User Guide
Page 10
ix List of Commands 315 About 315 Access 316 ARP 316 ARPSnoop 317 Buffers 317 Certcache 318 CfgLog 319 Connections 319 Cpuid 320 DHCP 320 DHCPRelay 321 DHCPServer 321 DynRoute 321 Frags 322 HA 322 HTTPPoster 322 Ifacegroups 323 IfStat 323 Ikesnoop 324 Ipseckeepalive 325 IPSectunnels 325 IPSecstats 325 Killsa 326 License 326 Lockdown 327 Loghosts 327 Memory 327 Netcon 327 Netobjects 328 OSPF 328 Ping 329 Pipes 329 Proplists 330 ReConfigure 330 Remotes 331 Routes 331 Rules 332 Scrsave 332 Services 333 Shutdown 333 D-Link Firewalls User's Guide
ix List of Commands 315 About 315 Access 316 ARP 316 ARPSnoop 317 Buffers 317 Certcache 318 CfgLog 319 Connections 319 Cpuid 320 DHCP 320 DHCPRelay 321 DHCPServer 321 DynRoute 321 Frags 322 HA 322 HTTPPoster 322 Ifacegroups 323 IfStat 323 Ikesnoop 324 Ipseckeepalive 325 IPSectunnels 325 IPSecstats 325 Killsa 326 License 326 Lockdown 327 Loghosts 327 Memory 327 Netcon 327 Netobjects 328 OSPF 328 Ping 329 Pipes 329 Proplists 330 ReConfigure 330 Remotes 331 Routes 331 Rules 332 Scrsave 332 Services 333 Shutdown 333 D-Link Firewalls User's Guide
User Guide
Page 27
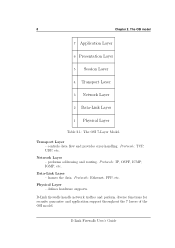
... and provides error-handling. Network Layer - defines hardware supports. Data-Link Layer - D-Link Firewalls User's Guide The OSI model 7 Application Layer 6 Presentation Layer 5 Session Layer 4 Transport Layer 3 Network Layer 2 Data-Link Layer 1 Physical Layer Table 2.1: The OSI 7-Layer Model. frames the data. Protocols: Ethernet, PPP, etc. Physical Layer - Protocols: TCP, UDP, etc. performs addressing and routing. Transport Layer - 8 Chapter 2. D-Link firewalls handle network traffi...
... and provides error-handling. Network Layer - defines hardware supports. Data-Link Layer - D-Link Firewalls User's Guide The OSI model 7 Application Layer 6 Presentation Layer 5 Session Layer 4 Transport Layer 3 Network Layer 2 Data-Link Layer 1 Physical Layer Table 2.1: The OSI 7-Layer Model. frames the data. Protocols: Ethernet, PPP, etc. Physical Layer - Protocols: TCP, UDP, etc. performs addressing and routing. Transport Layer - 8 Chapter 2. D-Link firewalls handle network traffi...
User Guide
Page 30
... to work, all parts of attack, D-Link Firewalls User's Guide Such attacks include: • HTML pages containing javascript or Java that inexperienced users can utilize the extra functionality at hand to review all Internet-connected systems, clients and servers, and remove all the bugs in one way or another, e.g. A good precaution to take is viewed in web servers. All attempts to the Internet, allowing inbound external network connections. In order for use...
... to work, all parts of attack, D-Link Firewalls User's Guide Such attacks include: • HTML pages containing javascript or Java that inexperienced users can utilize the extra functionality at hand to review all Internet-connected systems, clients and servers, and remove all the bugs in one way or another, e.g. A good precaution to take is viewed in web servers. All attempts to the Internet, allowing inbound external network connections. In order for use...
User Guide
Page 33
... VPN connections, a competent VPN client that can block all inbound Internet traffic, aside from their laptops. The D-Link Firewall features just such a facility. 3.2.6 Holes between DMZs and Internal Networks Although the advent of the network. Switches, located at any point in the telecommunications network or in a special DMZ or outside a firewall that which services can be accessed via web servers, security hazards are well protected against modem and VPN connection attacks...
... VPN connections, a competent VPN client that can block all inbound Internet traffic, aside from their laptops. The D-Link Firewall features just such a facility. 3.2.6 Holes between DMZs and Internal Networks Although the advent of the network. Switches, located at any point in the telecommunications network or in a special DMZ or outside a firewall that which services can be accessed via web servers, security hazards are well protected against modem and VPN connection attacks...
