User Guide
Page 3
... Types 42 8.2.2 Error Report & Connection Protection 46 8.3 Schedules 48 8.4 X.509 Certificates 49 8.4.1 Introduction to Certificates 49 8.4.2 X.509 Certificates in D-Link Firewall 51 D-Link Firewalls User's Guide
... Types 42 8.2.2 Error Report & Connection Protection 46 8.3 Schedules 48 8.4 X.509 Certificates 49 8.4.1 Introduction to Certificates 49 8.4.2 X.509 Certificates in D-Link Firewall 51 D-Link Firewalls User's Guide
User Guide
Page 4
iii 9 Interfaces 53 9.1 Ethernet 53 9.1.1 Ethernet Interfaces 53 9.1.2 Ethernet Interfaces in D-Link Firewalls 54 9.2 Virtual LAN (VLAN 56 9.2.1 VLAN Infrastructure 56 9.2.2 802.1Q VLAN Standard 57 9.2.3 VLAN Implementation 58 9.2.4 Using Virtual LANs to Expand Firewall Interfaces . . 59 9.3 ...-based Routing Tables 89 10.7.3 Policy-based Routing Policy 89 10.7.4 PBR Execution 89 10.7.5 Scenario: PBR Configuration 91 10.8 Proxy ARP 94 D-Link Firewalls User's Guide
iii 9 Interfaces 53 9.1 Ethernet 53 9.1.1 Ethernet Interfaces 53 9.1.2 Ethernet Interfaces in D-Link Firewalls 54 9.2 Virtual LAN (VLAN 56 9.2.1 VLAN Infrastructure 56 9.2.2 802.1Q VLAN Standard 57 9.2.3 VLAN Implementation 58 9.2.4 Using Virtual LANs to Expand Firewall Interfaces . . 59 9.3 ...-based Routing Tables 89 10.7.3 Policy-based Routing Policy 89 10.7.4 PBR Execution 89 10.7.5 Scenario: PBR Configuration 91 10.8 Proxy ARP 94 D-Link Firewalls User's Guide
User Guide
Page 5
... 99 12 DNS 101 13 Log Settings 103 13.1 Implementation 103 13.1.1 Defining Syslog Receiver 103 13.1.2 Enabling Logging 104 VI Security Polices 108 14 IP Rules 109 14.1 Overview 109 14.1.1 Fields 110 14.1.2 Action types 111 14.2 Address Translation 112 14.2.1 Overview ...112 14.2.2 NAT 112 14.2.3 Address translation in D-Link Firewall 114 14.3 Scenarios: IP Rules Configuration 116 15 Access (Anti-spoofing) 123 15.1 Overview 123 15.1.1 IP Spoo...
... 99 12 DNS 101 13 Log Settings 103 13.1 Implementation 103 13.1.1 Defining Syslog Receiver 103 13.1.2 Enabling Logging 104 VI Security Polices 108 14 IP Rules 109 14.1 Overview 109 14.1.1 Fields 110 14.1.2 Action types 111 14.2 Address Translation 112 14.2.1 Overview ...112 14.2.2 NAT 112 14.2.3 Address translation in D-Link Firewall 114 14.3 Scenarios: IP Rules Configuration 116 15 Access (Anti-spoofing) 123 15.1 Overview 123 15.1.1 IP Spoo...
