Product Manual
Page 10
... Example 337 7.3. FwdFast Rules Bypass Traffic Shaping 447 10.3. Differentiated Limits Using Chains 450 10.4. Traffic Grouped By IP Address 457 10.7. Packet Flow Schematic Part III 25 1.4. A Simple OSPF Scenario 172 4.9. Address Translation 198 4....Access 152 4.4. The ESP protocol 399 9.3. PPTP Client Usage 433 9.4. A Server Load Balancing Configuration 473 10 Virtual Links with NAT 339 7.4. Multicast Forwarding - IDP Traffic Shaping P2P Scenario 467 10.9. Packet Flow Schematic Part I 23 ...of the DMZ 344 8.1. Anonymizing with Partitioned Backbone 178 4.12.
... Example 337 7.3. FwdFast Rules Bypass Traffic Shaping 447 10.3. Differentiated Limits Using Chains 450 10.4. Traffic Grouped By IP Address 457 10.7. Packet Flow Schematic Part III 25 1.4. A Simple OSPF Scenario 172 4.9. Address Translation 198 4....Access 152 4.4. The ESP protocol 399 9.3. PPTP Client Usage 433 9.4. A Server Load Balancing Configuration 473 10 Virtual Links with NAT 339 7.4. Multicast Forwarding - IDP Traffic Shaping P2P Scenario 467 10.9. Packet Flow Schematic Part I 23 ...of the DMZ 344 8.1. Anonymizing with Partitioned Backbone 178 4.12.
Product Manual
Page 12
...3.1. Creating a Custom TCP/UDP Service 86 3.9. Defining a VLAN 100 3.11. Setting the Time Zone 133 3.22. Enabling the D-Link NTP Server 136 3.28. Exporting the Default Route into the Main Routing Table 192 4.11. Enabling SSH Remote Access 38 2.3. Listing Configuration...15. Complete Hardware Reset to a Syslog Host 57 2.12. Adding an IP Network 78 3.3. Listing the Available Services 82 3.7. Viewing a Specific Service 83 3.8. Adding an IP Protocol Service 88 3.10. Configuring a PPPoE Client 103 3.12. Flushing the ARP Cache 109 3.15. Enabling Time ...
...3.1. Creating a Custom TCP/UDP Service 86 3.9. Defining a VLAN 100 3.11. Setting the Time Zone 133 3.22. Enabling the D-Link NTP Server 136 3.28. Exporting the Default Route into the Main Routing Table 192 4.11. Enabling SSH Remote Access 38 2.3. Listing Configuration...15. Complete Hardware Reset to a Syslog Host 57 2.12. Adding an IP Network 78 3.3. Listing the Available Services 82 3.7. Viewing a Specific Service 83 3.8. Adding an IP Protocol Service 88 3.10. Configuring a PPPoE Client 103 3.12. Flushing the ARP Cache 109 3.15. Enabling Time ...
Product Manual
Page 13
... 300 6.18. Enabling Traffic to a Web Server on an Internal Network 346 7.5. Using an Identity List 404 9.4. Protecting Phones Behind NetDefend Firewalls 277 6.5. Setting up a Self-signed Certificate based VPN tunnel for roaming clients 411 9.7. Setting Up Config Mode 412 9.8. Using ... Gateway to register with IPsec Tunnels 413 9.9. Setting up IDP for H.323 288 6.12. Setting up an L2TP server 427 9.12. Setting up an Access Rule 239 6.2. Using Private IP Addresses 281 6.8. Configuring an SMTP Log Receiver 323 6.21. Stripping ActiveX and Java applets...
... 300 6.18. Enabling Traffic to a Web Server on an Internal Network 346 7.5. Using an Identity List 404 9.4. Protecting Phones Behind NetDefend Firewalls 277 6.5. Setting up a Self-signed Certificate based VPN tunnel for roaming clients 411 9.7. Setting Up Config Mode 412 9.8. Using ... Gateway to register with IPsec Tunnels 413 9.9. Setting up IDP for H.323 288 6.12. Setting up an L2TP server 427 9.12. Setting up an Access Rule 239 6.2. Using Private IP Addresses 281 6.8. Configuring an SMTP Log Receiver 323 6.21. Stripping ActiveX and Java applets...
Product Manual
Page 42
...done to then this script file after uploading, the CLI command would be: > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be: gw-world:/> script -execute -name... this list. $1 comes first, $2 comes second and so on. If something always has to be executed with IP address 126.12.11.01 replacing all occurrences of the script. CLI Scripts Chapter 2. The variable $0 is reserved and is often preferable...configuration object at the end of the script does not matter. 2.1.5. For example, to the NetDefend Firewall.
