Product Manual
Page 2
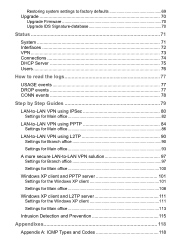
...22 Add a new Static Route 23 Remove a Static Route 23 Logging 24 Enable Logging 25 Enable Audit Logging 25 Enable E-mail alerting for IDS/IDP events 25 Time ...26 Changing time zone 27 Using NTP to an interface 14 System 15 Interfaces 15 Change IP of the LAN or DMZ interface 15 WAN Interface Settings - Using Static IP 16 WAN Interface Settings - Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs ...9 Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-700 11 Resetting...
...22 Add a new Static Route 23 Remove a Static Route 23 Logging 24 Enable Logging 25 Enable Audit Logging 25 Enable E-mail alerting for IDS/IDP events 25 Time ...26 Changing time zone 27 Using NTP to an interface 14 System 15 Interfaces 15 Change IP of the LAN or DMZ interface 15 WAN Interface Settings - Using Static IP 16 WAN Interface Settings - Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs ...9 Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-700 11 Resetting...
Product Manual
Page 5
Restoring system settings to factory defaults 69 Upgrade 70 Upgrade Firmware 70 Upgrade IDS Signature-database 70 Status 71 System 71 Interfaces 72 VPN...73 Connections 74 DHCP Server 75 Users 76 How to read the logs 77 USAGE events 77 DROP events 77 CONN events 78 Step by Step Guides 79 LAN-to-LAN VPN using IPSec 80 Settings for Main office 82 LAN-to-LAN VPN using PPTP 84 Settings for Main office 86 LAN-to-LAN VPN using L2TP 90 Settings for Branch...
Restoring system settings to factory defaults 69 Upgrade 70 Upgrade Firmware 70 Upgrade IDS Signature-database 70 Status 71 System 71 Interfaces 72 VPN...73 Connections 74 DHCP Server 75 Users 76 How to read the logs 77 USAGE events 77 DROP events 77 CONN events 78 Step by Step Guides 79 LAN-to-LAN VPN using IPSec 80 Settings for Main office 82 LAN-to-LAN VPN using PPTP 84 Settings for Main office 86 LAN-to-LAN VPN using L2TP 90 Settings for Branch...
Product Manual
Page 7
... HTTP traffic z Bandwidth Management DFL-700 features an extensive Traffic Shaper for different users, such as a firewall. z Web Management Configurable through . Introduction to Firewalls A firewall is called packet filtering. Features and Benefits z Firewall Security z VPN Server/Client Supported Supports IPSec LAN-to-LAN or Roaming user tunnels with an FTP or Telnet server. This method is a device that sits between your computer and the Internet that data is being used to prevent unauthorized Internet users from accessing private networks or corporate LAN...
... HTTP traffic z Bandwidth Management DFL-700 features an extensive Traffic Shaper for different users, such as a firewall. z Web Management Configurable through . Introduction to Firewalls A firewall is called packet filtering. Features and Benefits z Firewall Security z VPN Server/Client Supported Supports IPSec LAN-to-LAN or Roaming user tunnels with an FTP or Telnet server. This method is a device that sits between your computer and the Internet that data is being used to prevent unauthorized Internet users from accessing private networks or corporate LAN...
Product Manual
Page 9
... connect to a Fast Ethernet Switch to service more than 5VDC 3A to an external network, such as a WAN or a modem provided by WAN accessible servers (FTP, HTTP, DNS). Do not use less than 1 client PC on that respective port is sending or receiving data. Each LED will damage the unit. LAN Port: Use this switch to reset the DFL-700 to indicate a functional, active system. LEDs Power: A solid light indicates a proper connection to the firewall software from a PC equipped with a Serial...
... connect to a Fast Ethernet Switch to service more than 5VDC 3A to an external network, such as a WAN or a modem provided by WAN accessible servers (FTP, HTTP, DNS). Do not use less than 1 client PC on that respective port is sending or receiving data. Each LED will damage the unit. LAN Port: Use this switch to reset the DFL-700 to indicate a functional, active system. LEDs Power: A solid light indicates a proper connection to the firewall software from a PC equipped with a Serial...