User Guide
Page 6
... (ALG) 147 18.1 Overview 147 18.2 FTP 148 18.2.1 FTP Connections 148 18.2.2 Scenarios: FTP ALG Configuration 150 18.3 HTTP 155 18.3.1 Components & Security Issues 155 18.3.2 Solution 156 18.4 H.323 158 18.4.1 H.323 Standard Overview 158 18.4.2 H.323 Components 158 18.4.3 H.323 Protocols 159 18.4.4 H.323 ALG Overview....4.5 Scenarios: H.323 ALG Configuration 161 19 Intrusion Detection System (IDS) 181 19.1 Overview 181 19.1.1 Intrusion Detection Rules 182 19.1.2 Pattern Matching 182 D-Link Firewalls User's Guide
... (ALG) 147 18.1 Overview 147 18.2 FTP 148 18.2.1 FTP Connections 148 18.2.2 Scenarios: FTP ALG Configuration 150 18.3 HTTP 155 18.3.1 Components & Security Issues 155 18.3.2 Solution 156 18.4 H.323 158 18.4.1 H.323 Standard Overview 158 18.4.2 H.323 Components 158 18.4.3 H.323 Protocols 159 18.4.4 H.323 ALG Overview....4.5 Scenarios: H.323 ALG Configuration 161 19 Intrusion Detection System (IDS) 181 19.1 Overview 181 19.1.1 Intrusion Detection Rules 182 19.1.2 Pattern Matching 182 D-Link Firewalls User's Guide
User Guide
Page 7
....2.2 Authentication & Integrity 198 20.3 Why VPN in Firewalls 200 20.3.1 VPN Deployment 201 21 VPN Planning 207 21.1 VPN Design Considerations 207 21.1.1 End Point Security 208 21.1.2 Key Distribution 210 22 VPN Protocols & Tunnels 213 22.1 IPsec 213 22.1.1 IPsec protocols 214 22.1.2 IPsec Modes 214 22.1.3 IKE 215 22... Integrity & Authentication 219 22.1.5 Scenarios: IPSec Configuration 223 22.2 PPTP/ L2TP 228 22.2.1 PPTP 228 22.2.2 L2TP 234 22.3 SSL/TLS (HTTPS 243 D-Link Firewalls User's Guide
....2.2 Authentication & Integrity 198 20.3 Why VPN in Firewalls 200 20.3.1 VPN Deployment 201 21 VPN Planning 207 21.1 VPN Design Considerations 207 21.1.1 End Point Security 208 21.1.2 Key Distribution 210 22 VPN Protocols & Tunnels 213 22.1 IPsec 213 22.1.1 IPsec protocols 214 22.1.2 IPsec Modes 214 22.1.3 IKE 215 22... Integrity & Authentication 219 22.1.5 Scenarios: IPSec Configuration 223 22.2 PPTP/ L2TP 228 22.2.1 PPTP 228 22.2.2 L2TP 234 22.3 SSL/TLS (HTTPS 243 D-Link Firewalls User's Guide
User Guide
Page 8
....3 Automatic Client Login 272 25.4 HTTP Poster 273 25.4.1 URL Format 273 26 DHCP Server & Relayer 275 26.1 DHCP Server 275 26.2 DHCP Relayer 277 D-Link Firewalls User's Guide
....3 Automatic Client Login 272 25.4 HTTP Poster 273 25.4.1 URL Format 273 26 DHCP Server & Relayer 275 26.1 DHCP Server 275 26.2 DHCP Relayer 277 D-Link Firewalls User's Guide
User Guide
Page 9
viii XI Transparent Mode 280 27 Transparent Mode 281 27.1 Overview 281 27.2 Transparent Mode Implementation in D-Link Firewalls . . . . 282 27.3 Scenarios: Enabling Transparent Mode 284 XII Zone Defense 292 28 Zone Defense 293 28.1 Overview 293 28.2 Zone Defense Switches 293 28.2.1 ....4 Things to Keep in Mind 309 29.4.1 Statistics and Logging Issues 309 29.4.2 Configuration Issues 310 XIV Appendix 312 A Console Commands Reference 315 D-Link Firewalls User's Guide
viii XI Transparent Mode 280 27 Transparent Mode 281 27.1 Overview 281 27.2 Transparent Mode Implementation in D-Link Firewalls . . . . 282 27.3 Scenarios: Enabling Transparent Mode 284 XII Zone Defense 292 28 Zone Defense 293 28.1 Overview 293 28.2 Zone Defense Switches 293 28.2.1 ....4 Things to Keep in Mind 309 29.4.1 Statistics and Logging Issues 309 29.4.2 Configuration Issues 310 XIV Appendix 312 A Console Commands Reference 315 D-Link Firewalls User's Guide
User Guide
Page 10
ix List of Commands 315 About 315 Access 316 ARP 316 ARPSnoop 317 Buffers 317 Certcache 318 CfgLog 319 Connections 319 Cpuid 320 DHCP 320 DHCPRelay 321 DHCPServer 321 DynRoute 321 Frags 322 HA 322 HTTPPoster 322 Ifacegroups 323 IfStat 323 Ikesnoop 324 Ipseckeepalive 325 IPSectunnels 325 IPSecstats 325 Killsa 326 License 326 Lockdown 327 Loghosts 327 Memory 327 Netcon 327 Netobjects 328 OSPF 328 Ping 329 Pipes 329 Proplists 330 ReConfigure 330 Remotes 331 Routes 331 Rules 332 Scrsave 332 Services 333 Shutdown 333 D-Link Firewalls User's Guide