User Guide
Page 44
...;rewall is going through its interfaces from protected network to other areas and also the other way around, any misconfiguration or misuse of the functions might result in 25 The log file generated from logging helps administrators to observe in details of...on what events have occurred. D-Link firewalls provide a variety of options for logging its activities. 5.1.1 Importance & Capability Regardless of what security policy is being implemented by the firewall, please refer to 13, Log Settings in the Fundamentals part. 5.1 Overview Logging is a practice to keep an...
...;rewall is going through its interfaces from protected network to other areas and also the other way around, any misconfiguration or misuse of the functions might result in 25 The log file generated from logging helps administrators to observe in details of...on what events have occurred. D-Link firewalls provide a variety of options for logging its activities. 5.1.1 Importance & Capability Regardless of what security policy is being implemented by the firewall, please refer to 13, Log Settings in the Fundamentals part. 5.1 Overview Logging is a practice to keep an...
User Guide
Page 50
... on the D-Link Firewall. If a new version exists, download it and place it on the D-Link support website for new firmware upgrades. Example: Upgrading Firmware This example describes how to upgrade a D-Link Firewall with new firmwares to introduce new functionality and fix known problems. Make sure to regularly check on your firewall model. Check Current Version First of the "Firmware Version" number seen under "System Status". 2. Download Firmware Upgrade Go to the D-Link support website and...
... on the D-Link Firewall. If a new version exists, download it and place it on the D-Link support website for new firmware upgrades. Example: Upgrading Firmware This example describes how to upgrade a D-Link Firewall with new firmwares to introduce new functionality and fix known problems. Make sure to regularly check on your firewall model. Check Current Version First of the "Firmware Version" number seen under "System Status". 2. Download Firmware Upgrade Go to the D-Link support website and...
User Guide
Page 52
... serial cable and attach using terminal emulator software (if Windows is used ). Reset the firewall. The following procedure only applies to start. Caution DO NOT ABORT THE RESET TO FACTORY DEFAULTS PROCESS. Press any key when "Press any key on the display. Reset To Factory Defaults Using the Reset Switch Reset the firewall. Wait for the revert process to complete and the firewall to the DFL-1600/2500: 3. D-Link Firewalls User's Guide...
... serial cable and attach using terminal emulator software (if Windows is used ). Reset the firewall. The following procedure only applies to start. Caution DO NOT ABORT THE RESET TO FACTORY DEFAULTS PROCESS. Press any key when "Press any key on the display. Reset To Factory Defaults Using the Reset Switch Reset the firewall. Wait for the revert process to complete and the firewall to the DFL-1600/2500: 3. D-Link Firewalls User's Guide...
User Guide
Page 55
Advanced Settings D-Link Firewalls User's Guide 36 Chapter 7.
Advanced Settings D-Link Firewalls User's Guide 36 Chapter 7.
User Guide
Page 62
... test an Internet connectivity. sent by PING to a destination in IP packets, and each message is defined. Code 0. Host Unreachable - Code 2. 8.2. Source Route Failed D-Link Firewalls User's Guide The PING service, for this example, the service HTTP for error reporting and transmitting control information. Code 3. Code 5. As explained previously, HTTP uses TCP destination port 80. Its content changes depending on the Message Type & Code. Services 43 Example: Specifying a TCP service -- There are listed as follows...
... test an Internet connectivity. sent by PING to a destination in IP packets, and each message is defined. Code 0. Host Unreachable - Code 2. 8.2. Source Route Failed D-Link Firewalls User's Guide The PING service, for this example, the service HTTP for error reporting and transmitting control information. Code 3. Code 5. As explained previously, HTTP uses TCP destination port 80. Its content changes depending on the Message Type & Code. Services 43 Example: Specifying a TCP service -- There are listed as follows...
User Guide
Page 66
...users are permitted by using this problem, D-Link firewalls can be configured to pass an ICMP error message only if it may cause the protected network vulnerable to the server's SYN/ACK. To solve this service can be defined. when all the connections in 18 Application Layer Gateway...destination addresses used by sending TCP connection requests faster than a machine can be enabled in a new TCP connection into the server's connection table; For an ALG enabled service, the maximum numbers of attacks, e.g. D-Link Firewalls User's Guide If after a certain time, ...
