encrypts the data portion of encryption you require and the key size you want to use. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting...
... Encryption: A transmitting 802.11 device encrypts the data portion of encryption you require and the key size you want to use. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 This process is illustrated below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting...
WGR614v6 Reference Manual
Page 128
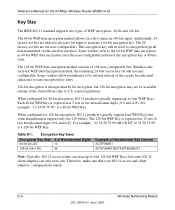
...-bit (24+40) 10 128-bit (24+104) 26 Example of the cryptic hexadecimal characters to ease encryption key entry. 128-bit encryption is a 40-bit WEP Key. When configured for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). Each 40-bit...
...-bit (24+40) 10 128-bit (24+104) 26 Example of the cryptic hexadecimal characters to ease encryption key entry. 128-bit encryption is a 40-bit WEP Key. When configured for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). Each 40-bit...
WGR614v6 Reference Manual
Page 129
... channel 2) in the same general vicinity will interfere with each other words, the AP can use WEP key 3 as the keys are listed in the same order. Wireless Channels The wireless frequencies used in 802.11b/g networks are in the ISM (Industrial, Scientific, and Medical) band between ...MHz 2404.5 MHz - 2429.5 MHz 2409.5 MHz - 2434.5 MHz Wireless Networking Basics D-7 202-10099-01, April 2005 Note: Whatever keys you enter for an AP, you must also enter the same keys for the 54 Mbps Wireless Router WGR614 v6 WEP Configuration Options The WEP settings must have the same WEP ...
... channel 2) in the same general vicinity will interfere with each other words, the AP can use WEP key 3 as the keys are listed in the same order. Wireless Channels The wireless frequencies used in 802.11b/g networks are in the ISM (Industrial, Scientific, and Medical) band between ...MHz 2404.5 MHz - 2429.5 MHz 2409.5 MHz - 2434.5 MHz Wireless Networking Basics D-7 202-10099-01, April 2005 Note: Whatever keys you enter for an AP, you must also enter the same keys for the 54 Mbps Wireless Router WGR614 v6 WEP Configuration Options The WEP settings must have the same WEP ...
WGR614v6 Reference Manual
Page 131
...offer system administrators no effective method to WEP? NETGEAR is optional. TKIP replaces WEP with a sniffing tool can monitor your network for 802.1x authentication is that the keys are cumbersome to IETF's RFC 2284. Wireless Networking Basics D-9 202-10099-01, April 2005... WEP encryption is implementing WPA and WPA2 on existing wireless devices to support WPA. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data ...
...offer system administrators no effective method to WEP? NETGEAR is optional. TKIP replaces WEP with a sniffing tool can monitor your network for 802.1x authentication is that the keys are cumbersome to IETF's RFC 2284. Wireless Networking Basics D-9 202-10099-01, April 2005... WEP encryption is implementing WPA and WPA2 on existing wireless devices to support WPA. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data ...
WGR614v6 Reference Manual
Page 132
These features were either not yet ready for the 54 Mbps Wireless Router WGR614 v6 How Does WPA Compare to WPA2 (IEEE 802.11i)? Michael message integrity code (MIC) - This infrastructure includes stations, access points, and authentication servers (... required hardware upgrades to implement. What are included in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - Temporal Key Integrity Protocol (TKIP) - The RADIUS server holds (or has access to) user credentials (for a mixture of WPA and WPA2 Security? The following ...
These features were either not yet ready for the 54 Mbps Wireless Router WGR614 v6 How Does WPA Compare to WPA2 (IEEE 802.11i)? Michael message integrity code (MIC) - This infrastructure includes stations, access points, and authentication servers (... required hardware upgrades to implement. What are included in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - Temporal Key Integrity Protocol (TKIP) - The RADIUS server holds (or has access to) user credentials (for a mixture of WPA and WPA2 Security? The following ...
WGR614v6 Reference Manual
Page 133
... privacy functions. TKIP includes a message integrity code (MIC) at the end of each plaintext message to access the network. • Key management. Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). The supplicant in the station uses the authentication and ... that uses a statically configured pass phrase on both the stations and the access point. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 The primary information conveyed in many home and small office environments will not be available nor desirable. Possible authentication methods ...
... privacy functions. TKIP includes a message integrity code (MIC) at the end of each plaintext message to access the network. • Key management. Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). The supplicant in the station uses the authentication and ... that uses a statically configured pass phrase on both the stations and the access point. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 The primary information conveyed in many home and small office environments will not be available nor desirable. Possible authentication methods ...
WGR614v6 Reference Manual
Page 134
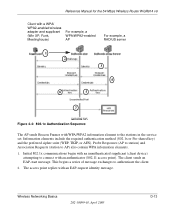
...authentication server, which employs mutual authentication so that 802.1x does not provide the actual authentication mechanisms. When using pre-shared key or 802.1x Figure 4-3: WPA/WPA2 Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, ...authentication. D-12 202-10099-01, April 2005 Wireless Networking Basics Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA/WPA2 Authentication: Enterprise-level User ...
...authentication server, which employs mutual authentication so that 802.1x does not provide the actual authentication mechanisms. When using pre-shared key or 802.1x Figure 4-3: WPA/WPA2 Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, ...authentication. D-12 202-10099-01, April 2005 Wireless Networking Basics Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA/WPA2 Authentication: Enterprise-level User ...
WGR614v6 Reference Manual
Page 135
Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10099-01, April 2005 D-13 Initial 802.1x communications begin with an unauthenticated supplicant... message exchanges to the stations in the service set. The client sends an EAP-start message. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3...
Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10099-01, April 2005 D-13 Initial 802.1x communications begin with an unauthenticated supplicant... message exchanges to the stations in the service set. The client sends an EAP-start message. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3...