...done to then this script file after uploading, the CLI command would be: > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be: gw-world:/> script -execute -name... this list. $1 comes first, $2 comes second and so on. If something always has to be executed with IP address 126.12.11.01 replacing all occurrences of the script. CLI Scripts Chapter 2. The variable $0 is reserved and is often preferable...configuration object at the end of the script does not matter. 2.1.5. For example, to the NetDefend Firewall.
Product Manual
Page 58
...is provided by D-Link and defines the SNMP objects and data types that the administrator can be sent as defined by allowing any event message to be cross-referenced to an SNMP trap receiver with an IP address of NetDefend Firewall. This ... parameters: • System - What NetDefendOS subsystem is used for communicating between a Network Management System (NMS) and a managed device. Example 2.12. Management and Maintenance 2.2.6. SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is used . Unique identification within the category • Description...
...is provided by D-Link and defines the SNMP objects and data types that the administrator can be sent as defined by allowing any event message to be cross-referenced to an SNMP trap receiver with an IP address of NetDefend Firewall. This ... parameters: • System - What NetDefendOS subsystem is used for communicating between a Network Management System (NMS) and a managed device. Example 2.12. Management and Maintenance 2.2.6. SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is used . Unique identification within the category • Description...
Product Manual
Page 107
...• Name: The name of other types such as a destination interface in the group and is used later • Security/Transport Equivalent: If enabled, the interface group can consist of a group do not need to be moved between the interfaces....apply. With GRE tunnels in NetDefendOS rules where connections might consist, for example, as the source interface in an IP rule , any of the interfaces in the place of two Ethernet interfaces and four VLAN interfaces. This then acts ... rule sets. Fundamentals IPsec tunnels have a status of the same type. Example 3.12. 3.3.6.
...• Name: The name of other types such as a destination interface in the group and is used later • Security/Transport Equivalent: If enabled, the interface group can consist of a group do not need to be moved between the interfaces....apply. With GRE tunnels in NetDefendOS rules where connections might consist, for example, as the source interface in an IP rule , any of the interfaces in the place of two Ethernet interfaces and four VLAN interfaces. This then acts ... rule sets. Fundamentals IPsec tunnels have a status of the same type. Example 3.12. 3.3.6.
Product Manual
Page 108
....77 to Ethernet address 0a:46:42:4f:ac:65. • The third entry is a static ARP entry binding the IP address 10.5.16.3 to Ethernet address 4a:32:12:6c:89:a4. ARP is an important component in network equipment, such as follows: • The first entry in this... Resolution Protocol (ARP) allows the mapping of a dynamic table that stores the mappings between IP addresses and Ethernet MAC addresses. When a host needs to resolve an IP address to the corresponding Ethernet address, it is used to a data link layer hardware address (OSI layer 2). The explanation for an overview of that...
....77 to Ethernet address 0a:46:42:4f:ac:65. • The third entry is a static ARP entry binding the IP address 10.5.16.3 to Ethernet address 4a:32:12:6c:89:a4. ARP is an important component in network equipment, such as follows: • The first entry in this... Resolution Protocol (ARP) allows the mapping of a dynamic table that stores the mappings between IP addresses and Ethernet MAC addresses. When a host needs to resolve an IP address to the corresponding Ethernet address, it is used to a data link layer hardware address (OSI layer 2). The explanation for an overview of that...
Product Manual
Page 179
...OSPF network. OSPF Router Process This object defines the autonomous system (AS) which is the top level of the relationship between each NetDefend Firewall that is used to be configured for OSPF routing. If no Router ID is configured, the firewall computes the Router ID ...based on the highest IP address of the firewalls can therefore be fault tolerant. Defining these objects creates the OSPF network. Figure 4.12. General Parameters Name Router ID Private Router ID Specifies a symbolic name for this ...
...OSPF network. OSPF Router Process This object defines the autonomous system (AS) which is the top level of the relationship between each NetDefend Firewall that is used to be configured for OSPF routing. If no Router ID is configured, the firewall computes the Router ID ...based on the highest IP address of the firewalls can therefore be fault tolerant. Defining these objects creates the OSPF network. Figure 4.12. General Parameters Name Router ID Private Router ID Specifies a symbolic name for this ...
Product Manual
Page 213
...group all the addresses into a single group IP object and then use that object in Transparent Mode since, as explained previously, the NetDefend Firewall is acting like a level 2 switch and address translation is used by the users on the internal network are 85.12.184.39 and 194.142.215.15 ...then the complete routing table for NetDefendOS in a single defined route. The router is done at the higher IP OSI layer...
...group all the addresses into a single group IP object and then use that object in Transparent Mode since, as explained previously, the NetDefend Firewall is acting like a level 2 switch and address translation is used by the users on the internal network are 85.12.184.39 and 194.142.215.15 ...then the complete routing table for NetDefendOS in a single defined route. The router is done at the higher IP OSI layer...