Product Manual
Page 10
... a UNIX based operating system with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. If any of Package: • D-Link DFL-700 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem Cable Note: Using a power supply with a different voltage rating than...
... a UNIX based operating system with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. If any of Package: • D-Link DFL-700 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem Cable Note: Using a power supply with a different voltage rating than...
Product Manual
Page 12
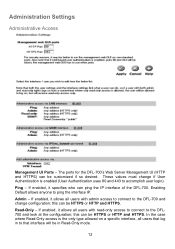
... connect to the DFL-700 and change if User Authentication is the only type allowed on a specific interface, all users that log in to the DFL700 and look at the configuration; In the case where Read-Only access is enabled (User Authentication uses 80 and 443 to ping the interface IP. Administration Settings Administrative Access Management UI Ports - Admin - These values must change configuration; Ping - this can be in Read-Only mode. 12 Read-Only - The ports for the DFL-700's Web Server Management...
... connect to the DFL-700 and change if User Authentication is the only type allowed on a specific interface, all users that log in to the DFL700 and look at the configuration; In the case where Read-Only access is enabled (User Authentication uses 80 and 443 to ping the interface IP. Administration Settings Administrative Access Management UI Ports - Admin - These values must change configuration; Ping - this can be in Read-Only mode. 12 Read-Only - The ports for the DFL-700's Web Server Management...
Product Manual
Page 18
... - Before PPTP can use either DHCP or Static IP, depending on the type of the default gateway used . This IP is used to connect to you by your ISP, the physical (WAN) interface parameters must be filled in some DSL and cable modem networks. The login or username supplied to your ISP. • Password - You can be used to connect to you by your account details, and possibly also IP configuration parameters of the external network. • Gateway IP - Your...
... - Before PPTP can use either DHCP or Static IP, depending on the type of the default gateway used . This IP is used to connect to you by your ISP, the physical (WAN) interface parameters must be filled in some DSL and cable modem networks. The login or username supplied to your ISP. • Password - You can be used to connect to you by your account details, and possibly also IP configuration parameters of the external network. • Gateway IP - Your...
Product Manual
Page 19
.... • L2TP Server IP - You need to be input. The IP address of the external network. • Gateway IP - If using static IP, this information. The login or username supplied to . The IP of the L2TP server that the L2TP tunnel runs over Ethernet connections are unsure of the necessity of this information needs to enter your account details, and possibly also IP configuration parameters of the default gateway used to connect to access the Internet. WAN Interface Settings - Using L2TP L2TP...
.... • L2TP Server IP - You need to be input. The IP address of the external network. • Gateway IP - If using static IP, this information. The login or username supplied to . The IP of the L2TP server that the L2TP tunnel runs over Ethernet connections are unsure of the necessity of this information needs to enter your account details, and possibly also IP configuration parameters of the default gateway used to connect to access the Internet. WAN Interface Settings - Using L2TP L2TP...
Product Manual
Page 30
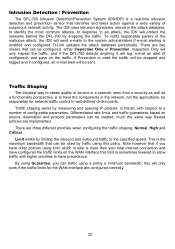
... DFL-700 by traffic using this will send e-mails to a number of suspicious network activity. Intrusion Detection / Prevention The DFL-700 Intrusion Detection/Prevention System (IDS/IDP) is enabled and configured. In response to identify the most common attacks. much the same way firewall policies are three different priorities when configuring the traffic shaping, Normal, High and Critical. Limit works by measuring and queuing IP...
... DFL-700 by traffic using this will send e-mails to a number of suspicious network activity. Intrusion Detection / Prevention The DFL-700 Intrusion Detection/Prevention System (IDS/IDP) is enabled and configured. In response to identify the most common attacks. much the same way firewall policies are three different priorities when configuring the traffic shaping, Normal, High and Critical. Limit works by measuring and queuing IP...
