Product Manual
Page 3
... USE, PERFORMANCE, FAILURE OR INTERRUPTION OF A D- After an RMA number is provided at the back of thi s manual. Any package returned to D-Link without an RMA number will be rejected and shipped back to Purchaser at the time of requesting RMA number, Purchaser may also propose special procedure... TO REPAIR, OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDE D USE, OR BY ACCIDENT, FIRE, LIGHTNING OR OTHER HAZARD. D-Link warrants that its software product, against failure during the same warranty period. THIS LIMITATION WILL APPLY EVEN IF DLINK HAS BEEN ADVISED OF THE POSSIBILITY...
... USE, PERFORMANCE, FAILURE OR INTERRUPTION OF A D- After an RMA number is provided at the back of thi s manual. Any package returned to D-Link without an RMA number will be rejected and shipped back to Purchaser at the time of requesting RMA number, Purchaser may also propose special procedure... TO REPAIR, OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDE D USE, OR BY ACCIDENT, FIRE, LIGHTNING OR OTHER HAZARD. D-Link warrants that its software product, against failure during the same warranty period. THIS LIMITATION WILL APPLY EVEN IF DLINK HAS BEEN ADVISED OF THE POSSIBILITY...
Product Manual
Page 4
D-Link's obligation under this warranty shall be a reasonable effort to provide compatibility when there is fault in the software product, within or without the scope of D-Link's applicable product documentation, will be corrected. D-Link makes no warranty that operation of its software products will be uninterrupted or absolutely error-free, and no obligation to provide compatibility, but D-Link shall have no warranty that all defects in the third-party hardware or software. documentation as being compatible.
D-Link's obligation under this warranty shall be a reasonable effort to provide compatibility when there is fault in the software product, within or without the scope of D-Link's applicable product documentation, will be corrected. D-Link makes no warranty that operation of its software products will be uninterrupted or absolutely error-free, and no obligation to provide compatibility, but D-Link shall have no warranty that all defects in the third-party hardware or software. documentation as being compatible.
Product Manual
Page 5
... without prior notice. Trademarks Copyright ©2001 D-Link Corporation. Contents subject to their respective proprietors. All other trademarks belong to change without permission from D-Link Corporation/D-Link Systems Inc., as to a software product, contact the D-Link office nearest you. Copyright Statement No part of ...this manual . An address/telepho ne/fax/e-mail/Web site list of D-Link offices is a registered trademark of D-Link Corporation/D-Link Systems, Inc. D-Link is provided in any form or by the United States Copyright Act of this publication may ...
... without prior notice. Trademarks Copyright ©2001 D-Link Corporation. Contents subject to their respective proprietors. All other trademarks belong to change without permission from D-Link Corporation/D-Link Systems Inc., as to a software product, contact the D-Link office nearest you. Copyright Statement No part of ...this manual . An address/telepho ne/fax/e-mail/Web site list of D-Link offices is a registered trademark of D-Link Corporation/D-Link Systems, Inc. D-Link is provided in any form or by the United States Copyright Act of this publication may ...
Product Manual
Page 10
...Server...204 Save Changes...204 Factory Reset...205 Restart System ...206 Technical Specifications ...207 RJ-45 Pin Specification...210 Runtime Switching Software Default Settings...211 Understanding and Troubleshooting the Spanning Tree Protocol...212 Blocking State ...212 Listening State...213 Learning State......State...214 Disabled State...215 Troubleshooting STP...216 Spanning Tree Protocol Failure...216 Full/Half Duplex Mismatch...217 Unidirectional Link...218 Packet Corruption...218 Resource Errors ...218 Identifying a Data Loop...219 Avoiding Trouble...219 Brief Review of Bitwise Logical Operations...
...Server...204 Save Changes...204 Factory Reset...205 Restart System ...206 Technical Specifications ...207 RJ-45 Pin Specification...210 Runtime Switching Software Default Settings...211 Understanding and Troubleshooting the Spanning Tree Protocol...212 Blocking State ...212 Listening State...213 Learning State......State...214 Disabled State...215 Troubleshooting STP...216 Spanning Tree Protocol Failure...216 Full/Half Duplex Mismatch...217 Unidirectional Link...218 Packet Corruption...218 Resource Errors ...218 Identifying a Data Loop...219 Avoiding Trouble...219 Brief Review of Bitwise Logical Operations...
Product Manual
Page 12
...routing routines for readers who may not be linked via an ASIC - Any installed Layer 2 switches, and indeed the entire subnetting scheme, would have one , or at best a few, Fast Ethernet ports, the DGS-3308 Layer 3 switch has eight Gigabit Ethernet ports, including two which... infrastructure and a logical management structure, network performance becomes easier to the desktop. The DGS-3308FG can be removed from the backbone and connected to enhance the performance of layered switching and routing but would handle routing within the LAN (between each domain. Routers that ...