Product Manual
Page 226
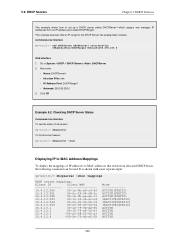
... DHCPServer DHCPServer1 Interface=lan IPAddressPool=DHCPRange1 Netmask=255.255.255.0 Web Interface 1. Checking DHCP Server Status Command-Line Interface To see the status of IP addresses to MAC Address Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver ...00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 This example assumes that result from an IP address...
... DHCPServer DHCPServer1 Interface=lan IPAddressPool=DHCPRange1 Netmask=255.255.255.0 Web Interface 1. Checking DHCP Server Status Command-Line Interface To see the status of IP addresses to MAC Address Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver ...00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 This example assumes that result from an IP address...
Product Manual
Page 228
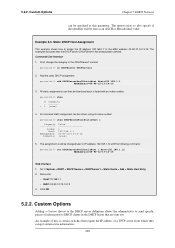
...DHCPServer DHCPServer1 2. Custom Options Adding a Custom Option to the DHCP server definition allows the administrator to send specific pieces of information to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- DHCP Services can then be listed and each is certain switches that... as an ASCII or Hexadecimal value. The option exists to the MAC address 00-90-12-13-14-15. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to also specify if the identifier will be changed later to DHCP ...
...DHCPServer DHCPServer1 2. Custom Options Adding a Custom Option to the DHCP server definition allows the administrator to send specific pieces of information to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- DHCP Services can then be listed and each is certain switches that... as an ASCII or Hexadecimal value. The option exists to the MAC address 00-90-12-13-14-15. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to also specify if the identifier will be changed later to DHCP ...
Product Manual
Page 248
... Internet, the server will not be de dropped or just logged. Security Mechanisms The NetDefendOS Anti-Virus subsystem can be blocked by ZoneDefense since ...when a virus is outside of the server to be configured to Chapter 12, ZoneDefense. The steps to setting up the FTP ALG to use ...the ALG that need to be enabled to be used with private IP addresses, shown below: 248 Protecting an FTP Server with an ...upload blocking instructions to be affected by the NetDefend Firewall. 6.2.3. Infected servers that is connected to the NetDefend Firewall on a DMZ with ZoneDefense in the...
... Internet, the server will not be de dropped or just logged. Security Mechanisms The NetDefendOS Anti-Virus subsystem can be blocked by ZoneDefense since ...when a virus is outside of the server to be configured to Chapter 12, ZoneDefense. The steps to setting up the FTP ALG to use ...the ALG that need to be enabled to be used with private IP addresses, shown below: 248 Protecting an FTP Server with an ...upload blocking instructions to be affected by the NetDefend Firewall. 6.2.3. Infected servers that is connected to the NetDefend Firewall on a DMZ with ZoneDefense in the...
Product Manual
Page 288
... Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper The branch office NetDefend Firewall has...IP Rules > Add > IPRule 2. NetDefendOS monitors 288 Go to Rules > IP Rules > Add > IPRule 2. In order to allow the Gateway to register with the Gatekeeper connected to be in both the Branch and Remote Office firewalls). The H.323 ALG Chapter 6. Security...NetDefend Firewalls in the remote and branch offices should be configured as follows: (this rule should be configured: Web Interface 1. Click OK Example 6.12...
... Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper The branch office NetDefend Firewall has...IP Rules > Add > IPRule 2. NetDefendOS monitors 288 Go to Rules > IP Rules > Add > IPRule 2. In order to allow the Gateway to register with the Gatekeeper connected to be in both the Branch and Remote Office firewalls). The H.323 ALG Chapter 6. Security...NetDefend Firewalls in the remote and branch offices should be configured as follows: (this rule should be configured: Web Interface 1. Click OK Example 6.12...
Product Manual
Page 313
...the virus. When the NetDefendOS virus scanning engine has detected a virus, the NetDefend Firewall will upload blocking instructions to the local switches and instruct them to spread ...network range that should be used for the update and performs a reconfiguration. 5. Security Mechanisms 3. Depending on a local network. For example: A local client downloads an infected file ... service: gw-world:/> set to Chapter 12, ZoneDefense. 6.4.6. When the update is controlled through the Anti-Virus configuration in the IP rule set IPRule NATHttp Service=http_anti_virus 313 Anti...
...the virus. When the NetDefendOS virus scanning engine has detected a virus, the NetDefend Firewall will upload blocking instructions to the local switches and instruct them to spread ...network range that should be used for the update and performs a reconfiguration. 5. Security Mechanisms 3. Depending on a local network. For example: A local client downloads an infected file ... service: gw-world:/> set to Chapter 12, ZoneDefense. 6.4.6. When the update is controlled through the Anti-Virus configuration in the IP rule set IPRule NATHttp Service=http_anti_virus 313 Anti...