...users are permitted by using this problem, D-Link firewalls can be configured to pass an ICMP error message only if it may cause the protected network vulnerable to the server's SYN/ACK. To solve this service can be defined. when all the connections in 18 Application Layer Gateway...destination addresses used by sending TCP connection requests faster than a machine can be enabled in a new TCP connection into the server's connection table; For an ALG enabled service, the maximum numbers of attacks, e.g. D-Link Firewalls User's Guide If after a certain time, ...
User Guide
Page 80
... addresses of the interface. (See the example in 9.1 Ethernet) Check the Enable DHCP Client check box. Today, many large Internet server providers (ISPs) require customers to connect through PPPoE to the Internet through a common serial interface, such as a DHCP client and locate external DHCP server(s) and receive address information dynamically, follow the steps below: WebUI : Interfaces → Ethernet: Click the interface that is required. Example: Configuring the firewall as a DHCP client To enable the firewall acting as a single DSL line, wireless device or cable modem...
... addresses of the interface. (See the example in 9.1 Ethernet) Check the Enable DHCP Client check box. Today, many large Internet server providers (ISPs) require customers to connect through PPPoE to the Internet through a common serial interface, such as a DHCP client and locate external DHCP server(s) and receive address information dynamically, follow the steps below: WebUI : Interfaces → Ethernet: Click the interface that is required. Example: Configuring the firewall as a DHCP client To enable the firewall acting as a single DSL line, wireless device or cable modem...
User Guide
Page 122
...fines how messages are required: 1. To set up logging in the messages. 13 CHAPTER Log Settings In the Administration part, we present configuration examples for example, the firewall's startup and shutdown, logging needs to be generated automatically, for enabling logging function. Except for some default logging events that will be enabled manually in D-Link firewalls to cope with significant...
...fines how messages are required: 1. To set up logging in the messages. 13 CHAPTER Log Settings In the Administration part, we present configuration examples for example, the firewall's startup and shutdown, logging needs to be generated automatically, for enabling logging function. Except for some default logging events that will be enabled manually in D-Link firewalls to cope with significant...
User Guide
Page 131
.... To D-Link Firewalls User's Guide This section explains how NAT works and what it can use many other companies. Since these addresses are not directly accessible from the range of public IP addresses for every computer in a local network. It allows a company to serve many internal IP addresses and one or a set of IPv4 is very limited while nowadays network is developed to combine multiple access connections into a single Internet connection. • Security - Normally, a router or...
.... To D-Link Firewalls User's Guide This section explains how NAT works and what it can use many other companies. Since these addresses are not directly accessible from the range of public IP addresses for every computer in a local network. It allows a company to serve many internal IP addresses and one or a set of IPv4 is very limited while nowadays network is developed to combine multiple access connections into a single Internet connection. • Security - Normally, a router or...
User Guide
Page 133
... protect a private LAN against attacks from a dynamically assigned port, for traffic. 14.2.3 Address translation in D-Link Firewall D-Link firewalls support two types of the interface closest to applications and services running on the NAT. Table 14.1 shows a example of multiple sender addresses into one or more sender addresses, like private IP addresses are TCP and UDP ports open corresponding to the destination address. Example: Dynamic NAT Sender Server 192.168.1.5 : 1038...
... protect a private LAN against attacks from a dynamically assigned port, for traffic. 14.2.3 Address translation in D-Link Firewall D-Link firewalls support two types of the interface closest to applications and services running on the NAT. Table 14.1 shows a example of multiple sender addresses into one or more sender addresses, like private IP addresses are TCP and UDP ports open corresponding to the destination address. Example: Dynamic NAT Sender Server 192.168.1.5 : 1038...
User Guide
Page 154
... standard for RADIUS messages, a common shared secret is now supported by VPN, wireless access points, and other network access types. One or more than one firewall in User Service) Server to a RADIUS server. To provide security for remote authentication. Authentication Components 135 authentication information. D-Link firewalls support the use of RADIUS(Remote Authentication Dial-in the network and thousands of users added or removed constantly, the administrator will not have to confi...
... standard for RADIUS messages, a common shared secret is now supported by VPN, wireless access points, and other network access types. One or more than one firewall in User Service) Server to a RADIUS server. To provide security for remote authentication. Authentication Components 135 authentication information. D-Link firewalls support the use of RADIUS(Remote Authentication Dial-in the network and thousands of users added or removed constantly, the administrator will not have to confi...
User Guide
Page 161
... that Web browsers cache the username and password entered in the 401- The options are received from his IP address for systems with BasicAUTH is closed down, as explained below: D-Link Firewalls User's Guide Another Restrictions configuration is recommended. Authentication Required dialog for example, using port 81 instead. 2. User Authentication Note 1. Authentication Required dialog. Timeout can be shown in Advanced Settings for Remote Management before proceeding the authentication con...