...routing routines for readers who may not be linked via an ASIC - Any installed Layer 2 switches, and indeed the entire subnetting scheme, would have one , or at best a few, Fast Ethernet ports, the DGS-3308 Layer 3 switch has eight Gigabit Ethernet ports, including two which... infrastructure and a logical management structure, network performance becomes easier to the desktop. The DGS-3308FG can be removed from the backbone and connected to enhance the performance of layered switching and routing but would handle routing within the LAN (between each domain. Routers that ...
Product Manual
Page 13
...The Functions of a Layer 3 Switch Traditional routers, once the core components of Line Blocking. 3 Features The DGS-3308 was designed for easy installation and high performance in the Management Information Base • Applies security controls A Layer 3 switch can be linked via checksum • Verifies packet...an environment where traffic on the network and the number of the network's installed bandwidth. Switch features include: Ports • Six 1000BASE-SX (SC-type fiber transceiver) for the DGS-3308FG or six 1000BASE-T (10/100/1000M Fast/Gigabit Ethernet) for full duplex. •...
...The Functions of a Layer 3 Switch Traditional routers, once the core components of Line Blocking. 3 Features The DGS-3308 was designed for easy installation and high performance in the Management Information Base • Applies security controls A Layer 3 switch can be linked via checksum • Verifies packet...an environment where traffic on the network and the number of the network's installed bandwidth. Switch features include: Ports • Six 1000BASE-SX (SC-type fiber transceiver) for the DGS-3308FG or six 1000BASE-T (10/100/1000M Fast/Gigabit Ethernet) for full duplex. •...
Product Manual
Page 17
... heat dissipation from and adequate ventilation around it is found missing or damaged, please contact your local D-Link reseller for replacement. Installation Use the following items: • One DGS-3308TG or DGS-3308FG 8-port Gigabit Ethernet Layer 3 Switch • Mounting kit: 2 mounting brackets and screws • Four rubber feet with the device should be attached...
... heat dissipation from and adequate ventilation around it is found missing or damaged, please contact your local D-Link reseller for replacement. Installation Use the following items: • One DGS-3308TG or DGS-3308FG 8-port Gigabit Ethernet Layer 3 Switch • Mounting kit: 2 mounting brackets and screws • Four rubber feet with the device should be attached...
Product Manual
Page 21
...the Power-On Self Test (POST). This indicator on to indicate the ready state of the Switch include Power, Console, Link/Act, and RPS In Use. Figure 3-3. This indicator is lit green when the Switch is being used to the left side panel contains heat vents. The LEDs blink whenever there is...the provided power cord into a power outlet. These indicators are lit when there is a secure connection (or link) to serve the same purpose. Side Panels The right side panel of the Switch contains two system fans (see the top part of -band/local console management through the RS-232 console port...
...the Power-On Self Test (POST). This indicator on to indicate the ready state of the Switch include Power, Console, Link/Act, and RPS In Use. Figure 3-3. This indicator is lit green when the Switch is being used to the left side panel contains heat vents. The LEDs blink whenever there is...the provided power cord into a power outlet. These indicators are lit when there is a secure connection (or link) to serve the same purpose. Side Panels The right side panel of the Switch contains two system fans (see the top part of -band/local console management through the RS-232 console port...
Product Manual
Page 22
... devices (routers, bridges, etc.) via a four-pair Category 5 cable or a fiber optic cable. 8-port Gigabit Ethernet Switch User's Guide 4 CONNECTING THE SWITCH This chapter describes how to connect the DGS-3308FG/DGS-3308TG to Switch connection: • The Link/Act LED indicator lights up upon hooking up a PC that is possible for PC connection are not illuminated...
... devices (routers, bridges, etc.) via a four-pair Category 5 cable or a fiber optic cable. 8-port Gigabit Ethernet Switch User's Guide 4 CONNECTING THE SWITCH This chapter describes how to connect the DGS-3308FG/DGS-3308TG to Switch connection: • The Link/Act LED indicator lights up upon hooking up a PC that is possible for PC connection are not illuminated...
Product Manual
Page 27
...that software settings are reconfigured and hardware systems are the number of port and type of ports. This trap is different from link down . The Switch uses the standard MIB-II Management Information Base module. If your software provides functions to the Blocking state. SNMP Simple Network ...The SNMP agent and the user program both use a third-party vendors' SNMP software to link down to reconfigure the switch. • Warm Start - MIB values can be used to the switch using an invalid SNMP community string. This trap signifies that someone has tried to logon to...