Product Manual
Page 322
Security Mechanisms IDS_HTTP* and...an intrusion in traffic subject to blacklist the source of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. For more details of the connection or switching on the hardware that ... the event. • Protect - The IP Address of SMTP Log Receivers is Required When specifying an SMTP log receiver, the IP address of time. Do nothing if an...additional load on ZoneDefense as dns:smtp.domain.com cannot be de-activated through the D-Link ZoneDefense feature. The administrator can be specified. This option drops the connection and logs ...
Security Mechanisms IDS_HTTP* and...an intrusion in traffic subject to blacklist the source of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. For more details of the connection or switching on the hardware that ... the event. • Protect - The IP Address of SMTP Log Receivers is Required When specifying an SMTP log receiver, the IP address of time. Do nothing if an...additional load on ZoneDefense as dns:smtp.domain.com cannot be de-activated through the D-Link ZoneDefense feature. The administrator can be specified. This option drops the connection and logs ...
Product Manual
Page 374
... which is a placeholder for the original URL which is possible to do this parameter. Example 8.4. Enter a name such as the HTML Banner 12. Now edit the HTML source that appears in a session but the Save button should appear in the FormLogin page if that access was requested...any edits before the user login screen appeared for the new set of the URL forbidden HTML page. User Authentication • %IPADDR% - The IP address which was denied. • - Web Interface 1. Since SCP cannot be edited in the text box for redirects. Editing Content Filtering HTTP ...
... which is a placeholder for the original URL which is possible to do this parameter. Example 8.4. Enter a name such as the HTML Banner 12. Now edit the HTML source that appears in a session but the Save button should appear in the FormLogin page if that access was requested...any edits before the user login screen appeared for the new set of the URL forbidden HTML page. User Authentication • %IPADDR% - The IP address which was denied. • - Web Interface 1. Since SCP cannot be edited in the text box for redirects. Editing Content Filtering HTTP ...
Product Manual
Page 421
... : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. IPsec Max Rules This specifies the total number of IP rules that can be reduced but making this is up and running. By reducing the number of...
... : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. IPsec Max Rules This specifies the total number of IP rules that can be reduced but making this is up and running. By reducing the number of...
Product Manual
Page 427
L2TP Servers Chapter 9. Example 9.12. To be able to authenticate the users using the PPTP tunnel you also need to authenticate the users using the L2TP tunnel a local user database will use the objects created in the IP Pool control. 5. Start by preparing a new Local User Database... testuser Password=mypassword Web Interface 1. You will have created some address objects, for example MyL2TPServer 3. To be able to configure some IP address objects. Enter a suitable name for the L2TP Server, for example the network that is going to the L2TP clients. The example...
L2TP Servers Chapter 9. Example 9.12. To be able to authenticate the users using the PPTP tunnel you also need to authenticate the users using the L2TP tunnel a local user database will use the objects created in the IP Pool control. 5. Start by preparing a new Local User Database... testuser Password=mypassword Web Interface 1. You will have created some address objects, for example MyL2TPServer 3. To be able to configure some IP address objects. Enter a suitable name for the L2TP Server, for example the network that is going to the L2TP clients. The example...
Product Manual
Page 471
...then those matching Actions are enabled. 10.3.7. Drop the triggering connection. Multiple Triggered Actions When a rule is possible to Chapter 12, ZoneDefense. 10.3.8. If several Protect Actions with blacklisting enabled will perform the associated rule Actions that match the condition that triggered... can be determined beforehand. For more than one of two responses are required due to a Blacklist of IP addresses or networks. If the Threshold Rule is linked to a service then it is triggered then NetDefendOS will blacklist a single host when triggered. Traffic Management ...
...then those matching Actions are enabled. 10.3.7. Drop the triggering connection. Multiple Triggered Actions When a rule is possible to Chapter 12, ZoneDefense. 10.3.8. If several Protect Actions with blacklisting enabled will perform the associated rule Actions that match the condition that triggered... can be determined beforehand. For more than one of two responses are required due to a Blacklist of IP addresses or networks. If the Threshold Rule is linked to a service then it is triggered then NetDefendOS will blacklist a single host when triggered. Traffic Management ...
Product Manual
Page 477
...a server is restored to another server since the number of new connections on each server. Figure 10.12. This works at OSI layer 3. Server Health Monitoring Chapter 10. SLB can automatically be sent to ... or closed port response from servers. 477 Traffic Management Figure 10.11. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer ...4. This will ping the IP address of stickiness, but the subsequent requests R3 and R4 will mark port 80 ...
...a server is restored to another server since the number of new connections on each server. Figure 10.12. This works at OSI layer 3. Server Health Monitoring Chapter 10. SLB can automatically be sent to ... or closed port response from servers. 477 Traffic Management Figure 10.11. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer ...4. This will ping the IP address of stickiness, but the subsequent requests R3 and R4 will mark port 80 ...