ix List of Commands 315 About 315 Access 316 ARP 316 ARPSnoop 317 Buffers 317 Certcache 318 CfgLog 319 Connections 319 Cpuid 320 DHCP 320 DHCPRelay 321 DHCPServer 321 DynRoute 321 Frags 322 HA 322 HTTPPoster 322 Ifacegroups 323 IfStat 323 Ikesnoop 324 Ipseckeepalive 325 IPSectunnels 325 IPSecstats 325 Killsa 326 License 326 Lockdown 327 Loghosts 327 Memory 327 Netcon 327 Netobjects 328 OSPF 328 Ping 329 Pipes 329 Proplists 330 ReConfigure 330 Remotes 331 Routes 331 Rules 332 Scrsave 332 Services 333 Shutdown 333 D-Link Firewalls User's Guide
User Guide
Page 13
... 262 24.2 A SLB Scenario 266 27.1 Transparent Mode Scenario 1 284 27.2 Transparent Mode Scenario 2 287 28.1 A Zone Defense Scenario 297 29.1 Example HA Setup 303 D-Link Firewalls User's Guide
... 262 24.2 A SLB Scenario 266 27.1 Transparent Mode Scenario 1 284 27.2 Transparent Mode Scenario 2 287 28.1 A Zone Defense Scenario 297 29.1 Example HA Setup 303 D-Link Firewalls User's Guide
User Guide
Page 22
1 CHAPTER Capabilities 1.1 Product Highlights The key features of D-Link firewalls can be outlined as: • Easy to use start-up wizard • Web-based graphical user interface (WebUI) • Effective and easy to maintenance • Complete control of security policies • Advanced application layer gateways (FTP, HTTP, H.323) • Advanced monitoring...
1 CHAPTER Capabilities 1.1 Product Highlights The key features of D-Link firewalls can be outlined as: • Easy to use start-up wizard • Web-based graphical user interface (WebUI) • Effective and easy to maintenance • Complete control of security policies • Advanced application layer gateways (FTP, HTTP, H.323) • Advanced monitoring...
User Guide
Page 23
4 Chapter 1. Capabilities • Zone Defence • High Availability (Some models) Details about how to make these features work can be found in specific chapters in this user's guide. D-Link Firewalls User's Guide
4 Chapter 1. Capabilities • Zone Defence • High Availability (Some models) Details about how to make these features work can be found in specific chapters in this user's guide. D-Link Firewalls User's Guide
User Guide
Page 27
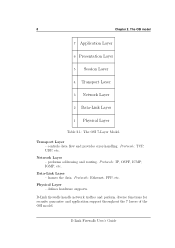
Network Layer - Protocols: TCP, UDP, etc. Data-Link Layer - Protocols: Ethernet, PPP, etc. frames the data. D-Link firewalls handle network traffics and perform diverse functions for security guarantee and application support throughout the 7 layers of the OSI model. D-Link Firewalls User's Guide Physical Layer - defines hardware supports. The OSI model...
Network Layer - Protocols: TCP, UDP, etc. Data-Link Layer - Protocols: Ethernet, PPP, etc. frames the data. D-Link firewalls handle network traffics and perform diverse functions for security guarantee and application support throughout the 7 layers of the OSI model. D-Link Firewalls User's Guide Physical Layer - defines hardware supports. The OSI model...
User Guide
Page 28
...decision based on your local area network to flow between networks and that network traffic 9 Most firewalls, including D-Link firewalls, ensure that unauthorized communication is a Firewall? When you connect your computer or your protected networks and prevent all outsiders from... gaining access to resources and material you to install less secure network services on factors such as sender address, destination address, protocol and ports. the Internet, measures need to be taken to...
...decision based on your local area network to flow between networks and that network traffic 9 Most firewalls, including D-Link firewalls, ensure that unauthorized communication is a Firewall? When you connect your computer or your protected networks and prevent all outsiders from... gaining access to resources and material you to install less secure network services on factors such as sender address, destination address, protocol and ports. the Internet, measures need to be taken to...
User Guide
Page 29
...existing problems. Complete protection can only be achieved through it. This is a necessary first step towards securing your network and computers. Security means much more than just firewalls. Many marketing executives and sales people smile and claim that all ...and secure once it was designed. Unfortunately, it discusses firewalls in most cases, installing a firewall is however not true. Please note that for these . Firewall Principles complies with , and in the software used, and by implementing appropriate measures to D-Link &#...