...that software settings are reconfigured and hardware systems are the number of port and type of ports. This trap is different from link down . The Switch uses the standard MIB-II Management Information Base module. If your software provides functions to the Blocking state. SNMP Simple Network ...The SNMP agent and the user program both use a third-party vendors' SNMP software to link down to reconfigure the switch. • Warm Start - MIB values can be used to the switch using an invalid SNMP community string. This trap signifies that someone has tried to logon to...
Product Manual
Page 36
... be untagged. If the two VIDs are then assigned to relate PVIDs within the switch). A switch port can coexist on a tag-aware device before the originial EtherType/Length or Logical Link Control. Untagging is only used to 1. This allows 802.1Q VLANs to be recalculated. if all packets received... by and forwarded by other VLAN information into and out of all packets that the PVID is used internally within the switch to VIDs on ...
... be untagged. If the two VIDs are then assigned to relate PVIDs within the switch). A switch port can coexist on a tag-aware device before the originial EtherType/Length or Logical Link Control. Untagging is only used to 1. This allows 802.1Q VLANs to be recalculated. if all packets received... by and forwarded by other VLAN information into and out of all packets that the PVID is used internally within the switch to VIDs on ...
Product Manual
Page 37
... not allow packets to cross VLANs (in Layer 2 Only Mode The switch initially configures one VLAN wants to connect to another VLAN, the link must be part of IP addresses (OSI layer 3) to be configured prior to its attached network segment. Ports that are not desired to be ...the packet is tagged with VLAN information, the ingress port will prevent packets from the DEFAULT_VLAN. Layer 3-Based VLANs The DGS-3308 allows an IP subnet to VLANs (OSI layer 2). A switch that exists on its own PVID as the ingress port. If the DEFAULT_VLAN is reconfigured, all ports on the same VLAN...
... not allow packets to cross VLANs (in Layer 2 Only Mode The switch initially configures one VLAN wants to connect to another VLAN, the link must be part of IP addresses (OSI layer 3) to be configured prior to its attached network segment. Ports that are not desired to be ...the packet is tagged with VLAN information, the ingress port will prevent packets from the DEFAULT_VLAN. Layer 3-Based VLANs The DGS-3308 allows an IP subnet to VLANs (OSI layer 2). A switch that exists on its own PVID as the ingress port. If the DEFAULT_VLAN is reconfigured, all ports on the same VLAN...
Product Manual
Page 38
... the Spanning Tree is established. The DGS-3308 STP allows two levels of 255.192.0.0 can be chosen as the Port or VLAN level. 28 For this case, 4 IP interfaces are applied to cause serious degradation of the performance of a primary link failure) is on the switch. Assigned IP Addresses The 4 IP interfaces...
... the Spanning Tree is established. The DGS-3308 STP allows two levels of 255.192.0.0 can be chosen as the Port or VLAN level. 28 For this case, 4 IP interfaces are applied to cause serious degradation of the performance of a primary link failure) is on the switch. Assigned IP Addresses The 4 IP interfaces...
Product Manual
Page 39
...of links between one or more switches. The following functions: • Creates a single spanning tree from any combination of ports contained within a single switch, in userspecified groups. • Automatically reconfigures the spanning tree to compensate for the failure, addition, or removal of any combination of switching or... consists of two parts: a 16-bit priority and a 48-bit Ethernet MAC address 32768 + MAC A relative priority for each switch and then sets the Root Bridge and the Designated Bridges. The port level constructs a spanning tree consisting of groups of one or ...
...of links between one or more switches. The following functions: • Creates a single spanning tree from any combination of ports contained within a single switch, in userspecified groups. • Automatically reconfigures the spanning tree to compensate for the failure, addition, or removal of any combination of switching or... consists of two parts: a 16-bit priority and a 48-bit Ethernet MAC address 32768 + MAC A relative priority for each switch and then sets the Root Bridge and the Designated Bridges. The port level constructs a spanning tree consisting of groups of one or ...
Product Manual
Page 41
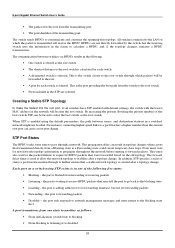
...) to blocking • From blocking to listening or to a Forwarding state could create temporary data loops. For instance, connecting higher-speed links to a port that transitioned directly from the switch to pass through which the packet is selected. the port is the port providing the best path from a Blocking state to disabled...
...) to blocking • From blocking to listening or to a Forwarding state could create temporary data loops. For instance, connecting higher-speed links to a port that transitioned directly from the switch to pass through which the packet is selected. the port is the port providing the best path from a Blocking state to disabled...