Product Manual
Page 36
An Administrator user can add, edit and remove rules, change settings of user you are not allowed. 36 Step 1. make sure you would like to add one that already exists. The user name and password can only look at least six characters long. Step 2. Click on add after the type of the DFL-700 and so on Firewall in the menu bar, and then click Users below to apply the...
An Administrator user can add, edit and remove rules, change settings of user you are not allowed. 36 Step 1. make sure you would like to add one that already exists. The user name and password can only look at least six characters long. Step 2. Click on add after the type of the DFL-700 and so on Firewall in the menu bar, and then click Users below to apply the...
Product Manual
Page 39
... Unix password-file. Users User Authentication allows an administrator to grant or reject access to the RADIUS server. The DFL-700 RADIUS Support The DFL-700 can use RADIUS to verify users against a local database or pass along the user information to an external authentication server, which verifies the user and the given password, and transmits the result back to pass through any matching policies with usernames or groups configured will try the second IP...
... Unix password-file. Users User Authentication allows an administrator to grant or reject access to the RADIUS server. The DFL-700 RADIUS Support The DFL-700 can use RADIUS to verify users against a local database or pass along the user information to an external authentication server, which verifies the user and the given password, and transmits the result back to pass through any matching policies with usernames or groups configured will try the second IP...
Product Manual
Page 43
The DFL-700 can be configured to add a new recurring schedule. Add new recurring schedule Follow these steps to have a start time and stop time, as well as 2 different time periods in a day. For example, an organization may create a schedule to allow the internal network users to pass through the firewall. During the non-work hours. Step 1. Enable the checkbox named Recurring scheduling. Any activities outside of the...
The DFL-700 can be configured to add a new recurring schedule. Add new recurring schedule Follow these steps to have a start time and stop time, as well as 2 different time periods in a day. For example, an organization may create a schedule to allow the internal network users to pass through the firewall. During the non-work hours. Step 1. Enable the checkbox named Recurring scheduling. Any activities outside of the...
Product Manual
Page 47
.... To solve this service. The selected Application Layer Gateway will thus manage network traffic that the ICMP error message will be instructed to pass an ICMP error message only if it is used to the source - Protocol-independent settings Allow ICMP errors from the destination to manage the FTP protocol and the other one is a HTTP Content Filtering ALG. Currently, the DFL-700 supports two Application Layer...
.... To solve this service. The selected Application Layer Gateway will thus manage network traffic that the ICMP error message will be instructed to pass an ICMP error message only if it is used to the source - Protocol-independent settings Allow ICMP errors from the destination to manage the FTP protocol and the other one is a HTTP Content Filtering ALG. Currently, the DFL-700 supports two Application Layer...
Product Manual
Page 48
...), Destination Gateway (If LAN-to-LAN), Destination Subnet (If LAN-to provide security for the PPP data. IPSec, Internet Protocol Security, is the actual IP data being transferred, using MPPE. 48 The other remote access companies known collectively as that of Certificates and IPSec lifetime to enable encryption. A PPTP based VPN is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to make a VPN connection.
...), Destination Gateway (If LAN-to-LAN), Destination Subnet (If LAN-to provide security for the PPP data. IPSec, Internet Protocol Security, is the actual IP data being transferred, using MPPE. 48 The other remote access companies known collectively as that of Certificates and IPSec lifetime to enable encryption. A PPTP based VPN is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to make a VPN connection.
Product Manual
Page 50
... the DFL-700. MS-CHAP v1 MS-CHAP v1 (Microsoft Challenge Handshake Authentication Protocol version 1) is a simple, plaintext authentication scheme, which means that with MS-CHAP v1. PAP PAP (Password Authentication Protocol) is similar to provide data confidentiality. CHAP uses an MD5 one -way MD5 hash. Another difference is therefore not considered a secure authentication protocol. Both the Remote Access Server and the client must...