...existing problems. Complete protection can only be achieved through it. This is a necessary first step towards securing your network and computers. Security means much more than just firewalls. Many marketing executives and sales people smile and claim that all ...and secure once it was designed. Unfortunately, it discusses firewalls in most cases, installing a firewall is however not true. Please note that for these . Firewall Principles complies with , and in the software used, and by implementing appropriate measures to D-Link &#...
User Guide
Page 30
...are frequently supplied with such components pre-installed in applications and operating systems put together. All attempts to secure the networks of an organization should be a security policy that inexperienced users can utilize the extra functionality at hand to use on protected Networks No fi...;rewall in the world can protect against data-driven attacks in web servers. In order for use . The common feature of most of attack, D-Link Firewalls ...
...are frequently supplied with such components pre-installed in applications and operating systems put together. All attempts to secure the networks of an organization should be a security policy that inexperienced users can utilize the extra functionality at hand to use on protected Networks No fi...;rewall in the world can protect against data-driven attacks in web servers. In order for use . The common feature of most of attack, D-Link Firewalls ...
User Guide
Page 31
... in this problem in the contents of attack include avoiding using browser-based email software or disabling scripting and introducing mail gateways that link in mind. Unfortunately, most common targets for data-driven attacks are of network-based attack, as mail servers, DNS servers and web...provide protection against. Web servers are activated once the document is susceptible to detect them. A firewall can occur in order to increase security, but it is not written with a net result of intruders being able to their enormous complexity. Here, the only solution is to ...
... in this problem in the contents of attack include avoiding using browser-based email software or disabling scripting and introducing mail gateways that link in mind. Unfortunately, most common targets for data-driven attacks are of network-based attack, as mail servers, DNS servers and web...provide protection against. Web servers are activated once the document is susceptible to detect them. A firewall can occur in order to increase security, but it is not written with a net result of intruders being able to their enormous complexity. Here, the only solution is to ...
User Guide
Page 32
... simplifying operations for the same reason as the protected network and can only filter data that which to local computers and all data security problems are as secure as browsers. Scripting languages provide almost unlimited access to great extent support scripting languages, for the benefit of users creates increased internal... figures, it can lead you, more than not, to make small, difficult to detect mistakes that more often than 50% of tasks. D-Link Firewalls User's Guide
... simplifying operations for the same reason as the protected network and can only filter data that which to local computers and all data security problems are as secure as browsers. Scripting languages provide almost unlimited access to great extent support scripting languages, for the benefit of users creates increased internal... figures, it can lead you, more than not, to make small, difficult to detect mistakes that more often than 50% of tasks. D-Link Firewalls User's Guide
User Guide
Page 33
...intruder can block all inbound Internet traffic, aside from their laptops. A basic precaution to their company's network via web servers, security hazards are well protected against modem and VPN connection attacks is becoming increasingly common for users on each laptop. It is to be installed... network. This way, they wish to VPN connections, it is only as high as a D-Link Firewalls User's Guide The VPN endpoints should always be secure, the total level of security is usually possible to dictate the types of whom they enjoy more companies begin to this , ...
...intruder can block all inbound Internet traffic, aside from their laptops. A basic precaution to their company's network via web servers, security hazards are well protected against modem and VPN connection attacks is becoming increasingly common for users on each laptop. It is to be installed... network. This way, they wish to VPN connections, it is only as high as a D-Link Firewalls User's Guide The VPN endpoints should always be secure, the total level of security is usually possible to dictate the types of whom they enjoy more companies begin to this , ...
User Guide
Page 34
... locating the data source, e.g. Rather, it from insecure networks to locate web servers in the DMZ, so therefore disabling "IP forwarding" would still be completely secure. 3.2. It is not IP packets being aware of the problems they communicate with the rest of hole. Note The problem here is now common practice...
... locating the data source, e.g. Rather, it from insecure networks to locate web servers in the DMZ, so therefore disabling "IP forwarding" would still be completely secure. 3.2. It is not IP packets being aware of the problems they communicate with the rest of hole. Note The problem here is now common practice...
User Guide
Page 35
... case of protection worth considering is that contains limited information to set up a separate data source that insecure machines can execute commands on "protected" machines. D-Link Firewalls User's Guide It should only contain information deemed sufficiently insensitive to be accessed from the internal data source to the external data...
... case of protection worth considering is that contains limited information to set up a separate data source that insecure machines can execute commands on "protected" machines. D-Link Firewalls User's Guide It should only contain information deemed sufficiently insensitive to be accessed from the internal data source to the external data...