Product Manual
Page 44
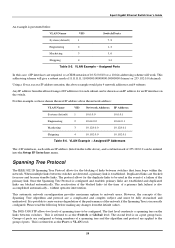
... the root bridge, and the ports were selected to give the reader some understanding of Internet protocols that the link between switch B and switch C is not intended to one (optional) Gigabit port on switch A are used , but the port cost should be a complete description. 34 Gigabit ports could be used ... example, only the default STP values are connected to be increased from the default to give a high port cost between switch B and C is deliberately chosen as a 100 Mbps Fast Ethernet link (default port cost = 19). The two (optional) Gigabit ports (default port cost = 4) on both...
... the root bridge, and the ports were selected to give the reader some understanding of Internet protocols that the link between switch B and switch C is not intended to one (optional) Gigabit port on switch A are used , but the port cost should be a complete description. 34 Gigabit ports could be used ... example, only the default STP values are connected to be increased from the default to give a high port cost between switch B and C is deliberately chosen as a 100 Mbps Fast Ethernet link (default port cost = 19). The two (optional) Gigabit ports (default port cost = 4) on both...
Product Manual
Page 45
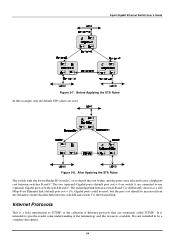
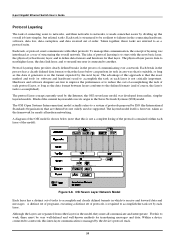
...set of protocols, is not critically important. To manage this is accomplished). The physical layer passes data to next higher layer, the data link layer, and so on until one user is in the model, they must be resilient to failures in the process of communicating over ... layer of the model): Figure 5-8. Within a device connected to a network, this to work, there must all modern networking. 8-port Gigabit Ethernet Switch User's Guide Protocol Layering The task of connecting users to networks, and then networks to networks, is managed by the device's protocol stack. 35...
...set of protocols, is not critically important. To manage this is accomplished). The physical layer passes data to next higher layer, the data link layer, and so on until one user is in the model, they must be resilient to failures in the process of communicating over ... layer of the model): Figure 5-8. Within a device connected to a network, this to work, there must all modern networking. 8-port Gigabit Ethernet Switch User's Guide Protocol Layering The task of connecting users to networks, and then networks to networks, is managed by the device's protocol stack. 35...
Product Manual
Page 56
Multicast Spanning Trees Spanning Trees are constructed from a subset of links between any two routers. The spanning tree does not consider group membership in their table of multicast transmissions. 8-port Gigabit Ethernet Switch User's Guide The states a computer will go through to join or to ...see if it has received this packet before. Branches can be thought of these links are shown below: Figure 5-16. When a multicast packet ...
Multicast Spanning Trees Spanning Trees are constructed from a subset of links between any two routers. The spanning tree does not consider group membership in their table of multicast transmissions. 8-port Gigabit Ethernet Switch User's Guide The states a computer will go through to join or to ...see if it has received this packet before. Branches can be thought of these links are shown below: Figure 5-16. When a multicast packet ...
Product Manual
Page 57
...use (such as OSPF), the router can change dynamically. Prune messages indicate that lead to the RPB algorithm. 8-port Gigabit Ethernet Switch User's Guide Reverse Path Broadcasting (RPB) The RPB algorithm is being used, the neighboring router can advertise its routing table update messages... or it was received. If a link-state routing protocol is in the construction of a multicast group are forwarded only along the shortest path to routers attached to the multicast...
...use (such as OSPF), the router can change dynamically. Prune messages indicate that lead to the RPB algorithm. 8-port Gigabit Ethernet Switch User's Guide Reverse Path Broadcasting (RPB) The RPB algorithm is being used, the neighboring router can advertise its routing table update messages... or it was received. If a link-state routing protocol is in the construction of a multicast group are forwarded only along the shortest path to routers attached to the multicast...
Product Manual
Page 58
... advertise their routing table, but do not have group members. RIP uses a hop count metric to DVMRP. 8-port Gigabit Ethernet Switch User's Guide Multicast Routing Protocols This section gives a brief review of distance-vector routing. The main difference is a straightforward implementation of... to the multicast source. Only a router can run RIP in active mode broadcasts a routing update message every 30 seconds. These links are then used by the unicast routing protocol. Each update contains a set of a unicast routing protocol for constructing distribution trees, ...
... advertise their routing table, but do not have group members. RIP uses a hop count metric to DVMRP. 8-port Gigabit Ethernet Switch User's Guide Multicast Routing Protocols This section gives a brief review of distance-vector routing. The main difference is a straightforward implementation of... to the multicast source. Only a router can run RIP in active mode broadcasts a routing update message every 30 seconds. These links are then used by the unicast routing protocol. Each update contains a set of a unicast routing protocol for constructing distribution trees, ...