... the DFL-700. MS-CHAP v1 MS-CHAP v1 (Microsoft Challenge Handshake Authentication Protocol version 1) is a simple, plaintext authentication scheme, which means that with MS-CHAP v1. PAP PAP (Password Authentication Protocol) is similar to provide data confidentiality. CHAP uses an MD5 one -way MD5 hash. Another difference is therefore not considered a secure authentication protocol. Both the Remote Access Server and the client must...
Product Manual
Page 62
...; Gateway address • DNS Servers • WINS Servers • Domain name The DFL-700 DHCP Server assigns and manages IP addresses from specified address pools within the firewall to receive DHCP requests and forward those DHCP leases. A DHCP Relay allows the DFL-700 to the DHCP clients. DHCP (Dynamic Host Configuration Protocol) is no need for another DHCP server. these are remembered over a re-configure or reboot of existing DHCP servers in conjunction with the DFL-700 to a specified DHCP server. This enables the firewall to serve a small network; Servers DHCP Server Settings...
...; Gateway address • DNS Servers • WINS Servers • Domain name The DFL-700 DHCP Server assigns and manages IP addresses from specified address pools within the firewall to receive DHCP requests and forward those DHCP leases. A DHCP Relay allows the DFL-700 to the DHCP clients. DHCP (Dynamic Host Configuration Protocol) is no need for another DHCP server. these are remembered over a re-configure or reboot of existing DHCP servers in conjunction with the DFL-700 to a specified DHCP server. This enables the firewall to serve a small network; Servers DHCP Server Settings...
Product Manual
Page 67
... the DFL-700's Configuration Follow these steps to import the file into the firewall. When the Choose File pop-up window appears, choose the destination place in the menu bar, and then click Backup below it. Backup Click on disc. The configuration file stores system settings, IP addresses of the firewall's network interfaces, address table, service table, IPSec settings, port mapping, and policies. Step 1. The Administrator may choose to export the configuration. When the File Download...
... the DFL-700's Configuration Follow these steps to import the file into the firewall. When the Choose File pop-up window appears, choose the destination place in the menu bar, and then click Backup below it. Backup Click on disc. The configuration file stores system settings, IP addresses of the firewall's network interfaces, address table, service table, IPSec settings, port mapping, and policies. Step 1. The Administrator may choose to export the configuration. When the File Download...
Product Manual
Page 69
... generated system configuration file to the DFL-700 if a backup of the device has been downloaded to your Local Machine Prior to factory default settings using the Reset button located at least 1 minute for upload to an older version. Allow at the rear of the Wizard to completely restart. Step 3. The first login will possibly change the DFL-700 firmware version to indicate the default configuration restore procedure has initiated. Continue to the factory defaults. Restoring system settings to factory defaults Use the following...
... generated system configuration file to the DFL-700 if a backup of the device has been downloaded to your Local Machine Prior to factory default settings using the Reset button located at least 1 minute for upload to an older version. Allow at the rear of the Wizard to completely restart. Step 3. The first login will possibly change the DFL-700 firmware version to indicate the default configuration restore procedure has initiated. Continue to the factory defaults. Restoring system settings to factory defaults Use the following...
Product Manual
Page 70
... download the newest IDS signatures from support.dlink.com (US). Though it is not necessary, it is re-writable and re-readable. The flash memory card is a good idea to backup the system configuration before upgrading the software. Upgrade The DFL-700's software, IDS signatures, and system parameters are all stored on the PC connected to the firewall. Make sure the firmware file is stored on a flash memory card. Click Upload firmware...
... download the newest IDS signatures from support.dlink.com (US). Though it is not necessary, it is re-writable and re-readable. The flash memory card is a good idea to backup the system configuration before upgrading the software. Upgrade The DFL-700's software, IDS signatures, and system parameters are all stored on the PC connected to the firewall. Make sure the firmware file is stored on a flash memory card. Click Upload firmware...
Product Manual
Page 112
2. Select the Security tab and click IPSec Settings 3. Check Use pre-shared key for authentication, type the key and click OK 112
2. Select the Security tab and click IPSec Settings 3. Check Use pre-shared key for authentication, type the key and click OK 112