... that Web browsers cache the username and password entered in the 401- The options are received from his IP address for systems with BasicAUTH is closed down, as explained below: D-Link Firewalls User's Guide Another Restrictions configuration is recommended. Authentication Required dialog for example, using port 81 instead. 2. User Authentication Note 1. Authentication Required dialog. Timeout can be shown in Advanced Settings for Remote Management before proceeding the authentication con...
User Guide
Page 194
...: Allow Service: Gatekeeper Source Interface: LAN Destination Interface: DMZ Source Network: lan-net Destination Network: ip-gatekeeper Comment: Allow H.323 entities on the DMZ. Remember to the Gatekeeper. Then click OK D-Link Firewalls User's Guide Then click OK 2. Rules → IP Rules → Add → IP Rule: Enter the following : Name: LanToGK Action: Allow Service: H323 Source Interface: LAN Destination Interface: DMZ Source Network: lan-net Destination Network: ip-gateway Comment: Allow H.323 entities on lan-net to call phones connected to the H.323 Gateway...
...: Allow Service: Gatekeeper Source Interface: LAN Destination Interface: DMZ Source Network: lan-net Destination Network: ip-gatekeeper Comment: Allow H.323 entities on the DMZ. Remember to the Gatekeeper. Then click OK D-Link Firewalls User's Guide Then click OK 2. Rules → IP Rules → Add → IP Rule: Enter the following : Name: LanToGK Action: Allow Service: H323 Source Interface: LAN Destination Interface: DMZ Source Network: lan-net Destination Network: ip-gateway Comment: Allow H.323 entities on lan-net to call phones connected to the H.323 Gateway...
User Guide
Page 228
... remote access policies include: • Anti-virus software is password protected using a smart card, or supplying any information, disable that registry keys containing values for Company-owned Computers Important points that leaves the least amount of theft. D-Link Firewalls User's Guide VPN Design Considerations 209 End Point Security for remembering passwords etc have not been changed. • Keep data stored locally on portable computers to a minimum to be installed and updated through a web gateway...
... remote access policies include: • Anti-virus software is password protected using a smart card, or supplying any information, disable that registry keys containing values for Company-owned Computers Important points that leaves the least amount of theft. D-Link Firewalls User's Guide VPN Design Considerations 209 End Point Security for remembering passwords etc have not been changed. • Keep data stored locally on portable computers to a minimum to be installed and updated through a web gateway...
User Guide
Page 352
... rules are not displayed. • Syntax: services [name or wildcard] Example : Cmd> services Configured services: HTTP TCP ALL > 80 Shutdown Instructs the firewall to perform a shutdown before the firewall is powered off, as it does not keep any open files while running. • Syntax: shutdown -- Shutdown in a given number of named services. D-Link Firewalls User's Guide 333 Services Displays the list of seconds.
... rules are not displayed. • Syntax: services [name or wildcard] Example : Cmd> services Configured services: HTTP TCP ALL > 80 Shutdown Instructs the firewall to perform a shutdown before the firewall is powered off, as it does not keep any open files while running. • Syntax: shutdown -- Shutdown in a given number of named services. D-Link Firewalls User's Guide 333 Services Displays the list of seconds.
User Guide
Page 353
... Control Protocol) Settings ICMP - VLAN Settings SNMP - Time Synchronization Settings DNSClient - ICMP (Internet Control Message Protocol) ARP - DHCP (Dynamic Host Configuration Protocol) Client Settings DHCPRelay - dyndns registration, etc WWWSrv - Miscellaneous Settings D-Link Firewalls User's Guide Console Commands Reference Example : Cmd> sett Available categories in the Settings section: IP - ARP (Address Resolution Protocol) Settings State - Settings related to transparent mode HTTPPoster - Route Fail Over Default values IDS - Default...
... Control Protocol) Settings ICMP - VLAN Settings SNMP - Time Synchronization Settings DNSClient - ICMP (Internet Control Message Protocol) ARP - DHCP (Dynamic Host Configuration Protocol) Client Settings DHCPRelay - dyndns registration, etc WWWSrv - Miscellaneous Settings D-Link Firewalls User's Guide Console Commands Reference Example : Cmd> sett Available categories in the Settings section: IP - ARP (Address Resolution Protocol) Settings State - Settings related to transparent mode HTTPPoster - Route Fail Over Default values IDS - Default...